In mathematics, the midpoint between the two points (x1, y1) and (x2, y2) is computed by the formula (1+x231 x1 + x2 1 + y2 2 Write a C++ program that receives two mathematical points from the user and computes and prints their midpoint. A sample run of the program produces Please enter the first point: (0,0) Please enter the second point: (1,1) The midpoint of (0,0) and (1,1) is (0.5, 0.5) The user literally enters "(0,0)" and "(1,1)" with the parentheses and commas as shown. To see how to do this, suppose you want to allow a user to enter the point (2.3,9), assigning the x component of the point to a variable named x and the y component to a variable named y. You can add the following code fragment to your program to achieve the desired effect:
In mathematics, the midpoint between the two points (x1, y1) and (x2, y2) is computed by the formula (1+x231 x1 + x2 1 + y2 2 Write a C++ program that receives two mathematical points from the user and computes and prints their midpoint. A sample run of the program produces Please enter the first point: (0,0) Please enter the second point: (1,1) The midpoint of (0,0) and (1,1) is (0.5, 0.5) The user literally enters "(0,0)" and "(1,1)" with the parentheses and commas as shown. To see how to do this, suppose you want to allow a user to enter the point (2.3,9), assigning the x component of the point to a variable named x and the y component to a variable named y. You can add the following code fragment to your program to achieve the desired effect:
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter3: Assignment, Formatting, And Interactive Input
Section: Chapter Questions
Problem 2PP: General math) a. Write a C++ program to calculate and display the midpoint coordinates of the line...
Related questions
Question
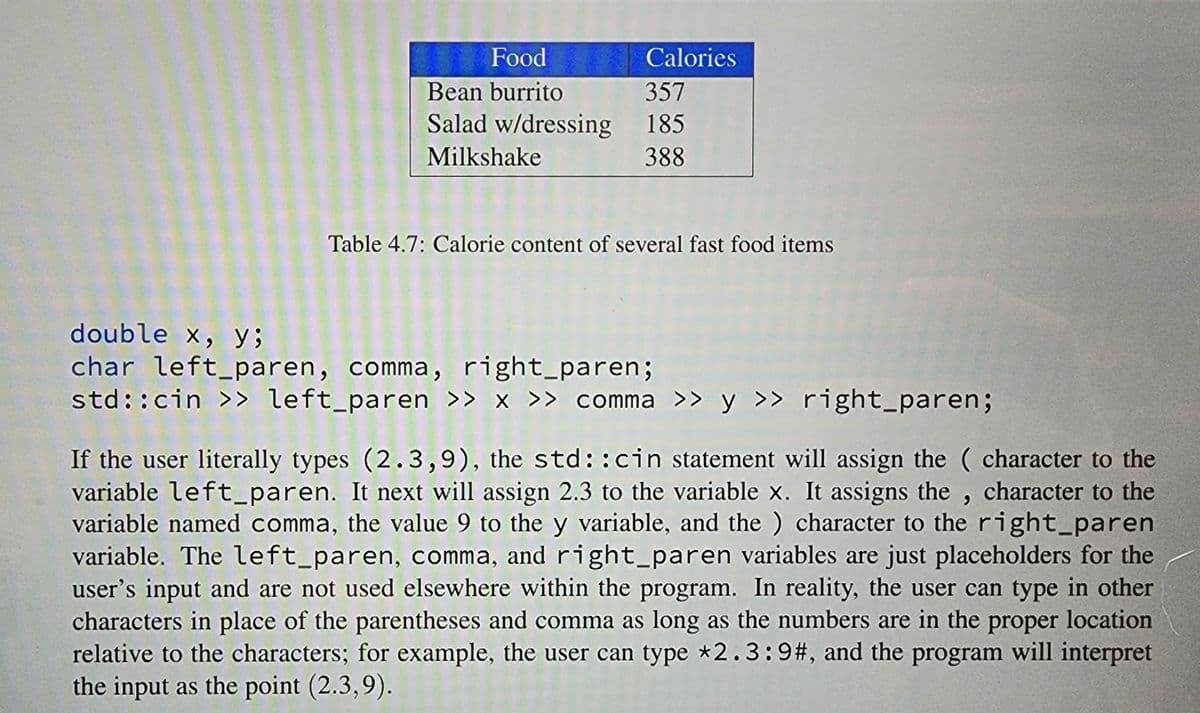
Transcribed Image Text:Food
Bean burrito
Salad w/dressing
Milkshake
Calories
357
185
388
Table 4.7: Calorie content of several fast food items
double x, y;
char left_paren, comma, right_paren;
std::cin>> left_paren >> x >> comma >> y >> right_paren;
If the user literally types (2.3,9), the std::cin statement will assign the character to the
variable left_paren. It next will assign 2.3 to the variable x. It assigns the, character to the
variable named comma, the value 9 to the y variable, and the ) character to the right_paren
variable. The left_paren, comma, and right_paren variables are just placeholders for the
user's input and are not used elsewhere within the program. In reality, the user can type in other
characters in place of the parentheses and comma as long as the numbers are in the proper location
relative to the characters; for example, the user can type *2.3:9#, and the program will interpret
the input as the point (2.3,9).
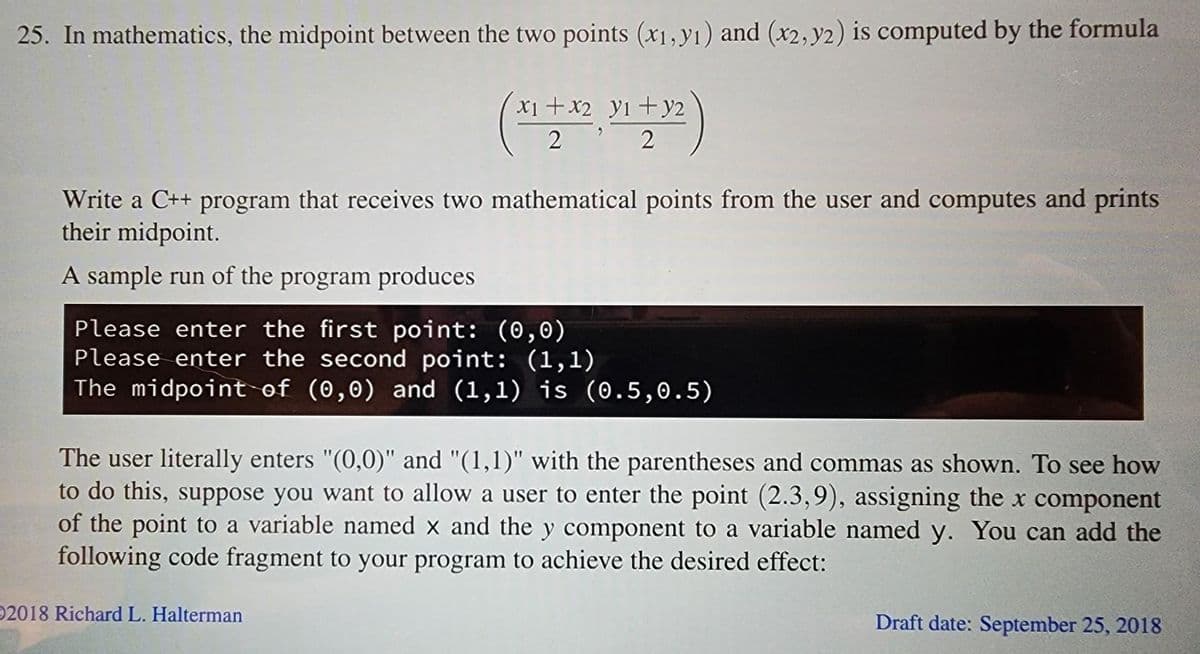
Transcribed Image Text:25. In mathematics, the midpoint between the two points (x1, y1) and (x2, y2) is computed by the formula
y2
(x1 + x2, 31 +32)
22
Write a C++ program that receives two mathematical points from the user and computes and prints
their midpoint.
A sample run of the program produces
Please enter the first point: (0,0)
Please enter the second point: (1,1)
The midpoint of (0,0) and (1,1) is (0.5, 0.5)
The user literally enters "(0,0)" and "(1,1)" with the parentheses and commas as shown. To see how
to do this, suppose you want to allow a user to enter the point (2.3,9), assigning the x component
of the point to a variable named x and the y component to a variable named y. You can add the
following code fragment to your program to achieve the desired effect:
2018 Richard L. Halterman
Draft date: September 25, 2018
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 2 images

Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr