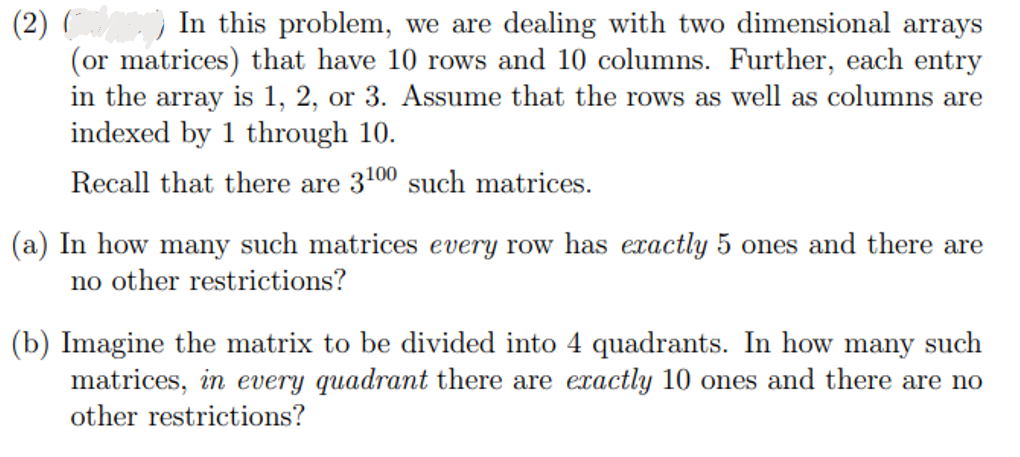
In this problem, we are dealing with two dimensional arrays (or matrices) that have 10 rows and 10 columns. Further, each entry in the array is 1, 2, or 3. Assume that the rows as well as columns are indexed by 1 through 10. Recall that there are 3100 such matrices. (a) In how many such matrices every row has exactly 5 ones and there are no other restrictions? (b) Imagine the matrix to be divided into 4 quadrants. In how many such matrices, in every quadrant there are exactly 10 ones and there are no other restrictions?
In this problem, we are dealing with two dimensional arrays (or matrices) that have 10 rows and 10 columns. Further, each entry in the array is 1, 2, or 3. Assume that the rows as well as columns are indexed by 1 through 10. Recall that there are 3100 such matrices. (a) In how many such matrices every row has exactly 5 ones and there are no other restrictions? (b) Imagine the matrix to be divided into 4 quadrants. In how many such matrices, in every quadrant there are exactly 10 ones and there are no other restrictions?
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter2: Basic Linear Algebra
Section: Chapter Questions
Problem 12RP
Related questions
Question
Explain Each Answer.
Transcribed Image Text:(2)
In this problem, we are dealing with two dimensional arrays
(or matrices) that have 10 rows and 10 columns. Further, each entry
in the array is 1, 2, or 3. Assume that the rows as well as columns are
indexed by 1 through 10.
Recall that there are 3100 such matrices.
(a) In how many such matrices every row has exactly 5 ones and there are
no other restrictions?
(b) Imagine the matrix to be divided into 4 quadrants. In how many such
matrices, in every quadrant there are exactly 10 ones and there are no
other restrictions?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole