In which of these circumstances is it advisable to use a POST request?
Chapter7: User Creation And Management
Section: Chapter Questions
Problem 3MC
Related questions
Question
Question 3
Full explain this question very fast solution sent me step by step
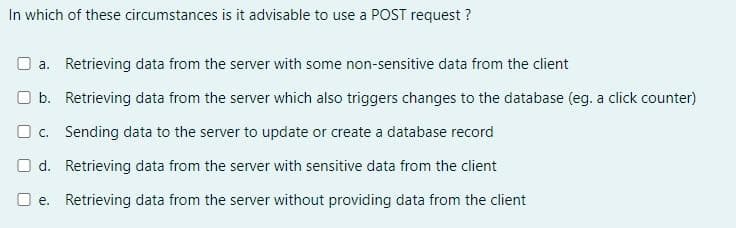
Transcribed Image Text:In which of these circumstances is it advisable to use a POST request?
a. Retrieving data from the server with some non-sensitive data from the client
b. Retrieving data from the server which also triggers changes to the database (eg. a click counter)
c. Sending data to the server to update or create a database record
d. Retrieving data from the server with sensitive data from the client
e. Retrieving data from the server without providing data from the client
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you


A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning


A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning