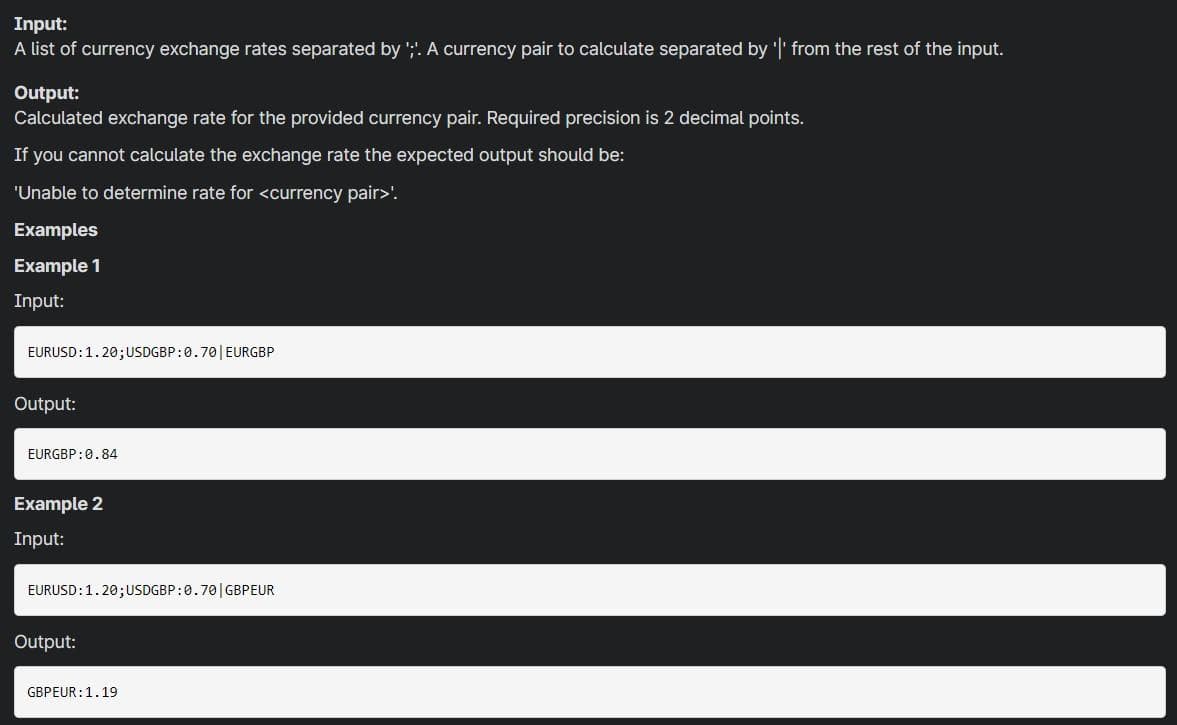
Input: A list of currency exchange rates separated by ';'. A currency pair to calculate separated by '|' from the rest of the input. Output: Calculated exchange rate for the provided currency pair. Required precision is 2 decimal points. If you cannot calculate the exchange rate the expected output should be: 'Unable to determine rate for '. Examples Example 1 Input: EURUSD:1.20;USDGBP:0.70| EURGBP Output: EURGBP:0.84 Example 2 Input: EURUSD:1.20;USDGBP:0.70|GBPEUR Output: GBPEUR:1.19
Q: What is a virtual private network (VPN) and what technologies are used to establish one?
A: A virtual private network (VPN) gives you online privacy and anonymity by creating a private network...
Q: Explains the difference between both management protocols CMIP and SNMP?
A: Common management information protocol is one of the protocols which was designed in order to give c...
Q: Develop a program (based on if-else structure) to recommend the optimum range of air flow for a give...
A: C++code for selecting fuel type and giving the result as expected in output #include <iostream>...
Q: Explain what the CPU should do in the event of an interrupt. Include the mechanism the CPU employs t...
A: Interrupt:- An interrupt is a signal which is sent to the processor emitted by hardware or software,...
Q: ur task is to check whether java is perfectly installed on your computer or not. this, you have to p...
A: Lets see the solution.
Q: Perform an experimental analysis on the two algorithms & Visualize their running times as a function...
A: Answer: What arguments would I use? Passing arguments: While running the program, we can pass valu...
Q: Explain why magnetic tape is still used in certain places
A: There are many advantages in the utilization of magnetic tapes contrasted with other capacity media....
Q: 2. In PHP, write a script to print the name of the file in which the script is running.
A: In PHP, write a script to print the name of the file in which the script is running.
Q: 1. What is a VPN had how does it make connections or communications more secure? 2. A managed switch...
A: A VPN is a Virtual Private Network. It allows people to connect over the internet, without going thr...
Q: Which column of the Zachman Framework specifies the essential knowledge required for Process Mining ...
A: - We need to talk about the process mining activity column of Zachman framework. - There are 6 col...
Q: Write down a Unix command that will update the security permissions on a file named file1.txt such t...
A: The solution to the given problem is below.
Q: C++ NOTES FROM MY TEACHER: okay, first your gonna need to set your curPtr to null. Otherwise, the w...
A: In order to reverse a doubly linked list all we need to do is swap prev and next pointers for all no...
Q: Do a 300-400 words comparison between Computer Assisting Coding and Alone Coder. Highlight the main ...
A: Computer assisted coding generate medical codes accurately from the clinic's documentation . Alone c...
Q: Create an application on C# that has two methods. The first one calculates the area of a rectangle. ...
A: The program is in next step -
Q: Q2) Write a Java code to satisfy the followings requirements: The class DrugStore has the private at...
A: Solving the above problem is very easy with java here is how :- Create the private data members ...
Q: What will be the output of the program ?
A: So, as we know here pointer stores the value at the address of str as: char *str = %c%s%c; main(){ p...
Q: I'd like to send in a PowerPoint presentation to have the APA citations and references checked again...
A: In order to display information, PowerPoint, developed by Microsoft, enables users to construct slid...
Q: An IT staff member examines the properties of World Wide Web Publishing Service on one of the organi...
A: Answer: I have given answered in the brief explanation
Q: Without using any loop In PHP programming languague The value of the input variable is 9,3,5,5,7.8 l...
A: I give the code in PHP along with output and code screenshot
Q: Your task is to check whether java is perfectly installed on your computer or not. for this, you hav...
A: According to the Question below the Solution:
Q: What is the difference between Data Mining and Process Mining?
A: Defined the difference between Data Mining and Process Mining
Q: The password is stored in a file. If you want to keep anything safe, hash it rather than encrypt it....
A: - We need to talk about a password file.
Q: I need help in following mcq What is AEh XOR BFh (AE₁₆ XOR BF₁₆)? Group of answer choices 11h (11₁₆...
A: AE in binary is written as 10101110 BF in binary is written as 10111111
Q: WHAT EXACTLY IS BLOCKCHAIN?
A: Defined about Block chain
Q: virtual private network (VPN) and what technologies are used to establish one
A: What is a virtual private network (VPN) and what technologies are used to establish one? Ans...
Q: Using the following data in the table find respective ro and s0 and remark on the data received Data...
A: Binary is a numeral system consisting of the digits 0 and 1. These digits are used by computers to s...
Q: d(x2), x)) de xe), x(3) Problem 2. Consider the following document-term dataset: (Barcelona) x(2) (C...
A: Answer: I have given answered in the handwritten format in brief explanation
Q: Write a program that starts out by flashing an LED connected to pin7 at 2Hz. On a button press (butt...
A: Given :- Write a program that starts out by flashing an LED connected to pin7 at 2Hz. On a button pr...
Q: Without using any loop in PHP programming languague The value of the input variable is 9.3,55 78 How...
A: Input : Input the list of values given in the question. Output : Get the sum of the list value wi...
Q: fahrenheit = celsius*9/5+32 1. What is the order of calculations in the conversion of a temperature?...
A: As per our guidelines, we are supposed to answer only one question. Kindly repost the remaining ques...
Q: What is connection pooling, and how does it work?
A: Connection pool means a group of connection objects.... Whenever our application needs such objects,...
Q: Explains the difference between both management protocols CMIP and SNMP?
A: Answer: However, CMIP is recognised to have a wider range of capabilities than SNMP, but is still no...
Q: 25. The following people are on 4 different committees. What is the fewest number of meetings that n...
A: There are subsets that help us decide.
Q: Complete the docstring: from typing import List def count_odds(values: List[List[int]]) -> List[i...
A: Answer: count_odds function: from typing import List def count_odds(values: List[List[int]]) -> L...
Q: Sort a array in JAVA using TreeSet data structure
A: An array is sorted using TreeSet data structure by using the descendingSet() method for returning a ...
Q: 15.a. How can a poorly attached connector affect signal strength in a fiber optic cable? A. Insertio...
A: Asper bartleby guidlines we are allowed to answer only one question please post them separately.
Q: do you agree or in-favor with the full automation of everything guided by artificial intelligence? W...
A: Answer: I am in-favor with the full automation of everything guided by Artificial Intelligence.
Q: The functional level of the forest and domain refers to the Windows Operating System version. is it ...
A: Functional levels are those levels which are used in managing and manipulating the active directory ...
Q: A class Person is given below as your base class. Your task is to create a class Employee which will...
A: The solution to the given problem is below.
Q: Name the three levels in the 3-level DB architecture.
A:
Q: Can you conceive of scenarios where range controls and null value controls will enhance data integri...
A: Introduction: Data integrity is the act of ensuring the correctness and consistency of data througho...
Q: ons of the benchmark is increased by 10% without affecting the CPI
A: given - Find the increase in CPU time if the number of instructions of the benchmark is increase...
Q: What exactly is a Unit Test Case?
A: Introduction: Unit testing is a type of testing in which the smallest part of an individual unit/com...
Q: ython please! Generalized image blender function Create a function blend images() which takes m...
A: from PIL import Image import numpy as np rgbArray = np.zeros((512,512,3), 'uint8') rgbArray[..., 0] ...
Q: column/width), what is the total capacity of the memory system? Show your answer in power of 2. (hin...
A: The answer is
Q: 5. Let R1 and R2 be regular expressions. Explain how to produce a regular expression R which describ...
A: A regular expression is a sequence of characters that specifies a search pattern in text.
Q: (10 pts) Assume a hash function H(m) which is collision resistant. This particular function maps a m...
A: Solution : Hash function A hash function is a mathematical function that converts a number-based...
Q: What are the three most important characteristics of a successful network? Describe one using your o...
A: Introduction: A network must be able to meet a variety of requirements. The three most crucial are p...
Q: Do you think using Virtual reality is dangerous?,
A: Answer: Yes, using Virtual reality is dangerous.
Q: iv) Define a Python function that takes an integer n as the parameter and returns true if n is in th...
A: Let the function be checkNum and this accepts an integer value and returns a boolean value and we ca...
Java

Step by step
Solved in 2 steps with 2 images

- Image shows the question, below is an example output: Latitude: 23 [FAILED] Calculated CRC: 3 Expected CRC: 6 1011100010110000--------00001000 0000100000001011--------00000011 Longitude: 80 [FAILED] Calculated CRC: 5 Expected CRC: 4 10100000001011000000----------0001000000 00010000000001011000----------0000011000 00000110000000010110----------0000001110 00000011100000001011----------0000000101 Elevation: 13548 [OK] 1101001110110000010110000000000000-----------------01100011101100000 0110001110110000001011000000000000-----------------00111011101100000 0011101110110000000101100000000000-----------------00010111101100000 0001011110110000000010110000000000-----------------00000001101100000 0000000110110000000000001011000000-----------------00000000110100000 0000000011010000000000000101100000-----------------00000000011000000 0000000001100000000000000010110000-----------------00000000001110000 0000000000111000000000000001011000-----------------00000000000101000…I'm running a 5-star restaurant and I can only have the best items on my menu. My menu offers 6 items, each represented by a number from 1-6. If an item on my menu does not sell or does not sell that much compared to others, I must act and replace it with something that sells! Identify which dishes do not sell. If every dish sells, print the set of dishes that were ordered least. Input: A single line containing the dish number that were ordered. Treat as one number. INPUT: 156356231 Output: The list of dishes not ordered in numerical order. If every dish sells, print the set of dishes that were ordered least. Separate each number with a new line. OUTPUT: 4A = {0,2,4,6} B = {{0},{2}, {4},{6}} C = A ∪ Ø D= A ∪ {Ø} E= { n ∈ ℕ | n² ∈ ℕ } F= { n² ∈ ℕ | n ∈ ℕ } Which are the following are true? 1. A ⊆ E, B ⊆ E, A ⊆ F, B ⊆ F, E ⊆ F, F ⊆ E. 2. O ∈ A, 0 ∈ B, {0} ∈ A, {0} ∈ B.
- A program developed for a web store represents customer account balances using a format that approximates real numbers. While testing the program,, a software developer discovers that some values appear to be mathematically imprecise. Which of the following is the most likley cause of the impression.- The account balance are represented using a fixed number of bits, resulting in over flows- The account balance are represented using a fixed number of bits, resulting in round off erros- The account balances are representedusing an unlimited number of bits, resulting in overflow errors.- The account balances are representedusing an unlimited number of bits resulting in round off errorsTrace the following Code and then print the output. msg db 'hello world$' newline db 10,13,'$' buffer db 10 dup mov ah,9 mov dx,offset msg int 21h ;new line mov ah,9 mov dx, offset newline int 21h ;enter a string from the keyboard lea dx,buffer mov ah,0ah int 21h ;new line mov ah,9 mov dx,offset newline int 21h ;adding the $ symbol at the end of the string mov bx,0 mov bl,buffer[1] mov buffer[bx+2],'$' mov ah,9 mov dx,offset buffer+2 int 21hGenerate a histogram of 20,000 randomly generated floating-point numbers according to a uniform distribution with a user-specified range [a, b], where a and b are parameters. The histogram will include the frequencies of numBins (>=21) values equal-width data bins that are equally evenly distributed between a and b. For instance, if a=2.0, b=10.0, you will calculate the frequencies total number of randomly generated values that fall into each of following data bins, where each bin has a width of (b-a)/21 and centers at 2.0, 2.0+(8.0/20)*1, 2.0+(8.0/20)*2, 2.0+(8.0/20)*3, ..., 2.0+(8.0/20)*20=10, respectively. To keep it simple, your can set the precision of each center at 0.1 (i.e., only consider the first digit after the decimal point, e.g., 2.0, 2.4, 2.8, etc.). Put all the above together, if the randomly generated value is 2.44323, it falls into the bin centering at 2.4 since rounding 2.44323 with a precision of 0.1 is 2.4.
- Develop a program that takes a set of pairs of data values (e.g. sales and month), fits a straight line to the data, and displays the results in a table and chart. Fitting a line or equation to data is done in many fields including business and scientific research. __________________________________________________________ #include <iostream> // Needed for cout and cin#include <iomanip> // Needed for setw and others#include <fstream> // Needed for ifstream#include <string> // Needed for string data type#include <cmath> // Needed for pow #include "Graph.h" // Used to graph the results using namespace std; // To use cout instead of std::cout // Function prototypesbool readArrays(ifstream& inFile, double x[], double y[], int size); int main() { // Do "Press return to continue..." on exit atexit([] {system("pause"); }); // Prompt for the name of the data file and store it in a string variable named fileName. // Put your code…Write a program that contains a function that receives two nonzero positive integers that represent the limits of a range and displays the even numbers that are in the range from smallest to largest (both limits are included) If there are no pairs in the given range, the message "No pairs" is sent.Write a program that does temperature converter :\n", "- The user will enter if he wants the result in Celsius or in Fahrenheit. Use the input function to read this option. \n", "- Ask the user the value of the temperature he wants to convert. Use the input function to read this value and convert accordingly.\n", "- If the user wants the temperature in Fahrenheit compute: $ Fahrenheit = Celsius*5/9+32$.\n", "- If the user wants the Celsius compute as follows: $ C = (F-32)*5/9 $.\n"
- A. The original Caesar cypher shifts each character by one: a becomes b, z becomes a, and so on. Let's make it a bit harder, and allow the shifted value to come from the range 1..25 inclusive. Moreover, let the code preserve the letters' case (lower-case letters will remain lower-case) and all non-alphabetical characters should remain untouched. Your task is to write a program which: asks the user for one line of text to encrypt; asks the user for a shift value (an integer number from the range 1..25 - note: you should force the user to enter a valid shift value (don't give up and don't let bad data fool you!) Test your code using the data we've provided. Test data Sample input: abcxyzABCxyz 123 2 Sample output: cdezabCDEzab 123 Sample input: The die is cast 25 Sample output: Sgd chd hr bzrsSAMPLE OUTPUT: Enter no. of views for - YouTuber 1: 987 YouTuber 2: 1010 YouTuber 3: 3217 YouTuber 4: 4532 YouTuber 5: 899 Minimum: YouTuber 5 [899 views] Maximum: YouTuber 4 [4532 views] Average: 2129.00 views YouTuber 1: NOT POPULAR YouTuber 2: NOT POPULAR YouTuber 3: POPULAR YouTuber 4: POPULAR YouTuber 5: NOT POPULAR Write a C program for the output above.Three employees in a company are up for a special pay increase. You are given a file, say Ch3_Ex5Data.txt, with the following data:Miller Andrew 65789.87 5Green Sheila 75892.56 6Sethi Amit 74900.50 6.1 Each input line consists of an employee’s last name, first name, current salary, and percent pay increase. For example, in the first input line, the last name of the employee is Miller, the first name is Andrew, the current salary is 65789.87, and the pay increase is 5%. Write a program that reads data from the specified file and stores the output in the file Ch3_Ex5Output.dat. For each employee, the data must be output in the following form: firstName lastName updatedSalary. Format the output of decimal numbers to two decimal places.

