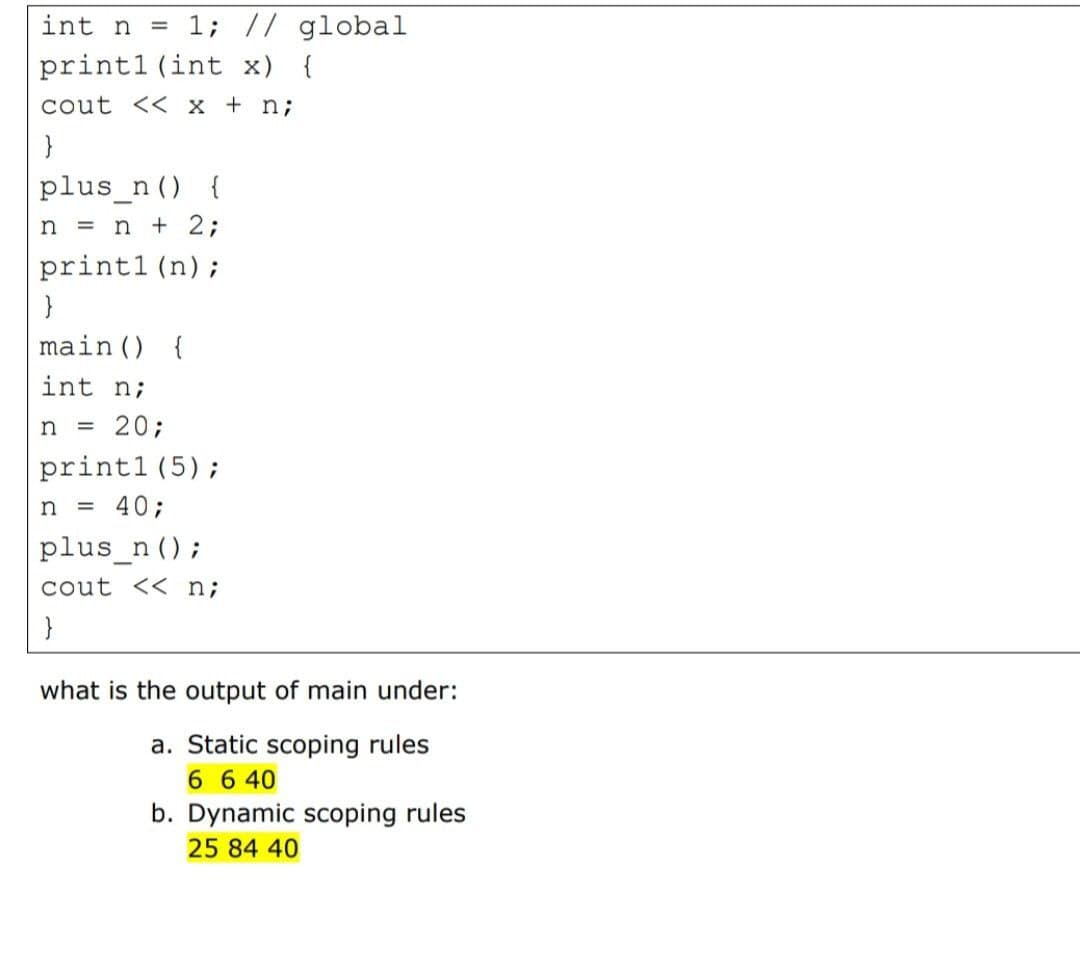
int n = 1; // global print1 (int x) { cout << x + n; plus_n () { n = n + 2; print1 (n); main() { int n; n 20; print1(5); n = 40; plus_n(); cout << n; } what is the output of main under: a. Static scoping rules 6 6 40 b. Dynamic scoping rules 25 84 40
Q: What do you mean by Rate Limiting?
A: A strategy that is used to limit network traffic is known as Rate Limiting.
Q: Suppose a signal travels through a transmission medium and its power is at the receiver is 53 Watt…
A: Attenuation is basically the loss of signal. Attenuation is the loss or degrading of the strength of…
Q: For the given set of data {40, 33, 26, 28, 24, 53, 42, 11, 33, 45}, sort the data in descending…
A: The Java code along with the snapshot of code and output is given below:
Q: use pythone language and inheritance to solve this. Thank you
A: class Product: def __init__(self,id,title,price): self.__id = id self.__title = title…
Q: Write a program to check whether the given number is even or odd.
A: NOTE : As the question is not specific about the programming language to be used to write the code ,…
Q: Draw the schematic for a multicell SRAM with 3 read ports and 2 write ports
A: i have given answer of the question below in second step:-
Q: What are the essential characteristics of cloud computing?
A: What are the essential characteristics of cloud computing?
Q: What Is A Symbol Table?
A: A data structure is a data organization, management and storage format that enables efficient access…
Q: In the framework of an information system, how do data, information, and decision-making interact?In…
A: Further, data is rational and concrete: A framework is a conceptual paradigm for organizing…
Q: Write a program that uses for loops to perform the following steps: Prompt the user to input two…
A: Ans: Code: #include <iostream> using namespace std; int main(){ int n1,n2; int…
Q: How would you describe a programming language's evolution?
A: Programming language: - Instructions in the programming language that the device understands must…
Q: Simplify following Boolean Expressions using Quine-McClukey tabular method.…
A: Simplify Boolean Expressions using Quine-MeClukey tabular method. here is the complete solution of…
Q: he Mentcare system is built by adapting a commercially available information system. What do you…
A: The testing methodology and numerous tests used in object-oriented software testing differ…
Q: The goal is to implement an intraprocedural reaching definition analysis. The input of the analysis…
A: Dаtа flоw аnаlysis: • рrорerties оf dаtа tаken intо соnsiderаtiоn the соntrоl flоw in…
Q: C++ First make 3 text files that each one includes 10 names and also make one text file that…
A: Name the three text files as names1.txt, names2.txt, names3.txt and text file with numbers as…
Q: How does a data breach affect cloud security? What are some of the potential countermeasures?
A: Given: Sales Suffering as a Result of a Data Breach Damage to one's reputation may also result in…
Q: Give an example of how mixed expressions are used.
A: Introduction: Mixed mode arithmetic occurs when one of the operands is a real number and the other…
Q: Please explain step-by-step how to find the time complexity (using Big O Notation) of a…
A: To find the big O notation of the straighforward algorithms is very easy . Let's understad by some…
Q: dentify an industry or company that makes use of MATLAB and in your own words discuss how this…
A: MATLAB is a programming language developed by MathWorks.
Q: Using System analytics, you may Undlinsareling Dwn dlivia"" (Bvo0) be able to got a cheupery of the…
A: Bring your own device (BYOD) Bring your own device (BYOD) refers to the trend of employees using…
Q: What does the phrase "time value of money" mean?
A: What does the phrase "time value of money" mean?
Q: What are the applications of Subneting?
A: According to the question the subnet allows to the community to carry out speedy and makes the…
Q: 7. Match the functionality of generalized low rank models on the left to its benefits on the right?…
A: L1 Regularization: It is also called Lasso Regression model. It is used to add some additional…
Q: Which data structure that would you use to represent the site map of Facebook? The site map of…
A: A sitemap is a file that contains all the URL'S of the website. Along with URL'S, it also contains…
Q: arts from 3 and column index is starting from 2. 2
A: In the Arrays:- a i j represents---> the entry in i th row and j th column. Whereas, In…
Q: Perform the XOR (exclusive OR) operation on the following bits: a)(10001) O(10000) )(00001) O…
A: We are going to apply XOR OPERATION on the given binary nunbers. I have solved all the 4 parts and…
Q: Explain in a few sentences what the term "memberwise assignment" refers.
A: Introduction: In a member-wise assignment, any member of one object may be assigned to another…
Q: What strategic choices do you have for legacy system evolution? When would you replace all or part…
A: Legacy systems means the usage of old software by an organization. They are called as legacy systems…
Q: What are the 2 types of backups? Where are backups stored?
A: Answer :
Q: --Problem -3 -Create a flowchart design that depicts the solving of the following problem: Asks user…
A: The Answer is in step2
Q: What Is A Symbol Table?
A: Symbol Table:- A symbol table is a dictionary it maps the name to information the compiler…
Q: Even if a programmer already understands a range of programming languages, why is it useful for him…
A: Origination: "When you join an open-source project or begin a new employment, the person who…
Q: What exactly is configuration management, and why is it so crucial?
A: Solution : Configuration Management It is the systems engineering strategy to ensuring that…
Q: 6. Write Scilab code to Plot graph of the polynomial function y= x3 -20x2 + 10x-1 over the interval…
A: In skilab we need to define an interval and assign the function to some variable. Using plot we can…
Q: List out the benefits of biometric authentication?
A: Examples of Biometric Security: Voice Recognition. Fingerprint Scanning. Facial Recognition. Iris…
Q: What distinguishes software product configuration from other configuration types? Is it possible to…
A: Product configuration: How to Configure a Product Product Configuration is the process of choosing…
Q: Why is the following term considered disjunctive normal form; A + ~B but the term…
A: A disjunctive normal form it is canonical normal form that consists of the disjunction of…
Q: Write a banking application where a user will enter their current balance and a transaction. The…
A: Find the required code in C given as below and output :
Q: You are given an array of integers below. Write a Java program to perform the following operation on…
A: Given: An array of integers is given. int []arr = {12, 7, 12, 53, 2, 5, 49, 5, 21, 0} Requirement:…
Q: Q3: Link between Five right choices in A and B lists, where N=|1 3; 3 5; 5 7ir List A a-3 b-2 List A…
A: sum function will give us column sum and thus it will give us vector [9 15] and min function will…
Q: Describe the procedure for storing data in a computer's internal memory.
A: Introduction: In most computers, the hard disc drive serves as the main data storage device. It…
Q: What exactly is database security and how does it work? Which of the two database security methods…
A: Introduction: The term "database security" relates to the safeguarding of sensitive data and the…
Q: make the code necessary to configure the upper 2 bits of Port T as input and the lower 4 as output.
A: Port configuration starts with the basics of duplex and speed. Switch ports sometimes need to have…
Q: Define the terms "response time," "bandwidth," "throughput," and "turnaround time." What is the…
A: Introduction: Response time refers to the time it takes for a user to make a request and for the…
Q: In HTML, onblur and onfocus are: Style attributes Event attributes O HTML elements
A: The style attribute determines an inline style for a component. The style attribute will supersede…
Q: Assume your boss requests you to inflate the benefit statistics for an IT proposal to boost a…
A: Justification: Raising the benefit estimates on IT proposals solely to increase the project's…
Q: Give instances of useful IT community resources for a systems analyst.
A: System analysts are responsible for maintaining and improving the computer systems of the…
Q: Using a typical benchmark program, the following machine characteristics result: Processor Clock…
A: a) MIPS rate can be computed as:
Q: (1) What are advantage and disadvantages of Apriori Algorithm (II) For the given below transaction…
A: Apriori algorithm advantages and disadvantages Associate algorithm
Q: Example 6: Write a program to create a matrix A(5*5), then print the elements of diagonal only.break
A: Step-1: StartStep-2: Declare an array A of size 5*5Step-3: Take input array elementsStep-4: Print…
Step by step
Solved in 2 steps

- IN HASKELL PROGRAMMING LANGUAGE PLEASE In case you do not know it: the game is played on a 3x3 grid that is initially empty. Two players are playing, by alternatingly making moves. A move by a player places their token (an X for player 1, an O for player 2) into a cell that was empty. We are using algebraic notations for indexing the positions in the board, with A,B,C indexing the columns and 1,2,3 the rows. Specifically, these coordinates would be used in the implementation for moves made by a human player. If the X X O Figure 1: Sample board position same token appears 3 times in any of the three columns, three rows or two main diagonals the game is over and that player wins. If the grid is filled without that happening the game is a draw. For the depicted board, we have Xs in positions C3 and A2, and an O in position B1. It would be O’s turn to make a move; a legal move would be C2, but it is not a good move, because X can force a win by responding A1. O cannot force a win, but…A binary operator is an operation that is performed on two operands. For example, addition is a binary operator that adds two operands (e.g., 2 + 4). In the provided UML diagram, all binary operators have two operands and an execute method that performs the appropriate operation on the operands. The AddOperation class should add the two operands. The SubtractOperation class should subtract the two operands. Here is an example of how a binary operator could be used: IBinaryOperator operator = new AddOperator(8, 12);System.out.println(operator.execute()); // should print 20operator.setLeftOperand(18);System.out.println(operation.execute()); // should print 30 crate a Main.java to test your codeLanguage is c++ Assignment 6 C: Minesweeper - Simplified. For many years, computers sold with the Windows operating system would contain a game called M inesweeper. The player would be presented with a grid, where they would have to click an empty part of the map. If they clicked on a hidden mine, the game would be instantly over. However, if they clicked a safe spot, a hint about nearby mines would be displayed and the player would click another spot. The goal would be to flag all the hidden mines without hitting one. (As an aside, many people did not know these rules and just clicked around randomly until they hit a mine)We will be developing a simplified version of this game. You will prompt the user for a grid size and then created a 2D array with equal width and height (C++ students: Check the Appendix for more information on how to do this). You will initialize the 2D char array with each element equallying a ‘?’ symbol. You will then randomly generate one “mine” value per…
- Java code: final static Scanner cin = new Scanner(System.in); public static void main(String[] args) { out.println("CPS 151 In-class assignment 3 by ___ your name here ___\n"); out.print("Enter n: "); int n = cin.nextInt(); long f = fib(n); out.println("\nfib(" + n + ") = " + f); out.println("\nCPS 151 In-class assignment 3 complete"); } // end main // standard fibonacci number computation using recursion static long fib(int n) { if (n < 0) terminate("Negative argument value not allowed, program ended"); if (n <= 1) return n; else return fib(n - 1) + fib (n - 2); } // end fib private static void indent(int level) { for(int Lcv = 1; Lcv <= level; Lcv++) out.print(" "); } // end indent private static void terminate(String errorMessage) { out.println(errorMessage); System.exit(1); } // end terminateidentify the following as better representing static or dynamic binding. a) an int is an int forever and ever amen b) 2/2.0 = 1.0 c) 3/2.0 -> error message d) binding is done at compile time e) binding is slower but more flexibleFor the code in java below it shows a deck of 52 cards and asks the name of the two human players and makes both players draw five cards from the deck. What I want to added into the code is for Player A to manually pick a card from his/her 5 cards and have Player B pick two cards that equal the value of Player A's card if possible. Main class code and Player class code shown below: Main class code: import java.util.ArrayList; import java.util.Scanner; import java.util.List; import java.util.Random; class Main { publicstaticvoid main(String[] args) { // card game, two players, take turns. String[] suits = {"Hearts", "Clubs", "Spades", "Diamonds"}; String[] numbers = {"A", "2", "3", "4", "5", "6", "7", "8", "9", "10", "J", "Q", "K"}; for(String oneSuit : suits){ for(String num : numbers){ System.out.println(oneSuit + " " + num); } } List<Player> listOfPlayers = new ArrayList<>(); Scanner sc = new Scanner(System.in); System.out.println("Name of Player 1");…
- 1. (Dice simulation) Java/C++ program that computes the exact probability distribution for the sum of two dice. Run experiments to validate this calculation simulating N dice throws, keeping track of the frequencies of occurrence of each value when you compute the sum of two random integers between 1 and 6. How large does N have to be before your empirical results match the exact results to three decimal places?Case Diagram and UML Class Diagram for this java code : (Below the code give some constructive critiques about the UML class diagram)…. Thanks import java.util.*; public class BeverlyBreads{public static void main(String[] args){Scanner input = new Scanner(System.in); //Array for breads String[] breads = new String[5]; //Bread choices breads[0] = "White Bread"; breads[1] = "Wheat Bread"; breads[2] = "Rye Bread"; breads[3] = "Pumpernickel Bread"; breads[4] = "Baguette"; //Prices for the breads double[] prices = new double[5]; prices[0] = 2.99; prices[1] = 3.49; prices[2] = 3.99; prices[3] = 4.49; prices[4] = 4.99; //Customer's Name System.out.println("Enter customer's name: "); String name = input.nextLine(); //Customer's Phone Number System.out.println("Enter customer's phone number: "); String phoneNumber = input.nextLine(); //Bread Selection System.out.println("Which bread would you like to order?"); for(int i = 0; i < breads.length; i++) { System.out.println(breads[i] + "…THIS NEEDS TO BE DONE IN C#! NOT JAVA! NOT C++, NOT PYTHON! PLEASE WRITE THIS IN C#! Take the following class: class Pokemon { string Name; string Type; int Health; } Override the ToString method so that it it outputs the Pokemon's heath. Example: Let's say we have a Pikachu named Sparky and it had 200 health. When we called ToString, we would get the following string: Rex: Pikachu (200)
- Write a Java program DecimalToBinary that implements the static method decimalToBinary() which converts decimal number N to its binary representation. Note: You are not allowed to use a built-in subroutine like Integer.toBinaryString(). (Consider the structure below shown in the picture. It must have the same structure)Change Java code below so that it outputs a 9x9 board and not a 3x3 board. import java.util.*; public class Tic_Tac_Toe{ static String[] board;static String turn;static String checkWinner(){for (int a = 0; a < 8; a++) {String line = null; switch (a) {case 0:line = board[0] + board[1] + board[2];break;case 1:line = board[3] + board[4] + board[5];break;case 2:line = board[6] + board[7] + board[8];break;case 3:line = board[0] + board[3] + board[6];break;case 4:line = board[1] + board[4] + board[7];break;case 5:line = board[2] + board[5] + board[8];break;case 6:line = board[0] + board[4] + board[8];break;case 7:line = board[2] + board[4] + board[6];break;}//For X winnerif (line.equals("XXX")) {return "X";} // For O winnerelse if (line.equals("OOO")) {return "O";}} for (int a = 0; a < 9; a++) {if (Arrays.asList(board).contains(String.valueOf(a + 1))) {break;}else if (a == 8) {return "draw";}} // To enter the X Or O at the exact place on board.System.out.println(turn + "'s turn; enter…(Numerical) Write a program that tests the effectiveness of the rand() library function. Start by initializing 10 counters to 0, and then generate a large number of pseudorandom integers between 0 and 9. Each time a 0 occurs, increment the variable you have designated as the zero counter; when a 1 occurs, increment the counter variable that’s keeping count of the 1s that occur; and so on. Finally, display the number of 0s, 1s, 2s, and so on that occurred and the percentage of the time they occurred.



