int sum (int n) {//assume n is non-negative if (0 == n) return 0; else n+ sum (n-1); |
Q: he following recursion occurs when there are more than two calls for each non-base case: : c)Multip...
A: SUMMARY: -Hence, we discussed all the points.
Q: Conver vert the following C code to MIPS ASsembly :
A: SUMMARY: -Hence, we discussed all the points.
Q: 11. In this problem you need to simulate part of a Yahtzee game. This turns out to be more complicat...
A: Solution:-- 1)The given question has required for the solution to be provided with the help of the...
Q: Hinclude Hinclude ciomanip> using namespace std; void test(int first, int& second); int main () int...
A: The output is below:
Q: mar created a file named hello.txt and also created an Alternate Data Stream named RData on that fil...
A: Lets see the solution.
Q: Algorithms are important to know if you want to use computers to invest in the financial market.
A: Solution: Since the role of human in commerce has diminished quickly. In their place take the comput...
Q: Hello! I am having trouble on how to write out the Java code based on the instructions (in bold //**...
A: entire code with comment is given in step 2.
Q: Write C++ program to read an integer number and check if it is positive or negative, even or odd, an...
A: C++ code to check negative, positive and odd, even #include <iostream> using namespace std; in...
Q: In healthcare, how do staffing models and labor-optimization algorithms help to make things more eff...
A: What Is Labor Optimization and How Does It Work: Labor Optimization strategies are now available to ...
Q: Create a recursive function and program for following equation using C++ f(5) = 5*(4/2)*3*(2/2)*1 ...
A: A recursive function consists of 2 cases: 1. Base case(i.e condition where recursion stops) 2. Recur...
Q: rite an 8051 assembly language program to determine if a sequence of bytes is a palendrome. The numb...
A: A palindrome is the string that is read from the front and back are read as the same. Program explan...
Q: The process of removing irregular portions of stones and facilitating their easy transportation is k...
A: The process of removing irregular portions of stones and facilitating their easy transportation is k...
Q: Let us know what this function does and why it's so important to u
A: Given To know about the function and it's uses
Q: 2. Bad Signal (C PROGRAMMING ONLY) by CodeChum Admin Thanks for helping me out on the previous prob...
A: As per the given problem, we need to complete the lionelRichie() function that prints the following ...
Q: PAYSLIP: Employee Number: Employee Name: 0111 Jon Mill Position: Programmer Hours Worked: 162 Pay Ra...
A: I give the code in JAVA along with output and code screenshot
Q: Manage Your Health, Inc. (MYH) is a Fortune 500 company that provides a variety of healthcare servic...
A:
Q: 3. Consider the world population data of Computer Problem 3.1.1. Find the best least squares (a) lin...
A: Given The answer is given below.
Q: why internet dependence is not good? what is the effect of internet depedence to our future
A: The internet is a very flexible and helpful network however it has many drawbacks and adverse effect...
Q: Describe how nonpreemption in the implementation of fair queuing results in a different packet trans...
A: Introduction: The round-robin technique is a service that is a widely used algorithm for CPU and net...
Q: Consider the following AES cipher key: 34 22 2a 3e 00 11 33 ff fe ab 22 11 3e e4 2c 55 What is the...
A: Consider the following AES cipher key: 34 22 2a 3e 00 11 33 ff fe ab 22 11 3e e4 2c 55 What is the f...
Q: Let X = {l ∈ Z | l = 5a + 2 for some integer a}, Y = {m ∈ Z | m = 4b + 3 for some integer b}, and Z ...
A: Given, X = {l ∈ Z | l = 5a + 2 Y = {m ∈ Z | m = 4b + 3 Z = {n ∈ Z | n = 4c − 1 To Prove: Y ⊆ Z
Q: c++ language, predict the output
A: 10 5 610 10 20
Q: 3. Practice on the following NumPy functions to create arrays mun Numpy functions your code: Upe svi...
A: Python code for the given NumPy functions import numpy as np a = np.zeros(2, dtype = int)print("Mat...
Q: Proseware, Inc., requires you to install a 24-port switch that directs TCP/IP traffic to logical add...
A: Switches are networking devices that receive the incoming data in form of packets and they direct th...
Q: 5. Consider the following modification of the independent set problem. As input, you receive an undi...
A: An Unaffiliated Group S is a collection of vertices in the given Graph = (V, E) in which no two vert...
Q: does an application work? In a new computer that an organisation buys, what are the different applic...
A: Lets see the solution.
Q: Using switches, 7-Segment LEDS and FAs, design and build a simple calculator to add two 4- bit numbe...
A: Below is the circuit
Q: 5. Use this array for the following practice: Arr = np.arange(10) 1a ol enoitonut 9mulM gniwollol or...
A: Dear learner , hope you are doing well , I will try my best to answer this question. Thank You!!
Q: Write an anonymous block to read two numbers from the keyboard, then find out what's the maximum bet...
A: Code: declare a number; b number;begin a:= &a; b:= &b; if a>b then dbms...
Q: Write a program in C that will add the numbers from 1 up to and including a given positive integer, ...
A: In this question we are asked to write a program in C which returns the add of numbers which are not...
Q: What makes it so hard to change things in genetic algorithms?
A: Introduction: The Genetic algorithms are used to query large amounts of data in computer science. Th...
Q: Explain why database design is critical in the educational setting.
A: Answer: A well-designed database aids in Adapting to the needs of the user. Produce high-performanc...
Q: Encrypt the message ‘STOP’ using the RSA system with n = 53 • 61 and e = 17.
A:
Q: Talk about the significance of data modelling?
A: Introduction : The practice of diagramming data flows is known as data modeling. The designer begins...
Q: Whenever FANUC picks up an item, it will read the UPC. Sometimes when analysing the UPC, the item ge...
A: According to the information given:- we have to follow the instruction to construct/ draw a use case...
Q: From the diagram, the risk management was taken by administrator failed to response the attacker tam...
A: Risk is the factor that needs to be taken care of otherwise it will produce a halt in the software o...
Q: Task1:In the driver file (main.cpp), perform the following sub-tasks.1.Create two objects of this cl...
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: Explain why the UDP
A: Q)Explain why the UDP protocol is called a simple demultiplexor. Answer: There are likely to be many...
Q: Given n pairs of parentheses, write a program in C++ to generate all combinations of well-formed par...
A: As per the requirement program is written. Algorithm: Step 1: Write the main() method Step 2: Ask th...
Q: Describe the field, constructor and method. Write its signature.
A: A function is a set of instructions that can be used to perform a certain task in computer programmi...
Q: Which of the following is an/are input/s to the Purchasing Transaction Processing System? Select one...
A: Transaction Processing system is a type of information system which is used to collect, store, modif...
Q: What is the worst-case time complexity of the function that determines efficiently if an item exists...
A: In the worst-case analysis, we calculate the upper bound on the running time of an algorithm.
Q: What does the Maple command mean?
A: Introduction: Maple command: The maple command is used to automatically finish the work of specific ...
Q: Use the strategy of the decimal to binary conversion implemented in Project 4, and the bit shift lef...
A: Code : # convert into binary def b_string (num): s="{0:b}" .format(num); retu...
Q: Find a,b,c a) 2.5 GB in MB? b) 32 x 210 bits in KB? c) 3.5 MB in bits?
A: Memory can be displayed in various forms which can be GB, MB, KB, or bits. Now we have some standard...
Q: Clustering and classification are two different things. What is the difference between them?
A: Introduction: In general, machine learning algorithms use either unsupervised or supervised learning...
Q: Perform the multiplication of the 4-bit number 1011 (multiplicand) with 1001 (multiplier) using the ...
A: Perform the multiplication of the 4-bit number 1011 (multiplicand) with 1001 (multiplier) using the ...
Q: Design a combinational circuit that accepts a 4-bit number and generates a 3-bit binary number outpu...
A: Sequential model: This NAND gate is a physical circuit during which the output is determined by the ...
Q: Q2 answer needed 1.1. Write a permutation of 9 integers which is not in sorted order. Sort the inte...
A: The answer is given below.
Q: Assuming that the time of an algorithm is given by: f(n) = 3n + (√n + 5)^4. Which of the following i...
A: The answer is O(n2).
Find the error in the code
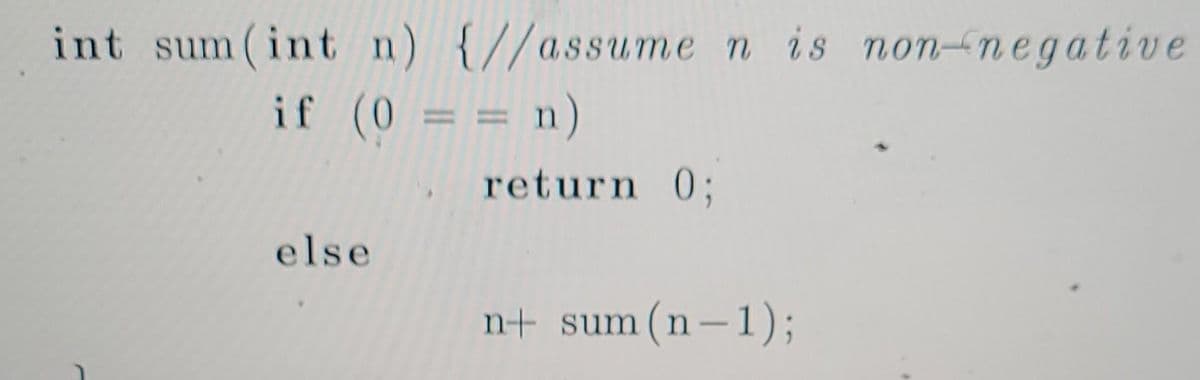
Step by step
Solved in 2 steps

- Write this method int maximum (int[] a) // returns the maximum element of a []Rewrite the following loops, using the enhanced for loop construct. Here, values is an array of floating - point numbers. a. for (int i = 0; i < values.length; i++) { total = total + values[i]; } b. for (int i = 1; i < values.length; i++) { total = total + values[i]; } c. for (int i = 0; i < values.length; i++) { if (values[i] == target) { save = i; }.Write a method that displays an n-by-n matrix usingthe following header:public static void printMatrix(int n)Each element is 0 or 1, which is generated randomly. Write a test programthat prompts the user to enter n and displays an n-by-n matrix. Here is asample run: Enter n: 3 ↵Enter0 1 00 0 01 1 1
- #include <mpi.h> int *Random_Num_Generator(int Num_Elements); int Compute_Product(int *array, int num_elements); int main(int argc, char* argv[]) { int comm_sz, my_rank;int i, Result; int Num_Per_Proc = atoi(argv[1]); // Seed the random number generator to get different results each time srand(time(NULL)); MPI_Init(&argc, &argv); MPI_Comm_rank(MPI_COMM_WORLD, &my_rank); MPI_Comm_size(MPI_COMM_WORLD, &comm_sz); // Generate a random array of elements on process 0int *Random_Nums = NULL; if (my_rank == 0){ Random_Nums = Random_Num_Generator(Num_Per_Proc * comm_sz); printf("The random numbers generated: \n"); for (i = 0; i < Num_Per_Proc * comm_sz; i++) printf("%d; ", Random_Nums[i]); printf("\n");} // Generate a buffer for holding a subset of the entire array int *Sub_Random_Nums = (int *)malloc(sizeof(int) * Num_Per_Proc); // Scatter the random integer numbers from process 0 to all processes MPI_Scatter(Random_Nums,…Given a non-negative integer N, the task is to find the Nth row of Pascal’s Triangle. import java.util.ArrayList;public class NthRowPascal{public static ArrayList<Integer> solution(int nth){// ↓↓↓↓ your code goes here ↓↓↓↓return new ArrayList<>();}}input an unsorted array A of n number and an integer k with 1<= k <= n. output an array B of size k that contains the k largest numbers in A with B[1] >= B2....>=[k] index of the array starts from 1 1. write algorothim pseudocode. analyze the bestcase .k . analyze the worse case of k.
- Java: Write a recursive method that finds and returns the sum of the elements of an int array. Also, write a program to test your method.Complete the private combinations method. Modify the code so that it is possible to compute combinations(“ABCD”,2) with fewer than 20 calls and combinations(“ABCDE”,3) with fewer than 30 calls. import static org.junit.Assert.*; import java.util.ArrayList; import org.junit.Test; /** * Recursive computation of all combinations of k characters from a string s. * */public class Combinations { private static int recusiveCalls = 0; /** * Generate all combinations of the characters in the string s with length * k. * * @param s * a string. * @param k * the length of the combinations * @return a list of all of the combinations of the strings in s. */ public static ArrayList<String> combinations(String s, int k) { return combinations("", s, k); } /** * Recursive Problem Transformation: * * Generate all combinations of length k of the characters in rest prefixed * with the characters in…Write a recursive method that returns thelargest integer in an array. Write a test program that prompts the user to enter alist of eight integers and displays the largest element.
- Count the number of elements in a that have values between 10 and 20 inclusive. int count=0; for(int i=0;i<10,i++) { if(a[i]>=10 && a[i]<=20) { count=count+1; } System.out.println(“count… = “+ count); }Correct answer will be upvoted else Multiple Downvoted. Don't submit random answer. Computer science. Ridbit begins with an integer n. In one action, he can perform one of the accompanying tasks: partition n by one of its appropriate divisors, or take away 1 from n in case n is more prominent than 1. An appropriate divisor is a divisor of a number, barring itself. For instance, 1, 2, 4, 5, and 10 are appropriate divisors of 20, however 20 itself isn't. What is the base number of moves Ridbit is needed to make to decrease n to 1? Input The principal line contains a solitary integer t (1≤t≤1000) — the number of experiments. The main line of each experiment contains a solitary integer n (1≤n≤109). Output For each experiment, output the base number of moves needed to lessen n to 1.in Python Minima in permutations. Write a program that takes an integer n from the command line, generates a random permutation, prints the permutation, and prints the number of left-to-right minima in the permutation (the number of times an element is the smallest seen so far). Then write a program that takes integers m and n from the command line, generates m random permutations of length n, and prints the average number of left-to-right minima in the permutations generated

