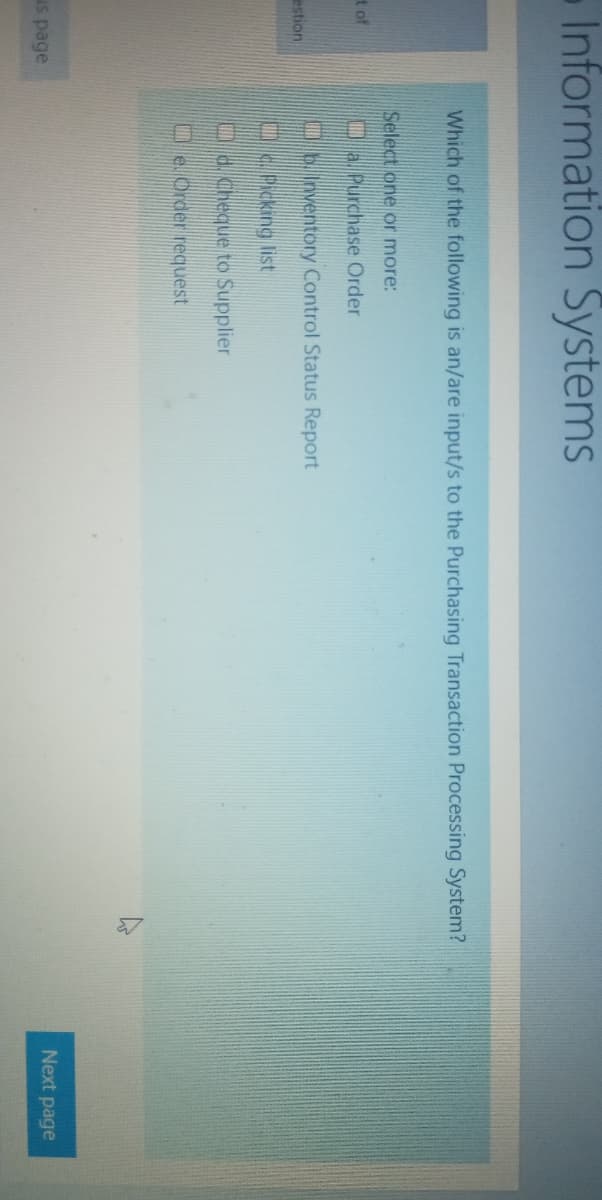
Which of the following is an/are input/s to the Purchasing Transaction Processing System? Select one or more: Oa. Purchase Order Ob.nventory Control Status Report Oc Picking list Od.Cheque to Supplier Oe. Order request
Q: QI Write program in fortran to find the maximum number of (x,y,z)?
A: Answer is given below
Q: Write C++ program to read an integer number and check if it is positive or negative, even or odd, an...
A: C++ code to check negative, positive and odd, even #include <iostream> using namespace std; in...
Q: 2. For the following pairs of functions, determine which function grows faster. f(z) = 6r3 – 5a2 +9,...
A: As we know if limit extends to infinite f(x)/g(x) = 0 ==> g(x) grows faster if limit extends to ...
Q: make a c prorgam input 5 7
A: As per the requirement program is written. Algorithm: Step 1: Write main()method Step 2: Define the ...
Q: Please help I’m not sure what to do I’ve done it over and over and it keep giving me an errors
A: Logic:- within input pass message which you want to show while taking input. Within print pass mes...
Q: ) Define the term of methodologies, techniques, and tools?
A: Methodologies, tools and techniques are different terms, although they look similar but meaning of e...
Q: Determine whether the following argument is valid or invalid. Include a truth table and a few words ...
A: Here, I have to provide a solution to the above question.
Q: Give numerical instance to Elgamal with respect to key generation, encryption and decryptipn using 1...
A: Lets see the solution.
Q: DECODE
A: Code: #include <bits/stdc++.h> // header files to read from console and print to console using...
Q: How do I import a image file, for example a flower.png with the image of a sunflower, to a java prog...
A: How do I import a image file, for example a flower.png with the image of a sunflower, to a java prog...
Q: onsider the function the following rati 10 4- --6 -4 -4 to
A: Given Consider the function the following rational function 10-8 6 4 I 2 -4 rn 1. The equation of ...
Q: Hello this code writtten in c++. Code runs perfectly fine i just want a way to change it make it dif...
A: C++ program to check whether expressions are balanced or not
Q: Create an essay about the given question. What can we do about the growing e-waste problem?
A: let us see the answer:- Introduction:- In our digital age, it appears that fewer and fewer customers...
Q: Question : By using Python Programming Language, Plot two simple bar diagrams showing the average re...
A: we will plot data using matplotlib as data values are not clear i have wrtten all formula and how to...
Q: Instruction: Create a java program that generates elements (randomly from 10 – 75) of a 2-dimensiona...
A: Logic :- (I) To generate random number in range:- arr[i][j]= Min + (int)(Math.random() * ((Max - M...
Q: 5. E = { amb" | m, n >0 }
A:
Q: Create a list of sublists. Each sublist contains a rank (an integer from 1 to 13) and a suit ('Heart...
A: 1)THE CODE # import random class import random # declare the deck deck= [ ["A", "Spades"], ...
Q: Create a Java Project (with a class and a test class) to represent some real-world entity such as a ...
A: For this use a real life example of pet which will be a class comprising of attribute.
Q: regular expression that represents the following language
A: Given :- The language L = { dv, dvdv, dvdvdv, dvdvdvdv, ...... } , an infinite regular language is m...
Q: What to consider when we design interfaces for different environments?
A: We consider some points when we design any interface First we check the interaction pattern which n...
Q: The question is whether society has become too reliant on computer applications for commerce, commun...
A: It is arguably true that the society has become too reliant on computer applications. If we look aro...
Q: Use the Monte Carlo method to estimate the following. 1 1. lo' exp(exp(x)) dx 2. E(N) where N is def...
A: Given The answer is given below.
Q: Give some examples where traffic analysis could jeopardize security. Describe situations where end-t...
A: When it comes to network traffic analysis, there are a variety of scenarios where the results could ...
Q: Show me the world by CodeChum Admin Hi Programmer, I'm planning to impress my crush. It seems that ...
A: Algorithm: Start Implement display() method that takes an array 'world'and it's size 'n' as argumen...
Q: 3. Consider the world population data of Computer Problem 3.1.1. Find the best least squares (a) lin...
A: Given The answer is given below.
Q: Proseware, Inc., requires you to install a 24-port switch that directs TCP/IP traffic to logical add...
A: Switches are networking devices that receive the incoming data in form of packets and they direct th...
Q: Create two classes: Rectangle and Cuboid. Cuboid is a child class for rectangle Rectangle - length: ...
A:
Q: Write a Normal Polish Notation program WITHOUTusing standard java libraries for stacks, queues etc.Y...
A: JAVA Program: import java.util.*; public class Polish{ static boolean ifOperator(String ch) { ...
Q: Write down a simple code for stroing studnet data in a link list. You must be able to search the rec...
A: A palindrome is the string that is read from the front and back are read as the same. Program explan...
Q: For each customer who has a post-paid service, show how many of these customers have opted to have ...
A: COUNT(): The COUNT() function calculates the number of items that meet a given set of criteria. Synt...
Q: In what ways can constellations be useful to people? Give two examples.
A: NOTE :- Below i explain the answer in my own words by which you understand it well. constellati...
Q: Consider the following convolutional layer. Input volume: 16163 Four 22 fiters with stride 2 and pad...
A: Given: Goal: We have to find number of parameters in given convolutional layer with given details.
Q: he question is "Write a python script using scapy to create a fragment with 20 bytes of IP header an...
A: SUMMARY: -Hence, we discussed all the points.
Q: Encode õevõpov with Huffman coding. a. List all symbols and their probabilities b. Find the Huffman ...
A: The Answer is given below!!
Q: Given a hard drive with the following characteristics: 1024 B sector 15,000rpm 4 ms average seek tim...
A: The rotational speed is 15000 rpm That is, 15000 rotation 60 second 1 rotation x seco...
Q: assume the ff. input values: 7364 2635 Show the output of the ff. program: include ciostream> using ...
A: input :- 7 3 6 4 output:-
Q: 3. Find the Culprit by CodeChum Admin
A: the answer to the following question:-
Q: From the diagram, the risk management was taken by administrator failed to response the attacker tam...
A: Risk is the factor that needs to be taken care of otherwise it will produce a halt in the software o...
Q: What are the best solutions in algorithms?
A: Algorithms are problem solving procedures which can be figured out mathematically. Converting an alg...
Q: In your own words, what does "Logical Before Physical" means on the context of systems analysis and ...
A: Introduction: System analysis and design: It is a field that deals with the designing and analytics ...
Q: rite an 8051 assembly language program to determine if a sequence of bytes is a palendrome. The numb...
A: A palindrome is the string that is read from the front and back are read as the same. Program explan...
Q: What are the advantages of using a compiled language over an interpreted language? In which circumst...
A: Compilers translate compiled languages into machine code that can be executed by the processor. As a...
Q: Describe the field, constructor and method. Write its signature.
A: A function is a set of instructions that can be used to perform a certain task in computer programmi...
Q: Compare and contrast the terms readability and writability regrading to the languages Java and C
A: In programming languages, writability and readability is very important. Re-designing existing code ...
Q: What makes it so hard to change things in genetic algorithms?
A: Introduction: The Genetic algorithms are used to query large amounts of data in computer science. Th...
Q: Using an implicit cursor, write an anonymous block that will add 25% to the salaries of all employee...
A: Code: DECLARE total_rows number(2);BEGIN UPDATE Employee SET salary = salary + (0.25*salary)WHERE de...
Q: ProcessBurst Time Priority Arrival Time P1 10 3 0 ...
A: Shortest Job First:- The Shortest Job First is one of the scheduling algorithms in the CPU where the...
Q: Exercise 5 Consider the electrical network shown. 50 V 40 V 32 22 20 30 V 20 V Find current flows ov...
A: Solution (a)Finding Equations to solve (b) Solving in MATLAB % Define equations as symbolic syms ...
Q: Write a loop that will increment the RBX register four times. Use the INC instruction to increment R...
A: The answer is given below:-
Q: 18.a. What does an Ethernet network use to synchronize data traffic? A. Coding B. UTP C. STP D. WDM
A: Defined an Ethernet network used to synchronize data traffic
Step by step
Solved in 3 steps

- The questions in this section are all based on the “Online Book Exchange System (EyesHaveIt.com)” Case Study on the last page of this document. Read the case study carefully before answering these questions. A system analyst in your team has identified main user goals for the system, as shown below. Use ONLY the goals in this list to draw a Use Case diagram with all the actors and associations required.Goals List Online account registration Searching for book Adding and Removing book Viewing order status Opening dispute on order Listing book Notifying shipments TheEyesHaveIt.Com Book Exchange Case Study TheEyesHaveIt Book Exchange is a type of e-business exchange that does business entirely on the Internet. The company acts as an exchange point for both buyers and sellers of used books. For a person to offer books for sale, he/she must register an account with TheEyesHaveIt. The person must provide their full name, current physical address, telephone number, and e-mail address. A…Good morning Sir. Please Sir.Thx. 1.Please draw 2 activity diagram about online shopping system (must use swimlane).HCI What category of users are those who make use of College Information Management System (CIMS) for the first time? (Choose one) a. Casual User b. Novice c. Expert User d. Regular User
- As part of your Systems Analysis project to update the automated accounting functions for Cinimod Corporation, a global maker of confectionaries, you will interview Trish Mensah, the chief accountant. 1. Write four open-ended questions that you will email to Trish prior to your interview. 2. Explain why it is preferable to conduct an interview in person rather than via email.(should be well explained)A ________ is an organized collection of people, procedures, software, databases, anddevices that provides routine information to managers and decision makers.a. transaction processing system (TPS)b. management information system (MIS)c. enterprise resource planning (ERP) systemd. supply chain management systemAs part of your Systems Analysis project to update the automated accounting functions for Cinimod Corporation, a global maker of confectionaries, you will interview Trish Mensah, the chief accountant. 1. State which structure you will choose for this interview. Why? (should be well explained) 2. Trish has four subordinates who also use the system. Would you interview them also? Why or why not?(should be well explained)
- As part of your Systems Analysis project to update the automated accounting functions for Cinimod Corporation, a global maker of confectionaries, you will interview Trish Mensah, the chief accountant. Explain why it is preferable to conduct an interview in person rather than via email.(should be well explained)HCI What category of users are those who make use of College Information Management System (CIMS) for the first time? a. Casual User b. Novice c. Expert User d. Regular UserAnswer the following questions in a Microsoft® Word document and save the file on your computer with your last name in the file. (Example: module_01_review_Jones.doc) What are four major components of an information system? Apply Michael Porter’s three strategies and the Five Forces Model for successfully competing in the marketplace to a new business and to an established business. How might the strategies differ? What are three differences between computer literacy and information literacy? What are two applications of transaction-processing systems? Provide one example of management information systems in the private sector and one in the public sector. What are two differences between data and information? Explain three applications of computers and information systems in the daily life of a college student. List three decisions that are supported by a HRIS, FIS, and LIS.
- 11) An organization's IT infrastructure must effectively integrate several business functions in order to accomplish the fulfillment process. True or False? True FalseCreate a Sequence Diagram for an online money remittance that can solve the following objectives: General objectives: Improve the business's operational efficiency and productivity and increase customer satisfaction with its services. Specific objectives: To strictly monitor the transaction history by providing accurate and timely transaction reports. To create a system that automatically updates in real-time. Ask for the customers' and users' feedback or suggestions to improve the system. To upgrade the current processing speed of the system .What kind of process can be defined as a set of activities performed across a an organisation that creates output that is of value to the customer? a. An input process b. A quality process c. A business process d. An information process



