is needed to create a new instance of the class? O A field O An instance attribute OA constructor A superclass O A private attribute
Q: In order to improve the overall quality of your project, could you quickly explain any two of the…
A: Quality Regulation: To maintain development and maximize welfare, governments must manage both the…
Q: What incentives does a mobile network operator have to continue investing in its network…
A: The following are some financial inducements for a mobile network operator to keep investing in a…
Q: CHALLENGE ACTIVITY 1.8.2: Total cost. A drink costs 2 dollars. A taco costs 3 dollars. Given the…
A: Step-1: Start Step-2: Declare variables tacos, drink and totalCost Step-3: Take input for drink and…
Q: Give an illustration while outlining the features and capabilities of the central processor unit of…
A: Introduction: The central processing unit, or CPU, is a component of all different kinds of…
Q: Consider a network layer that senses collisions and retransmits imme- diately on detection of a…
A:
Q: Give realistic real-world examples that distinguish between hard and soft real-time communication…
A: Definition: Real-time systems are a unique class of systems where a task must be completed before to…
Q: Every time you call a method, you are required to provide the required data.
A: A method is an executable that is class-defined. Class and instance methods are both supported by…
Q: A computer may generate and analyze information in a variety of ways due to its versatility. Could…
A: Computers, like human brains, process information. The central processing unit (CPU) of a computer…
Q: cache. Address: 2-way cache Block size: 2
A: The answer is
Q: Discuss situations under which the least frequently used page- replacement algorithm generates fewer…
A: Cache eviction strategies include LRU (Least replacement algorithm) and LFU (Least frequently used…
Q: What do we mean exactly when we refer to a computer network? What elements make up the network as a…
A: Introduction Networking, otherwise called PC networking, is the act of shipping and trading…
Q: Explain how the probabilistic and deterministic methods to Ethernet vary from one another.
A: Deterministic ethernet -- Deterministic Ethernet refers to a networked communication technology that…
Q: In order to improve the overall quality of your project, could you quickly explain any two of the…
A: Quality can be summarized as the study and application of identifying and achieving desired…
Q: Explain how the probabilistic and deterministic methods to Ethernet vary from one another.
A: Introduction Ethernet is the conventional innovation for interfacing gadgets in a wired local area…
Q: Give a simple heuristic for finding two paths through a network from a given source to a given…
A: Two methods may be used to obtain a simple heuristic for identifying two routes within a network…
Q: What role is the Internet of Things (IoT) playing in everyday life for ordinary people? List five…
A: The Internet of Things (IoT) is the technology behind the smart appliances which we often use in…
Q: Is it accurate to say that a computer has a lot of parts yet doesn't need power?
A: It is not accurate to say that a computer has a lot of parts yet doesn't need power.
Q: In step 4 of the CSMA/CA protocol, a station that successfully transmits a frame begins the CSMA/CA…
A:
Q: A network has to fulfill three requirements in order to function correctly and efficiently and carry…
A: Given: We need to stress the three things a network needs to have in order to work well and…
Q: In the context of a computer network, explain how dependability and availability are related. the…
A: An electronic network: This system of interconnected computers allows for the sharing of data and…
Q: Consider a network layer that senses collisions and retransmits imme- diately on detection of a…
A: Early Ethernet technology for local area networks mostly employed the access control (MAC) technique…
Q: What are the three characteristics that a network must have in order to be functional and effective?…
A: Start: Production schedulers now specify the location and methods of production as well as the…
Q: Give a simple heuristic for finding two paths through a network from a given source to a given…
A:
Q: It is important to talk in-depth about the new scalability-enabling cloud computing capabilities.…
A: Given: Describe the significance of new cloud computing features that enable scalability. Give…
Q: The role played by the Internet of Things in the development of smart homes. Give some examples.
A: Introduction: If a home has multiple smart appliances that you can control from a distance by…
Q: c) () If a CPU has 24 address lines and 24 bit data bus. Show the design of L3 (direct mapped cache)…
A:
Q: The words "computer architecture" and "computer organization" are not equivalent when referring to…
A: Computer architecture describes what a computer can accomplish, while computer organization…
Q: Explain how the probabilistic and deterministic methods to Ethernet vary from one another.
A: Answer : Probabilistic methods : Thus methods is used to connecting devices on the basis of…
Q: Any aspects of software engineering that have escaped attention? Explain?
A: Answer:
Q: Consider a network layer that senses collisions and retransmits imme- diately on detection of a…
A: Definition: The media access control system known as CSMA/CD (Carrier Sense Multiple Access/…
Q: Identify the syntax as either valid or invalid Mov al, 6789
A: The syntax is Valid as is a logical error and will result in overflow of AL register
Q: e of networking in the field a
A: Solution - In the given question, we have to tell the significance of networking in the field of…
Q: Why is the implementation of a destructor by a class required?
A: Introduction: Unless we have dynamically allocated memory or a pointer in the class, the default…
Q: Is it accurate to say that a computer has a lot of parts yet doesn't need power?
A:
Q: The rational unified model and the traditional waterfall paradigm should be compared and contrasted.
A: Here, we've highlighted distinctions between the traditional waterfall approach and the logical,…
Q: Discuss situations under which the least frequently used page- replacement algorithm generates fewer…
A: Least Frequently Used Algorithm: The least often used page replacement algorithm is the one that…
Q: A network is a collection of potential channels via which computers might talk to one another. What…
A: Introduction A computer network is a system in which various nodes are linked to one another in…
Q: What distinguishes Windows modes that force the machine to shut down from those that don't?
A: Given: A tool called Installer Windows Module checks the Windows updates on your computer…
Q: What does the phrase "computer network" really mean? What are the many components that combine to…
A: A network comprises multiple nodes, or computers, that are connected to facilitate sharing resources…
Q: How can quality assurance promote the use of native Android and iOS applications with e-commerce…
A: E-Commerce Domains: The address and identity of your online store are provided by your domain…
Q: Doesnt it hast to go 6,2,5,1 since there is a directed edge from 2 to 6? my answer is:(starting…
A: Here's the solution:
Q: The derivation of an O(log(N)) program for Fibonacci series also explain it.
A: find the n th term in O(log(N)). For that compute it using power formula. You can calculate the…
Q: The Ghana Statistical Services (GSS) is interested in your statement in “b” above but it is of the…
A: #include <iostream>using namespace std; // The function for returning valuesstring…
Q: Discuss situations under which the least frequently used page- replacement algorithm generates fewer…
A: Discuss situations under which the least frequently used page replacement algorithm generates fewer…
Q: Discuss situations under which the most frequently used page-replacement algorithm generates fewer…
A: Introduction: LRU (Least replacement algorithm) and LFU (Least frequently used) are nothing but…
Q: One of the string objects may be used to determine where the substring is.
A: Contiguous substrings of a string are sets of characters. As a result, it must be a continuous…
Q: What does the phrase "computer network" really mean? What are the many components that combine to…
A: Start: A network is made up of the a multiple nodes, or computers, that are connected to one another…
Q: In this comparison, the Classical Waterfall model and the Rational Unified model will both be…
A: In the given question there are number of different software development methodologies used in the…
Q: Describe how you interpret the term "software crisis" in relation to current software engineering…
A: Introduction: The problem of producing feasible and useful computer programmes within the time…
Q: A collection of 2" stations uses the adaptive tree walk protocol to arbitrate access to a shared…
A: The answer for the above question is given in the below steps for your reference.
OOPs
In today's technology-driven world, computer programming skills are in high demand. The object-oriented programming (OOP) approach is very much useful while designing and maintaining software programs. Object-oriented programming (OOP) is a basic programming paradigm that almost every developer has used at some stage in their career.
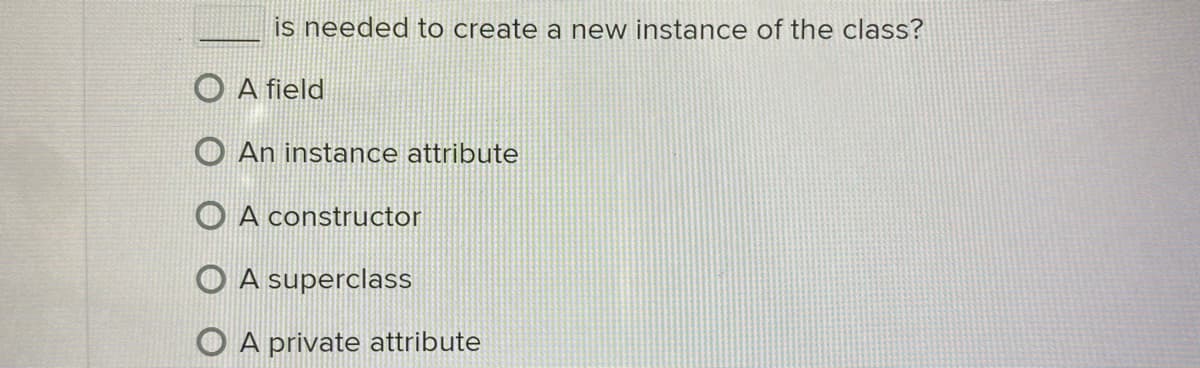
Constructor
The easiest way to think of a constructor in object-oriented programming (OOP) languages is:
Step by step
Solved in 2 steps

- tri1 and tri2 are instances of the Triangle class. Attributes height and base of both tri1 and tri2 are read from input. In the Triangle class, define instance method print_info() with self as the parameter to output the following in one line: 'Height: ' The value of attribute height ', base: ' The value of attribute baseCreates a class Student with 3 attributes: name, id and level. a. Add a constructor able to create a Student; b. Add the methods getId and getLevel; c. Add the method display able to display the attributes,Please complete the following tasks: Write a class “Actor” that contains two attributes with the appropriate level of visibility explicitly defined. “Name” which is a String, Private, “NumberofAwards” which is an integer, private Write a default Constructor for this class that initializes the name to “Bob Smith” , and the number of awards to 0. Write an overload the constructor for this class that accepts actor’s name as a parameter Write accessor methods for each of the attributes. Write a method “winsAnOscar” that increases the number of awards by one and prints “The crowd applauds for <actor’s name>!” Be sure to use accessors where appropriate. Make sure your header is complete, with the appropriate level of visibility and any required keywords.
- Which of the following statement is not true? An anonymous inner class is compiled into a class named OuterClassName$InnerClassName.class An anonymous inner class must always extend a superclass or implement an interface, but it cannot have an explicit extends or implements clause. An anonymous inner class always uses the no-arg constructor from its superclass to create an instance. If an anonymous inner class implements an interface, the constructor is Object(). An anonymous inner class must implement all the abstract methods in the superclass or in the interface.Creates a class Student with 3 attributes: name, id and level. a. Add a constructor able to create a Student; b. Add the methods getId and getName; c. Add the method display able to display the attributes,Is there a different way of doing this problem? Question: Create a class AccessPoint with the following attributes: x - a double representing the x coordinate y - a double representing the y coordinate range - an integer representing the coverage radius status - On or Off Add constructors. The default constructor should create an access point object at position (0.0, 0.0), coverage radius 0, and Off. Add accessor and mutator functions: getX, getY, getRange, getStatus, setX, setY, setRange and setStatus. Also, add a set function that sets the location coordinates and the range. Add the following member functions: move and coverageArea. Add a function overlap that checks if two access points overlap their coverage and returns true if they overlap. Add a function signalStrength that returns the wireless signal strength as a percentage. The signal strength decreases as one moves away from the access point location. Test your class by writing a main function that creates five access…
- User: Make a class called User. Create two attributes called first_name and last_name,and then create several other attributes that are typically stored in a user profile. Makea method called desctibe_user() that prints a summary of the user's information. Makeanother method called greet_user() that prints a personalized greeting to the user.Then - Create several instances representing different users, and call both methods for each user. Admin: Write a class called Admin that inherits from the User class. Add an attribute,privileges, that stores a list of strings like "can add post”, "can delete post”, "can banuser”, and so on. Write a method called show_privileges() that lists the administrator'sset of privileges. Then - Create an instance of Admin, and call your method.Modified Circle class and test file: Add a new attribute for color (or any other new attribute) Add get/set methods for this new instance variable, including data validation in set method (assuming background is black, i.e. circle color can't be black, reset to any non-black color if black is entered ). Add a new constructor to pass the color attribute as an argument. Add an instance method to display all properties of a Circle object. Create 2 objects using different constructors in test file, with invalid data. Use this test java file test java file: class CircleTest{ public static void main(String[] args){ int num = 10; Circle c1 = new Circle(0.001); Circle c2 = new Circle("black", -9); c1.display(); c2.display(); c1.setRadius( -1); c1.setColor("black"); c1.display(); }}An aggregate object refers to an instance of a class that ....... (FILL IN THE GAP ) A contains attributes B contains private attributes C contains static methods D contains private methods E contains other objects
- Which one is true? A) An inner class can be declared public or private subject to the same visibility rules applied to a member of the class. B)An inner class can be declared static. A static inner class can be accessed using the outer class name. A static inner class cannot access non-static members of the outer class. C)An inner class supports the work of its containing outer class and is compiled into a class named OuterClassName$InnerClassName.class. D)Inner classes can make programs simple and concise.1. Create 2 interfaces: BankInterface and PetInterface. BankInterface contains only 1 abstract method: accountType() which does not return anything and takes 1 String argument: accType. PetInterface contains only 1 abstract method: petType() which does not return anything and takes 1 String argument petType. 2. Create an abstract class named Student. This class contains 2 instance variables, 1 constructor, and 2 abstract methods. a. Instance variables: stId and stName (Use must use appropriate data type.) b. A 2-argument constructor that will be called from its subclass (the concrete class) to load 2 instance variables of this level during the creation of an object in its subclass. c. 2 abstract methods: getStId and getStName.. Each of these methods, when sub classed into concrete ones, should return the respective values of the instance variables stId and stName. d. At this level you should do something to get the object state at this level. 3. Create a concrete class named…1. Create 2 interfaces: BankInterface and PetInterface. BankInterface contains only 1 abstract method: accountType() which does not return anything and takes 1 String argument: accType. PetInterface contains only 1 abstract method: petType() which does not return anything and takes 1 String argument petType. 2. Create an abstract class named Student. This class contains 2 instance variables, 1 constructor, and 2 abstract methods. a. Instance variables: stId and stName (Use must use appropriate data type.) b. A 2-argument constructor that will be called from its subclass (the concrete class) to load 2 instance variables of this level during the creation of an object in its subclass. c. 2 abstract methods: getStId and getStName.. Each of these methods, when sub classed into concrete ones, should return the respective values of the instance variables stId and stName. d. At this level you should do something to get the object state at this level. 3. Create a concrete class named…





