Is the erd crows foot notation drawn for the case study correct
Chapter7: Developing An Excel Application
Section: Chapter Questions
Problem 3RA
Related questions
Question
Is the erd crows foot notation drawn for the case study correct
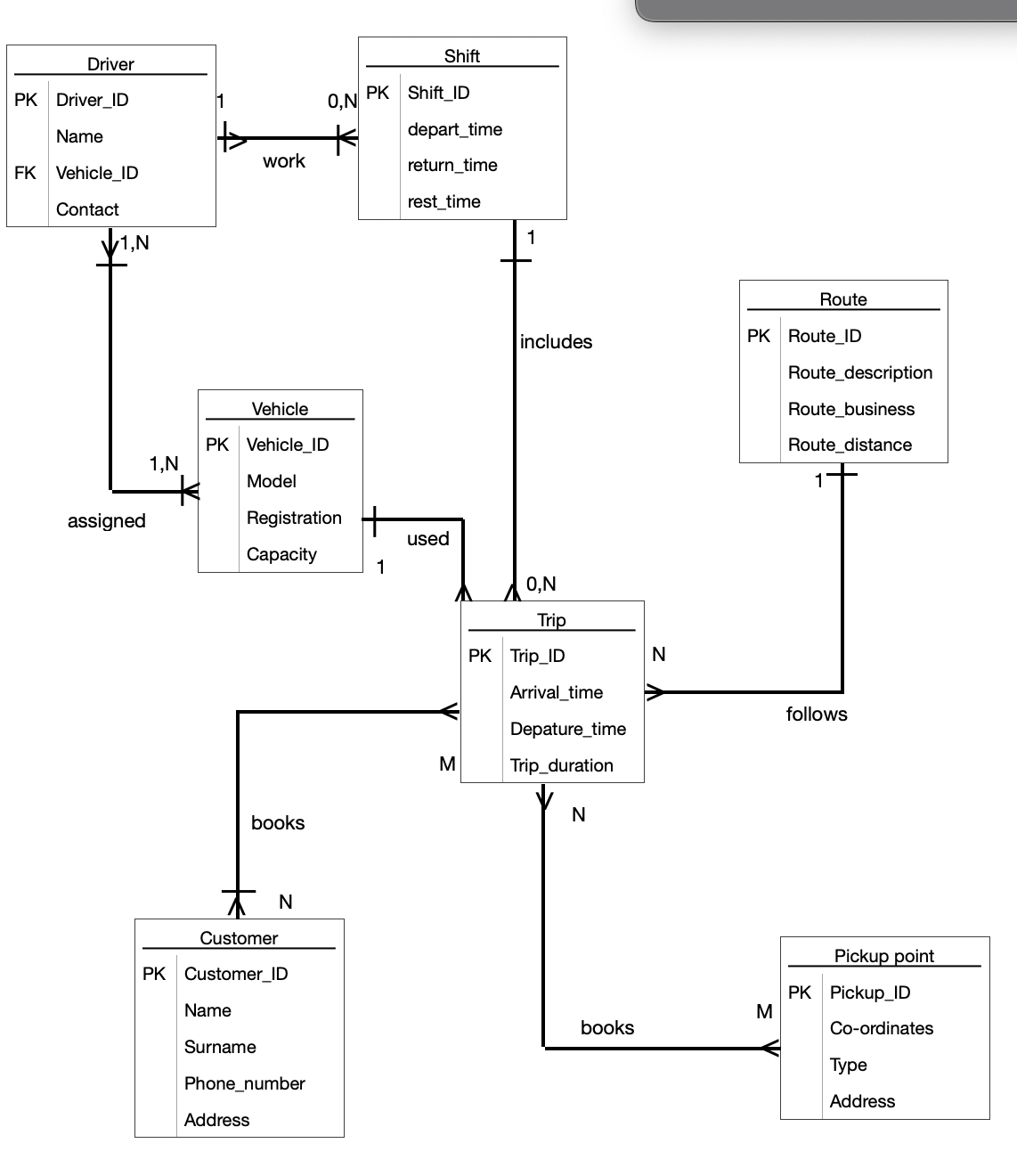
Transcribed Image Text:Driver
PK Driver_ID
Name
FK Vehicle_ID
Contact
1,N
assigned
1,N
work
Vehicle
PK Vehicle ID
Model
Registration
Capacity
books
Name
Surname
Customer
PK Customer_ID
Address
N
O,N
K
Phone_number
Shift
PK Shift_ID
1
depart_time
return_time
rest_time
used
M
includes
O,N
Trip
PK Trip_ID
Arrival time
Depature_time
Trip_duration
N
books
N
Route
PK Route_ID
M
Route_description
Route_business
Route distance
follows
Pickup point
PK Pickup_ID
Co-ordinates
Type
Address
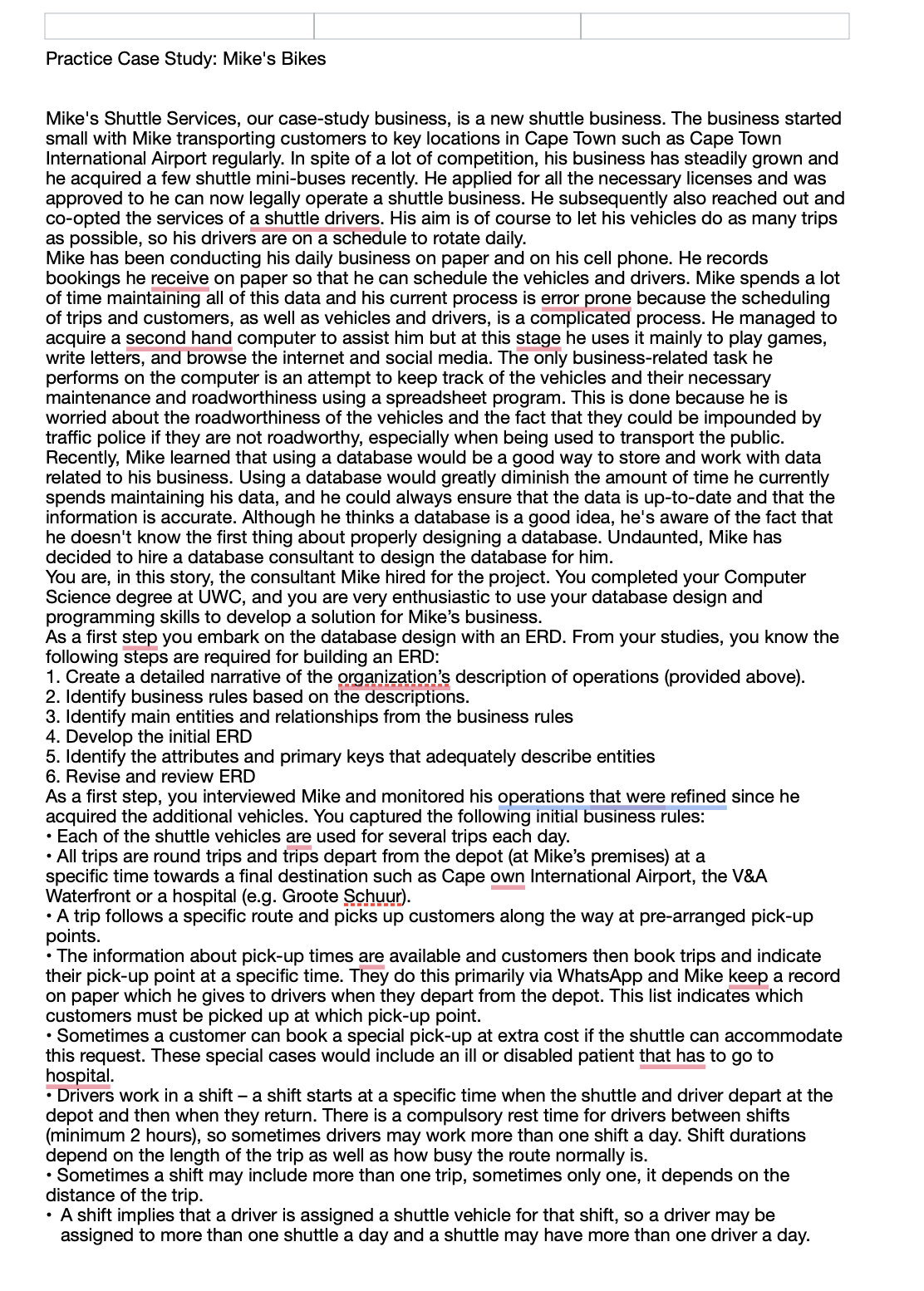
Transcribed Image Text:Practice Case Study: Mike's Bikes
Mike's Shuttle Services, our case-study business, is a new shuttle business. The business started
small with Mike transporting customers to key locations in Cape Town such as Cape Town
International Airport regularly. In spite of a lot of competition, his business has steadily grown and
he acquired a few shuttle mini-buses recently. He applied for all the necessary licenses and was
approved to he can now legally operate a shuttle business. He subsequently also reached out and
co-opted the services of a shuttle drivers. His aim is of course to let his vehicles do as many trips
as possible, so his drivers are on a schedule to rotate daily.
Mike has been conducting his daily business on paper and on his cell phone. He records
bookings he receive on paper so that he can schedule the vehicles and drivers. Mike spends a lot
of time maintaining all of this data and his current process is error prone because the scheduling
of trips and customers, as well as vehicles and drivers, is a complicated process. He managed to
acquire a second hand computer to assist him but at this stage he uses it mainly to play games,
write letters, and browse the internet and social media. The only business-related task he
performs on the computer is an attempt to keep track of the vehicles and their necessary
maintenance and roadworthiness using a spreadsheet program. This is done because he is
worried about the roadworthiness of the vehicles and the fact that they could be impounded by
traffic police if they are not roadworthy, especially when being used to transport the public.
Recently, Mike learned that using a database would be a good way to store and work with data
related to his business. Using a database would greatly diminish the amount of time he currently
spends maintaining his data, and he could always ensure that the data is up-to-date and that the
information is accurate. Although he thinks a database is a good idea, he's aware of the fact that
he doesn't know the first thing about properly designing a database. Undaunted, Mike has
decided to hire a database consultant to design the database for him.
You are, in this story, the consultant Mike hired for the project. You completed your Computer
Science degree at UWC, and you are very enthusiastic to use your database design and
programming skills to develop a solution for Mike's business.
As a first step you embark on the database design with an ERD. From your studies, you know the
following steps are required for building an ERD:
1. Create a detailed narrative of the organization's description of operations (provided above).
2. Identify business rules based on the descriptions.
3. Identify main entities and relationships from the business rules
4. Develop the initial ERD
5. Identify the attributes and primary keys that adequately describe entities
6. Revise and review ERD
As a first step, you interviewed Mike and monitored his operations that were refined since he
acquired the additional vehicles. You captured the following initial business rules:
• Each of the shuttle vehicles are used for several trips each day.
• All trips are round trips and trips depart from the depot (at Mike's premises) at a
specific time towards a final destination such as Cape own International Airport, the V&A
Waterfront or a hospital (e.g. Groote Schuur).
• A trip follows a specific route and picks up customers along the way at pre-arranged pick-up
points.
• The information about pick-up times are available and customers then book trips and indicate
their pick-up point at a specific time. They do this primarily via WhatsApp and Mike keep a record
on paper which he gives to drivers when they depart from the depot. This list indicates which
customers must be picked up at which pick-up point.
• Sometimes a customer can book a special pick-up at extra cost if the shuttle can accommodate
this request. These special cases would include an ill or disabled patient that has to go to
hospital.
• Drivers work in a shift - a shift starts at a specific time when the shuttle and driver depart at the
depot and then when they return. There is a compulsory rest time for drivers between shifts
(minimum 2 hours), so sometimes drivers may work more than one shift a day. Shift durations
depend on the length of the trip as well as how busy the route normally is.
• Sometimes a shift may include more than one trip, sometimes only one, it depends on the
distance of the trip.
• A shift implies that a driver is assigned a shuttle vehicle for that shift, so a driver may be
assigned to more than one shuttle a day and a shuttle may have more than one driver a day.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage