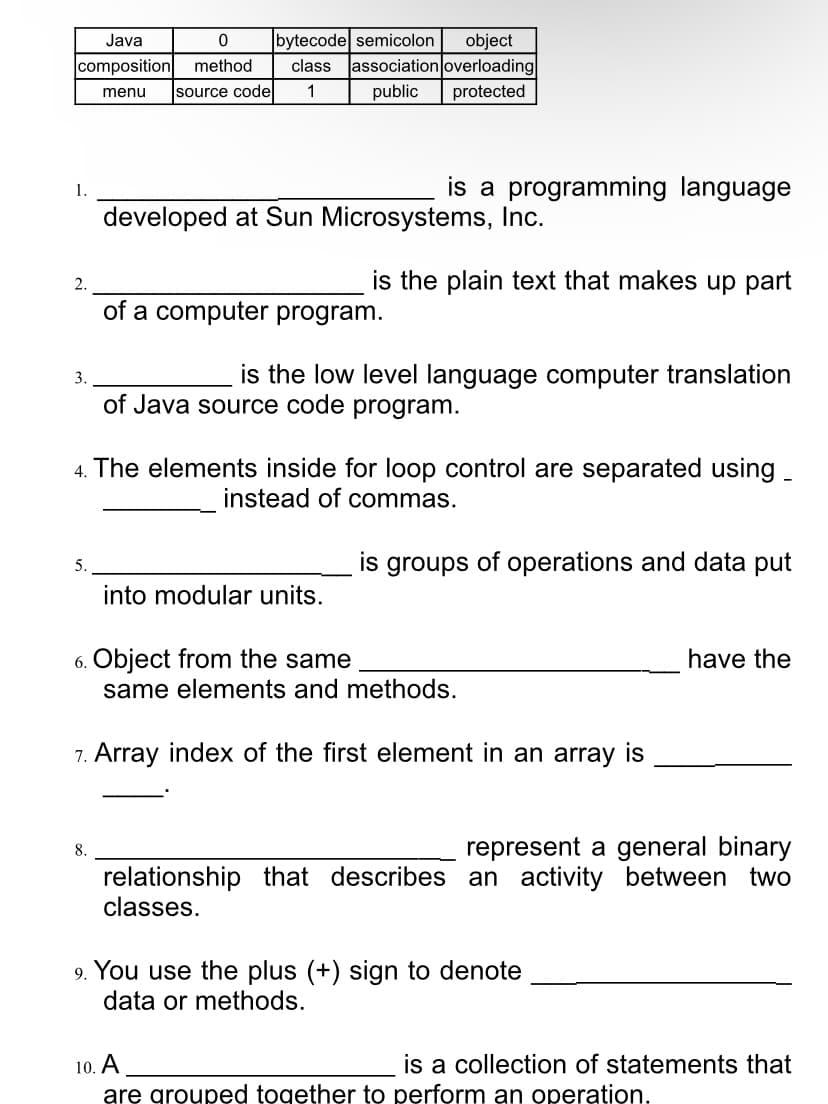
Java bytecode semicolon object class association overloading public composition method menu source code 1 protected is a programming language 1. developed at Sun Microsystems, Inc.
Q: What exactly is metadata? What exactly is metadata in the context of a result set? When is it…
A: Introduction: The term "metadata" refers to information that describes other information. In…
Q: Write only method to delete specific element from 1D array (named : list - with size n) if it found…
A: As per answering guidelines solving the first question completely.
Q: Is or can any of the business be put up as a SaaS?
A: Disclaimer: “Since you have asked multiple questions, we will solve the first question for you. If…
Q: What are the two most common types of software?
A: Software is a set of instructions that tells a machine how to do certain tasks. This is in contrast…
Q: Discuss which of the several Process flow models encourages more engagement with customers and…
A: In a software process model, The software development process is abstracted. Models Specified the…
Q: Explain the flow of this program ? def new_game(): guesses = [] correct_guesses = 0…
A: The given code is a quiz application where the program displays 4 questions one by one with its…
Q: 1. Write an assembly program to perform unsigned division of: A. Byte (210) over byte (50) B. Word…
A: The Answer is in below Steps
Q: Describe the signal pattern produced on the medium by the Manchester-encoded preamble of the IEEE…
A: The answer as given below:
Q: Assume you work on a network project for "x" company. Discuss the concept of non-repudiation as it…
A: introduction: Non-repudiation, which essentially means that someone cannot falsely deny that they…
Q: In what ways are standards bodies vital for networking, and how should a department ensure that…
A: The significance of network standardization organizations Standards ensure that the service supplied…
Q: Computer science What are the technologies used for Successful virtual environments.
A: Introduction: Trust, attention, and communication are three elements that all effective virtual…
Q: What techniques does a social engineering hacker employ in order to obtain knowledge about a user's…
A: Social engineering: Social engineering is the strategy for influencing people's psychology in order…
Q: low does Excel represent internally the values we see on a spreadsheet? Da) All of the values are…
A: As per our company guide lines we are supposed to answer only one parts, please send other parts aa…
Q: Explain why combining ethnography and prototyping is beneficial for requirements elicitation.
A: Introduction: Prototyping: When introduced at the right moment, screen mockups can help with…
Q: FAA Case Question: Why will it take several years for FAA to convert to new hardware and software?
A: FAA regulate the new approaches in the system by adopting new hardware as well as software, where…
Q: Computer science What exactly is the significance of linux partitioning?
A: Introduction: The practice of dividing a hard drive into different partitions using partition…
Q: Explain what causes a system to become stuck in a stalemate.
A: A database management system (DBMS), such as SQL Server, relies on the timeliness of file input and…
Q: What problems do you think can arise in extreme programming teams when many management decisions are…
A: Introduction: Extreme Programming (XP) is an agile software development approach that attempts to…
Q: Computer science In terms of user interface design, what does mapping imply?
A: Introduction: Mapping is a method of bridging the gap between the demands of users or consumers and…
Q: What are the two operating system modes, as well as the two fundamental functions of an operating…
A: Operating system has different modes of operation and the main functionality of operating system.…
Q: All of the terms subnet, prefix, and BGP route must be defined and compared.
A: Intro Subnet: A subnet is a segment of the main network. Subnetting is the process of splitting a…
Q: If the following sequence of operations takes place on an initially empty stack: push (8) -> pop ->…
A:
Q: Examine the role of women in the information technology industry and explain any three current…
A: Introduction: Given question has asked to examine the role of women in IT industry and also to…
Q: Discuss how selecting the pivot and the cut-off value affects the quicksort's performance.
A: Pivot The pivot value is the value that is chosen to partition the array into sub-arrays. Now,…
Q: 6. If the starting address location changes, in which of the following cases, the program has to be…
A: D compile time binding is the correct option Explanation:- Because compile time binding describe…
Q: Recognize and categorize the data on your computer or personal digital assistant. What information…
A: Information: Information stored on a personal computer may be of several types. The data…
Q: Give an example of memory protection.
A: Introduction of Memory protection: Memory protection is used for security reasons to control the…
Q: What are the most serious threats to the organization's data?
A: Threats The risk of an inadvertent or malicious computer security breach, the lack of secrecy,…
Q: associates belongs 1..1 Branch Staff Customer 1.. 0.1 1.. From this model, is it always possible to…
A: Explanation: 1.There are 3 entities present in the given diagram. The first one is the branch that…
Q: In java Write a method public static ArrayList merge(ArrayList a, ArrayList b) that merges one…
A: ALGORITHM:- 1. Declare and initialise 2 integer arraylists. 2. Pass them to the merge() method. 3.…
Q: 1. What is the meaning of Computer Vision? Is there a difference between Computer Vision and…
A: According to our guidelines, we are allowed to solve only the first question. Please post the other…
Q: Explain what causes a system to become stuck in a stalemate.
A: Justification: A stalemate occurs in the game of chess when the player whose turn it is to move is…
Q: What is the most important goal of normaliz the process of normalization?
A: Normalization is a procedure for getting sorted out data in a database. It is critical that a…
Q: Surpreeth wishes to add two more client entries to the customer table. Which command is used to do…
A: Intro We are given a situation in a database table where we are going to apply SQL command to add…
Q: Without using (SUB) instruction, write an assembly program to compute W from the following equation:…
A: the solution is an given below :
Q: Describe the processes required to get a fresh new computer ready for use.
A: Intro Preparing a brand new computer focuses on the performance and the infrastructure of the…
Q: Question: Draw horizontal partitioning of student portal (any of 3 functionalities) Question:…
A: There are two types of partitioning operations or two ways to partition a table: Horizontal…
Q: with the aid of a diagram illustrate the differences between a model and a diagram
A: Model - It is a 3-d representation of product. It is easy to build model before actual product to…
Q: The number of general-purpose processors does not need to be specified when categorising computer…
A: Introduction: Based on their computer architecture, computer systems are classified into the…
Q: 1. Explain the meanings of the words "Software Requirements and Specifications" and "Software…
A: Intro: 1. Explain the meanings of the words "Software Requirements and Specifications" and "Software…
Q: In modern cryptography, what is Perfect Security?
A: Introduction: The perfect security in modern cryptography is one-time pad, commonly known as OTP,…
Q: B/ what is the general formula for each expression? 1-linear spacing. 2- rand function. 3- subplot.
A: Please refer below for your reference: According to the guidelines of company we are restricted to…
Q: MOV M,C STA 2000H IDAY D
A: In 8085 Instruction set, this instruction MOV M, r will copy 8-bit value from the register r to the…
Q: System administrators are well-versed in the systems they oversee. What are the essential skills for…
A: Introduction: System administrators have two key responsibilities: problem solving and problem…
Q: Give this program a unique name and suitable background story/premise ? def new_game():…
A: The above code is of quiz game in which there are certain questions and each question has 4 options…
Q: Converting an offline firm to an internet business (in any industry or area). You must plan…
A: Thus, a systems methodology is primarily a process that incorporates system-scientific approaches,…
Q: For database professionals, normalization is a critical topic. It is useful for creating, situation…
A: Introduction Normalization is the process of organizing data in a database that includes creating…
Q: An airline company wanted a system that could dynamically package hotels and other ground products…
A: Introduction: The Pareto Principle is nearly ubiquitous in application. The revenues from 20% of…
Q: Write an application that accepts from the user the wholesale cost of an item and its markup…
A: The above code in C# is provided below:
Q: plot of y(t) -1 -2 -3 -4 -2 4
A: From the given graph, we can get the data points for plotting. Code: t=[-3 -2 -2 0 0 1 1 4 4 5];…
Step by step
Solved in 2 steps

- text1 = """ Python is an amazing programming language. It is also one of the primary languages in the data analysis field""" text2 = "Python is a genus of constricting snakes in the Pythonidae family. You can find amazing pictures of python snakes in this link" try: ifsorted(get_common_words(text1, text2)) == sorted(['amazing', 'of', 'the', 'is', 'python', 'in']): score['question 10'] = 'pass' else: score['question 10'] = 'fail' except: score['question 10'] = 'fail' get_common_words(text1, text2)C++ Language: write code. and algorithm or related theory of the following question. Give secreenshoots. Narrative 2: We need to have a generic module which reads in file and gives the output in the format which would facilitate other programs to do comparison like the one we saw above to carry out analysis and comparison. Response Required: Write a program that reads a given text, outputs the text as is, and also prints the number of lines and the number of times each letter appears in the text. An uppercase letter and a lowercase letter are treated as being the same; that is, they are tallied together. Since there are 26 letters, we use an array of 26 components to perform the letter count. We also need a variable to store the line count. The text is stored in a file, which we will call textin.txt. The output will be stored in a file, which we will call textout.txt Input: A file containing the text to be processed. Output: A file containing the text, number of lines, and the number…09.Text:Python Programming You are given an exhibit an of length N and Q inquiries. Each question is portrayed by a couple of whole numbers, I and r. Answer each inquiry with the accompanying: assuming we take each aftereffect of the components with lists among 1 and r (comprehensive) and record their items, what will be the littlest missing positive number? Input • The primary line of the information contains a solitary number T signifying the quantity of experiments. The portrayal of T experiments follows. The primary line of each experiment contains two space-isolated numbers N and Q. The subsequent line contains N space-isolated numbers a1, a2,..., an. Every one of the following Q lines contains two space-isolated numbers, I and r, meaning the question's reach. . Yield For each question, yield the littlest missing aftereffect item on a new.
- Python please You got one pizza with sausage that has been sliced into a few pieces. The list of sausage count specifies how many slices of sausage are in each piece. You start cutting the pizza into n + 1 pieces since you want to distribute it with your n buddies. Each component is made up of one or more successive portions. You generously choose to eat the portion that contains the fewest overall slices of sausage. Find the most sausage slices you can have overall. Input # of people; list of (#number of sausage) on the cunks for example: Output print the maximum number of sausage you can have. Example: 9;8,1,4,5,7,8,9,10,3,3,4,6,7,8,8,8,4,3,4,9,9,9,4,6,5,7,8 Print: 15Computer Science Write in Javascript please and use high order functions liek map or filter or reduce let obj = [ { mode: "hot" }, { temp: "low" }, { mode: "cold } ] I want to create a function that get object by key such as: myFunc("mode"); returns { mode: "hot" } next call of myFunc("mode") returns { mode: "coldFormat Requirement Algorithms in pseudo code MUST be placed in code blocks/fences, and use either the cpp or java syntax highlighter. Algorithms should follow the pseudo code standard described in handout 1. Your pseudo code should be placed in a code block, for example Algorithm alg_name(a, b) { // A description of the algorithm // input: a - a positive decimal integer; b - an integer // ouput: the sum of a and b c = a + b // or, c <- a + b return c } Do NOT change the template except the answer portion. Formulas and equations should be in math mode using Latex math symbols. Markdown math tutorial: http://tug.ctan.org/info/undergradmath/undergradmath.pdf Ways enter into the math mode in Notion: https://www.notion.so/help/math-equations
- Bishops on a binge def safe_squares_bishops(n, bishops): A generalized n-by-n chessboard has been taken over by some bishops, each represented as a tuple (row, column) of the row and the column of the square the bishop stands on. Same as in the earlier version of this problem with rampaging rooks, the rows and columns are numbered from 0 to n - 1. Unlike a chess rook whose moves are axis-aligned, a chess bishop covers all squares that are on the same diagonal with that bishop arbitrarily far into any of the four diagonal compass directions. Given the board size n and the list of bishops on that board, count the number of safe squares that are not covered by any bishop. To determine whether two squares (r1, c1) and (r2, c2) are reachable from each other in one diagonal move, use abs(r1-r2) == abs(c1-c2) to check whether the horizontal distance between those squares equals their vertical distance, which is both necessary and sufficient for the squares to lie on the same diagonal. This…Course: Data Structure and Algorithms: Language: Java Please solve problem completely according to requirement, program should must be follow all the rules of menu base system which are required and write in question: Attach the output's screentshots and explain every line with comments: Whole code should be user defined inputs not same like exmple: Task 2: (Stacks): Make a program fro Stack ising java which should evaluate the algebraic expresions.Evaluation of Algebraic Expression: Your program will take an infix algebraic expression as an input from user. It will check that whether it is a valid expression or not. Then It will be converted into postfixexpression, and at the end it will be evaluated and print the result of the expression.For example:if input is: (3+5)*(7 output: it is invalid. If input is: (3+5)*7 , displayPostfix form: 35+7*Answer: 56JAVA INTELLIJ Design an experiment to compare the Selection, Insert, and Bubble Sort Algorithms. Comments in code please so I understand! Thanks :) Come up with a collection of questions that pertain to comparing algorithms. (i.e. How do they compare with small groups of data, large groups of data, semi-sorted data , data in a small range, data in a large range, etc). After that, design, code, and run the experiment. **PLEASE WRITE SEPERATE PARAGRAPH WITH ANSWERED QUESTIONS** Lastly, a writeup explaining what you did, your results (what the experiment yielded), and your conslusions (how you interpret them). The following questions need to be addressed: – What questions were you looking at? – How you decided to look at them? – What did you do? – What were the results? – What are your conclusions?
- Course: Data Structure and Algorithms: Language: Java Resolve the errors from the guuven code and made this programe run able: Programe is for to solve the algebric expression using stack in java: Attach the output's screentshots and explain every line with comments: import java.util.Arrays;import java.util.Scanner;import java.util.HashSet;import java.util.StringTokenizer; public class ArithmeticExpressionInfix { public static String evaluate(String inputAlgebraicExpression){ inputAlgebraicExpression = inputAlgebraicExpression.replaceAll("\\s+", ""); GenericStack<String> stack = new GenericStack<String>(inputAlgebraicExpression.length()); StringTokenizer tokens = new StringTokenizer(inputAlgebraicExpression, "{}()*/+-", true); while(tokens.hasMoreTokens()){ String tkn = tokens.nextToken(); if(tkn.equals("(") || tkn.equals("{") || tkn.matches("[0-9]+") ||…InClass Exercise Task01 (V1.0)Requested files: Inclass_Task01.java ( Download)Type of work: Individual workThe Namibia University of Science and Technology would like to introduce an automated student number and email generation system. The system takes into consideration the following: a) To generate the student number it takes three letters(the first, middle and last letter) of the student’s surname and adds it to the first three letters from the first name, then finally adds a three digit postfix number. b) To generate the email is quite easy it just takes the first letter from the first name and adds it to the surname , then it adds the @students.nust.na postfix Your task is to create a program that can achieve the above requirements when given the students surname, first name and three digit postfix through CMD arguements Sample run 1: java InClass01_task01 Kandjeke Jenifer 003 Output: Good day Jenifer welcome to NUST. Your email address is : jkandjeke@students.nust.na Student…neural networks Program to generate random numbers from 11 to 21 as class 1 and generate random numbers from 9 to 55 as class append them to the lists. Take 8 data in each list and plot it.

