Java Write an application that inputs five numbers, each between 10 and 100, inclusive. As each number is read, display it only if it’s not a duplicate of a number already read. Provide for the “worst case,” in which all five numbers are different. Use the smallest possible array to solve this problem. Display the
Java Write an application that inputs five numbers, each between 10 and 100, inclusive. As each number is read, display it only if it’s not a duplicate of a number already read. Provide for the “worst case,” in which all five numbers are different. Use the smallest possible array to solve this problem. Display the
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter10: Classes And Data Abstraction
Section: Chapter Questions
Problem 22PE
Related questions
Question
In Java Write an application that inputs five numbers, each between 10 and 100, inclusive. As each number is read, display it only if it’s not a duplicate of a number already read. Provide for the “worst case,” in which all five numbers are different. Use the smallest possible array to solve this problem. Display the complete set of unique values input after the user enters each new value.
Rough output in screenshot
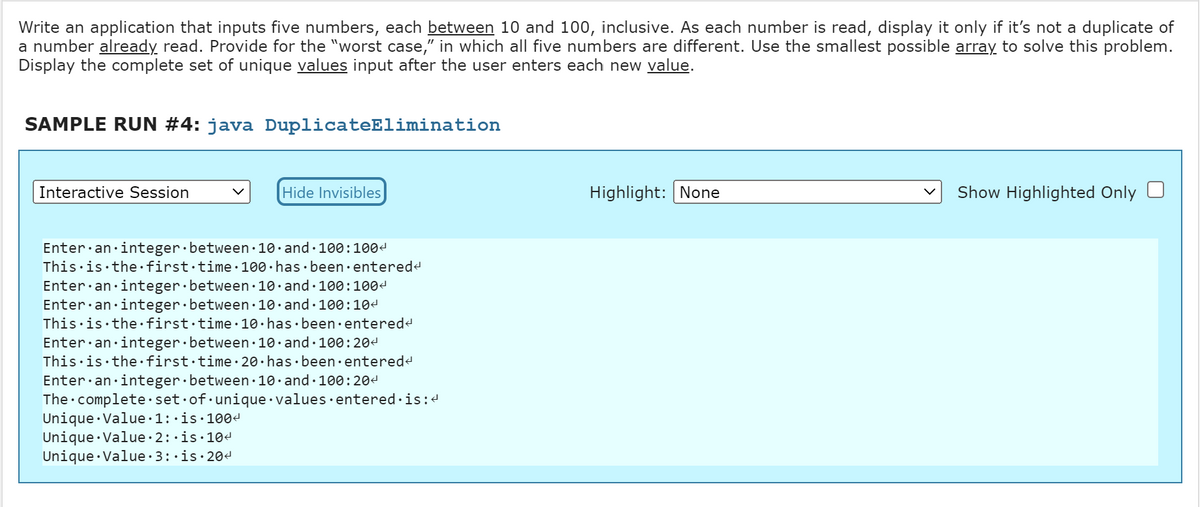
Transcribed Image Text:Write an application that inputs five numbers, each between 10 and 100, inclusive. As each number is read, display it only if it's not a duplicate of
a number already read. Provide for the "worst case," in which all five numbers are different. Use the smallest possible array to solve this problem.
Display the complete set of unique values input after the user enters each new value.
SAMPLE RUN #4: java DuplicateElimination
Interactive Session
Hide Invisibles
Enter an integer between 10 and 100:1004
This is the first time 100 has been entered<
Enter an integer between 10 and 100:100<
Enter an integer between 10 and 100:10<
This is the first time. 10 has been entered<
Enter an integer between 10 and 100:20<
This is the first time 20 has been entered<
Enter an integer between 10 and 100:204
The complete set of unique values entered is:<
Unique Value 1:.is.100<
Unique Value. 2:.is.10<
Unique Value 3:.is.20<
Highlight: None
Show Highlighted Only
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning