C++ Only: Karan has N items in his store (numbered 1 to N); And in i Each valid (1 <= I<= N). the weight of the i th object is Wi. As Chef is very sensitive to nature. Karan wants to arrange all the weights on one side and the weights on the other side. Karan can arrange two dependent items with the help of an exchange during a single operation. Karan needs the minimum working number required to set the All-Equal weight item on one side and the All-Odd Weights on the other. Karan cannot solve this problem so he asks you to solve it. Help Chef solve this problem.
C++ Only: Karan has N items in his store (numbered 1 to N); And in i Each valid (1 <= I<= N). the weight of the i th object is Wi. As Chef is very sensitive to nature. Karan wants to arrange all the weights on one side and the weights on the other side. Karan can arrange two dependent items with the help of an exchange during a single operation. Karan needs the minimum working number required to set the All-Equal weight item on one side and the All-Odd Weights on the other. Karan cannot solve this problem so he asks you to solve it. Help Chef solve this problem.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter10: Classes And Data Abstraction
Section: Chapter Questions
Problem 19PE
Related questions
Question
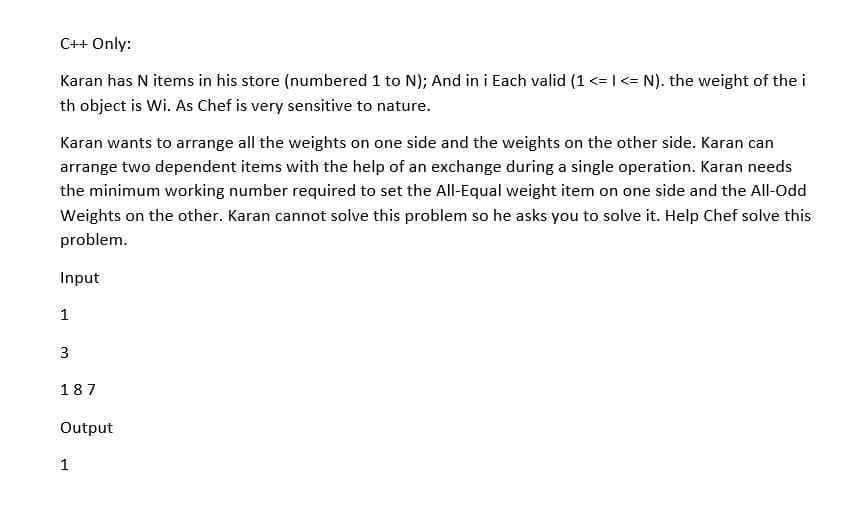
Transcribed Image Text:C++ Only:
Karan has N items in his store (numbered 1 to N); And in i Each valid (1 <= I<= N). the weight of the i
th object is Wi. As Chef is very sensitive to nature.
Karan wants to arrange all the weights on one side and the weights on the other side. Karan can
arrange two dependent items with the help of an exchange during a single operation. Karan needs
the minimum working number required to set the All-Equal weight item on one side and the All-Odd
Weights on the other. Karan cannot solve this problem so he asks you to solve it. Help Chef solve this
problem.
Input
1
3
187
Output
1
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning