Let C be the code given by the matrix Suppose x = (11010) and y = H = /0 1 1 1 00 0 10 1 0 0 0 1 0/ (10110) are received. Determine if either x or y is a codeword?
Q: Using no more than five words, please explain how the instruction set interacted with the data and…
A: A detailed plan consisting of: The Detailed Instructions Instruction set is also sometimes referred…
Q: What are the names of the five levels that make up the Internet Protocol stack? What are the primary…
A: Answer:
Q: Many talented engineers around the world want to contribute to his project. The re-discharge flows…
A: Algorithm: The first line of the input contains a single integer TT denoting the number of test…
Q: How can I make a page seem the same in different versions of the same programme, such as NS and…
A: How Do I Make A Page Look The Same In Different Browsers? You cannot and should not waste time…
Q: What exactly is the connection between machine language and assembly language?
A: Machine Language and Assembly Language: The term "assembly language" refers to a kind of low-level…
Q: Use Java Programming Language Write a GUI to calculate the number of servings that a circular pizza…
A: import java.awt.Color;import java.awt.Font;import java.awt.Frame;import java.awt.GridLayout;import…
Q: Recognize the benefits and drawbacks of today's networked world.
A: Networked world: Students from several nations work together on a scientific project over the World…
Q: vances in artificial intelligence that have been made so far, speculate about the technology's…
A: SUMMARY“Artificial Intelligence (AI) will change the world further than anything differently in…
Q: Suppose you decide to use P(x)= x18+x7+1 for an m-sequence PRNG. a) What is the cycle length? b) How…
A: Pseudo Random Number Generator(PRNG) refers to an algorithm that uses mathematical formulas to…
Q: What distinguishes vertical microcode from horizontal microcode is its vertical orientation.
A: Definition: Microcode is a notion in processor design that adds an organisational layer between the…
Q: Defining Question-Answering in AI and demonstrating how it relates to Natural Language Processing is…
A: I offered a resolution: Data recovery originally included question answering, but it has now grown…
Q: What are the three different kinds of page layouts that CSS supports?
A: Please find the detailed answer in the following steps.
Q: Question 4. Consider the language L over the alphabet (a, b, c, d } such that L = {abcd:n> 0, m>0}.…
A: Given: L = {anbncmdm : n > 0, m>0} We have to develop CFG for the language L.
Q: Determines the maximum speed at which instructions may be carried out.
A: Execution of instructions: Execution time is the overall time a CPU spends processing a specific…
Q: # function that finds factor def factors(n): print("Factors of",n,"are:") for i in range(1, n + 1):…
A:
Q: Explain in detail the various security risks, and elaborate on why some of them are specific to…
A: The three most common WLAN security threats include: denial of service attacks - where the intruder…
Q: What influence will AI have in the future? What software based on artificial intelligence is…
A: The above question that is influence will in ai have in the future and what software based on…
Q: A process may be terminated in several ways, but what exactly does it imply when it does?
A: Inspection: This question provides an explanation as to what it signifies when a process is…
Q: # Write a C program in code blocks to find the sum of digits of a given number using recursion.…
A: The program is written in step 2
Q: 3. () Apply Warshall's algorithm to find transitive closure of the following digraph. Give its…
A:
Q: (4) Elgamal public key cryptosystem (encryption): Start with the prime p = 29 and the primitive root…
A: The ElGamal encryption is based on the Diffie-Hellman Key Exchange method. It uses the same domain…
Q: When and why would one choose to use the time-sharing processing method rather than the batch…
A: Batch processing is a method for automating and processing multiple transactions collectively. Batch…
Q: You have been tasked, in your capacity as a network administrator, to set up a brand-new computer…
A: Second-stage network management involves setup and configuration. This involves configuring files,…
Q: Airplane Records Write a program to keep data and perform statistical analysis for a set of 4…
A: Using Array : #include <iostream>using namespace std; //structure of Passengerstruct…
Q: What exactly does it imply when people talk about cascading style sheets? Where does CSS rank in…
A: What exactly does it imply when people talk about cascading style sheets? Cascading Style Sheets is…
Q: Under what circumstances are threads running at the user level preferable to those running at the…
A: An execution flow across the process code is referred to as a thread. It has its program counter to…
Q: Is there ever a situation in which using threads at the user level is preferable than using threads…
A: The Answer start from step-2.
Q: Explain in detail the various security risks, and elaborate on why some of them are specific to…
A: Threats to information security may be take various forms, including software assaults, the theft…
Q: Write a program to help them analyze their data. Your program must contain parallel arrays: an array…
A: Introduction: In this question, we are asked to create two array, 1st is 1D and 2nd is 2D In 1st…
Q: Is it possible to make CFG for infix and postfix expression using derivation tree?? a. Yes b. No…
A: HI THERE,I AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: In light of the advances in artificial intelligence that have been made so far, speculate about the…
A: Artificial intelligence - (AI) is the ability of a computer or a robot controlled by a computer to…
Q: can you type the naswer i don't understand the hand writing. Thank you.
A: Typed Answer: Depending on the value of T there will be different-different Gantt chart, waiting…
Q: Given: 13-Node Graph O 75 ΑΠ 118 T Z M to B-241 O to B-380 P to B-100 RV to B-193 140 S to B-253 T…
A: Please refer below for your reference: The A* algorithm helps us in searching for the shortest path…
Q: Is there ever a situation in which using threads at the user level is preferable than using threads…
A: Answer:
Q: analysing
A: In the current digital era, when social media platforms and online business assets frequently power…
Q: The characteristic that is present on the majority of controls determines, at run time, whether or…
A: GUI programming: An user interface for a graphics-based operating system that facilitates…
Q: When you open a new Visual C# project in the Designer, what is automatically generated and…
A: The solution to the given question is: When a new project is started in a Visual C# project , Visual…
Q: Explain in an easy-to-understand way the primary differences between multiprogrammed batch…
A: Answer:
Q: How do you determine whether a problem in one application is being caused by a problem in another…
A: Start: Take a look at a programme that is now being executed by Microsoft Office. A problem with…
Q: What are the stages that must be traversed before an instruction may be carried out? Give a quick…
A: Before instruction needs to carried out, there are several stages to traverse.
Q: In order to explain or understand the information that a prediction model provides, what approaches…
A: Prediction Model: A popular statistical method for forecasting behaviour is predictive modelling.…
Q: To What Advantages Does the Use of CSS Lead?
A: Given: The advantages of using CSS are then CSS reduces time CSS may be created once and used in…
Q: The mapping f: R → R, f(x) = x2, which of the following are correct? f is one-to-one. f is not a…
A:
Q: b. Use the double colon operator to create a row array with the next values [1000,995,990,...,10]
A: Due to company policies I am compelled to solve only one question and that is the first question.…
Q: what is the correct code to get the Hello World printed?
A: Correct Code is: <!DOCTYPE html> <html> <head> Print Hello World! </head>…
Q: Create a Java program that detects whether the mouse is clicked inside or outside a circle. The…
A: We need to use the MouseListener class and the paint method) to draw a circle and show the result…
Q: What are the three different kinds of page layouts that CSS supports?
A: CSS stands for the cascading style sheets . It is the designing framework use to develop the…
Q: "Java Virtual Machine" refers to what?
A: Java Virtual Machine (JVM) is a machine that provides the runtime environment to drive the java code…
Q: GSM time slot is 577 s (microseconds) in duration and includes far more than a snapshot of each…
A: The answer is
Q: Investigate the Foursome of Cortez (in software development). What was the impact of GoF on Java…
A: Designing object-oriented software is hard, and designing reusable…
Help transposing the matrix in number 6 to figure out which is the codeword
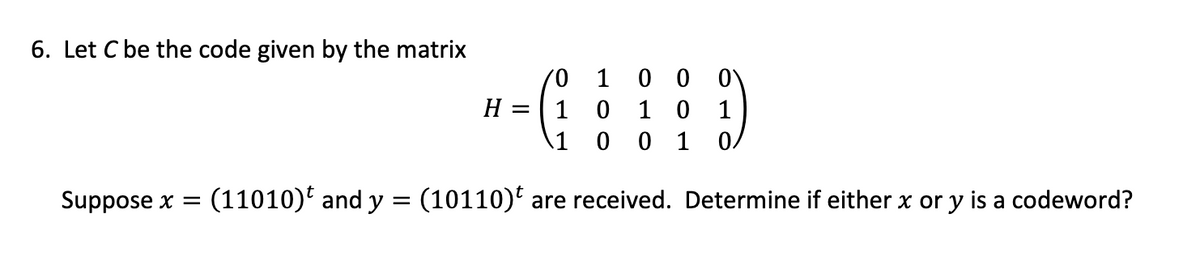
Step by step
Solved in 2 steps

- Give answer of both subparts. (Don't use AI)A list of positive and negative numbers are in A2 through A400, and the square root of the absolute value is needed for each cell. Which function typed into B2 and copied through B400 will provide this information? a. =A2^(1/2) b. =SQRT(A2) c. =SQRT(ABS(A$2)) d. =SQRT(ABS(A2))Consider the following code which includes a parity check for the third digit: C=(000,011,101,110). You get the third digit by adding the first two and then using the remainder on division by 2. Can this code detect and count single errors? how can this be implemented?
- Let S = {x | x = 3n, n ∈ Z+}. Which of the following expression(s) is/are true?a. 3 ∈ S b. 3 + 6 ∈ S c. ∅ ⊂ S d. S ⊆ S e. 1 ∈ SGiven a number n, identify and print which in the given set of numbers are factors of n. Should there be no factors listed in the set of numbers, print "I'm alone". For example, given the number 36 and the set of numbers 2, 3, 5, 7, 12. Only print the numbers which are factors of 36, which are 2, 3, 12. Input The first line contains the number n; The second line contains how many numbers there are in the set of numbers; The third line contains the set of numbers. INPUT: 36 5 2·3·5·7·12 Output The set of numbers that are factors of n separated by a new line in order of appearance. If there are none, print "I'm alone" OUTPUT: 2 3 12Given the following declarations: int j = 50; int e[5] = {5,10,15,20,25}; int *x = e, *y; Suppose that the first element of e is stored at location D600, j is stored at location D664 and an integer takes up 4 bytes.
- Assume double[][] x = new double[2][5], what are x.length, and x[1].length?Let A denote the set of bit strings of length 5 that begins with 10 and B denote the set of bit strings of length 5 that terminate at 00. the number of elements in A∩B is ____An airline association assigns three-letter codes to represent airport locations. For example, the airport code for Clark, Pampanga, is CPP. Notice that repetition is allowed in forming this code. How many airport codes are possible?
- Please write in C program to print out a list of bit strings that can be created by using combination How many bit strings of length 12 containa) exactly three 1s?b) at most three 1s?c) at least three 1s?d) an equal number of 0s and 1s?Encryption is commonly used to disguise messageson the internet. A Caesar cipher performs a shift ofall of the characters in a string (based on their ASCIIvalues, see Table 2.1), e.g.h e l l o → m j q q tThe example shows a shift with a distance of 5characters, i.e. h(ASCII:104) → m(ASCII:109)Write a C/C++ program that asks the user to input aline of plaintext and the distance value and outputsan encrypted text using a Caesar cipher, with theASCII values range from 0 through 127. Useunderscores (ASCII: 95) to represent spacecharacters.Underscore characters should not be encrypted,and any character that is encrypted may notbecome an underscore. In this case, the charactershould be changed to the next character in theASCII table.The program should work for any printablecharacters.NB: No strings (datatype) or library functions maybe used.See Figure 2.1 for example output.What is the smallest 32-bit floating point number f such that 128+f>128 ? What is the smallest 32-bit floating point number g such that 1+g>1? What is the relation between f and g? Write a short C++ answer to support it.

