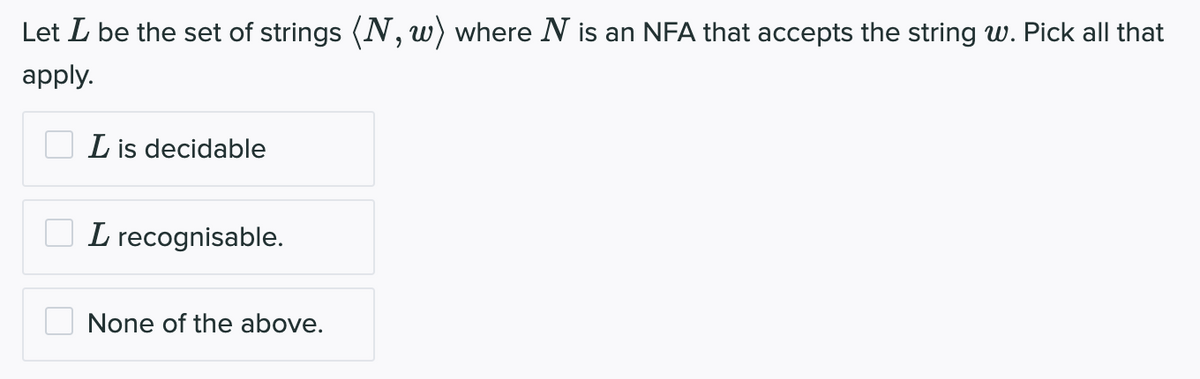
Let L be the set of strings (N, w) where N is an NFA that accepts the string w. Pick all that apply. L is decidable L recognisable. None of the above.
Q: An insurance business has asked the most efficient approach for allowing access to its systems.…
A: (INTRODUCTION) Access control: what is it? In essence, access control is a part of data security…
Q: Can you describe a biassed exponent and its potential utility?
A: The answer is given in the below step.
Q: modify the java program below to use try-catch logic to detect input errors and display an error…
A: Given code: import javax.swing.*; public class Main { public static void main(String[] args) {…
Q: doing out internet research The adventures of Mafiaboy When and how did he start hacking websites?…
A: Start: The FBI seized Mafiaboy while they were monitoring him after he made the assertion that he…
Q: How can you differentiate between the many types of computer networks? using a real-world example to…
A: Introduction Computer networking alludes to interconnected registering gadgets that can trade…
Q: acts several aspects of contemporary society. What are the primary pros and downs
A: Introduction: The internet has its own set of advantages and disadvantages; it can be extremely…
Q: Why is hashing passwords preferable than encrypting them?
A: Passwords Preferable: Experts advise using salt and a powerful, slow hashing algorithm like Argon2…
Q: Give examples of data manipulation, fraud, and web piracy.
A: DML is also known as data manipulation language.
Q: Do you think that error correction is more useful for wireless applications? Give instances to…
A: The process of identifying mistakes in sent communications and reassembling the original, error-free…
Q: Which regions and zones can assist in enhancing the robustness, performance, availability, and…
A: Please find the answer below :
Q: Why are functions essential in programming to begin with?
A: While writing programs you will use functions weather earlier or later, it's the need of…
Q: Object-oriented programming has a variety of characteristics. Answers that are duplicates will get…
A: Programming Methodology: A programming paradigm is a method of generating and implementing…
Q: Examine the many kinds of access control systems and how they vary. Identify the various types of…
A: Answer : The different kinds of access control systems are : Role based access control mandatory…
Q: What causes the gap between our law and our technology.
A: Technology and law are constantly in conflict with one another. The speed of technological…
Q: What does clustering mean in particular? What applications does it have for data mining?
A: The answer to the question is given below:
Q: What is a meteor with a long history?
A: A meteor that has been around for a significant amount of time is said to have a long history. It's…
Q: How Can You Use Locality to Your Advantage in Your Programs?
A: We have two different kinds of locales: Temporal and spatial localizationA resource that is…
Q: As part of your research, investigate cloud computing and social networking blogs in depth.
A: Given: Members of social networks may access shared resources from anywhere thanks to cloud…
Q: What are the two separate sorts of Internet-based services made accessible to mobile application…
A: Answer is
Q: How are sessions susceptible to being hijacked? Can anything be done to stop this from occurring?
A: Session Hijacking: IP spoofing, the most popular technique for session hijacking, involves an…
Q: Why is MATLAB the tool of choice when presented with a challenge in Computational Geometry?
A: Computational Geometry: The study of algorithms that may be expressed in terms of geometry is the…
Q: Is the security of the cloud endangered by a data breach? What more can you tell me about…
A: Breach of data: Session Hijacking is an attack that enables unauthorized access to authorized…
Q: Four functions to which do all routers contribute
A: Router: It is a piece of hardware in the network that moves data packets from one location to…
Q: Describe in further detail what a challenge–response authentication system is and how it operates.…
A: Authentication procedures known as challenge-response are used in computer security to safeguard…
Q: Is a process exception necessary, and if so, for what reason?
A: Introduction It is an issue that emerges during the execution of a program. A C++ exception is a…
Q: Detail the concept behind an authentication challenge–response system. What makes this system more…
A: Showing something to be true or authentic is the process or action of proving it is called…
Q: Describe some strategies for session theft. Can anything be done to stop this from occurring?
A: Session Hijacking is an attack that enables unauthorized access to authorized session connections:…
Q: Which Linux distribution formed the foundation of Ubuntu?
A: Ubuntu is based on Debian. Debian is developed by what is known as his Debian Project, a…
Q: You should brush up on your knowledge of social networking blogs in addition to cloud computing and…
A: DEFINITION Examples of social networking sites with blogs that provide data or information on…
Q: Internet is used for research purposes. Mafiaboy's activities How did he get access to the websites…
A: Mafiaboy Activities: He joined the earliest online hacker circles while he was a teenager. And in…
Q: This article outlines the pros and cons of global networking and cloud computing.
A: Internet of Things: With the use of the cloud computing technology, companies may provide their…
Q: Filter tools like sed and awk are frequently used in pipelines to prepare data. Is this statement…
A: - We have to verify the statement about filter tools like awk and sed.
Q: What do you think the four most crucial qualities are while creating software? Please share your…
A: The process of thinking of, defining, designing, programming, documenting, testing, and correcting…
Q: strongest rationale for shifting data to the cloud? What is your greatest security-related concern?
A: Introduction: Cloud computing refers to anything that involves providing hosted services over the…
Q: What kind of hard drive does Windows 7 prohibit defragmentation from occurring on?
A: The performance of your hard drive might significantly improve after defragmentation. Defragmenting…
Q: What are the most effective cloud-based data backup procedures?
A: You obviously need backups, if you ask the question. But it is advisable to create duplicates of…
Q: How can the numerous threats to a safe and trustworthy computer network be mitigated?
A: A set of computers connected form a computer network. Networking allows computers to connect…
Q: multi-user operating system that enables users to share time and resources. How well does this…
A: The following are the issues associated with process protection in a multiprogramming and…
Q: Do you feel that persons who are physically or mentally handicapped may benefit in some way from…
A: The TCP/IP protocol stack is used by the worldwide network of linked computer networks known as the…
Q: consider data backup and recovery from several
A: the solution is an given below :
Q: Is a process exception necessary, and if so, for what reason?
A: Introduction In this question we are asked that Is a process exception necessary, and if so, for…
Q: Where can I get additional information regarding compressed and encrypted Encrypting File System…
A: The Encrypting File System (EFS) which refers to on Microsoft Windows it is the feature that are…
Q: A select procedure in a relational database can shrink a table's size by deleting columns that don't…
A: Database: A database is a collection of data that is arranged for easy access and management. You…
Q: Comparing and contrasting the ideas of virtual memory and virtual machines is essential. How similar…
A: Virtual memory is an abstraction that gives to a programmer the illusion of having infinite memory…
Q: Discover the difficulties involved in developing a data architecture to support the new service.
A: Organizations encounter the following obstacles when they build their infrastructures: The financial…
Q: When is the optimal time to schedule a network upgrade?
A: Answer: We need to write the what is optimal time to take the update the schedule the network. in…
Q: methods for hijacking a session. Exist possible countermeasures to this onslaught, and if so, what…
A: Session Hijacking Session hijacking is basically a web attack that is carried out by destroying…
Q: What were some of the data security and privacy issues that made the Veterans Administration (VA)…
A: Answer:
Q: Peter wants to use the electrical plug to power his computer. Describe the steps your computer must…
A: To avoid the computer overheating: Set up the monitor and computer case on a desk or work surface…
Q: Please explain the pros and downsides of employing shared vs private L2 caches for single-threaded,…
A: Here we have given solution regarding pros and downsides of employing shared vs private L2 caches.…
Step by step
Solved in 2 steps

- def reverse_sentence(s: str) -> str:"""Given a sentence <s>, we define a word within <s> to be a continuoussequence of characters in <s> that starts with a capital letter andends before the next capital letter in the string or at the end ofthe string, whichever comes first. A word can include a mixture ofpunctuation and spaces.This means that in the string 'ATest string!', there are in fact only twowords: 'A' and 'Test string!'. Again, keep in mind that words start with acapital letter and continue until the next capital letter or the end of thestring, which is why we consider 'Test string!' as one word.This function will reverse each word found in the string, and return a newstring with the reversed words, as illustrated in the doctest below.>>> reverse_sentence('ATest string!')'A!gnirts tseT' """ do it on python, and do not use any list, import or split, or append or join.def reverse_sentence(s: str) -> str:"""Given a sentence <s>, we define a word within <s> to be a continuoussequence of characters in <s> that starts with a capital letter andends before the next capital letter in the string or at the end ofthe string, whichever comes first. A word can include a mixture ofpunctuation and spaces.This means that in the string 'ATest string!', there are in fact only twowords: 'A' and 'Test string!'. Again, keep in mind that words start with acapital letter and continue until the next capital letter or the end of thestring, which is why we consider 'Test string!' as one word.This function will reverse each word found in the string, and return a newstring with the reversed words, as illustrated in the doctest below.>>> reverse_sentence('watchNow')'watchwoN' >>> reverse_sentence('hot')'hot' """ do it on python, and do not use any list, import or split, or append or join.def reverse_sentence(s: str) -> str:"""Given a sentence <s>, we define a word within <s> to be a continuoussequence of characters in <s> that starts with a capital letter andends before the next capital letter in the string or at the end ofthe string, whichever comes first. A word can include a mixture ofpunctuation and spaces.This means that in the string 'ATest string!', there are in fact only twowords: 'A' and 'Test string!'. Again, keep in mind that words start with acapital letter and continue until the next capital letter or the end of thestring, which is why we consider 'Test string!' as one word.This function will reverse each word found in the string, and return a newstring with the reversed words, as illustrated in the doctest below.>>> reverse_sentence('ATest string!')'A!gnirts tseT'""" pass
- def reverse_sentence(s: str) -> str:"""Given a sentence <s>, we define a word within <s> to be a continuoussequence of characters in <s> that starts with a capital letter andends before the next capital letter in the string or at the end ofthe string, whichever comes first. A word can include a mixture ofpunctuation and spaces.This means that in the string 'ATest string!', there are in fact only twowords: 'A' and 'Test string!'. Again, keep in mind that words start with acapital letter and continue until the next capital letter or the end of thestring, which is why we consider 'Test string!' as one word.This function will reverse each word found in the string, and return a newstring with the reversed words, as illustrated in the doctest below.>>> reverse_sentence('ATest string!')'A!gnirts tseT' """Let A be the set of all strings of decimal digits of length 5. For example 00312 and 19483 are two strings in A . You pick a string from A at random. What is the probability that the string has no 4 in it?Let the universal set be the set ? of all real numbers and let ? = {x ∈ r |0 < x ≤ 2},? = {x ∈ r |1 ≤ x < 4}, ? = {x ∈ R |3 ≤ x < 9}. 4 what is A U C
- The reverse of a string x denoted by rev(x) and is defined by the following recursiverule: •rev(ε) = ε•rev(xa) = a.rev(x) Prove that if A is a regular set then so is the following set:rev(A) = {rev(x) : x ∈A}Given a string S, find the longest palindromic substring in S. Substring of string S: S[ i . . . . j ] where 0 ≤ i ≤ j < len(S). Palindrome string: A string which reads the same backwards. More formally, S is palindrome if reverse(S) = S. Incase of conflict, return the substring which occurs first ( with the least starting index). Example 1: Input: S = "aaaabbaa" Output: aabbaa Explanation: The longest Palindromic substring is "aabbaa".With simply the at, length, and substr string methods and the + (concatenate) operator, construct a function that accepts a string s, a start position p, and a length l and returns a subset of s without the characters starting at position p. Strings begin at 0. (“abcdefghijk”, 2, 4) yields “abghijk”.
- Suppose that B is the infinite set of strings made from one or more a’s and b’s. B = { "a", "b", "aa", "ab", "ba", "bb", "aaa", "aab", "aba" ... } Prove that B is countable. Your proof must work for all strings in B. Hints: make sure it works for strings like "a", "aa", "aaa", etc. Also make sure it works for strings like "ab", "aab", "aaab", etc.Implement a method String[] dedup(String[] a) that returns the objects ina[] in sorted order, with duplicates removed.For this problem, please kindly show your work Let ?L be a set of all finite binary strings that representing a binary number divisible by 2 (or 102102). What is a REGEX of ?L? Design an FA ?a such that ?a accepts ?L, i.e., ?=?(?)

