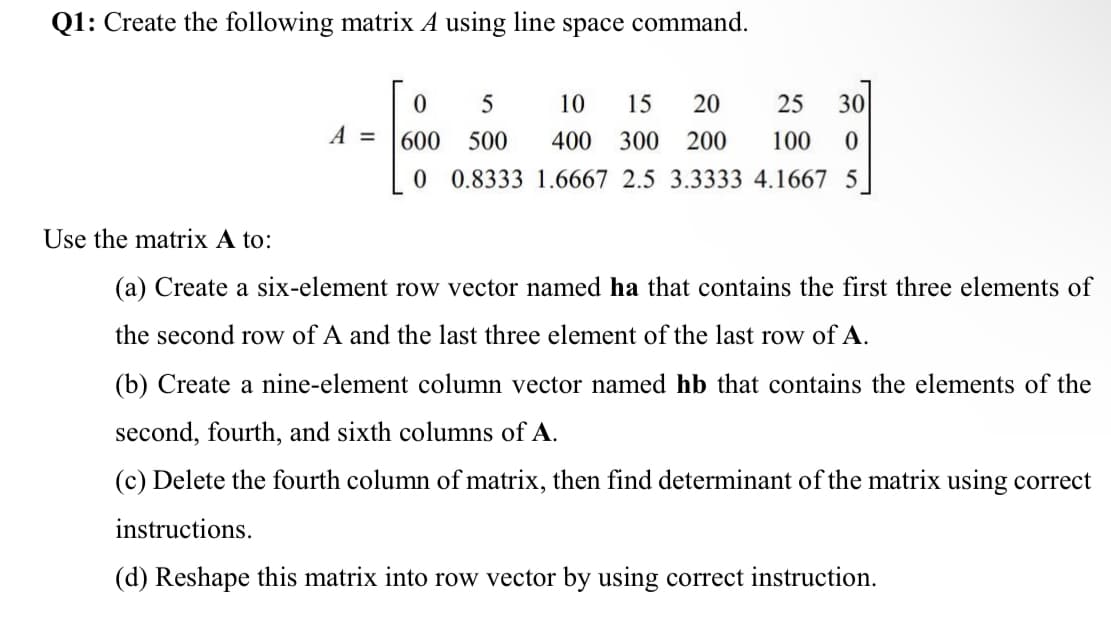
line space command.
Q: Provide examples of design principles that will be used to create the proposed system's user…
A: Introduction: The guiding concept of structure. Your design should organise the user interface in a…
Q: Create a structure named MyStruct containing two fields: field1, a single 16-bit WORD, and eld2, an…
A: Given Structure name: MyStruct Fields: filed1, a single 16-bit WORD field2, an array of 20 32-bit…
Q: ore than 90% of all microprocessors/microcontrollers produced are employed in embedded computer…
A: Intro More than 90% of all microprocessors/microcontrollers produced are employed in embedded…
Q: 9. You are the Network Engineer of a firm that needs to subnet a Class C IP address range of…
A: Below I have provided the handwritten solution of the given question:
Q: What are some of the expenses related to putting a database system into place?
A: Introduction: A database is an organised collection of information or data that is often recorded in…
Q: "The Internet is a computer network that connects billions of computing devices all around the…
A: Introduction: Through computer terminals, computers, and other devices, both individuals and…
Q: What topologies would you suggest for networks?
A: This question provides information about network topologies. The network architecture connects…
Q: What elements should you consider while weighing the benefits and drawbacks of scattered data…
A: Introduction: The variance properties of a statistical series are shown. They are often…
Q: What essential steps should you take to achieve this? Before analysing the hard disc, the computer…
A: Intro When a computer is turned on, a process known as booting takes place, which is launching the…
Q: Which of these features are often encountered in network diagrams?
A: Answer:
Q: Ask the user for an Integer input called “limit”: * write a while loop to write even numbers…
A: Use a while loop to check condition whether limit has been reached 0 or not and then use another…
Q: What is the difference between static and dynamic memory allocation?
A: Introduction: The computer system receives instructions from programmes. The program's primary goal…
Q: Could you kindly explain network topologies to me?
A: Network Topology: The arrangement or pattern by which computer systems and network devices will be…
Q: We ensure that all communication taking place on the present iteration of the Internet between the…
A: Introduction : The Named Data Networking aims to develop a new architecture that can capitalize on…
Q: ne mobile app interface shown in Figure 4, identify an appropriate type of virtual keyboard that uld…
A: Keyboard can be of multiple types but two major types mostly used are:- 1. Qwerty keyboard 2. Numpad…
Q: Because of recent technological advances, the majority of today's appliances can connect wirelessly.…
A: Introduction: Technology has revolutionized our world and daily lives. Additionally, technology for…
Q: ative Analysis
A: CPU scheduling: Scheduling of processes/work is done to finish the work on time. CPU Scheduling is a…
Q: Given the binary floating-point value 1101.01101, how can it be expressed fractions? as a sum of…
A: Given binary number : 1101.01101
Q: Programming is more important than performance, therefore don't base your decision just on how well…
A: Deep/shallow binding is appropriate when a method can be passed to a function as an argument. When a…
Q: The logical NOT operator is a unary operator. it takes only one operand .A Three operand
A: NOT (!) Logical Operator: This operator returns true when the operand is false and returns false…
Q: A programmer's viewpoint is needed to explain why deep access is preferable than shallow access; do…
A: Given: Do not just base your argument on performance issues; instead, explain why deep access is…
Q: When physical filenames are introduced into system code and the file structure suggested by these…
A: The problems that might arise while developing a system can be avoided by following these…
Q: Q2: A- Give a short answer to i- ii- ii- iii- iv- V- vi- vii- ix- the following: Why POP instruction…
A: 1) PUSH stores a constant or 64 bit register out onto the stack. The POP instruction retrieves the…
Q: Why is the MetaData component so crucial in the architecture of a data warehouse infrastructure
A: Introduction Processing done in the data warehouse is distinct from processing done on operational…
Q: Why do you think data quality is one of the most important aspects of data warehousing? Describe the…
A: Introduction: Data quality is a way of assessing the state of data based on variables, including…
Q: Instead of arguing that deep access is better because of its superior performance, explain why deep…
A: Dynamic scope allocation: Non-block structured languages use dynamic allocation rules for scope. It…
Q: How does the latest version of Nessus differ from previous versions, and what features and benefits…
A: Introduction: Tenable, Inc. built Nessus, a proprietary vulnerability scanner. Tenable.io is a…
Q: To what extent should the effectiveness and efficiency of interpersonal skills be assessed…
A: It is the ability with which we communicate in daily life, such as communication skills, speaking,…
Q: Do subsystems of large computer processes and programmes make sense when disassembled? What are the…
A: Introduction: Decomposition is the process of breaking large computer processes and programmes down…
Q: What recommendations do you have for network system topologies?
A: Network architecture A network's topology is the physical and coherent arrangement of its nodes and…
Q: What do you know about the Meta Data repository, and where exactly does it live inside the DWH…
A: A software tool known as a metadata repository is used to maintain descriptive data about the data…
Q: ain the differnece between soql and sosl sales
A: Introduction: Below the differnece between soql and sosl salesforce.
Q: Mossaic Tiles, Ltd. Gilbert Moss and Angela Pasaic spent several summers during their college years…
A:
Q: Did usability objectives and user experience goals differ in any way in your design?
A: There are distinctions between the objectives of usability and those of the user experience, which…
Q: What does "cloud storage" actually mean?
A: Introduction: The technology known as cloud storage is currently the most popular method for storing…
Q: What exactly is a semaphore, and what are the various types of semaphores? Give examples of its…
A: Introduction: Semaphore is a technology that allows processes to more sophisticatedly coordinate…
Q: The rise of artificial intelligence (AI) in everyday life is viewed as a double-edged sword.
A: Introduction: Al has become an important part of our everyday lives, and as an industry, it is…
Q: Linked networks must comprise communications processing equipment such as switch routers and hubs.…
A: Intro Switch routers: In order to transport data inside and across networks, a switch router…
Q: In order to protect communications between itself and its abroad peers, a government agency decides…
A: A "proprietary" product is protected because the owner can only utilise it. For private cryptography…
Q: Java Script Create a function that calculates the number of different squares in an n *n square…
A: Explanation to output If n = 0 then the number of squares is 0If n = 1 then the number of squares is…
Q: Q1) (A) If y is (2,4,......, 10) Write a program to print the values of x. X = Write the values of x…
A: no programming language is mentioned, I am using Matlab. Code: y=2:2:10…
Q: The most often used two technologies in wireless networks are: Mesh networks as well as ad hoc…
A: Introduction: In everyday life, several sorts of technology are employed.
Q: Section 10.7 10.10 (The My Integer class) Design a class named MyInteger. The class contains the…
A: C++ is the programming languages that are used to create the web applications. It is cross platform…
Q: The layers of a DBMS-based application may be described in a few sentences.
A: Given: A database may be created and maintained using a software programme called a database…
Q: True/False Changing the div CSS selector width to 30% makes the resize when the browser width is…
A: Option True is correct choice Use the CSS max-width Essentially use the CSS max-width property to…
Q: IWrite classes based on your smart home simulator design. In methods, just print out something.…
A: Program: class Gettersetter:def __init__(self, age = 0):self._age = age# getter methoddef…
Q: For the purpose of argument, let us imagine that an airline has a database that employs a technique…
A: Introduction: Let us take a database system that uses snapshot isolation in context of airline.…
Q: Do you know where the Meta Data Repository is located in the DWH environment? Is there a reason for…
A: Answer:
Q: Draw the State diagram of Muscat Sheraton Hotel Reservation System for the below given case study…
A: Introduction: State Diagram: A state diagram is used to represent the condition of the system or…
Q: The rise of computer technology, information technology, information networks, and the internet…
A: Intro The proliferation of computer technology, information technology, information networks, and…
Trending now
This is a popular solution!
Step by step
Solved in 6 steps with 9 images

- Assume the variable books_vector is a vector that contains six elements. Which of the following commands creates an array of this vector with three rows and two columns?. Load the file thermo scores.dat and name it thermo scores.(a) Extract the scores and student number for student 5 into a row vectornamed student 5.(b) Extract the scores for Test 1 into a column vector named test 1.(c) Find the standard deviation and variance for each test.(d) Assuming that each test was worth 100 points, find each student’s finaltotal score and final percentage. (Be careful not to add in the studentnumber.)(e) Create a table that includes the final percentages and the scores from theoriginal table.(f) Sort the matrix on the basis of the final percentage, from high to low (indescending order), keeping the data in each row together. (You may needto consult the help function to determine the proper syntax.)Create a 1-by-1000 row vector called M containing random integer numbers between 8 and 256. Using logical array indexing, assign all elements with value greater than 200 to a variable called up200. Display the dimension of variable up200.MatLab Continuing previous task, create another variable called up100 containing all elements in M that are greater than 100 but less than 200. Display the dimension of vector up100. Append variable up200 to variable up100.Please give code for MatLab
- Q2: Create the flowing matrix H H= 1 5 2 6 3 7 10 11 4 12 Use the matrix H to 1- Create a four element row vector named E that contains the elements of the first row of H. 2. of H 3. Create a eight element row vector named B that contains the elements of the first and second row Create a three element column vector named F that contains the elements of the first column of H. 4- Create row of H a eight element column vector named Z that contains the elements of the first and secondAssume numbers is a vector that contains these integers:2 4 6 8 10Then the following code executes:numbers. resize (9) :numbers. resize (11, 5) ;What does the vector contain now?O 11 1111 11 11 0 0 0 0 2 4 6 8 10000002468 10 5 502 4 6 8 10 0 0 0 0 11 11 11 11 1105500002468 100246810 000055Assume vec1 is a vector that contains these integers:10 20 30 40 50 60 70 80 90 100And vec2 is a vector that contains these integers3 6 9 12 15Then the following code executes:vecl.resize(7):vecl.swap (vec2) ;What do the vectors contain now?Cvec1 contains 3 6 9 12 15vec2 contains 10 20 30 40 50 60 70vec1 contains 3 6 9 12 15 0 0Ovec2 contains 10 20 30 40 50 60 70vec1 contains 3 6 9 12 15O vec2 contains 50 60 70 80 90 100vec1 contains 0 0 3 6 9 12 15O vec2 contains 50 60 70 80 90 100This code creates a compiler error.please answer all questions You need to generate a (5x12) rain matrix (Rain[5][12]) that contains the average rainfall over 12 months for a 5 year period. You program should do the following steps: 1) Create a 5x12 integer rainfall matrix 2) Create a 5 element array of int pointers(int * Rain[5]) and assign each pointer to the address of the first element of each row 3) Populate the elements of the matrix with pseudo-random numbers having a range from 0-100 inches. Use the rand( ) function to generate your temperatures. The output of rand() should be mod with 100 (rand()%100) in order to get reasonable rainfall values. Init the random number generator with long seed = srand(67) This task should be performed by a function, void RainGen(int* Rain[ ], int R, int C), that populates all the matrix entries. 4) After generating all rainfall matrix entries, print the entire matrix using the function, void Print(int* Rain[ ], int R, int C); 5) Calculate the…
- 1. Import data: Import the csv file HIV prevalence and assign it to a variable called “HIV”.2. Enter data with function c: Assign the data 2 3 0 3 1 0 0 1 to a variable "typos" and print it out.3. Creating Matrices: Create a matrix 1:8 with 2 rows and 4 columns, fill the matrix by column anduse matrix subscript [2,3].4. Using Factors. Status factor consists of “low”, “middle” and “high”. With the default factor level,the order should be “high”, “low”, “middle”. Override the default factor levels for the charactervector status created in alphabetical order by specifying levels option.5. Creating Data frames. The columns are n, s and b. n is a numeric vector consisting of 2, 3 and 5. sis a character vector consisting of aa, bb and cc. b is a logical vector consisting ofTRUE,FALSE,TRUE. Create a data frame and assign it to the variable df.6. Format: Please submit the document in Microsoft Word or Adobe PDF format. Other formats,such as Microsoft Excel, R, or Corel WordPerfect, will…1)Complete the following script so that the variable totarea will contain the total area of all polygons in a polygon shapefile, flcounties.shp. import arcpy infc = r"D:\data\flcounties.shp" rows = arcpy.da.SearchCursor(infc,____________ ) totarea = 0 for row in rows: totarea += ___________ print totarea 2)Complete the following script so that it will read all the polygons in a simple polygon shapefile, flcounties.shp, and print out the x and y coordinates of all the the vertices of each polygon. import arcpy infc = r"D:\data\flcounties.shp" rows = arcpy.da.SearchCursor(infc,__________ ) for row in ______________ : ptarray =row[0] . ____________ for pt in______________ : print "{0}, {1}".format( _______________ , _____________) Subject: Python ProgrammingIN MATLAB SOFTWARE Task 5 Create a 1-by-1000 row vector called M containing random integer numbers between 8 and 256. Using logical array indexing, assign all elements with value greater than 200 to a variable called up200. Display the dimension of variable up200. Task 6 Continuing previous task, create another variable called up100 containing all elements in M that are greater than 100 but less than 200. Display the dimension of vector up100. Append variable up200 to variable up100.
- In the table below are votes cast for both major party candidates in the 2016 recent presidential election for a random sample of states (every fifth alphabetically). Insert a code chunk that creates a vector of Trump votes. Name it something intuitive. Repeat for Clinton votes. Check your work by listing each vector. State Name | Trump Vote Count | Clinton Vote Count ----------- | ---------------- | ----------------- Alabama | 1,318,255 | 729,547 California |4,483,814 | 8,753,792 Florida | 4,617,886 | 4,504,975 Indiana | 1,557,286 | 1,033,126 Maine | 335,593 | 357,735 Mississippi | 700,714 | 485,131 New Hampshire |345,790 | 348,526 Ohio | 2,841,006 | 2,394,169 South Carolina | 1,155,389 | 855,373 Vermont | 95,369| 178,573 Wyoming | 174,419 | 55,973 ```{r} ``` *** **Question 2:** Continuing to work with the 2016 election results, insert a code chunk that computes the **percent** of the vote Clinton won in each state and assign them to a vector. Check your work by printing out…C++ Help Integers are read from input and stored into a vector until 0 is read. Output the elements from index n to the last index of the vector, where n is specified by the vector's last element. End each number with a newline. Ex: If the input is 7 12 18 2 0, the vector's last element is 2. Thus, the output is: 18 2 Note: The input has at least three integers, and the vector's last element is always less than the vector's size. #include <iostream>#include <vector>using namespace std; int main() { vector<int> intVect; int value; int i; int n; cin >> value; while (value != 0) { intVect.push_back(value); cin >> value; } // insert code here return 0;}In C++ please and where I can copy and paste please. This program will store roster and rating information for a soccer team. Coaches rate players during tryouts to ensure a balanced team. (1) Prompt the user to input five pairs of numbers: A player's jersey number (0 - 99) and the player's rating (1 - 9). Store the jersey numbers in one int vector and the ratings in another int vector. Output these vectors (i.e., output the roster). Ex: Enter player 1's jersey number: 84 Enter player 1's rating: 7 Enter player 2's jersey number: 23 Enter player 2's rating: 4 Enter player 3's jersey number: 4 Enter player 3's rating: 5 Enter player 4's jersey number: 30 Enter player 4's rating: 2 Enter player 5's jersey number: 66 Enter player 5's rating: 9 ROSTER Player 1 -- Jersey number: 84, Rating: 7 Player 2 -- Jersey number: 23, Rating: 4 ... (2) Implement a menu of options for a user to modify the roster. Each option is represented by a single character. The program initially outputs the menu,…

