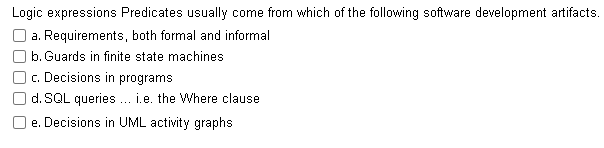
Logic expressions Predicates usually come from which of the following software development artifacts. O a. Requirements, both formal and informal O b. Guards in finite state machines O. Decisions in programs O d. SQL queries. i.e. the Where clause O e. Decisions in UML activity graphs
Q: We are very dependent on technology for ALL security needs. what are some of the common things you s...
A: check further steps for the answer :
Q: A cryptography student has accidentally used the same keystream to encrypt two different messages, M...
A: A cryptography student has accidentally used the same keystream to encrypt two different messages, M...
Q: Give an example of a case in which the complete denial of a service to a user (in which the user rec...
A: Introduction: The computer's denial of service attack (DOS attack) represents a cyber-attack. The ...
Q: 3. WRITE A JA VA PROGLan DuT KCLEPTS AN ORDINALY Numsey. and- BUTPUT ITS tauIVALENT (2oma NumenALS ....
A: “Since you have asked multiple questions, we will solve the first question for you. If you want an...
Q: Why run a k-Means cluster p that apply. O Find groups not explicit
A: Why run a k-Means cluster process on data? Select all that apply. Find groups not explicitly labeled...
Q: ore's law play in supercomputing, grid comp
A: Moore's law play in super-computing, grid computing, and cluster computing
Q: Given the following sets: A = {2, 3, 4}, B = {1, 5, 10}, C = {-1, 1, 2}, D = {2, 5, 10} What is the ...
A: Note: This is multiple questions-based problem. As per company guidelines, only the first question i...
Q: Using the Language Prolog, Does [[A|B], C] match with [mineDog,loneStar,greenCat]
A: Answer: False.
Q: ajectory that AI will take over the next five years in cybersecurity
A: Artificial intelligence (AI) has been a huge increase enabler for many industries, because of its po...
Q: 2. Write a function which will take list as a argument and this function will return a reversed list...
A: Given :- Write a function which will take list as a argument and this function will return a reverse...
Q: The metrics that are calculated for the training set measures the goodness of fit of the fitted mode...
A: Training data is the initial data used to train machine learning models.
Q: Apply Vigenère Cipher using the key "SPANISH" to find the cypher text for the following plain text. ...
A: The answer is given below.
Q: tudy about a full virtualization based hypervisor and explain its working and ecture. (Please must e...
A: "Virtualized environments." A virtual machine, which itself is essentially a means of separating hel...
Q: -In CMOS gates, what occurs when the frequency of the input signal increas A) The power dissipation ...
A: Question: In CMOS gates, what occurs when the frequency of the input signal increases: A) The power ...
Q: 1.Write a C# Sharp program that takes four numbers as input to calculate and print the average. Tes...
A: Given: We have to write a C# Sharp program that takes four numbers as input to calculate and print t...
Q: ~p →r^~. b. а. t - S и u →~p d. e. u V w
A: Lets see the solution.
Q: Using pointer arithmetic, update nthCharPtr to point to the 4th character in oddOrEven.
A: Arithmetic operation on pointers is like normal arithmetic operations only but the difference is tha...
Q: Calculate what is the maximum viewing distance for a given setup to be able to distinguish a details...
A: The viewing distance on a led screen is defined as the correct distance so that our eyes generate a ...
Q: Activity 1: Describe how communication is influenced by Use a separate sheet for your answers.
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN ...
Q: hy do mobile apps usually require many pages? Describe the standard structure of ionic code used to ...
A: Lets see the solution.
Q: can you write a shell script for searching a world inside of a text file?
A: Algorithm: Start Read word to search If grep -q $word hello.txt, then print word found else print n...
Q: give 1 sample process that can be executed in kernel components.
A: Under Linux kernel: During Microkernel, a function can program I/O Controller buttons, operate OS sy...
Q: What other goods, outside computers, are equipped with microprocessors?
A: First of all what is a microprocessor? Computers' brains are microprocessors. They manage the flow o...
Q: Philippine currency is broken down into 1000, 500, 100, 50, 20, 10, 5, and 1 peso coin. Write a PHP ...
A: PHP short form of hypertext preprocessor is a scripting language used in web development alongsid...
Q: What error might we get when running the following code? Assume obj is an instance of some class. ob...
A: b. TypeError: robo() takes 3 positional arguments but 2 were given.
Q: Who was the person who invented the multi-touch device?
A: the first human-controlled multi-touch device was been developed at the University of Toronto by N...
Q: Consider a Direct Mapped cache with 32-bit memory address reference word addressable. Assume a 2 wor...
A: Memories location: The stack is a link to the mainframe of storage, which is used exclusively by ve...
Q: Answer the 2 questions, will upvote if complete, short solution/explanation will do
A: SUMMARY: - Hence, we discussed all the points.
Q: Consider Bag, SinglyLinkedList, and DoublyLinkedLists classes for integers. Implement and test the f...
A: 5 public int getNthNodeData(int index) { Node current = head; // init...
Q: What is the big-O notation for the worst-case runtime of the code fragment below? for (i = 0; i < N;...
A:
Q: What is the hex representation of the given RISC-V instruction? Note: just translate the beq instruc...
A: Solution Instruction: beq x5, x5, loop offset = 4 13-bit immediate imm[12:0] = 0 0 000000 0010 0 imm...
Q: Write a code in AVR to load values $30, $15 and $40 using register R16 into locations $101, $102 and...
A: LDI R16, $30 ; Initialize the value. Load the value $30 in the registerR16. LDI R17, $15 ; Initiali...
Q: Consider the following recursive algorithm. 1]) ALGORITHM Riddle(A[0..n â^' 7/Input: An array A[0..n...
A: Answer: I have done code and also I have attached code and code screenshot as well as output
Q: a. What is the syntax error in Program B. b. Correct the syntax error. You are only required to wr...
A: Note: The answers of the first three subparts are given only. Please repost the last subpart to get ...
Q: A-Convert each of the following decimal numbers to excess-5code: a- (76)10 (67)1o then add the two n...
A: A decimal number is expressed in base 10 formats. The excess-5 code is the representation of decimal...
Q: In Ruby programming language, write a program to input the radius of a sphere(in cm) and print the v...
A: As given, we need to write a ruby program that takes radius of the sphere as input and print the vol...
Q: Consider the following page reference string: 1, 2, 1, 3, 2, 4, 5, 1, 4, 3, 5, 2, 1, 2, 4, 3, 5 What...
A: the answer is given below:-
Q: ven F: Z to Z and G:Z to Z by the rules F(n) = 2n and G(n) = [n/2] for every integer n. Is Go F =Fo ...
A: 1)B Because the values are already given for Fand G. So while executing it update the value of ...
Q: A- Using any method, design a 2's complement converter circuit which accepts 4 bit of input data, an...
A: I have answered this question in step 2.
Q: What's the difference between event bubbling and capturing an event?
A: Event capturing and event bubbling are concepts of JavaScript. These are two ways of event propagati...
Q: You are given a Binary Search Tree Program. Uses the Decision Table Test Method to find the Rules, C...
A: Below i have answered:
Q: the IOPS number calculated for the CIO to determine a purchase of new storage equipment and the vend...
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: Define the term architecture formally with any two examples (Subject: Software Design and Architect...
A: Introduction: A computer system is essentially a device that automates complex activities. It should...
Q: The words "crawling" and "indexing" the web are used to describe how the web is crawled and indexed.
A: CRAWLING: Online crawling is the process of indexing data on websites with the help of software or ...
Q: Explain how we should change the insertion and deletion algorithms in a B+-tree to implement and mai...
A: A b+ tree i8s one of the trees which is an m array tree containing a variable but contains a large n...
Q: Write a C# Sharp program to check whether a given number is even or odd.
A: The C# program is given in the below steps.
Q: 1.Scilab a. List all commands with their corresponding functions and symbols
A: Due to company policies, I am compelled to solve only one question that is the first question. Pleas...
Q: Given the following adjacency matrix: Nodes A B C E F A 1 C 1 1 1 E 1 1 F i) Draw a graph based on t...
A: Answer:
Q: 1. Giving the following Java program representing the class student, complete the missing code. a. G...
A: Here, I have to write a java program for the given class Student and complete the parts given.
Q: Explain briefly the importance of data analytics in business and in education?
A: Data analytics is an emerging field which has potential to bring revolution in the business and educ...
Step by step
Solved in 3 steps

- Correct answer will be upvoted else Multiple Downvoted. Computer science. every subject (aside from precisely one), there exists an essential theme (for the point I, the essential point is pi). Ivan can't give a talk on a subject prior to giving a talk on its essential theme. There exists no less than one substantial requesting of themes as per these essential imperatives. Requesting the subjects effectively can assist understudies with understanding the talks better. Ivan has k uncommon sets of points (xi,yi) with the end goal that he realizes that the understudies will comprehend the yi-th subject better if the talk on it is led just after the talk on the xi-th theme. Ivan needs to fulfill the requirements on each such pair, that is, for each i∈[1,k], there should exist some j∈[1,n−1] to such an extent that qj=xi and qj+1=yi. Presently Ivan needs to know whether there exists a requesting of subjects that fulfills this multitude of imperatives, and if something like one exists,…CENGAGE MINDTAP Programming Exercise 4-6 can anyone help me how to solve?Five schoolgirls sat for an examination. Their parents – so they thought – showed an undue degree of interest in the result. They therefore agreed that, in writing home about the examination, each girl should make one true statement and one untrue one. The following are the relevant passages from their letters: Betty Kitty was 2nd I was 3rd Ethel I was on top Joan was 2nd Joan I was 3rd Ethel was last Kitty I came out 2nd Mary was only 4th Mary I was 4th Betty was 1stWrite a prolog program to solve this puzzle. A completely working solution is required for extra points, i.e. all or nothing proposition.
- Take the values that i attached and solve question 7 plz solve correctly and show neat and clean work plz using matlabQuestion Pap ( B) Full explain this question very fast solution sent me step by step Don't ignore any part all part work uPlease send me answer with 10 min!! please answer all the questions!! I will rate you good for sure!! Can someone explain a few things about the code below? 1.The tools, libraries, and APIs utilized 2.Search methods used and how they contributed toward the program goal 3.Inclusion of any deep learning models 4.Aspects of the program that utilize expert system concepts 5.How the program represent knowledge 6.How symbolic planning is used in the program CODE BELOW: import numpy as np # Define a simple function for the neural network to learn def function(x): return x**2 + 2*x + 1 # Define the neural network architecture input_size = 1 hidden_size = 16 output_size = 1 # Initialize the weights and biases W1 = np.random.randn(input_size, hidden_size) b1 = np.random.randn(hidden_size) W2 = np.random.randn(hidden_size, output_size) b2 = np.random.randn(output_size) # Define the sigmoid activation function def sigmoid(x): return 1 / (1 + np.exp(-x)) # Define the derivative of…
- are the instructions for combining components to process information and generate the desired output. Group of answer choices People Procedures Databases NetworksComputer science When it comes to database systems, add your own opinions and argument points on the phrases "time variation" and "time invariant."Try explaining processes in fields other than systems analysis using Structured English.
- Correct answer will be upvoted else Multiple Downvoted. Don't submit random answer. Computer science. challenge comprises of n issues, where the tag of the I-th issue is meant by an integer simulated intelligence. You need to AK (take care of all issues). To do that, you should take care of the issues in some request. To make the challenge more amusing, you made additional impediments on yourself. You would rather not take care of two issues continuously with a similar tag since it is exhausting. Additionally, you fear huge leaps in troubles while tackling them, so you need to limit the number of times that you take care of two issues continuously that are not neighboring in the challenge request. Officially, your settle request can be depicted by a change p of length n. The expense of a change is characterized as the number of lists I (1≤i<n) where |pi+1−pi|>1. You have the prerequisite that api≠api+1 for all 1≤i<n. You need to know the base conceivable expense of…Correct answer will be upvoted else Multiple Downvoted. Computer science. Berland local ICPC challenge has quite recently finished. There were m members numbered from 1 to m, who contended on a problemset of n issues numbered from 1 to n. Presently the article is going to happen. There are two issue creators, every one of them will tell the instructional exercise to precisely k back to back errands of the problemset. The creators pick the section of k continuous errands for themselves autonomously of one another. The sections can correspond, meet or not cross by any means. The I-th member is keen on paying attention to the instructional exercise of all continuous errands from li to ri. Every member consistently decides to pay attention to just the issue creator that tells the instructional exercises to the most extreme number of assignments he is keen on. Leave this greatest number alone artificial intelligence. No member can pay attention to both of the creators, regardless of…Which of the following is not a valid assertion regarding supervised learning?

