LTE . The classes Name and Date are separate classes used as properties in the Employee class. 9:59 Class Employee is the superclass of the classes SalariedEmployee and HourlyEmployee The superclass has the
LTE . The classes Name and Date are separate classes used as properties in the Employee class. 9:59 Class Employee is the superclass of the classes SalariedEmployee and HourlyEmployee The superclass has the
Chapter11: Advanced Inheritance Concepts
Section: Chapter Questions
Problem 3PE
Related questions
Concept explainers
OOPs
In today's technology-driven world, computer programming skills are in high demand. The object-oriented programming (OOP) approach is very much useful while designing and maintaining software programs. Object-oriented programming (OOP) is a basic programming paradigm that almost every developer has used at some stage in their career.
Constructor
The easiest way to think of a constructor in object-oriented programming (OOP) languages is:
Question
Java program code assignment
Transcribed Image Text:LTE
grossaper
9:59
The classes Name and Date are separate
classes used as properties in the Employee
class.
Class Employee is the superclass of the
classes SalariedEmployee
and
Hourly Employee. The superclass has the
attributes name and date of hire and methods
to set and get these attributes. It also has 2
methods: equals() which check if the objects
are same and toString() which convert the
properties to a printable string. Also the
method read() which used as an input
method.
The SalariedEmployee subclass has in
addition to the attributes of the super-class
the attribute annualSalary and set and get
methods for it. This class also defines the
read() method and grossPay() which in this
case returns the salary of the employee.
The HourlyEmployee subclass has in addition
to the attributes of the super-class, the
hours Worked and hourlyRate attributes. It
provides 'get' and 'set' methods for these
attributes. Also it provides the methods
equals() and toString(). Finally, it provides
an implementation of the method
grossPay(), which returns the product of the
hourly rate with the hours worked for each
employee.
Ims.kku.edu.sa
After creating this class hierarchy create a Main
class with a main function. This function will
have an array of type Employee and size 2.
Place in the position 0 of this array a
SalariedEmployee object and in the position 1
an Hourly Employee object. Then set some
appropriate values for the two objects. Finally
create a loop that calls the grossPay() method on
both objects of the array and display the
.returned value
Transcribed Image Text:annualSalary: double
LTE II.
2) Code should display the correct output.
3) Submit the mini project before deadline
4) Each student should upload the Answer in
Blackboard
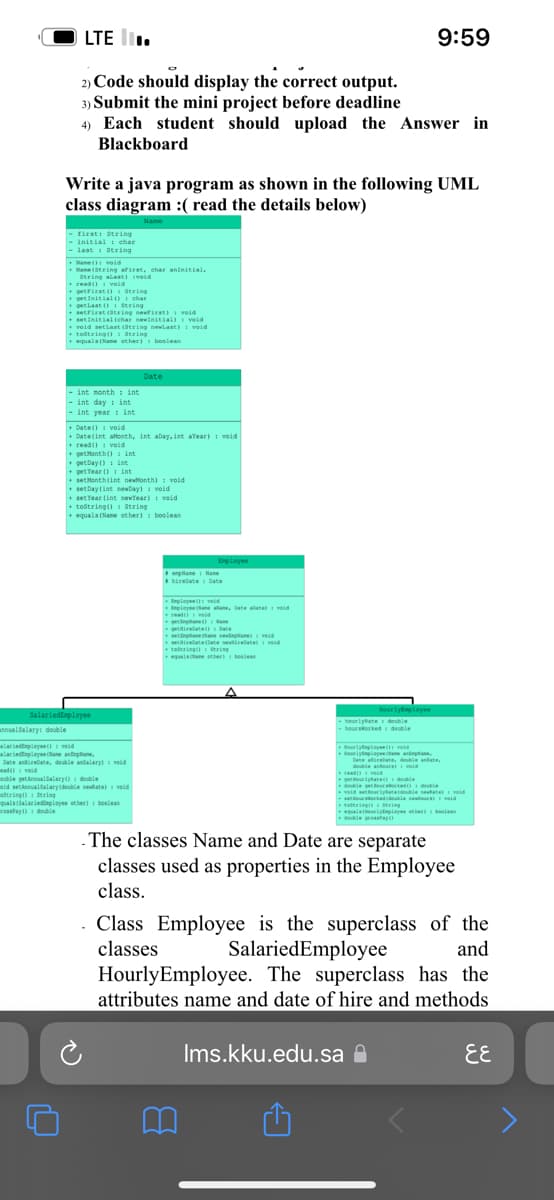
Write a java program as shown in the following UML
class diagram :( read the details below)
Name
-first: String
- initial char
- last String
Name(): void
Same (String aFirst, char aninitial,
U
String alast) (void
read(): void
+getFirst (): String
char
getInitial ()
get Last ()
setFirst (String newfirst) void
String
set initial (char newInitial)
veid
void setlast (String newlast) void
toString(): String
equala (Name other) boolean
- int month int
- int day int
- int year: int
SalariedEmployee
+Date() void
+ Date(int aMonth, int aDay, int Year) void
read(): void
getMonth(): int
getDay(): int
+get Year (int
setMonth(int newMonth): void
setDay (int newDay): void
set Year (int newYear): void
toString(): String
+ equals (Name other): boolean
alariedEmployee(): veid
alariedEmployee Olane annplane,
Date airebate, double andalary) veid
ead():void
Date
souble getAnnualalary(): double
oid setAnnualSalary(double newate): void
oString(): String
quals(Salariediaployee other): boolean
rossPay(): double
Employee
plane Name
hirebate Date
+ Deployee(): ved
Employee ane alane, Date alate void
read():void
get
getiredate() Date
a)
se) veid
+tiratelate sevirebate
taltring String
equals lane other): boolean
-hourlyRate: double
hoursworked double
HourlyEmployee
HourlyEmployee void
Hourlynpes Ca
9:59
read
M
Date airelte, double anate,
double dour) void
getourlyRate double
doble getur orked d
void setourlyRate(double newatel: void
-orked(double ours) void
totring(): String
equals(NourișEsployee other) boles
double grossfay()
The classes Name and Date are separate
classes used as properties in the Employee
class.
Ims.kku.edu.sa
. Class Employee is the superclass of the
classes SalariedEmployee
and
Hourly Employee. The superclass has the
attributes name and date of hire and methods.
६६
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT