m 5.2 km F D 2.2 km 4.7 km 2.9 km 6.4 km с 3 km 4.1 km 7 km A 3.2 km B
Q: Does a method that accepts an array as an argument really have access to the original array, or is…
A: Introduction: When programming in C, an array may be provided to a function by value by declaring…
Q: Talk about the potential for attackers to use your system as a platform for a widely spread assault.
A: Malware You've probably had a close encounter with malware if you've ever seen an antivirus warning…
Q: Does a method that accepts an array as an argument really have access to the original array, or is…
A: When writing code in C, an array can be passed as a value to a function by stating its name in the…
Q: a statement be distinguished fro
A: Solution - In the given question, we have to tell can a statement be distinguished from an…
Q: 110.0010) = (?)p BCD BCD with BCD weight
A: The answer is
Q: Look through the method header below, then, as an example, write a call to the method. an internal…
A: The answer to the question is given below:
Q: The question was: What are the methods and difficulties for using blockchain in the banking…
A: Answer: - Methods for implementing blockchain include: - Having cryptographic keys: This aids in…
Q: When is it important to do a type conversion run-time check?
A: The following are the conditions for a type conversion: When a user works with float data type and…
Q: What are the three stages a software must follow while using a file?
A: Software is a set of computer programs and related documents and data.
Q: What does a language that is "highly typed" mean? Static typing, what do you mean?
A: statically-typed languageA statically-typed language is a language like Java, C++, etc where the…
Q: What does the keyword out mean when it is placed before an argument to the method in a method call?
A: A keyword out is called method is required to assign or initialize a value of a parameter before…
Q: 2. What do you mean by p persistent CSMA(carrier sense multiple access)?
A: Carrier-Sense Multiple Access (CSMA) is a media access control (MAC) protocol in which nodes verify…
Q: Justify why the professional software produced for a customer is more than simply a collection of…
A: Please refer below for your reference: The professional software produced for a customer is more…
Q: Why, in your opinion, is Internet data costly in Ghana? What might be done to reduce users' data…
A: Why, in your opinion, is Internet data costly in Ghana There are several reasons why Internet…
Q: What is the definition of data structure?
A: A data structure is a way to organize information so that it can be accessed and used efficiently.…
Q: What exactly are aggregates, and how can I tell? Who will gain from them?
A: let us see the answer:- Introduction:- A piece of software called an aggregator is made to gather…
Q: How does information go across the layers of the Internet? model?
A: Introduction: If you use an Internet Protocol (IP) and TCP packet routing network, then it works…
Q: Give a thorough analysis of the network adapter's operating features.
A: Answer is in next step.
Q: Which is better for collaboration: Office 365 or Google Docs?
A: Google docs: To explain if Google Docs vs Office 365 is the superior option. The online word…
Q: What two categories do the.NET Framework and the C# data types fall under?
A: C# data types: All data types in C# and the.NET framework can be divided into two categories. It's…
Q: In simple words, describe the clock generator.
A: Start: A circuit known as a clock generator produces a timing signal to synchronize the functioning…
Q: The capabilities of various requirements engineering CASE systems will be identified and explained…
A: The automation of all or a portion of the systems development process is what is referred to as…
Q: What are the two parameters that a TryParse function expects from you when you write code?
A: #note: since programming language is not specified we are providing answer in c# TryParse method…
Q: student information (name, age, allowance per month). The number of students whose information must…
A: Output Screenshot;
Q: Give a brief explanation of the concept of virtual machines.
A: Definition Virtual machine: A virtual machine is a straightforward piece of software that replicates…
Q: What benefits do enumeration types provide over a collection of named constants? What benefits does…
A: 1.Enumeration User created data types are enumeration types. It allows adding a number of data…
Q: If a TryParse method successfully converts the string parameter, where is the result stored?
A: Introduction Step 1: Values hold on by “TryParse()” method:If the “TryParse()” methodology converts…
Q: Pseudo code for a radix r:=px decimation in time FFT.
A: Pseudo code for a radix r:=px decimation in time FFT:
Q: What precisely is a grouping of items (also known as a container instance)?
A: In my view the grouping of items means :
Q: Why does Pinterest see Google as one of its biggest rivals? Pinterest prioritises the smartphone…
A: Why Pinterest see Google as one of its biggest rivals Pinterest sees Google as one of its biggest…
Q: What Makes Up a Computer System's Components? Give a succinct explanation.
A: What Makes Up a Computer System's Components? Give a concise explanation. Every computer system…
Q: a brief explanation of the microcode interpreter
A: The outcome of more basic machine language interpretation is microcode. The register or circuit…
Q: When is it important to do a type conversion run-time check?
A: situation requiring type conversion conditions for type conversion When a user enters an integer…
Q: When a child process utilizes unnamed pipes to read the parent's message buffer, what happens…
A: In Inter - process communication Unnamed Pipe is used in between the communication of a child…
Q: Why does a Random object's intended seed value correspond to the system time?
A: Introduction: The past value number made by the generator is the seed value. At the point when there…
Q: Is it true that C has loops controlled by enumerations? Explain.
A: Loops That Are Controlled By Enumeration (Continued) It is forbidden to change I while the loop body…
Q: Description of Each request has its own object. b. Directions versus c. Model-View-Controller
A: The objects Request and Response Hyper Text Transfer protocol is what the whole internet is based on…
Q: Describe the operation of wireless LANs and demonstrate your familiarity with their setup and…
A: The answer to the question is given below:
Q: Give a thorough analysis of the network adapter's operating features
A: An investigation of the network: Processing Elements, Memory, Direct Memory Access (DMA), and…
Q: Consider a Disk I/O transfer, in which 1500 bytes are to be transferred, but number of bytes on a…
A: An seak time is the length of time it takes for a disk drive to locate a given piece of information…
Q: Create an IP address plan as efficiently as possible for the network shown below. The address space…
A: Given that,Address space= 192.168.10.0/25Network A = 50pcsNetwork B = 20pcs
Q: Is there a certain kind of object you need to make in order to read information from a text file?
A: Object of a file A file object is a kind of object that is connected to a particular file and gives…
Q: The words prefix, infix, and postfix notation should be defined. What does the term "Cambridge…
A: Initial notation: Here, we move the operator's operands to the left. Ex: In this case, (A+B) is…
Q: The definitions of "strict" and "loose" name equivalency are given.
A: GIVEN: The definitions of "strict" and "loose" name equivalency are given.
Q: What does the keyword out mean when it is placed before an argument to the method in a method call?
A: 1) The out is a keyword in C# which is used for the passing the arguments to methods as a reference…
Q: Is there a certain kind of object you need to make in order to read information from a text file?
A: Note: The answer is given by considering the context of the java language. Introduction Text…
Q: Is there a certain kind of object you need to make in order to read information from a text file?
A: File object: An object that is linked to a particular file and offers the software a means of…
Q: It is recommended that you format CDs or hard drives at least seven times before discarding them…
A: The following are the justifications for formatting discs or hard drives: To assure that data cannot…
Q: What are named arguments, and how do they function?
A: In the given question named argument or keyword arguments refer to a computer language's support for…
Q: Reflect on your experiences around how technology has been used in the classroom and its role in…
A: Reflect on your experiences around how technology has been used in the classroom and its role in…
SOLVE USING DIJKSTRA'S
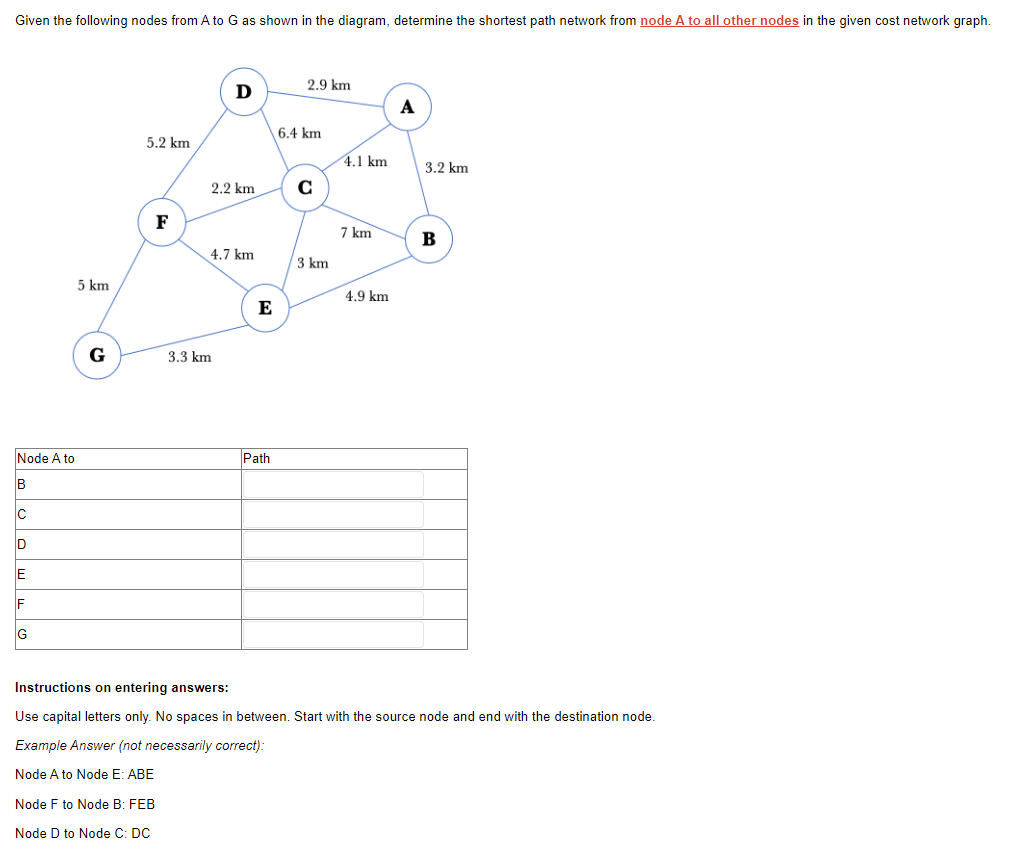
Step by step
Solved in 3 steps with 2 images

- Given the following nodes from A to G as shown in the diagram, determine the shortest path network from node A to all other nodes in the given cost network graph.Consider the following network. With the indicated link costs, use Dijkstra’s shortest-path algorithm to compute the shortest path from x to all network nodes. Show how the algorithm works by computing a table similar to Table 5.1. I am in need of help solving this problem and figuring out how to come up with the values in the table.Consider the following network. With the indicated link costs, use Dijkstra’s shortest-path algorithm to compute the shortest path from u to all network nodes. a) Fill the following table to show the Dijkstra’s shortest-path algorithm works by computing the path and cost form u to all other network nodes. b) Construct the resulting least-cost-path tree from u.
- Consider the network shown below, and Dijkstra’s link-state algorithm. Here, we are interested in computing the least cost path from node E to all other nodes using Dijkstra's algorithm. Using the algorithm statement used in the textbook and its visual representation, complete the "Step 3" row in the table below showing the link state algorithm’s execution by matching the table entries (i), (ii), (iii), (iv) and (v) with their values.With the indicated link costs, use Dijkstra’s shortest-path algorithm to compute the shortest path from D to all network nodes. Show how the algorithm works by filling in the following table, where d(x) is the cost of the least-cost path from the source node D to destination x as of the current iteration of the algorithm, p(x) is the previous node (neighbor of x) along the current least-cost path from the source D to x, N’ is the subset of nodes whose shortest path from the source D has definitely been known. According to the table computed in 1), show the shortest path tree rooted at D. According to the results from 1) and 2), create the forwarding table, in which each row consists of two fields, destination and next hop.In order to function optimally, what are the three conditions that must be true for each given network? Spend a minute or so explaining what one is like in your own words.
- P3. Consider the following network. With the indicated link costs, use Dijkstra’s shortest-path algorithm to compute the shortest path from x to all network nodes. Show how the algorithm works by computing a table similar to Table 5.1 .In designing a communication network, the Minimum Spanning Tree is being used to show the connected subset of the original network graph showing the least amount of links needed to interconnect all the nodes based on all the link costs. Given the diagram below, create the minimum spanning tree (MST) using Kruskal’s Algorithm. With your final MST, find the sum of all the edge weightsWhat are the three conditions that must be true for a network to function optimally? Give me a minute of your time and describe one to me in your own words.
- Summarize the three conditions that must be met by a network for it to function optimally.What three things must exist for a network to perform optimally? Let's take them one at a time and analyze them thoroughly.How exactly would I be able to paraphrase this pseudo-code so that it can make a bit more sense? 1.Initialtzation: generate a random solution X ← RandomSolution() 2. Solve the traffic assignment problem at equilibrium for each link: (flow, cost) ← NonLinearComplementary(X) 3. Evaluate the objective value for the current solution: f (X) ← EvaluateObj Val (f low, cost) 4. T ← Tmax 5 while (T > Tmin) do 6 I ← 1 7 while (t < ltermax)do 8 X' ← FindNeighborSolution(X) 9 (flow,cost) ← NonLinearComplementary(X') 10 f(X') ← EvaluateObf Val (f low, Cost) 11 Δ ←(f(x) - f(x')) 12 if(Δ<0)then 13 BoltzmannValue ← exp(-Δ/T) 14 if (BoltzmannValue < Random (0,1)) then 15 Accept the new solution: X ← X' 16 end If 17 Else I8 Accept the new solution: X ← X' 19 end if 20 i ← i+1 21 end while 22 T ←T ∞ 23 end while ________

