make -s > ./main Enter String: Party on the Quad Enter Key: Homecoming Original Message: Party on the Quad Encrypted Message: WODXACZBUKXIMH Decrypted Message: PARTYONTHEQUAD > 0
Q: code a c++ program, game of 23 (please do not use break) The game of "23" is a two-player game that...
A: #include<iostream> using namespace std; class Game//Class { public: int logic(int x, int t...
Q: 2. Write a Java program that determines if a number is positive or negative. Ехample: Input a number...
A: Here in this question we have asked to write a Java program which determine that given number is pos...
Q: n PHP language, write a program to input a string from the user and print every character of the str...
A: Answer
Q: There are two basic approaches to the design of OS kernel. One is called microkernel approach, and t...
A: 1) monolithic kernel 2) xv6 allocates one kernel stack for each process. The kernel stack is separat...
Q: On the motherboard, what are the two primary components?
A: On the motherboard, what are the two primary components?
Q: In chapter 4, MARIE instructions are 16-bit long (4-bit opcode and 12-bit address). So, MARIE can ad...
A: We need to describe why MIPS instructions that are 32-bit long (with 6-bit opcode) but can address u...
Q: de up of ma
A: CPUs are made up of many parts.
Q: what is Hard disk?
A: Hard Disk also known as HDD is a hard drive (a physical device) that is used for storage purposes. i...
Q: Where did Charles Babbage come up with the idea for the computer?
A: After years of experimentation, Charles Babbage came up with the first computer-like device we know ...
Q: Question 2 Which of the following is the proper recursive case for the following function int Recurs...
A: Note: Valid recursive call must lead to termination condition or base case in the given function : t...
Q: Write a C++ program to store the names of students in the class. The program should display the name...
A: Given: Write a C++ program to store the names of students in the class. The program should display t...
Q: What is the output of the following program segment? * c = putchar (c); putchar (F(c)); putchar (c);...
A: As per the requirement program is executed in c language. If we execute the same program as it is we...
Q: What steps are involved in projecting a 3d point to the 2d image in pinhole camera model? Rotating a...
A: Whats steps are involved in projecting a 3d point to 2D point image in pinhole camera model? Here se...
Q: Create an unsigned 16-bit number that stores the value 13330 (decimal). Show what the memory contain...
A: Create an unsigned 16-bit number that stores the value 13330 (decimal). Show what the memory contain...
Q: Which of the four conditions would be violated if a user could remove jobs from a spooling system? S...
A: Some devices, such as tape drives and printers, cannot usefully multiplexthe I/0 requests of multipl...
Q: dware, how do you classify the va
A: There is Computer hardware which is classified in four categories
Q: this is image analysis you need to write matlab code no built in function include signal to nois...
A: C++ code: #include<iostream> #include<cstdlib> #include<cmath> #include<ctime&g...
Q: to decimal for
A: Given Binary Number: 1011101 Multiply each digit of the binary integer by the power of two that co...
Q: 13. Boolean Expression: write a truth table for the following (A+B) Đ (C D)
A: A+B is true, if either A is true or B is true. C.D is true only when both C and D are true X ⊕ Y is ...
Q: . Discuss and write the difference between Grid computing and cluster computing?
A: Grid Computing Cluster Computing 1. A group of physically close-by machines setup. Term usually im...
Q: Identify, list, and define an information system's six components.
A: Identify, list, and define an information system's six components.
Q: Construct a Java program to provide a file named file.txt if it does not exist. Write 100 integers ...
A: I give the code in Java as per your requirement along with output and code screenshot
Q: Normalization should be defined
A: Answer: To ensure the integrity of data, normalisation is necessary. Basically, it's the process of ...
Q: Using C++ . Create a queue using a linked list as your container and use a class. The system must ha...
A: Using C++ . Create a queue using a linked list as your container and use a class. The system must ha...
Q: Create a toolbar and a layout.
A: Introduction: A toolbar (formerly known as a ribbon) is a graphical control element on which on-scre...
Q: Question 1. Given the flowchart below, a) Cross-out the erronous arrow and draw the correct arrow. b...
A: Here remove the erronous arrow , and design right flow chart: =====================================...
Q: What are homogenous coordinates, and what are they useful for? Alternative system of coordinates use...
A: A) It is an alternative system of coordinates used in projection geometry and computer graphics.
Q: Explain Russell’s approach to “knowledge about” and denotation. Do denoting phrases have meaning? In...
A: One of the most important thinkers in the history of philosophy, Bertrand Russell (1872-1970) was a ...
Q: Who created the motherboard, and when?
A: A motherboard is a printed circuit board in general-purpose computers and other expandable systems. ...
Q: what does uncertain loop means ? using this example import random x=True while x==True: n=random.ra...
A: EXPLANATION: The uncertain loop refers to the loop whose number of iterations is not defined. The n...
Q: 3. Nested squares: write a Matlab script which draws a sequence of squares using a random color for ...
A: According to the information given:- We have to follow the instruction to construct the nested squa...
Q: Which of the following policy settings are not supported by Local Group Policy on Windows 10? (Choos...
A: in Folder redirection , You must be a member of the Domain Administrators security group, the Enter...
Q: Using R programming - Dataset contains around 65k+ traffic-related violation records and display 10 ...
A: Libraries Used :- PandasMatplotlibSeabornmissingno
Q: Identify three key Web site performance measures.
A: Given :- Identify three key Web site performance measures.
Q: Let A be an array of integers of size 10, whose ith entry is represented by A[i] for i = 0 to 9, and...
A: - According to the rules, we have to check for the element 85 position in the array.
Q: 1- Create a new user on either VM (on 60 or 65). Use the following requirements: Create a user call...
A: -Create a new user on either VM . Create a user called victor Set victor's password to Victor123! (...
Q: # your code here def multiply_numbers(a,b,c): # Called function receive three values from the callin...
A:
Q: When did the modern computer get its start
A: The computers have evolved through various phases and as we know initially they are of size of a ver...
Q: If this code runs from its start until the endpo : $0x1,8edx $0x8,%ecx Весх, &есх 0x40107e : mov Ox4...
A:
Q: Suppose I is a set of formulae. Show that if IU {A, B} ► 1 then IE¬(A ^ B). (Hint: The deduction the...
A:
Q: complete the function that returns the area of a circle with radius r , note, use math.pi for pi.
A:
Q: Big-O Coding Exercise Show your solution and explanations. Show that a function y = n^4 + 3 can not ...
A: We need to prove that y=n^4+3 is not O(1).
Q: By infinitely increasing the bandwidth of a channel, this channel will have infinitely large error-f...
A: Hello student Greetings Hope you are doing great. As per our policy guidelines, in case of multiple ...
Q: The number of goals achieved by two football teams in matches In a league Is given in the form of tw...
A: Please refer below code and output for the problem above: It contains proper comment at each line: l...
Q: Write a program that accepts the lengths of three sides of a triangle as inputs. The program output ...
A: Start input three side check if square of largest side is equal to the sum of square of two smalles...
Q: What do you mean by "partitioning" in terms of operating systems? Examine the pros and downsides of ...
A: In order to maintain, manage and allocation of the computer's main memory, Memory management plays ...
Q: When would you utilize a data mart instead of a data warehouse for business intelligence? Describe a...
A: Data Storage: Storage of data refers to a sort of technology used to store information and make it e...
Q: • The number of gallons of paint required • The hours of labor required • The cost of the paint • Th...
A: Solution: ws = float(input('Enter number of square feet of wall space to be painted:'))pg = float(in...
Q: What ethical and societal ramifications do artificial intelligence and robots have? Will having robo...
A: Introduction: Artificial intelligence is a branch of computer science that comprises the development...
Q: What kinds of exceptions are captured during compilation?
A: Introduction: The two kinds of exceptions are Checked and Unchecked Exceptions in Java.The exception...
Step by step
Solved in 2 steps

- count the frequent letter of the combined of two string example : if x = icyz and j = ixpc, then there are 8 different passwords that you can choose: icyz,icyc, icpz, icpc, ixyz, ixyc, ixpz, ixpc. icpc has the most frequent letter so the output is 2 please help with c++ code (studio.h, string.h,math.h only)public void OnSend(View v){ String phoneNumber = number.getText().toString(); String smsmessage = message.getText().toString(); if(phoneNumber == null || phoneNumber.length() == 0 || smsmessage == null || smsmessage.length() == 0){ return; } if(checkPermission(Manifest.permission.SEND_SMS)){ SmsManager smsManager = SmsManager.getDefault(); smsManager.sendTextMessage(phoneNumber, null, smsmessage, null, null); Toast.makeText(this, "Message sent", Toast.LENGTH_SHORT).show(); } Question 2: Explain the following code: button.setOnClickListener(new View.OnClickListener() { @Override public void onClick(View v) { FragmentManager fm = getSupportFragmentManager(); FragmentTransaction ft = fm.beginTransaction(); XFragment xfragment = new XFragment(); ft.add(R.id.Main_fragment, xfragment);…Complete the following function according to its docstring. def check_password_exclusive(passwd: str) -> bool: """ An exclusive strong password has a length greater than or equal to 6, and contains ONLY letters and numbers. Return True if and only if passwd is considered an exclusive strong password. >>> check_password_exclusive('I<3csc108!') False >>> check_password_exclusive('time2sleep4me') True """
- if [ $(id -u) -eq 0 ];then read -p "enter username:" username read -s -p "enter password:" password egrep "^$username"/etc/passwd>/dev/null if [ $? -eq 0];then echo "$username exists!" exit 1 else pass=$(perl -e 'print crypt($ARVG[0], "password")' $password) useradd -m -p "$pass" "$username" [ $/ -eq 0 ] && echo "user has been added to system!" || echo "Failed to add a user!" fi else echo "Only root may add to the system" exit 2 fi * recheck the code if this is valid syntax for account management or suggest /do another user account management shell script that runs in unix terminal and please attache the output at the endcan you varify the address for example if i do not have a "-" or a "st" then it prints out invalid put if i do then its valid document.getElementById("AddressLbl").innerHTML = ""; if (!validateVal(document.getElementById("Address").value)) { document.getElementById("AddressLbl").innerHTML = "Mandatory!" }Directions: Write security if the underlined word on the subsequent statementmakes it true and virus it makes the statement a false one, then write the correctterm/word to correct it.
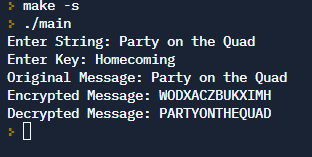
- Text Encryption Encryption plays an important role in protecting messages that are transmitted across the network. There are many symmetric and asymmetric encryption techniques that can be used in order to encrypt text messages. Some of these techniques are Caesar, Rows-Columns Transposition, Rail- fence, and Playfair cipher encryption as well as advance encryption algorithms. In this project, you are required to write a code that is capable of encrypting any given text (or text file) into a cipher text using any two different methods. You should prompt the user to choose the method that they would like to encrypt their text from a given list. Challenge: develop your code to decrypt the cipher text that is encrypted above Example: Assume the text TO SERVE AND TO PROTECT is required to be encrypted using Row-Column with the password ALERT Then the text message in Rows-Columns Transposition will become: TVTTSAPCOEOEENRTRDOX. The same text message in Rail-fence with depth of 4 would…E-mails have the address of the __________senderin the header portion of the mailUsing C-programming; Enhanced security and anti-fraud protectionUse of string functionsSystem is encrypted with username and passwordPassword characters will change into asterisk per inputIf the username and password are correct, display “VALID” otherwise “INVALID”Example:Username: iamwhatiamPassword: *******VALID!
- JavaScript triggers? It has a "onclick" function.please code in python A tweet is a string that is between 1 and 280 characters long (inclusive). A username is a string of letters and/or digits that is between 1 and 14 characters long (inclusive). A username is mentioned in a tweet by including @username in the tweet (notice the username does not include the @ symbol). A retweet is way to share another user's tweet, and can be identified by the string RT, followed by the original username who tweeted it. Your job is to fill in the function count_retweets_by_username so that it returns a frequency dictionary that indicates how many times each retweeted username was retweeted.tweets = ["This is great! RT @fakeuser: Can you believe this?", "It's the refs! RT @dubsfan: Boo the refs and stuff wargarbal", "That's right RT @ladodgers: The dodgers are destined to win the west!", "RT @sportball: That sporting event was not cool", "This is just a tweet about things @person, how could you", "RT…Write in C Language Frequent Letter Your Facebook account has just been hacked and you want to change its password. To create a strongpassword, Facebook just recommended you two strings S and T, each contains N lowercase English letters. You want to choose a password containing N lowercase English letters such that the i th character is either the i th character of S or the i th character of T. For example, if S = icyz and T = ixpc, then there are 8 different passwords that you can choose: icyz, icyc, icpz, icpc, ixyz, ixyc, ixpz, ixpc. The strength of your password is defined as the number of occurences of the most frequent letter. For example, the strength of icyz is 1 and the strength icpc is 2. You are wondering what is the strength of the strongest password that you can choose.



