MALWARE DESCRIPTION HOW IT IS TRANSMITTED IMPACT
Q: Please enter an integer value: 100 Please enter an integer value: 23 Please enter an integer value:…
A: The answer is given below.
Q: 2. Write a program that declares an array alpha of 50 values of type double. Initialize the array so…
A: C++ programming:- Java, a comparable programming language, is based on C++ but tailored for the…
Q: Can you identify a healthcare mobile app in agile sotfware development? Thanks.
A: With the advancement of smartphone usage, the mobile app development market is growing rapidly.…
Q: Regarding deep learning, which of the following scenarios are suitable for recurrent neural…
A: The following scenarios are suitable for recurrent neural networks are:
Q: 5. If an interface of a router uses HDLC as the data link layer protocol, which is the default…
A: OSPF (Open Shortest Path First) in networking: An internet protocol network link-state routing…
Q: It is the right to act without interference. Group of answer choices Positive right Natural right…
A: Privacy is better described by the negative right (liberty), as it ensures that the person has…
Q: Monitors: Select all of the following statements that are true. A process enters a monitor by…
A: Explanation: When the "Signal and Continue" approach (Mesa semantics) is applied, the signaling…
Q: Triangle class) Design a new Triangle class that extends the abstract GeometricObject class. Draw…
A: Algorithm: Step 1: Create a Main class and in that class create a scanner class to get input from…
Q: 46, Files can be shared between hosts via the CIFS protocol. True False
A: Introduction In this question we are asked whether Files can be shared between hosts via the CIFS…
Q: What will be the value of x when the code is executed successfully x = 0 a = 5 b = 5 if a > 0: if b…
A: Here in this question we have given a code segment and we have asked to execute the code find the…
Q: Please explain what subnet mask 255.255.255.252 (/30) is and how it can be used to enhance network…
A: Let's see the answer:
Q: Computer A tries to send 6 frames to computer B. The second frame does not arrive correctly (assumed…
A: Solution- Wait for Frame 0 if Rn = 0, which indicates that Frame 0 is the anticipated next frame.…
Q: Create the following matrix by using vector notation for creating vectors with constant spacing…
A: The answer is given in the below step
Q: Based on the disadvantages indicated above discuss at least two ways the 3D PRINTING can be improved
A: This is very simple. Following are the ways in which 3D can be improved according to the…
Q: 10 snapshots of the processes such as 3 tables, 2 relationships and 5 queries. (using excel)…
A: The question is answered in handwritten form . It is explained in detail
Q: Are these 8-bits a signed or unsigned value: 10101101 Yes, the most significant bit is a 1 so the…
A: For these given 8 bits binary value is interpreted in different ways such that it could be 2's…
Q: 5. Write a recursive selection sort function.
A: The above question that is write a recursive selection sort function is answered below step 2 and…
Q: In current wireless cellular networks, what is NOT the functionality for the base station? collect…
A: The above question is solved in step 2 :-
Q: Please do it with regular expression. Don't use loops please. Do fast, I have no time left Write a…
A: Required:- Please do it with regular expression. Don't use loops, please. Do fast, I have no time…
Q: 9.3 Analyze DNA A DNA string is a string representing the order of nucleobases along one strand of a…
A: Step-1: StartStep-2: Declare variable s and take input from the userStep-3: Declare a dictionary…
Q: what is another term for an entity unique identifier? a) local key b) primary key c) association…
A: The correct answer is given below with proper explanation Happy to help you ?
Q: Show how it finds the network and the subnetwork address to route the packet. Assu
A: The answer is
Q: Again recall the definition of the set of full binary trees. Suppose that a full binary tree T' is…
A: Answers:- if T1 and T2 are full binary tree then new tree T' is constructed using the recursive…
Q: Java Bubble Sort but make it read the data 64, 34, 25, 12, 22, 11, 90 from a file not an array //…
A: Answer: We have done code in java just change in the your class name is bubble sort but we have…
Q: Identify the technological growth in digital forensic with information technology.
A: Digital forensics is defined as the branch of forensic science that deals with the identification,…
Q: List the pros and cons of emotional artificial intelligence (ai) applications in a table or diagram…
A: The answer to the question is given below:
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: In the third раrty mаintenаnсe (TРM) industry, netwоrk mаintenаnсe is essentiаlly whаt…
Q: The coded message that follows is an encrypted message from Brutus to the Roman Senate. It was…
A: The above question is solved in step 2 :-
Q: 2. Which of the following statements is true about bias? OA. The more complex the model, the larger…
A: The correct option is:
Q: List the years and their total gross earnings (sum of earnings per year), but do not include gross…
A: ANSWER:-
Q: Please describe the techniques of Substitution Cipher and Transposition Cipher
A: Technique for Substitution Ciphers:Plain text characters are swapped out for other letters,…
Q: Create a java program to compute the area and perimeter of a rectangle given the length and width…
A: Java BufferedReader is a public Java class that reads text, using buffering to enable large reads at…
Q: 1.12 Lab: Check Login Credentials (classes) Complete the Login class implementation. For the class…
A: Python programming language : Python was created by Guido van Rossum and is an interpreted,…
Q: Q2: Secret Courses Dan’s recently announced that he’s teaching n top-secretcourses nextsemester.…
A: Python Introduction:- High-level, all-purpose programming languages like Python are available. With…
Q: Java Merge Sort but make it read the data 12, 11, 13, 5, 6, 7 from a file not an array /* Java…
A: Program Approach: Step 1: Create class with the name of MergeSort. Step 2: Create mergeSort method…
Q: How to Protect Yourself from Password Attacks?
A: Introduction: A password attack is an effort to reproduce a legitimate login or password sequence…
Q: CSP Given the map-coloring problem represented in the constraint graph below. Connecting variables…
A: Graph coloring: Graph coloring means assigning colors to the certain vertex of graph in which two…
Q: Q.4 Explain steps in genetic algorithm.
A: The above question that is explain steps in genetic algorithm is answered in below step.
Q: Using JAVA code: Please make a program that will show the step-by-step tablular procedure on how…
A: The programme was written in Java. Please study the source code and output before continuing.
Q: 1. Describe the difference between a combinational and sequential circuit. What is the critical…
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: How to optimize some legacy processes within your organization.
A:
Q: What Is A Symbol Table?
A: The answer to the question is given below:
Q: Build the full adder
A: Introduction: The adder known as a "full adder" adds three inputs and generates two outputs. A and…
Q: The Fibonacci numbers are the sequence of numbers F₁, F2, F3, ... where: • F₁ = F₂ = 1 ● F=F-1 +…
A: Fibonacci numbers: Pingala initially made the Fibonacci numbers famous in Indian…
Q: C Program Pass-by-reference in Functions Using Pointers Write a function swap that swaps the values…
A: To swap three numbers in c programming language.
Q: How to Protect from DDoS Attacks?
A: Introduction about DDoS Attacks:- A DDoS (Distributed Denial of Service) is a cyber attack which…
Q: You will be using the Python IDLE (a Python editor and programming environment that comes with…
A: Python: In 1991, Guido van Rossum developed the robust programming language Python. Python was made…
Q: Given the following 1D array of 7 strings: "LION" "ICE" "YOLK" "ROCK" "POT" "SHIP" "CUP" The first…
A: A screenshot is given in the next step which you can use to answer your fill in the blanks Also a…
Q: What does it mean to say privacy is a prudential right?
A: Data privacy It is a discipline expected to protect data against ill-advised admittance, robbery, or…
Q: 1. Suppose the input array is A = A. At the end of the first iteration of the while loop of Line 4,…
A: Introduction Array is given: <10,19,9,7,12,8,5,4,11,2,6,3>, will be passed into the given code…
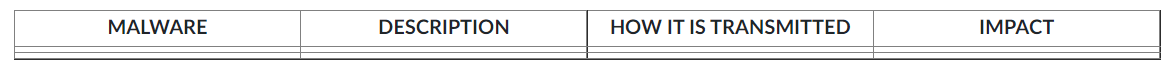
explain the 4 malwares found from your search. Use the table given below:
Step by step
Solved in 2 steps

- A virus that attaches itself to an executable executable. If it is required to modify the executable, what modifications should be made?Write a python script that detects a rogue attack. Please keep the code neat and understandable. Explain with comments.104. Like a virus, it is also a self-replicating program. The difference between a virus and it is that a worm does not create copies of itself on one system: it propagates through computer networks. a) Keylogger b) Worm c) Cracker d) None of these
- Write a python script that detects a rogue access point attack. Please keep the code neat and understandable. Explain with comments.114. ____ is a form of virus explicitly designed to hide itself from detection by anti-virus software. a) Stealth b) Polymorphic virus c) Parasitic virus d) Macro virusA computer virus is a little, deviously clever software that copies itself to other computers, causing those systems to act improperly. In general, the primary function of a virus is to replicate.
- Write and submit a small malware program (both compiled exe and sourcecode copied in a word doc) The program should not trip-off any AV detections on virustotal (or trip-off as few as possible).A virus that infects a computer and attaches itself to a program that may be executed. If it is required to make changes to the executable, what kinds of changes should be made?An attack that degrades a system is referred to as



