Matching Type: Choose appropriate controls with the given possible frauds and errors. - You can choose multiple controls for 1 number of possible errors and controls - controls already answered from preceding number can still be answered for succeeding number.
Matching Type: Choose appropriate controls with the given possible frauds and errors. - You can choose multiple controls for 1 number of possible errors and controls - controls already answered from preceding number can still be answered for succeeding number.
Chapter5: Operating Activities: Purchases And Cash Payments
Section: Chapter Questions
Problem 1M
Related questions
Question
Matching Type: Choose appropriate controls with the given possible frauds and errors.
- You can choose multiple controls for 1 number of possible errors and controls
- controls already answered from preceding number can still be answered for succeeding number.
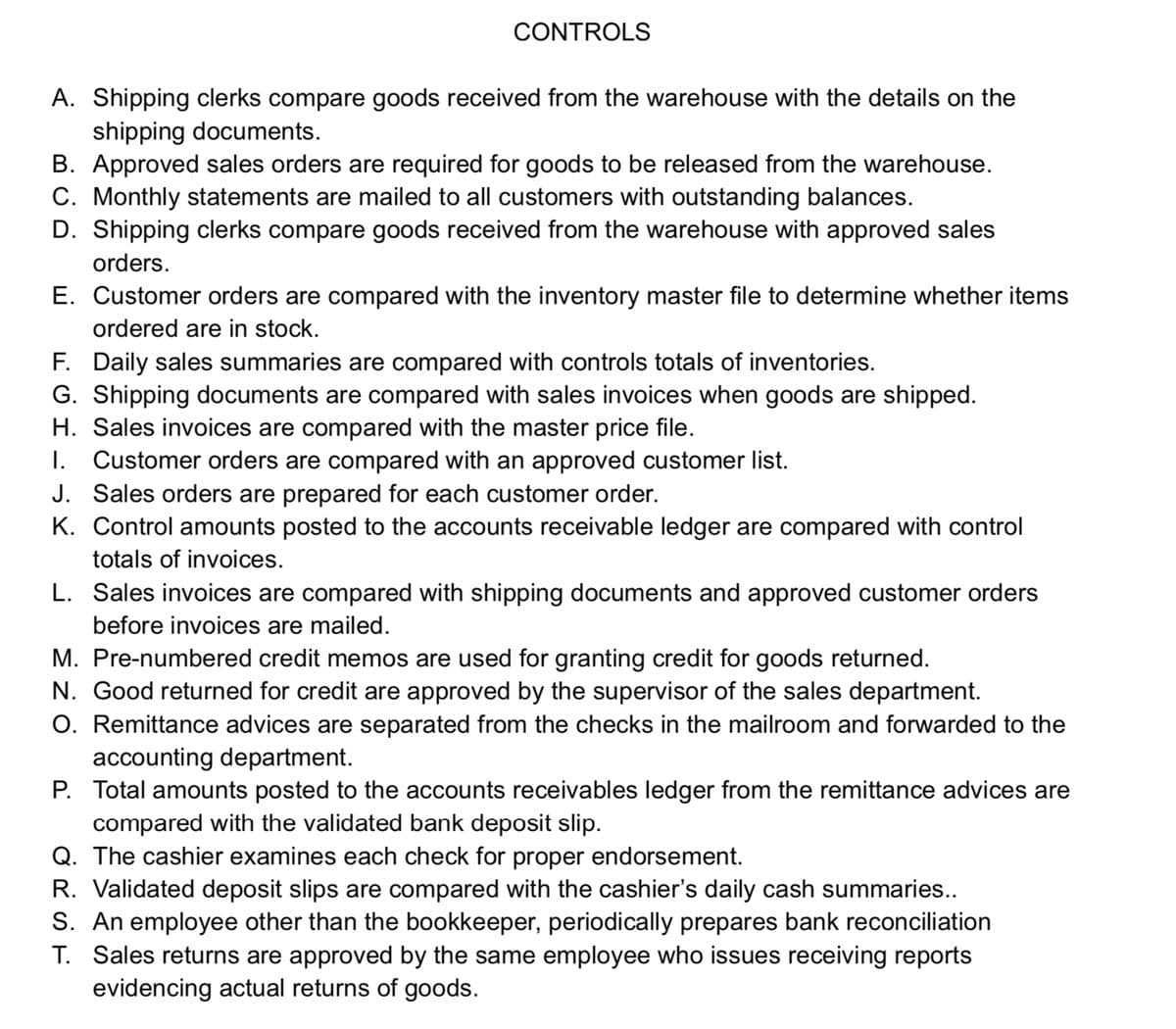
Transcribed Image Text:CONTROLS
A. Shipping clerks compare goods received from the warehouse with the details on the
shipping documents.
B. Approved sales orders are required for goods to be released from the warehouse.
C. Monthly statements are mailed to all customers with outstanding balances.
D. Shipping clerks compare goods received from the warehouse with approved sales
orders.
E. Customer orders are compared with the inventory master file to determine whether items
ordered are in stock.
F. Daily sales summaries are compared with controls totals of inventories.
G. Shipping documents are compared with sales invoices when goods are shipped.
H. Sales invoices are compared with the master price file.
I. Customer orders are compared with an approved customer list.
J. Sales orders are prepared for each customer order.
K. Control amounts posted to the accounts receivable ledger are compared with control
totals of invoices.
L. Sales invoices are compared with shipping documents and approved customer orders
before invoices are mailed.
M. Pre-numbered credit memos are used for granting credit for goods returned.
N. Good returned for credit are approved by the supervisor of the sales department.
O. Remittance advices are separated from the checks in the mailroom and forwarded to the
accounting department.
P. Total amounts posted to the accounts receivables ledger from the remittance advices are
compared with the validated bank deposit slip.
Q. The cashier examines each check for proper endorsement.
R. Validated deposit slips are compared with the cashier's daily cash summaries..
S. An employee other than the bookkeeper, periodically prepares bank reconciliation
T. Sales returns are approved by the same employee who issues receiving reports
evidencing actual returns of goods.
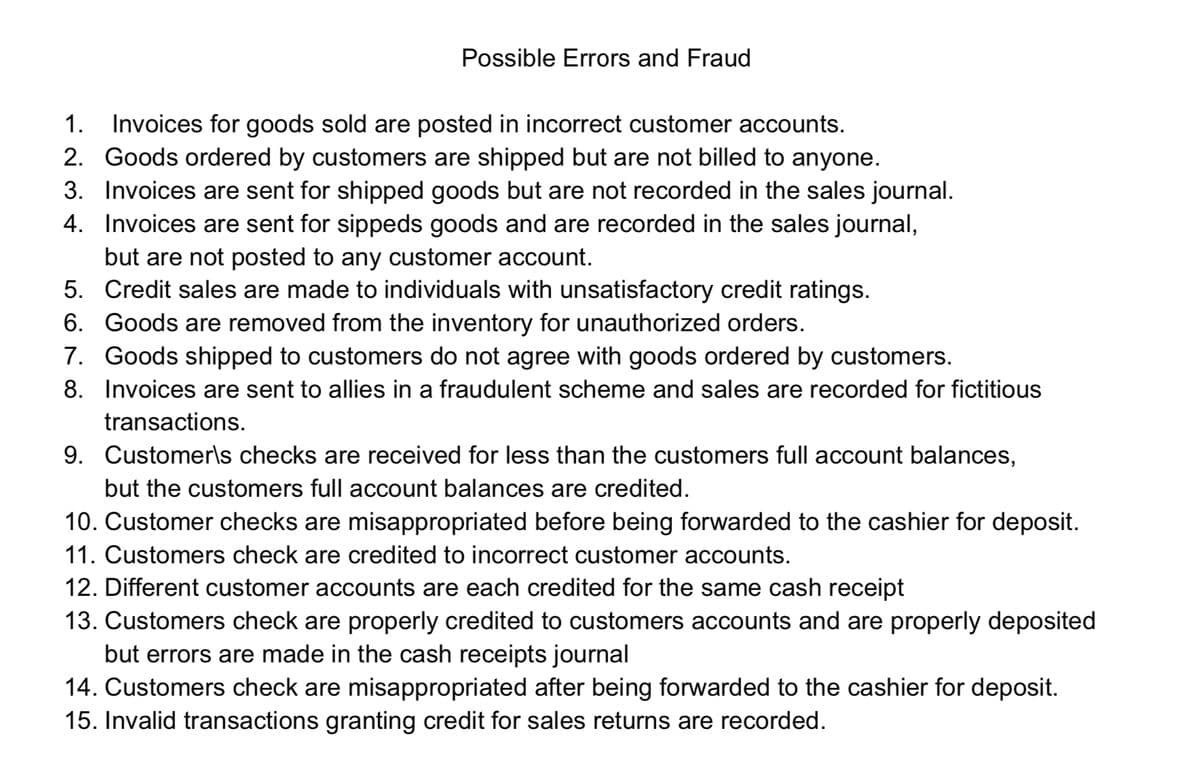
Transcribed Image Text:Possible Errors and Fraud
1. Invoices for goods sold are posted in incorrect customer accounts.
2. Goods ordered by customers are shipped but are not billed to anyone.
3. Invoices are sent for shipped goods but are not recorded in the sales journal.
4. Invoices are sent for sippeds goods and are recorded in the sales journal,
but are not posted to any customer account.
5. Credit sales are made to individuals with unsatisfactory credit ratings.
6. Goods are removed from the inventory for unauthorized orders.
7. Goods shipped to customers do not agree with goods ordered by customers.
8. Invoices are sent to allies in a fraudulent scheme and sales are recorded for fictitious
transactions.
9. Customer\s checks are received for less than the customers full account balances,
but the customers full account balances are credited.
10. Customer checks are misappropriated before being forwarded to the cashier for deposit.
11. Customers check are credited to incorrect customer accounts.
12. Different customer accounts are each credited for the same cash receipt
13. Customers check are properly credited to customers accounts and are properly deposited
but errors are made in the cash receipts journal
14. Customers check are misappropriated after being forwarded to the cashier for deposit.
15. Invalid transactions granting credit for sales returns are recorded.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, accounting and related others by exploring similar questions and additional content below.Recommended textbooks for you

