MC9: In wireless LAN communication, MACA is widely used. In this protocol, in order to avoid collision, a sender can send sender is granted the privilege to send a frame to the receiver only after it receives request signal to a receiver. The replied from the receiver. O RTS, RTS CTS, CTS RTS, CTS CTS RTS
Q: Classify each of the following as a property of TCP or UDP protocols No. Property protocol 1 It…
A: I have provided a solution in step2.
Q: Consider a simple UDP-based protocol for requesting files (based somewhat loosely on the Trivial…
A:
Q: Write a program by c programming language for VLSM calculator Input will be: 1) Input by user -…
A: Given Create a Python program for a binomial series of experiments. The program should ask the user…
Q: router with IP address 125.45.23.12
A:
Q: An IP address can be written as a 32-bit number. For a class B network, the two most significant…
A:
Q: The routing technique FLOODING is used in certain contexts. It means that Group of answer options…
A: Flooding means a data packet arriving through one network interface of a router is forwarded to…
Q: In classful addressing, an IP address 123.23.156.4 belongs to ______ class format. a. A b. B c.…
A: There is one multiple choice question. In this one IP address is given and its class format is…
Q: All dynamic routing protocols make routing decisions that are decided by an a) Central…
A: Here, We have to determine who make routing decisions.
Q: What exactly is routing, and how does it operate in practise? In this essay, we will examine and…
A: Introduction The question is about defining routing and routing methods and here is the solution in…
Q: Suppose Alice with a Web-based e-mail account (such as Gmail) sends it message to Bob, who accesses…
A: Alice-> HTTP ->Web-based mail server-> SMTP-> Mail server for Bob ->POP3 ->Bob.
Q: puter Science: True or False. "With no persistent connections between browser and origin…
A: "With no persistent connections between browser and origin server, it is possible for a single TCP…
Q: Task2: In packet switching technology the packet size is an import parameter when it con o…
A: Bundle exchanging is a technique for moving the information to an organization in type of parcels.…
Q: True or False: [ ] Telephone network is an example of Packet Switching network. [ ] It is the…
A: 1. Telephone network is an example of Packet Switching network. ANS: - False The telephone network…
Q: Write a program to simulate the behavior of the CSMA/CD protocol over Ethernet when ther are N…
A: Actually, CSMA/CD is Carrier Sense Multiple Access with Collision Detection , Which carries…
Q: Write the following Wireshark display filter expressions to dis- play: a) any traffic except with a…
A: Since there are multiple parts in a question so first three parts will be answered. Please upload…
Q: Some application programs can take advantage of the services provided by two transport-layer…
A: Introduction: TCP is a connection-oriented protocol, while UDP is a protocol that is connectionless.…
Q: A subnet mask is a 32-bit number that masks an IP address, and divides the IP address into network…
A: 1) JUMP 2)15.0.0.0 below is the explanation.
Q: Answer the following questions briefly. How does resource reservation work in the TCP / IP model?…
A: Solution is : 1. RSVP is abbreviation for Resource Reservation Protocol. RSVP Resource Reservation…
Q: Answer true or false to the following questions and briefly justify your answer: With the SR…
A: SR protocol Suppose the sender has a window size of 4 and sends packets 1,2,3 and 4 at t0. The…
Q: 10. Suppose a computer sends a frame to another computer on a bus topology LAN. The physical…
A: We need to answer questions related to layers of OSI model or TCP/IP model.
Q: 3.4-6 Cumulative ACK. What is meant by a cumulative acknowledgment, ACK(n)? O A cumulative ACK(n)…
A: Your question is about What is meant by a cumulative acknowledgment, ACK(n)? Let's see the solution…
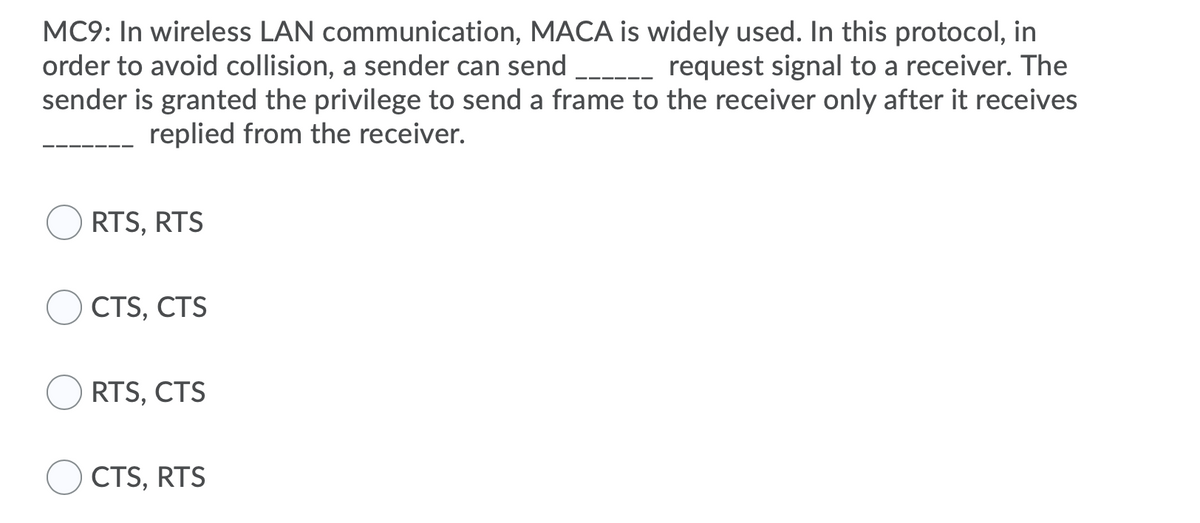
Q: In wireless LAN communication, MACA is widely used. In this protocol, in order to avoid collision, a…
A: Answer:-
Q: Data collision occurs when m which protocols and whose La use these protocols without w
A: There are Multiple access protocol- ALOHA, CSMA, CSMA/CA and CSMA/CD. The data link layer is used to…
Q: A network system has 5 protocol layers. Applications generate messages of length M bytes. At each of…
A: Answer: a. 5h/(5h+M)
Q: Certain application apps may make use of two transport-layer protocols (UDP or TCP). After a packet…
A: The answer :
Q: network. ii. Consider an application that transmits dataiat a steady rate.(for example, the sender…
A: answer : 1.A circuit switched network would be well appropriate for this application. The…
Q: The _______ is the physical path over which a message travels. a. Protocol b. Medium c. Signal d.…
A: Given Mcq:- The ___ is the physical path over which a message travels.a. Protocolb. Mediumc.…
Q: Consider an HTTP 1.1 client and server. The RTT delay between the client and server is 1 seconds.…
A: Basically,know about the RTT stands for the round-trip time taken for an object request and then its…
Q: IPV6 TUNNELING AND ENCAPSULATION Consider the network shown below which contains four IPV6 subnets,…
A: IPv4 and IPv6 are the version of IP protocol. IP stands for internet protocol and IPv4 means…
Q: Packet buffering in Go-Back-N. What are some reasons for discarding received-but- out-of-sequence…
A: Complete answer is below:
Q: Before a packet can be transmitted to a host or router, it must first go via two levels of…
A: Switching of packets: Packet switching is a way of arranging data transferred across a digital…
Q: The UDP protocol is a messaging protocol. Token-based protocols like TCP are known as byte-oriented…
A: Given: The UDP protocol is a messaging protocol. Token-based protocols like TCP are known as…
Q: Create a network consisting of three nodes i.e., Server, PC1, and PC2 (Topology shown in Figure…
A: Introduction: oOMNeT++ is a component-based C++ simulation toolkit and framework that is mostly used…
Q: Suppose Alice, with a Web-based e-mail account (such as Hotmail or Gmail), sends a message to Bob,…
A: POP3: POP3 stands for Post Office Protocol 3 and is a client or server model in which email is…
Q: 4. In one of the pairs of protocols given below, both the protocols can use multiple TCP connections…
A: Correct answer is #1. HTTP: is a request-response protocol used for transporting information…
Q: Suppose the router receives a Protocol Data Unit greater than the next hop's Maximum Transmission…
A: Suppose the router receives a Protocol Data Unit greater than the next hop's Maximum Transmission…
Q: Consider an HTTP 1.0 client and server. The RTT delay between the client and server is 2 seconds.…
A: Given that, RTT (round trip time)= 2 sec Transmission delay= 3 sec Here, the stop and wait protocol…
Q: By using routing, the AS gets rid of the packet as inexpensively as possible. 1) distance vector 2)…
A: By using ____ routing,the AS gets rid of the packet as inexpensively as possible.
Q: Suppose that a mobile device is moving between networks. The home agent has register foreign agent…
A: Option B
Q: Write aprogram to find the ip dotted decimal notation conversion from decimal to binary
A: This is JAVA class to convert IP to decimal: - public class IpConverter { public static void…
Q: uestion 16 /hich of the following is considered a feature of TCP protocol? A Point-to-Point B…
A: TDP and UDP are the two protocols used for communication. These are the communication protocols,…
Q: Answer true or false to the following questions and briefly justify your answer: With GBN, it is…
A: Global Benchmarking Network (GBN) GBN uses cumulative acknowledgement in which it starts an…
Q: When using HTTP streaming, are the TCP receive buffer and the client's application buffer the same…
A: The Answer for the given question is in step-2.
Q: A workstation uses the HTTP protocol to download a large file from a web server. No proxy server is…
A: C. The router sends an ICMP link congested message to the server.:- It depends on Internet Control…
Q: Question 2 Routing refers to determining the route taken by packets from source to destination, and…
A: Given that true/ false question so we provide both true and false explanation.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- UDP Echo ApplicationA UDP Echo program is a simple network application that demonstrates the basicprinciples of UDP communication. In this program, a server listens for incoming UDPpackets from clients, and when it receives a packet, it echoes (sends back) the samepacket to the client. The client sends a message to the server, and the server returns thesame message. It's often used for testing network connectivity and understanding thefundamentals of UDP communication. (Answer the following question using python) Implement both the server and client components of this UDP Echo program whileadhering to the features outlined below. Please ensure that your implementation followsgood coding practices and provides clear prompts and feedback to the user, making ituser-friendly and robust. Please refer to the class example to guide your implementation. 1) UDP Echo Server Receiving and Displaying Messages: The UDP Echo server should be able toreceive messages sent by clients. For each…14.Which one is true for Go-Back-N protocol ? In case of errors, receiver sends negative acknowledgement for the packet with error. There is no buffer area in the receiver The packets reach to the receiver without any errors. The packets are received in the order that they send1. It is a protocol for encapsulating data packets that use one routing protocol inside the packets of another protocol. 2. It is a hash function that has been deprecated for uses other than as a non-cryptographic checksum to verify data integrity and detect unintentional data corruption. 3. An algorithm which is a pseudorandom function family in that it can easily generate arbitrary portions of the keystream without having to start from the beginning. 4. What is the most popular and widely implemented flavor of STP? 5. An algorithm that comprises of a series of linked operations, some of which involve replacing inputs by specific outputs (substitutions) and others involve shuffling bits around (permutations). 6. It is calculated using port cost values associated with port speeds for each switch port along a given path in STP 7. A proprietary architecture that authenticates users and devices using the identity-enabled network approach, and enables the government workforce to connect…
- There are 4 routers Router A, B, C and D Router B and D are connected in a network system, RIP is the routing protocol running on the routers, DV(distance vector) algorithm is the routing algorithm for RIP, a new link is added to the system to conect router A and C, will this addition trigger router A to re-compute its DV?Consider a node called A that sends packets to an adjacent node called B. To control the packet flow to node B, node A employs a credit manager scheme in which parameters C=3(credits), C_max=4(credits) and \tao=6(msec), respectively. node A has an infinite buffer to temporarily store packets. When a packet arrives at node A, node A stores the packet at the bottom of the buffer. Node A also has a single server (transmitter). As soon as the server becomes idle, the server picks up a packet at the head of the buffer, if any, and serves the packet for packet transmission time T_p as far as there remains a credit. (The packet transmission time T_p = 4 (msec).) We observed the arrival times of the first 12 packets, denoted by aA(1)⋯A(12), which were as follows: n A(n) 1 0.5 msec 2 1.0 3 1.5 4 2.0 5 4.5 6 5.5 7 6.5 8 12.5 9 13.0 10 13.5 11 14.0 12 14.6 1. Let R(n) denote the departure time of the n th packet from the buffer for n∈{1,2,...}. Find R(n) for…In a bit-oriented link-layer protocol, the start and end of a frame are each marked by a flag, which is a sequence of exactly 6 consecutive 1 bits. Bit stuffing is used during the rest of the frame: after sending 5 consecutive 1 bits, a 0 is added. The bits below contain an example frame, with the leftmost bit received first. The content of the frame is a sequence of bytes, sent most significant bit first. Put the values of the first four bytes of the frame content, in order, in the four answer boxes below. You may enter the values in either decimal (e.g. 76, 123) or hexadecimal (e.g. 2a, f7). 00101011111010001111110011100111110000111101111101010110100010010011111101101100100 57−240−123−229
- 22. A datagram subnet allows routers to drop packets whenever they need to. The probability of a router discarding a packet is p. Consider the case of a source host connected to the source router, which is connected to the destination router, and then to the destination host. If either of the routers discards a packet, the source host eventually times out and tries again. If both host-router and router-router lines are counted as hops, what is the mean number of a. (a) hops a packet makes per transmission? b. (b) transmissions a packet makes? (c) hops required per received packet?22. A datagram subnet allows routers to drop packets whenever they need to. The probability of a router discarding a packet is p. Consider the case of a source host connected to the source router, which is connected to the destination router, and then to the destination host. If either of the routers discards a packet, the source host eventually times out and tries again. If both host-router and router-router lines are counted as hops, what is the mean number of a. (a) hops a packet makes per transmission? b. (b) transmissions a packet makes? c. (c) hops required per received packet?The usage of static routing has been met with opposition for several reasons, but which of the following is NOT one of them? O. Extra hardware or bandwidth is unnecessary. O.b. The routing tables are modest in size, need just occasional attention. Any alteration to the topology will, of course, have consequences for the setup. The path to the destination never deviates from that one.
- ABC Company needs to deploy an application through which incoming TCP packets are to be scrutinized according to the content type and the payload information it carries. While content types are explicitly available through the flag, payload contents are to be read and sorted. To sort this incoming TCP packets payload, identify the method and sort the payload accordingly. Imagine the inputs accordingly. Write a Code Using JAVA STREAM FILTERAnswer true or false to the following questions and briefly justify your answer: With the SR protocol, it is possible for the sender to receive an ACK for a packet that falls outside of its current window.In this programming assignment, you will implement a decentralized peer-to-peer network architec-ture (P2P), including the basic implementation of the BitTorrent protocol (BTP). General P2P architec-tures can be classified into centralized and decentralized, In P2P centralized architectures, new peers senda request to the Traker (normally done via HTTP) requesting a list containing all the IP addresses ofthe peers that are already connected to the P2P network sharing the same file. The tracker then, replieswith a response containing such list. In P2P decentralized architecture, each peer is also a Traker, and itcan share only limited resources because it only sees the partial network. On the other hand, P2P decen-tralized networks avoid single point of failure since they do not depend of centralized trackers. Examplesof P2P applications that are/were implementing centralizing architectures are Nasper, the Berkeley OpenNetwork Infrastructure (BOINC) and some versions of BitTorrent.…



