Mr. White and Pinkman earned money from their first drug contract. There is an N type of dollar such as A1, A2, A3...... An, each value is different. They have an argument about money sharing. So they decide to throw a coin in order to decide who gets the first choice If the head (H) appears then Mr. White will get a chance to vote first and then Pinkman if not when he says Tails (T) it is time for Jessy Pinkman to vote first and then Mr. White. Each person will select the dollar value in his or her time and the person will not be able to select a dollar note that has already been used. This will continue until all the dollars are allocated between them and in each election, they will throw a coin to decide. You should find the one who receives the extra portion of the money and its value.
Mr. White and Pinkman earned money from their first drug contract. There is an N type of dollar such as A1, A2, A3...... An, each value is different. They have an argument about money sharing. So they decide to throw a coin in order to decide who gets the first choice If the head (H) appears then Mr. White will get a chance to vote first and then Pinkman if not when he says Tails (T) it is time for Jessy Pinkman to vote first and then Mr. White. Each person will select the dollar value in his or her time and the person will not be able to select a dollar note that has already been used. This will continue until all the dollars are allocated between them and in each election, they will throw a coin to decide. You should find the one who receives the extra portion of the money and its value.
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter17: Markov Chains
Section: Chapter Questions
Problem 12RP
Related questions
Question
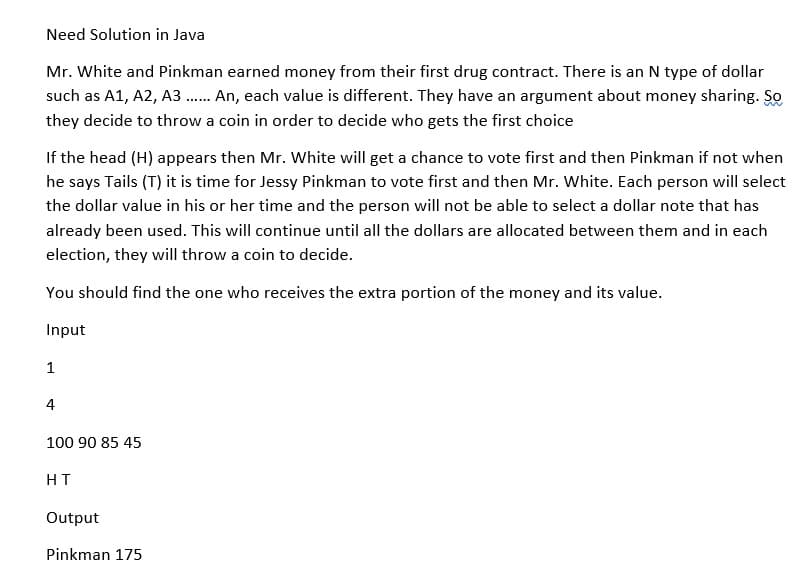
Transcribed Image Text:Need Solution in Java
Mr. White and Pinkman earned money from their first drug contract. There is an N type of dollar
such as A1, A2, A3 ...... An, each value is different. They have an argument about money sharing. So
they decide to throw a coin in order to decide who gets the first choice
If the head (H) appears then Mr. White will get a chance to vote first and then Pinkman if not when
he says Tails (T) it is time for Jessy Pinkman to vote first and then Mr. White. Each person will select
the dollar value in his or her time and the person will not be able to select a dollar note that has
already been used. This will continue until all the dollars are allocated between them and in each
election, they will throw a coin to decide.
You should find the one who receives the extra portion of the money and its value.
Input
1
4
100 90 85 45
HT
Output
Pinkman 175
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole