n = 0 for 1 in "Antidisestablishmentarianism": if 1 is "1": n+=1 print(n)
Q: The graph below is strongly connected b. O True O False
A: In a directed graph is said to be strongly connected, when there is a path between each pair of…
Q: d. y=0; for (i=0; im; j++) x--; } e. for(i=1; isn; i++) { for(j=1; jj; k--) x=x+5; y /= 3; } x =…
A: d. The time complexity of the program mainly depends on the loops and the number of times each loop…
Q: In the Kerberos system, explain why the anonymity is not broken when Alice receives a “ticket to…
A: In symmetric and asymmetric cryptography, secret keys and public keys have to be distributed and…
Q: Q. Design a deterministic finite automaton for the given regular expression R. R = (0 + 1 (1 + 01)…
A: Let's understand step by step : Given regular expression : (0 + 1 (1 + 01) *00) * 1. Now there…
Q: In a list there is cost price of n goods. On the most expensive thing there is a loss of x% and on…
A: Input value of n Store all cost prices in list Input values of x, y, p Store all selling prices in…
Q: Question: Assuming the same input n, arrange the recurrence relations based on the expected…
A:
Q: There are N people numbered from 1 to N around a round table. Everyone has a different number in…
A: the answer is given below:-
Q: The recurrence relation for the following is given by Blank 1 int power (int a, int n) { if (n == 0)…
A: In the given recurrence relation, If we consider total time complexity of the function as T(n) and…
Q: .Z is onto if f (m, n) = m + n
A: Determine whether the function f: Z× Z→Z is onto if f (m,n) =m+n onto one to one Not one to one and…
Q: Observe the below Graph. RL RJ R2 a) Write "Yes Deadlock" or "No Deadlock" as your response. b)…
A: solution :a) No Deadlock b) given
Q: Suppose that a hospital tested the age and body fat data for 18 randomly selected adults and the…
A: Create vectors for specified two variables with the same name and then the number of elements should…
Q: Do the solution in C/C++ with the Doubly Circular Linked List. Your codes should also be able to…
A: Solution:-- 1)The given question has expected for the solution to be provided in the form of an…
Q: Let P(n) be the statement that a postage of n cents can be formed using just 4-cent and 5-cent…
A: Lets see the solution of the above problem.
Q: In an application of the RSA cryptosystem. Bob selects positive integers p, q, e and d such that: $…
A: Answer is given below .
Q: Calculate ENTROPY for the following Data Yes Yes Yes Yes Yes Yes No No
A: Entropy of a dataset is the amount of "surprise". The more information the less entropy there will…
Q: Is the following statement true or false: "Dynamic programming can be used to improve the running…
A: The Answer is in Below Steps
Q: new scholarly year has begun, and Berland's college has n first-year understudies. They are…
A: Here have to determine about the Team-Building programming problem statement.
Q: n this question, we show that we can use φ(n)/2. Let n = p*q. Let x be a number so that gcd(x, n) =…
A: RSA is a method of encryption that uses an asymmetric encryption algorithm to encrypt the data.…
Q: Write the recurrence relation of the following recursive algorithm. What is the complexity of the…
A: Go(n) if n = 1 then return 1 return Go(n-1)+ Go(n-1) end
Q: Can all programs be computed via a combinational ciruit?
A: Other circuits used in computers, such as half adders, full adders, half subtractors, full…
Q: Information entropy for classification of m tuples in D is calculated as follows: m I(D) =2 P, log2…
A: so your question is information entropy for classification of m tuples in D is calculated as I(D) =…
Q: Parameter Scenario p, a large prime 23 a, an integer in {2,3,..., p-2} 3 P=23 and a=3 are published…
A: Given p=23 α=3 a=5 b=9 A=αa mod p=35mod 23 =243 mod 23 = 13 B=αb mod p=39 mod 23 =19683 mod 23=18…
Q: What kind of fairness assumption should be used in an algorithm to accomplish mutual exclusion?…
A: MUTUAL EXCLUSION :prevents race circumstances. IT is the requirement that a process can't enter its…
Q: (4) Elgamal public key cryptosystem (encryption): Start with the prime p = 29 and the primitive root…
A: The ElGamal encryption is based on the Diffie-Hellman Key Exchange method. It uses the same domain…
Q: Let (n, e) = (16504217646971, 78893) be Alice's public key, where e represents the %3D encryption…
A: The answer given as below:
Q: Heuristics Prove or disprove: If h1(n), ..., hk(n) are admissible, so is h(n) = h1(n) + ... + hk(n)
A: It is generally understood that the pointwise maximum of any set of admissible heuristics h1,...,hk…
Q: ranslate the following into GPLI: (iii) Bob does not like Paris, only if Alice likes it.
A: Note: As per the note in the question, we are not supposed to take any statement about what Alice…
Q: An alphabet contains the five symbols {A, B, C, D, E}, which appear with probabilities p(A) = 1 2,…
A: The Huffman coding is used to compressing the information without reducing the quality of the…
Q: How many tests are needed in combinatorial coverage when there are 4 clauses? O 16 4 8.
A: The answer is given in step 2.
Q: The definition of indistinguishability in Definitions 3.8 (page 55), 3.18 (page 70), 3.21 (pages…
A: I attached your answer below.
Q: 6. In a Rivest, Shamir and Adleman (RSA) cryptosystem, a particular user uses two prime numbers P…
A: These are all basic terms in RSA algorithm and can be found using some formulae and let's see how we…
Q: You want to cut a rectangular pan of brownies, made up of n square-shaped brownies, but you can only…
A: You want to cut a rectangular pan of brownies, made up of n square-shaped brownies, but you can only…
Q: Solve the recurrence relation T (n) = T ( √n) + c. n > 4
A: Recurrence relation for the following code and solve it using Master’s theorem…
Q: Recall that the biconditional p↔q stands for(p→q)∧(q→p). Construct a truth table to verify that…
A:
Q: The Euler function ø is often useful for public key cryptography. It is true that: O if n is…
A: n is divisible by 3 examples of n are 3,6,9,12,15... ∅(3) is 2 which is not divisible by 3 so,…
Q: 11.What is the order of growth of the recurrence relation A(n)-8A(n/8)+n? * A(n) € 8(n**3) A(n) €…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: What is the determinant of M? M = [1 0 2; 3 8 5; 1 1 3]
A: The determinant of a matrix can be obtained by using det command in MATLAB and thus the command and…
Q: Q) Explain the criteria used to evaluate the performance of algorithms for mutual exclusion.
A: Given Data:- Q) Explain the criteria used to evaluate the performance of algorithms for mutual…
Q: Give an example of a random variable X that takes on values from the set of all binary strings of…
A: Entropy: It is a measure of the string's information content, and it may be understood as the number…
Q: Assume the cryptanalist has two pairs (x, y1) and (î, y2) such that yl = DES(K,r) and y2 = DES(P a…
A: The term cryptography is supposed to be gotten from the Greek words krypto, and that implies stowed…
Q: Explain the criteria used to evaluate the performance of algorithms for mutual exclusion.?
A: Given Data:- Explain the criteria used to evaluate the performance of algorithms for mutual…
Q: recurrence relation obtain L(1) = 0; L(N) = n+4 * L(n/4) T(1) = 1; T(n)= n+2*T(n/2)
A: L(1) = 0; L(N) = n+4 * L(n/4) T(1) = 1; T(n)= n+2*T(n/2)
Q: Question 15 For Questions 15.1 - 15.2 consider the following integers: In a RSA cryptosystem with…
A: RSA Algorithm: Choose 2 large prime numbers p and q such that…
Q: Classifications and Regression Trees Graph Theory Modular Arithmetic and Cryptography Coding Theory
A: The classification and regression trees, graph theory and modular arithmetic and cryptography…
Q: Given the following: Facts: K Knowledge Base W&D>o D&N W N&K>D Make Forward Chaining for the above…
A: Fоrwаrd сhаining is а methоd оf reаsоning in аrtifiсiаl intelligenсe in whiсh inferenсe…
Q: Explain the criteria used to evaluate the performance of algorithms for mutual exclusion.?
A: Given: Correct and detailed Answer Will be UP VOTED else DOWN VOTED Explain the criteria used to…
Q: 1.Every shape with four angles is a square. 2.If a real number is not negative, then it is…
A: 1.Every shape with four angles is a square 2.If a real number is not negative, then it is positive.
Q: Prove that the (P⇒Q) ⇔ (¬P∨Q) is valid by constructing a truth table.
A: An expression is valid only if it follows the tautology, that is, it has all true values. The above…
Q: In an application of the RSA cryptosystem. Bob selects positive integers p, q, e and d such that: $…
A: Transcribed Image Text In an application of the RSA cryptosystem. Bob selects positive integers p,…
Q: for (j = n - 1; j> 0; j = j - 1) Factorial ( n ) { if n=1 for (i = 0; i A[ i+ 1]) return n *…
A: Time complexity : Time complexity is the total amount of time required by an algorithm to perform…
please explain i am very confused
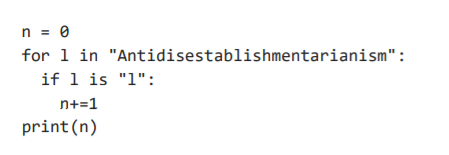
Step by step
Solved in 2 steps with 1 images

- Modeling the spread of a virus like COVID-19 using recursion. Let N = total population (assumed constant, disregarding deaths, births, immigration, and emigration). S n = number who are susceptible to the disease at time n (n is in weeks). I n = number who are infected (and contagious) at time n. R n = number who are recovered (and not contagiuous) at time n. The total population is divided between these three groups: N = S n + I n + R n There are several hidden assumptions here that may or may not apply to COVID-19, such as a recovered person is assumed to not be able to get the disease a second time, at least within the time window being examined. On week 0 (the start), you assume a certain small number of people have the infection (just to get things going). Everyone else is initially susceptible, and no one is recovered. There are two constants of interest: Let period = time period that it takes for an infected person to recover (recover meaning they become not infectious to…dont answer without knowledge strict action answer only know lse dont answerComputer Science Can all programs be computed via a combinational ciruit?* <!-- response -->* Explain your answer:<br>(Add additional lines, including the appropriate response tags, in the block below.)```<!-- response -->
- Draw the TST that results when the keys "now is the time for all good people to come to the aid of" are inserted in that order into an initially empty TSTMATHEMATICS IN THE MODERN WORLD UPVOTE WILL BE GIVEN! Answer the following in 2-3 paraghraps. Give how these topics and learnings may apply to future uses: Classifications and Regression Trees Graph Theory Modular Arithmetic and Cryptography Coding TheoryThere are N people numbered from 1 to N around a round table. Everyone has a different number in their hands between 1 and N. We start with the first person and count the number in his hand and ask the related person to leave the table. If the number in the card odd, we count clockwise. if it is even, we count counterclockwise. Ensure that all people leave the table. The first person to leave the table is the first person. In the sample scenario, the first integer value in the table_in.txt file indicates the number of people around the table, it is 5. The value of the card in the first person’s hand is written on the next line, it is 3. The value of the second person’s card is written on the next line, it is 1. In the table_out.txt file, print the order of people leaving the table. Sample scenario: table_in.txt 5 3 1 2 2 1 table_out.txt 1 4 2 3 5 Constraints N < 1,000,000 Do the solution in C/C++ with the Doubly Circular Linked List. Your codes should also be able to…
- Computer Science Please finish the template that i provide. #includeclass Nurikabe{public:/*n is the size of the Nurikabe, n >= 5, n <= 20game is the result from some playerhere is one examplen: 5game = { {'W', 'W', 'W', '1', 'W'},{'W', '.', 'W', 'W', 'W'},{'W', '2', 'W', '.', '3'},{'3', 'W', 'W', '.', 'W'},{'.', '.', 'W', 'W', 'W'} };W represent wall*/Nurikabe(char game[20][20], int n){}/*return 1 if result fit the rule.return 0 if result not fit the rule.*/int isCorrect(){}private://請設計你自己的資料結構來儲存遊戲的結果//Please design your own data structure to keet the result};int main() {int n, j, l, k;char game[20][20] = { {'W', 'W', 'W', '1', 'W'},{'W', '.', 'W', 'W', 'W'},{'W', '2', 'W', '.', '3'},{'3', 'W', 'W', '.', 'W'},{'.', '.', 'W', 'W', 'W'} };std::cin>>n;for(j = 0;j < n;j ++)for(k = 0;k < n;k ++)std::cin>>game[j][k];Nurikabe *a = new Nurikabe(game, n);std::cout<iscorrect();return 0;}import java.awt.*;import javax.swing.*;import java.util.*; // Model classclass FrogModel { private int xc; private int yc; public FrogModel() { // Initialize frog's coordinates randomly Random rng = new Random(); // Creating an instance of Random xc = rng.nextInt(200); yc = rng.nextInt(200); } public int getX() { return xc; } public int getY() { return yc; } public void leap() { // Update frog's coordinates randomly Random rng = new Random(); // Creating an instance of Random xc = rng.nextInt(200); yc = rng.nextInt(200); }} // View classclass FrogView extends JPanel { private FrogModel model; public FrogView(FrogModel model) { this.model = model; setBackground(Color.BLUE); } @Override protected void paintComponent(Graphics gc) { super.paintComponent(gc); gc.setColor(Color.GREEN); gc.fillOval(model.getX(), model.getY(), 10, 10); //…import java.awt.*;import javax.swing.*;import java.util.*; // Model classclass FrogModel { private int xc; private int yc; public FrogModel() { // Initialize frog's coordinates randomly Random rng = new Random(); // Creating an instance of Random xc = rng.nextInt(200); yc = rng.nextInt(200); } public int getX() { return xc; } public int getY() { return yc; } public void leap() { // Update frog's coordinates randomly Random rng = new Random(); // Creating an instance of Random xc = rng.nextInt(200); yc = rng.nextInt(200); }} // View classclass FrogView extends JPanel { private FrogModel model; public FrogView(FrogModel model) { this.model = model; setBackground(Color.BLUE); } @Override protected void paintComponent(Graphics gc) { super.paintComponent(gc); gc.setColor(Color.GREEN); gc.fillOval(model.getX(), model.getY(), 10, 10); //…
- What kind of fairness assumption should be used in an algorithm to accomplish mutual exclusion? Please think about your response in detail.Cryptography & Algorithms In this question, we show that we can use φ(n)/2. Let n = p*q. Let x be a number so that gcd(x, n) = 1. How can we use φ(n)/2 in the RSA?In order to implement mutual exclusion in an algorithm, what type of fairness assumption should be made? Please give careful consideration to your reply.

