Name * Enter your name Address Enter your address Email * Enter your email Subject Type the subject Message Type your message here... Phone Enter your phone number Submit
Q: Simply said, disk prefetching is exactly what it sounds like. What are the positive and negative…
A: INTRODUCTION: Cache memory is computer memory that is tiny in size and volatile. It holds frequently…
Q: Do yourself a favor and print off a duplicate of update.txt just in case you lose track of its…
A: To Determine File Location: If you know the file's name but not its position, you can use the…
Q: Post-delivery adjustments are those made to a software product after it has already been released to…
A: Put the following system to use: A software product may be modified after it has been delivered in…
Q: Create a Python program that uses the Pool object and the multiprocessing function to spawn 10…
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT-------------
Q: version of the software becom
A: Software is an integral part of modern life. It powers everything from the smartphones we use to the…
Q: Exploit the following code testuser@kali:~$ cat vuln1.c #include #include int main(int argc,…
A: -p linux/x86/exec specifies the payload to use, which is a Linux/x86 shell that will execute…
Q: There are three conditions that need to be satisfied for a network to function optimally. Please use…
A: 1) A network is a collection of computers and servers, mainframes, network devices, peripherals, or…
Q: 5. Convert the following high-level code into RISC-V assembly language. Assume that the signed…
A: Please note that as per bartleby standards if multiple questions are posted then only the first…
Q: Virtual machines may be run off of computer hard disks (VMs). Why would you use a virtual machine…
A: Introduction :- As comparison to physical machines, virtualization has many advantages, including…
Q: What's the dissimilarity between a splitstream update, patch, release, and version in terms of…
A: In the context of software maintenance, the terms "splitstream update," "patch," "release," and…
Q: For security purposes, what medium is utilized to keep secret codes? Websites, compact discs, and…
A: According to the information provided, we must specify the kind of storage where encrypted passwords…
Q: The fundamental capabilities of Phases of Compiler are as follows. If you could define each step and…
A: Phases of compilation: Steps begin with a source program and end with an output program. Each level…
Q: Please provide the top six reasons why you want to learn about compilers.
A: Introduction: Compilers: A coder alters a program's language or type. Assembly code, C code, or…
Q: Modify the following program to read dictionary items from a file and write the inverted dictionary…
A: In Python, a dictionary is a data structure that is used to store key-value pairs. Dictionaries are…
Q: include include nt main() id.t pid; /* fork a child process */ pid = fork(); if (pid < 0) { /*…
A: The code is a basic implementation of a process forking and waiting for the child process to…
Q: Provide an illustration of the meanings of the following terms: ready-made software and tailor-made…
A: Off-the-shelf software is essentially a standardised, mass-produced, reasonably priced, and…
Q: Do you know what options you have for the evolution of your legacy systems? When will it be more…
A: Introduction: Legacy systems are software applications that have been in use for a long time and are…
Q: Many operating systems have different methods of understanding virtual machines. Argue your side of…
A: In this question we have to understand and provide argument on "Many operating systems have…
Q: I was wondering whether you were familiar with the many applications of SSH. Why don't you just go…
A: Here is a list of commonly used SSH acronyms and their meanings: SSH - Secure Shell: A protocol…
Q: Function Name fibonacci palindrome sumEven fullName stringLength largestNum any_recursive Task ask…
A: We have to create a program which will ask the Function Name- fibonacci…
Q: Write a class named Book that has the following data members: - title :: A string that holds the…
A: here are the codes: Book.h #ifndef BOOK_H#define BOOK_H #include <string> class Book…
Q: What sets apart computers and their components?
A: Your answer is given below.
Q: In this exercise we examine in detail how an instruction is executed in a single- cycle datapath.…
A: Arithmetic Logic Unit: ALU stands for Arithmetic Logic Unit, which is a digital circuit that…
Q: Are you familiar with the many applications of the SSH protocol? Are you interested in compiling a…
A: The answer is given in the below step
Q: What kinds of technological means (hardware and/or software) does the workflow management system…
A: Workflow management systems (WfMS) typically employ a range of technological means, including…
Q: Given a square matrix of size ?×?�×� that only contains integers, compute the sum of the two…
A: The task is to write a function in Python using NumPy library that takes a square matrix of size n x…
Q: A nutshell description of what makes up the "kernel" of an OS.
A: The kernel is the core component of an operating system (OS) that manages system resources, provides…
Q: Walk me through the steps of a failsafe strategy. How does the security of data on mobile devices…
A: Introduction: Backup plan parts. To avoid data loss, have a backup plan. In the case of a server…
Q: Is the new method for erasing files only applicable to certain operating systems?
A: On Symbian, Android, and the iPhone, the method for erasing files is the same. These operating…
Q: There are a number of techniques for doing forensic analysis on Windows files, including those…
A: The question is asking about the various methods or approaches used to analyze Windows files,…
Q: Specifically, what characteristics distinguish a client computer from a server computer?
A: A network computer that shares resources with other computers is known as a server. A client…
Q: Problem 3. Binary Tree Q4. Given the binary tree on the picture, match the following questions with…
A: The answer is given below for the above given question:
Q: When it comes to Compiler Phases, how well versed are you on the fundamentals? Instances of each…
A: The various steps in the conversion of source code into executable code are referred to as compiler…
Q: Why do different OSes have to be separated into different categories?
A: Your answer is given below.
Q: The CPU will stop whatever it is doing to deal with the signal. This case employs the following…
A: Introduction :- Spooling signals for interruptions is a technique for handling interrupts or signals…
Q: When we say "distributed computing," what do we mean exactly?
A: Distributed computing, also known as distributed processing, is the technique of connecting many…
Q: a SQL query to display the customer ID, name, and order ID for all customer orders. For those…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Explain and show how to work with disks, directories, and files in an operating system.
A: Introduction: Explain and put to use the operating system's processes for generating, reading, and…
Q: The central processing unit (CPU) is at the very core of any computer, but why is that?
A: The administration of all devices and handling of memory access to the device are handled by the…
Q: Can the data-erasing algorithm be used on Symbian, Android, or iOS devices without causing problems?
A: According to the information given:- We have to define the data-erasing algorithm be used on…
Q: While it seems to be a computer, its software really controls the hardware to do the tasks for which…
A: The choice "B" -- "An embedded system" -- is the one that represents the right response to the…
Q: Create a set of use cases for the following health club membership system: Problem: When members…
A: A use case is a description of a specific action or interaction that a user or actor may have with a…
Q: of an efficient network? Spend a moment
A: A well-functioning network refers to a computer network that operates efficiently and effectively,…
Q: What three components does a successful network need to have? There was a brief pause in the action.
A: Introduction: In today's digital age, networks play a crucial role in connecting people and…
Q: Does the IOT temperature monitoring system's introduction and summary make sense?
A: Introduction: The Internet of Things (IoT) has revolutionized the way we interact with technology,…
Q: Create a catalog of the various DNS record types. Real-world examples and rationales for their…
A: Various DNS record types along with real-world examples and rationales for their application. A…
Q: Task 1: Make the program stops after the vehicle passes the signal location by 5 feet. Task 2:…
A: JavaScript is a popular language because of its flexibility, ease of use, and versatility when it…
Q: Can you tell me what batch files are used for and where they could be found on a computer?
A: Batch files are often used to assist in loading applications, running numerous processes at once,…
Q: When comparing SSL and TLS, what are the key distinctions? Can a distinction be drawn between these…
A: SSL: The domain name and browser used SSL security technology. Client and mail client software is…
Q: How similar are containers to virtual machines?
A: INTRODUCTION: Virtual machines: Virtual machines are resource-intensive software packages that…
HL CSS Form 4..
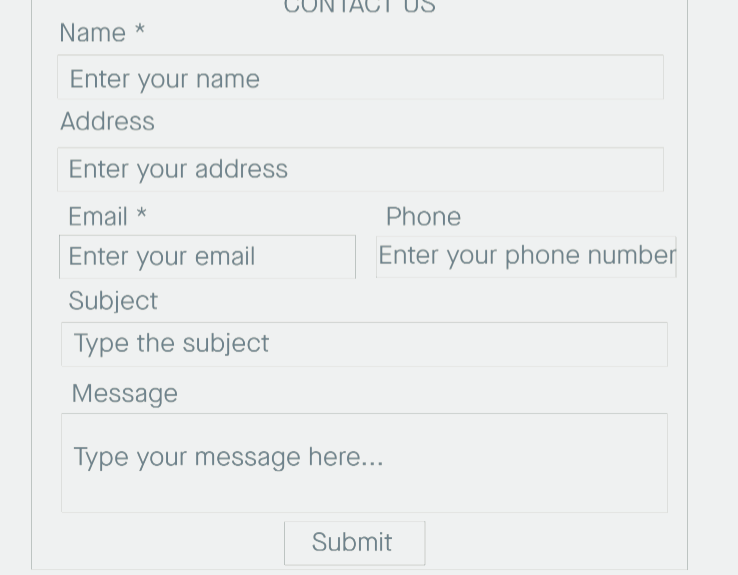
Step by step
Solved in 4 steps with 3 images

- Extract e-mails and passwords from several .txt files from a path to the folder to be searched and rewrite them in a symbolic .txt file : in Python code (do it in Visual Studio Code and run it)Example: hey... email: username+123@example.com, password: 627hsjwu* these are my company's credentials... See you later Now I want to put in a result.txt the email and the password separated by the symbol :need the screenshots of the answer, the screenshots must be taken using the program 'netbeans' please give me answer quick as possible thanks.Question 1BackgroundYou are required to write program that will read a file, encrypt the content of the file, and thencreate a new file that contains the encrypted content.Your program will make use of the following classes:Page – This class will be used to represent the content of the file that was read.PageManager – This class will be used to read page content from and to a file.APM11A1Encryptor – This class will be used to encrypt the content of a file using the Caesar-Ciphermethod.APM11A1 - AdvancedProgrammingAdvancedAPM11A1Encryptor – This class will be used to encrypt the content of a file using theExclusive-OR method.Caesar CipherCaesar was a Roman military and political leader during 100BC to 44BC. In order to make thecommunication channels secure during war, he invented an encryption technique called the CaesarCipher. The cipher requires a sentence and a key to function properly. Each character in the sentencewas then shifted according to the value of the key. Computer…
- Extract e-mails and passwords from several .txt files from a path to the folder to be searched and rewrite them in a symbolic .txt file : in Python code (do it in Visual Studio Code and run it)Example:hey... email: username+123@example.com, password: 627hsjwu*these are my company's credentials... See you later Now I want to put in a result.txt the email and the password separated by the symbol :I have tried it in visual code studio and it doesn't work, can you explain step by step how it works pleaseStep 1I'll talk about the refresh rate in this response. arrow forwardStep 2The number of times your display updates with fresh pictures each second is referred to as the refresh rate. The useable area of the screen is another term for this. Refresh rate is the display standard that deals with the useable area of the screen.Asap please. Can we create an object inside an object in JAVASCRIPT? If yes then write a program to create an object inside another object.
- Create a simple program that will search, add, save and delete student information stored in a textfile. btnSearch – search student information using Student No. and load data in the widgets. btnNew – generate unique student number and clear entries and text values. btnSave – store data in the textfile. btnDelete – delete existing student record using student number.Please help me with this using java. 1) Create a login/sign up page with a place to type up username and password or to create a username and password(Refer to first image) 2) then create a game menu with two clickable buttons play game and instructions. And include a image ( Refer to Second image) then connect them together. The program starts if with the login/sign up page. Once user has entered or create username and password l. It then goes to the game menuprivate OnlineStudent readOnlineStudent(Scanner pIn) { String id = pIn.next(); String lname = pIn.next(); String fname = pIn.next(); OnlineStudent student = new OnlineStudent(id, fname, lname); String fee = pIn.next(); int credits = pIn.nextInt(); if (fee.equals("T")) { student.setTechFee(true); else { student.setTechFee(false); } student.setCredits(credits); return student; keep getting class, interface,enum or record expected. I need help
- create a login and registration page using python and mysqlI got the code but please put proper indentation. The code is in the below link on your website please do proper indentation to this Engineering/Computer ScienceQ&A Library/create a Login and registration page using python and mysql please TYPE the code The one I recieved befor was all imageshttp://dpeled.com/calc_p.asm)1. Save the program into your ASM folder and run it.2.Write a line by line explanation (comments).3.What does the program do? What will be displayed?4. Explain the logic of the program how it achieves its purposeFirst, launch NetBeans and close any previous projects that may be open (at the top menu go to File ==> Close All Projects). Then create a new Java application called "PatternMaker" (without the quotation marks) according to the following guidelines. The program prompts the user for five input values: An integer value between 1 and 10 (inclusive) for the number of rows to be printed A second integer value between 1 and 10 (inclusive) for the number of columns to be printed A string value for the starting string of the pattern A string value for the second string of the pattern A string value that separates the first two strings The program must use nested for loops to print a rectangular array of alternating first and second strings of the pattern, separated by the separator string and such that the first string in the first row uses the "first string" provided by the user, but each subsequent row alternates the starting string between the "second string" the user provided and the…





