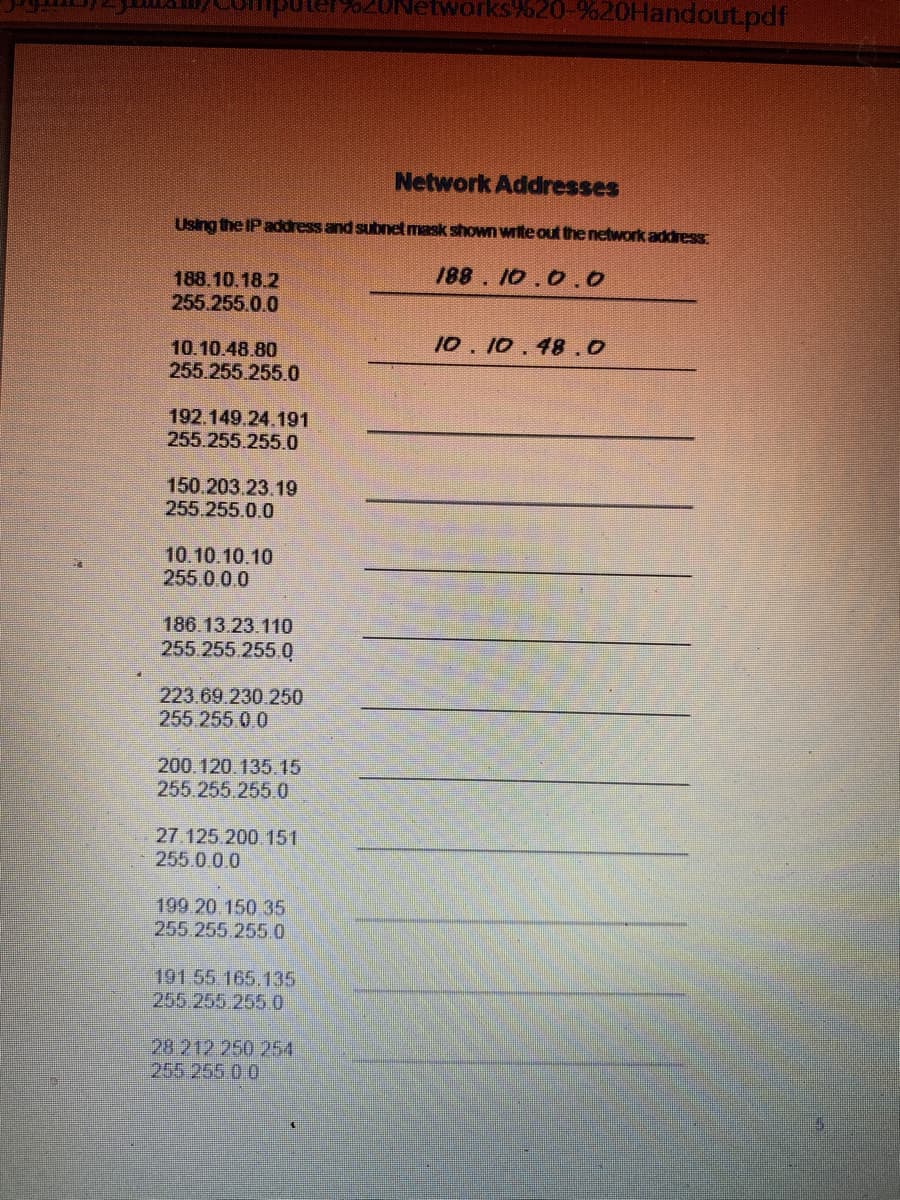
Network Addresses Using the IP address and subnet mask shown write out the network address 188. 10.0.0 188.10.18.2 255.255.0.0 10.10.48.0 10.10.48.80 255.255 255.0 192.149.24.191 255.255.255.0 150.203.23.19 255.255.0.0 10.10.10.10 255.0.0.0
Q: What is the difference between IP address and MAC address for a computer?
A: IP Address: The internet protocol address (IP address) is a numerical identifier that is connected…
Q: An IP address 151.50.50.23 belongs to class C. Is it true or false?
A: IP is an Internet Protocol address of a machine on the computer network. Each machine on the…
Q: 2) Internet Protocol version six (IPv6) addresses are displayed in a) Binary b) Decimal c)…
A: Internet Protocol version six (IPv6) addresses are displayed in Hexadecimal.…
Q: Calculate the physicals address if CS = 105h and IP = 1204h * %3D Choose e unit of address…
A: Solution:
Q: How much do you agree with the statement, "Network address translation is intended to save IPv4…
A: Network address translation (NAT) translates one IP address space to another by changing network…
Q: 2. Show the steps to ping the IP address of another computer
A: Ping on a computer: Ping is a computer system architecture powerful application that checks whether…
Q: a. ARP spoofing b. MAC address flooding C. DHCP spoofing d. DHCP starvation
A:
Q: mum of one Cisco 4321 router, two Cisco 2960 switches, and 5 PCs. Fully configure the network and…
A: Q. Background /Scenario In this Packet Tracer Physical Mode (PTPM) activity, you will design and…
Q: Claflin has a public IP address space that ranges from 98.101.183.0 to 98.101.183.63. What netmask…
A: Task : Range of IP address = 98.101.183.0 - 98.101.183.63 The task is to find the netmask for the…
Q: Configure hostnames and IP addresses on two Cisco Internetwork Operating System (IOS) switches using…
A: Here is the solution for the above problem :
Q: Any protocols or features that are mentioned when an error message reading "404 Not Found" appears…
A: Answer:
Q: 1a) Write a python script using nmap that scans a specified domain or ip address and returns open…
A: PROGRAM CODE: import nmapnmScan = nmap.PortScanner()nmScan.scan('127.0.0.1', '21-443') # run a…
Q: What best describes a non-routable IP address? a. It is not pingable. b. It only exists on the…
A: Answer. It does not exist outside of an internal network
Q: The organization has a Network IP 11.0.0.0/27. Find out the 8099th, 3973th SID, their respective…
A: Dear Student, Here, Network IP 11.0.0.0/27 is a class A ip address. To find the sir we divide 8099…
Q: List at least 10 ways to protect your network from malicious and harmful attacks. Based on your OS,…
A: Introduction: A good network security system helps business reduce the risk of falling victim of…
Q: List port numbers: email, internet, secure shell, ntp, dns, telnet, dhcp, Microsoft remote
A: The list of port address are given below.
Q: MAC address is flat therefore it is _whereas, IP address is hierarchical therefore it is not…
A: Portability of MAC flat addresses - LAN card can be moved from one LAN to another. IP addresses…
Q: steps involved when the user opens their browser and visits the website discord.com
A: Given :- A desktop computer with the IP address 192.168.0.5 is running multiple applications as…
Q: Explain the PKI and PKC as well as X.509 in detail
A: Note:- In the BNED Guidance, only the first question can be answered at a time. Resend the question…
Q: It's important to know the meaning of an IP address and its role in a computer network system
A: IP (Internet Protocol) address: A device on the internet or a local network is identified by its IP…
Q: Computer Science A company recently removed 50 computers that were connected via Cat 5e cables and…
A: Given: Computer Science A company recently removed 50 computers that were connected via Cat 5e…
Q: IP addresses are important for computers to be able to communicate with eachother on the Internet.…
A: Required: Regular expression to accept an IP address. RegEx has been provided in the next step.
Q: ubnet mask of 255.255.240.0. What is the maximum number of hosts it can handle ? a. 1024 b. 2048 c.…
A: Given: A network on the Internet has a subnet mask of 255.255.240.0. What is the maximum number of…
Q: Part II: Relate the devices provided below with their corresponding definition by providing the…
A: Answer : 1) Switch -> Interconnects computers and cabling to form a Local area network. 2)…
Q: What organizations uses Mandatory Access Control (MAC)?
A: Please give positive ratings for my efforts. Thanks. ANSWER MAC is used by the US government…
Q: TRUE or FALSE? In a centralized computer network, the failure of a single machine or…
A: The military desired to create a national communication network to aid in the resistance to the…
Q: (1) A. Using the IP address and subnet mask shown write out the network address: (PLEASE SHOW…
A: Answer : if we do bitwise AND operation for subnet mask and IP address then we will get network…
Q: As Network administrator, you decide to implement a monitoring system that detects any suspicious…
A: Answer : The IDS ( Intrusion detection system ) is the technology which can detect any suspicious…
Q: nternet protocol version 4 ( IPV4 ) Represents each IP address as a 32-bit binary number. Internet…
A: In IPv4, total number of address possible is 232 since IPv4 is 32 bit address IPv6 is 128 bit. So…
Q: a MAC address and a Hardware address? What is the length of a MAC address both in Bits and Bytes?…
A: Difference Between MAC and Hardware AddressA Hardware Address is a 12-digit number that begins with…
Q: 3. The desktop computer with the IP address 192.168.0.5 is running multiple applications What are…
A: Given: To explain how browser works.
Q: Short answer Computer networking What’s the issue with IPv4 addresses?
A: Introduction: Each Internet Protocol network node, such as a device, router, or computer network, is…
Q: tracert 10.10.10.6 nslookup 10.10.10.4 Hardware/MAC IP address Address IP config all
A:
Q: 2(b) There is no IPV6 broadcast address, true or false, explain briefly.
A: Every electronic device compulsorily requires a unique IP Address. Almost all of them can connect to…
Q: Cloud computing. A ____ is a combination load balancer and application server that is a server…
A: Given, Statement: A ____ is a combination load balancer and application server that is a server…
Q: bers should be mentioned. Do you know why it is believed that FTP transmits
A: Introduction: File Transfer Protocol(FTP) is an application layer protocol which moves files between…
Q: List the Address on host 1 on subnet 0,1,2,3,10?
A: Given, Class C IP address = 195.1.1.0 Current mask = 255.255.255.0 Number of bits required for 10…
Q: Question 1. What are MAC addresses?
A: Since you have asked multiple questions , so we have answered first for you. If you want answer of…
Q: 192.168.10.10 255.255.255.O This address and mask example of Select one: O a. IPV6 b. Classful OC…
A: The above address and mask are the examples of subnetting.
Q: PT9.1.3 - Identify MAC and IP Address Put the printscreen of questions no. 1, 9, 12, 13 and 14 1.…
A: 1. Were there different types of cables/media used to connect devices? Ans. Yes, Copper and Fiber
Q: Broadcast address for the given IP address 23.56.7.91 Select one: a. 23.255.255.255
A: Please find the answer below :
Q: Find the class for the given IP address 185.75.255.10
A: IP Addresses are categorized based on the address range into 5 classes and are as follows: Class A…
Q: What are the first 24 bits of a hardware address used for? IP (internet protocol) address Vendor…
A: Answer to the given question: The first 24 bits of a hardware address is used for Vendor…
Q: 802.11 a/b/g/n–WEP, WPA, WPA2, MAC address filtering, SSID broadcast Bluetooth–pairing codes,…
A: I have answer this question in step 2.
Q: O a. DHCP spoofing O b. MAC address flooding O c. DHCP starvation O d. ARP spoofing
A: layer 2 attack does provide wrong default gateway to the end devices
Q: To utilise computers at college, do you need to develop a set of remote access policies?
A: Introduction: A document that discusses and specifies permitted ways of remotely connecting to the…
Step by step
Solved in 2 steps

- 24. In IPV 4, the IP address 200.200.200.200 belongs to a. Class A b. Class B c. Class C d. Class DA network configuration of a modem is given as following:LTE interface IP = 77.110.156.22 MASK 255.255.252.0Default GATEWAY = 77.110.156.1Masquerade NAT, and DNS address = 1.1.1.1Local IP setup: 192.168.128.1 MASK 255.255.255.0And, ip route 192.168.128.0 255.255.252.0 192.168.128.254 Devices numbered R1, R2, R4, R5 are routers. PC is a computer.Image of network with interface names such as f1/0 are added. You must use only static IP addreses and static IP routes to configure the network and make PC able to connect (ping) to Modem.I know this is "broad" for computer science, as this concept is networking based. So, I'm a cybersecurity student, I am good at pretty much everything else but networking in respect to the field (for a beginner obviously) My question is as follows: Basically, I've been given a network with 100 hosts, 50 hosts, and 20 hosts.I've been given an IP address of 172.34.100.0 /17Basically, I've been told to plan out this VLSM and subnet this network, but I have no idea where to start. Can you help me out? Let me know if you require more info, I'd be happy to lend it.
- in the folllowing ip address 141.132.196.33/15 how many bits are allocated to the node portion of the address?Internet protocol version 4 ( IPV4 ) Represents each IP address as a 32-bit binary number. Internet protocol version 6 ( IPV6 ) represents each IP adress as a 128-bit binary number. WHich of the following best describes the result of using 128-bit addresses instead of 32-bit adresses- 4 times as many address are available- 96 times as many addresses are available - 2^4 times as many adresses are avialabe- 2^96 times as many adresses are availableq22- An IP address of 132.192.191.250 with a mask of 255.255.255.248 what is the broadcast address of the subnet in which the IP address is belong to? Select one: A. 132.192.191.255 B. 132.192.191.249 C. 132.192.191.251 D. 132.192.191.248 E. 132.192.191.252
- Find the address in all networks. Subnets =1000. Hosts =60 Address = 165.100.0.0. class- 0 -127 128- 191 Write down the default subnet mask and customized subnet mask. Def = 255.255.0.0 1111 1111. 1111 1111. 1111 1111. 1100 0000 -> 255.255.255.192 2^ 6= valid ip addresses 64 hosts -2 62 hosts 165.100.0.0 - 165.100.0.1 TO 165.100.0.62 165.100.0.63 => 64 165.100.0.64 - 165.100.0.128 165.100.0.192 165.100.0.193 to 165.100.0. 254 165.100.0.255 What is the 10th subnet range? Find the 4th subnet DBA. Determine the assignable addresses for 4th subnet range Give the 15th subnet id and the last host address in the 3rd subnet Give the CIDR notation.True or False (Include valid reason) a) A backdoor is another way into a system or program bypassing the main system authentication. Hence, all backdoors have malicious intent. b) One way to mitigate ARP spoofing attack on a host is to set static IP-to-MAC assignments on its ARP cache.The subnet mask in use on a 10.11.12.0 subnet is 255.255.255.128 (or /25) Select the IP address below that is on the same subnet with 10.11.12.1, 10.11.12.2, and 10.11.12.3 A. 10.11.12.42 B. 10.11.12.130 C. 10.0.0.1 D. no correct answer
- Identify the default subnet mask and CIDR value for the IP address 13.75.137.90 •Please solve it with stepsIP Address is 69.67.214.64/26 Subnet Mask: Maximum usable hosts: Network Address: Broadcast Address: IP Address is 10.9.3.255/21 Subnet Mask: Maximum usable hosts: Network Address: Broadcast Address: Subnet 192.168.3.0/25 into 7 subnetworks (show working) How many subnets can you get for 27 hosts from 172.16.3.0/26 (show working) Subnet 192.168.1.0/24 into 6 subnetworks but there is a requirement that only the first subnetwork needs to have at least 58 hosts (show working)The internet service providers send and receive the data in the form of packets. These packets contain the source and destination address for communication. A malicious user captures the packet during the communication and uses the source address to communicate with the destination machine. Based on the given scenario answer the following questions: 1-List any TWO disadvantages of doing such attack on the network.

