nguage
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter8: I/o Streams And Data Files
Section8.4: File Streams As Function Arguments
Problem 3E
Related questions
Question
I need help with this function in C language
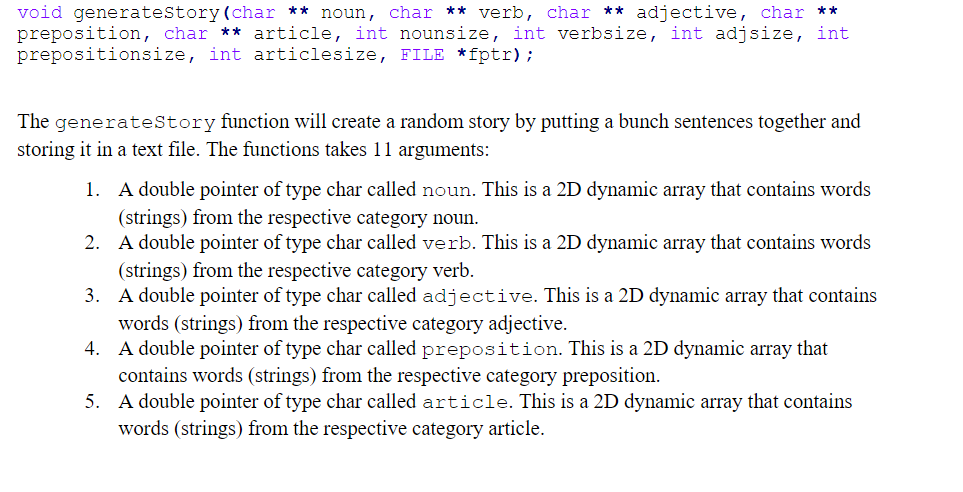
Transcribed Image Text:void generatestory (char ** noun, char ** verb, char ** adjective, char **
preposition, char ** article, int nounsize, int verbsize, int adjsize, int
prepositionsize, int articlesize, FILE *fptr);
The generateStory function will create a random story by putting a bunch sentences together and
storing it in a text file. The functions takes 11 arguments:
1. A double pointer of type char called noun. This is a 2D dynamic array that contains words
(strings) from the respective category noun.
2. A double pointer of type char called verb. This is a 2D dynamic array that contains words
(strings) from the respective category verb.
3. A double pointer of type char called adjective. This is a 2D dynamic array that contains
words (strings) from the respective category adjective.
A double pointer of type char called preposition. This is a 2D dynamic array that
contains words (strings) from the respective category preposition.
5. A double pointer of type char called article. This is a 2D dynamic array that contains
words (strings) from the respective category article.
4.
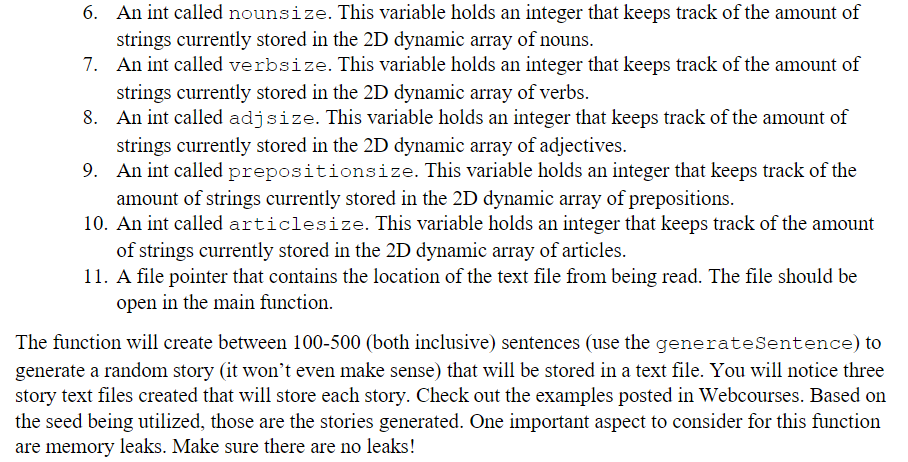
Transcribed Image Text:6. An int called nounsize. This variable holds an integer that keeps track of the amount of
strings currently stored in the 2D dynamic array of nouns.
7. An int called verbsize. This variable holds an integer that keeps track of the amount of
strings currently stored in the 2D dynamic array of verbs.
8. An int called adjsize. This variable holds an integer that keeps track of the amount of
strings currently stored in the 2D dynamic array of adjectives.
9. An int called prepositionsize. This variable holds an integer that keeps track of the
amount of strings currently stored in the 2D dynamic array of prepositions.
10. An int called articlesize. This variable holds an integer that keeps track of the amount
of strings currently stored in the 2D dynamic array of articles.
11. A file pointer that contains the location of the text file from being read. The file should be
open in the main function.
The function will create between 100-500 (both inclusive) sentences (use the generateSentence) to
generate a random story (it won't even make sense) that will be stored in a text file. You will notice three
story text files created that will store each story. Check out the examples posted in Webcourses. Based on
the seed being utilized, those are the stories generated. One important aspect to consider for this function
are memory leaks. Make sure there are no leaks!
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 5 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr