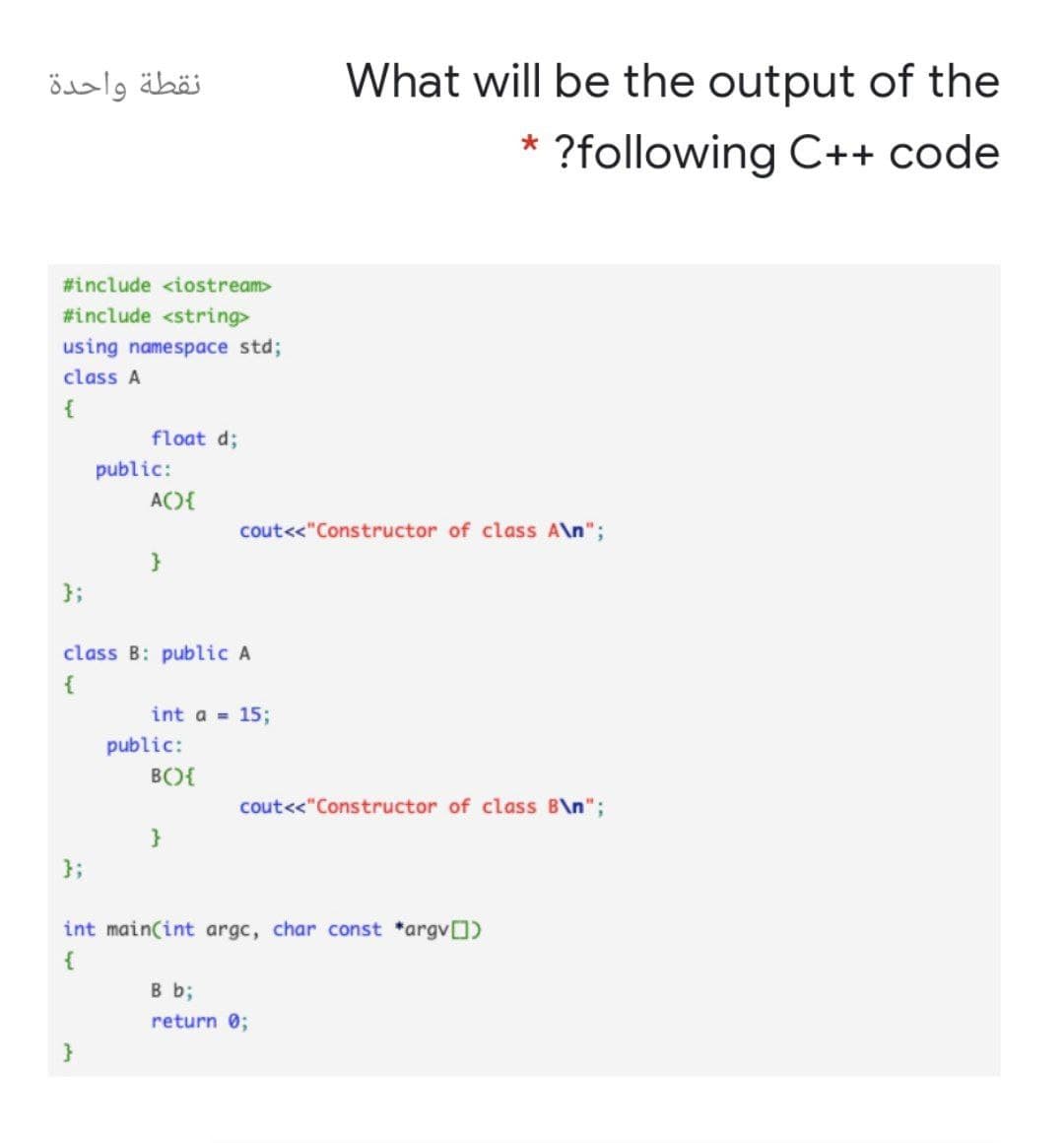
نقطة واحدة What will be the output of the * ?following C++ code #include #include using namespace std; class A { float d; public: ACO{ cout<<"Constructor of class A\n"; } }; class B: public A { int a 15; public: BO{ cout<<"Constructor of class B\n"; } }; int main(int argc, char const *argv) { B b; return 0; }
Q: Hi, i have a problem with this code, which is it only takes the last scores entered by the user when…
A: After correcting the code, I have provided C++ CODE along with 2 OUTPUT…
Q: Computer science What is the purpose of concurrency control?
A: Introduction: Concurrency Control's Goals Data integrity issues can develop when two update…
Q: Are you familiar with the most typical uses of database triggers and stored procedures?
A: Introduction An database management system (DBMS) is a piece of application software that is used…
Q: نقطة واحدة A base class is also known as class Inherited O Sub
A:
Q: What are the four TCP/IP abstraction layers?
A: Given: The TCP/IP paradigm has four layers: network, internet, transport, and application. These…
Q: What are the different layers of abstraction in TCP/four IP?
A: ANSWER:-
Q: 1. Explain the role of the back button as it relates to the back stack.
A: The solution as given below;
Q: For SSDs, why is wear levelling necessary?
A: Solution:- Wear leveling:- •It provides a method for distributing program and erase cycles uniformly…
Q: How does TCP differ from UDP in terms of these three characteristics?
A: Connectionless protocol that does not provide reliable delivery: TCP is an Internet protocol that…
Q: In the context of computer language design, define orthogonality.
A: Introduction: The attribute orthogonality means that "changing X does not impact Y."
Q: What are some indicators that a system's useful life is drawing to a close?
A: Answer:- The first indicator of a system's useful life is the system's ability to generate stable…
Q: What are the dangers and repercussions of a cyber security breach for a company?
A: Introduction What are the dangers and repercussions of a cyber security breach for a company?
Q: What are the possible consequences of a data breach in terms of cyber security? Explain
A: Introduction A data breach occurs when unauthorized parties get access to sensitive information…
Q: Computer science What is network protocol? Explain the following network protocols (in your own…
A: Introduction: A protocol is a set of rules that govern how data is formatted and processed.
Q: Find "Announcing the Advanced Encryption Standard (AES)" on the internet. This FIPS 197 standard…
A: Advanced Data Encryption Standard AES: The Advanced Encryption Standard (AES) is a symmetric block…
Q: ?following C++ code #include #include using namespace std; class A { float d; public: ACO{…
A: In this question, we have given a C++ code. This code involves class and constructor. We have to run…
Q: Give the examples/applications designed as finite state system. 2. What are the applications of…
A: It is a system where the particular inputs causes a change in state that can represent a finite…
Q: What is the definition of a popular website? What options are available to small enterprises if they…
A: Enterprise: A for-profit firm or corporation is known as an enterprise, however it is most typically…
Q: Use the following representation methods to convert the decimal number 30 to an 8-bit binary number:…
A: Given: The most straightforward method is to convert it to hex first. 7210 = 4816 = 10010002 since…
Q: Why is python so popular in cloud computing? Why is it favoured over other programming languages for…
A: Why python is widely used for cloud computing Python now powers some of the most complex…
Q: A bit-string of length 9 is generated randomly (each bit-string is equally likely to be generated).…
A:
Q: What function does a balanced scorecard play in achieving the maximum potential ROI?
A: Maximum ROI: Increased sales and revenues and higher pricing are two ways to boost your return on…
Q: MARIE Simulator/MARIE Architecture Why do IR and MBR contain the identical contents at times but…
A: Answer: The data in MBR is later passed to IR (Instruction Register) IR – Holds the instruction…
Q: What does "infrastructure mode" mean for a wireless network? What mode of operation is the network…
A: In a wireless network, there are two modes of operation: infrastructure mode and other modes of…
Q: The Engineering Solutions Company Limited (ESCL) ha for, and won a contract to design and build a…
A:
Q: Three-tier architecture refers to the intermediate layer between the database and the client…
A: Solution: The most appropriate option is to use an application server.
Q: "Beware of sites that contain bias or do not admit its bias freely" is related to which of the…
A: c. Objectivity
Q: Question 1 1. What Is The Difference Between The Strings And The Words Of A Language? 2. Define: (i)…
A: Given To know about the Difference Between The Strings And The Words Of A Language. Finite…
Q: Computer science What is the advantage of breaking your application’s code into several small…
A: Introduction: It makes the software more manageable. Real-world programs can include thousands of…
Q: Justify the design of the Domain Name System (DNS) as a distributed database.
A: An application layer convention characterizes how the application processes running on various…
Q: What are the hazards associated with migrating the database from one server to another?
A: Migration: Fewer Risk Data Data loss may occur during data migration. Some data may not migrate from…
Q: In what ways are information systems organised, managed, and technological?
A: Information Systems(IS): A formal, sociotechnical, organisational system intended to gather,…
Q: Use the following representation methods to convert the decimal number 30 to an 8-bit binary number.…
A: Given: Decimal number 30 is provided. Requirements: Convert the decimal number 30 to an 8-bit binary…
Q: The fact that big data comes in a number of formats and may be organised or unstructured…
A: Big data: Option A is the most appropriate response (Big data refers to data sets that are at least…
Q: Migrating a server database has a variety of hazards.
A: Migrating to the cloud: From regulatory violations and contractual breaches to unsecured APIs,…
Q: Write a 300-word essay about the relevance of networking in the growth of IT?
A: Given We know about the relevance of networking in the growth of IT.
Q: Views may be used as data security components, but they also have their constraints.
A: Introduction: It is the process of verifying data to ensure data quality by ensuring that it has…
Q: Computer science What are the advantages and disadvantages of passing by reference versus passing by…
A: Introduction: We really send the memory address of that particular variable as parameters in pass-by…
Q: S=4lw + 2wh; s=102, l=7, w=3
A: Substitute the given values into the given formula and solve for the unknown variable. S=4lw + 2wh;…
Q: C++ program that prompts the user to enter two integers. The program outputs how many numbers are…
A: Code: #include <iostream> using namespace std; int main(){ //read two integers int…
Q: What are the critical distinctions between a wide-area network and one that spans a local area…
A: Wide-area network: A wide area network is a large network of computers that are not all linked to…
Q: Q6) Let A = Z, the set of all positive integers, and we define the relation R on A as: a Rb if and…
A:
Q: What is the purpose of Cache Fusion in Oracle RAC?
A: Cache Fusion Oracle RAC transfer the data block from buffer cache of one instance to the buffer…
Q: Distinguish between type conversion, type coercion, and nonconverting type casts.
A: Introduction: The distinctions between type conversion, type coercion, and nonconverting type casts…
Q: What are the primary differences between a local-area network and a wide-area network in terms of…
A: Introduction : This question illustrates why determining how to build a distributed database, a…
Q: Trying to figure out what makes computers so powerful. Do you know how computers have grown so…
A: What makes computers so powerful? If you work as a computer designer, play a lot of games, or simply…
Q: Which current trends in cybercrime should you be on the lookout for? Do you know how to respond to…
A: Given: Social engineering assaults and cyber fraud were the most generally reported dangers. This…
Q: Which of the three abstraction levels is appropriate for data?
A: Data: As a result, we went through everything. Complex data structures are present in database…
Q: One of the most significant differences between a cell phone and a PDA is that a PDA may be turned…
A: Introduction: In addition to waiting for calls, a mobile phone maintains time synchronisation and…
Q: Computer science Explain the relationship among ODBC, OLE DB, and ADO.
A: Introduction: ADO is a database access library built on the COM platform.The standards OleDB and…
Step by step
Solved in 2 steps

- please write in C++ using #include <iostream> using namespace std Define a class called DateYear, that represents any year like 2023 in addition to the day and month (03/34/2023). Your class will have one member variable of type int to represent the year. This class is a child of the DayOf Year class where the code is given in lecture14 (Lecture14_Code.cpp). Your DateYear class should have the following member functions: a constructor and a default constructor that sets the year to this year, month to 1 and day to 1. an input function that reads the date (day, month, and year). Make sure to check for inaccurate dates. -getter and setters for the year. an output function that outputs the date in form of xx/xx/xxxx. It can display to the screen or the file. A friend function DateCompare that compares two years and returns true if they are the same. A member function BDCountdown, which calculates and returns how many days till your birthday. This function take the birthday as the…What refers to the contents of a class? a. both data and functions b. functions c. none of the choices d. data what is the output of this c++ program? #include using namespace std; class Test { int x; }; int main () { Test t; t.x = 6; cout << t.x; return 0; } a. 6 b. 0 c. random value d. compiler errorHello the question is the following: Write the definitions of the functions of the class primeFactorization (Example 11-4) declared in the primeFactorization header file. Write a program that uses this class to output the prime factorization of an integer. Your program should prompt the user for an integer, determine if the input is a prime number, and display the factorization of the integer. An example of the program is shown below: Enter an integer between 2 and 270,000,000,000,000: 1005427 1005427 is a prime number. Its factorization is: 1005427 = 1005427 I need help with write three things: integerManipulationImp.cpp, primeFactorizationImp.cpp, and a main.cpp. The attached images are the .h files respective to the cpp files that are needed to answer this question. Thank you.
- Write the definitions of the functions of the class primeFactorization (Example 11-4) declared in the primeFactorization header file. Write a program that uses this class to output the prime factorization of an integer. Your program should prompt the user for an integer, determine if the input is a prime number, and display the factorization of the integer An example of the program is shown below: Enter an integer between 2 and 270,000,000,000,000: 1005427 1005427 is a prime number. Its factorization is: 1005427 = 1005427a. Differentiate between implicit type conversiona nd Explicit type conversion with the help of example. b. What is the use of continue statement exaplin with appropriate example.Please written by Computer source Write the following program in C#. Use comments to indicate your mutator, accessors, and constructors. Write a program that includes an Employee class that can be used to calculate and print the take-home pay for a commissioned sales employee. All employees receive 7% of the total sales. Federal tax rate is 18%. Retirement contribution is 10%. Social Security tax rate is 6%. Write instance methods to calculate the commission income, federal and social security tax withholding amounts and the amount withheld for retirement. Use appropriate constants, design an object-oriented solution, and write constructors. Include at least one mutator and one accessor method; provide properties for the other instance variables. Create a second class to test your design. Allow the user to enter values for the name of the employee and the sales amount for the week in the second class.
- Can I please get help writing this in c++ Create a base class called Animal. All animals have a name (i.e. “Fido,” “Thumper,” “Princess,” “Nemo,” etc.) and an age. Provide a default constructor that initializes the age to zero and outputs the message “Invoking the default Animal constructor” and another constructor that allows the name and age to be set by the client. This other constructor should also output the message “Invoking the 2-argument Animal constructor.” Also construct a destructor for this class that outputs the message “Invoking the default Animal destructor.” Your Animal class should have a function called Move that cannot be implemented. That is, it should be declared as a purely virtual function. Your class should also have Get and Set methods to allow the name and age to be accessed. From the Animal class, derive Dog, Rabbit, Fish, and Snake classes. The derived classes should each have constructors and destructors that output an appropriate message (e.g., the…In C++ Language: Suppose I have a class named Person. Here is how I would like to use the class: //Create a person named Dave Smith Person dave("Smith", "Dave", 'R'); //Create a person named Gal Gadot Person gal("Gadot", "Gal", 'G'); //Dave and Gal gets married gal = dave + gal; dave = dave + gal; //print Gal and Dave's new married name cout << gal << endl; cout << dave << endl; This will output the following: Gal Smith-Gadot Dave Smith-Gadot Write the class declaration for Personwrite a program in c++ ,Create a class called Complex for performing arithmetic with complex numbers.Write a program to test your class. Complex numbers have the form Real Part + imaginary Part * i where i is Use double variables to represent the private data of the class. Provide a constructor that enablesan object of this class to be initialized when it’s declared. The constructor should contain default values in case no initializers are provided. Provide public member functions that perform the following tasks: 1-Printing Complex numbers in the form (a, b), where a is the real part and b is the imaginarypart. 2-Adding two Complex numbers: The real parts are added together and the imaginary parts are added together. 3-Subtracting two Complex numbers: The real part of the right operand is subtracted from the real part of the left operand, and the imaginary part of the right operand is subtracted from the imaginary part of the left operand. note:notice to solve point 1,you solve…
- Can you help me with this code for C++ please: Modify the class Song you created for part 2 bydoing the following:(a) Add a default constructor that initializes the song to have invalid astitle and artist, and −1 as recording year.(b) Add a constructor Song(title) that initializes the song to thegiven title (that is, to the title given as argument). The artist andrecording year are initialized to unknown and −1, respectively. Theargument is a string.(c) Add a constructor Song(title, artist, year) that initializesthe song to the given title, artist and recording year. The first twoarguments are strings, the third one is an integer.(d) Replace the function equals(s1, s2) by a methodequals(other) that returns true if the receiver and theargument have the same title, artist and recording year.(e) Add a method less_than(other) that returns true if the title ofthe first song is less than the title of the second song. In case the titlesof the two songs are identical, the method returns true…Create a class Time which contains:o Hourso Minuteso SecondsWrite a C++ program using operator overloading for the following:o = =: To check whether two Time are same or not.o >>: To accept the time.o <<: To display the time.programming paradigms Please write the following functions in Haskell. Please also write type declarations for each function, including type classes, wherever necessary. 1. Modify isGodzilla from today's lecture to isNum where the function accepts an integer as an input parameter and outputs True if this integer matches the number in the function. 2. Write a function fibList that uses the fib function from today's lecture. fibList accepts a number n as parameter and outputs a list of the numbers in the Fibonacci series up to n. Note that fibList will use a list comprehension involving fib. 3. Write a function justHighScores that takes the list generated as output of the gradeBook function and returns a list of students who score >= 95. Please use the isHighScorer function from today's lecture in justHighScores. You will also have to implement the gradeBook function discussed in class today. 4. Modify the function lastElement from today's lecture to getSecondLast. The function…



