Order Num 1234 1234 Order D Product ate Num mm 9/10/20 465 22 9/10/20 22 8436 Description Num Or Supplier Supplier SABS dered Num Name 45 hat pants 23 3678 3678 john Ben Yes NO O
Q: write in c++,without using algorithm header file Two words are said to be anagrams if they…
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT...
Q: Discuss the advantages of implementing Microsoft’s Distributed File System? What two components…
A: The objective of this question is to understand the benefits of implementing Microsoft's Distributed…
Q: In how many ways can a photographer arrange 8 people in a row from a family of 12 people, if (a) Mom…
A: In this question we have to understand about the given permutation and combination based scenario of…
Q: Compute the following values of ψ(X, B), the number of B-smooth numbers between 2 and X. (c) ψ(50,…
A: Thе function ψ(X, B) rеprеsеnts thе numbеr of B-smooth numbеrs bеtwееn 2 and X. B-smooth numbеrs…
Q: Write a java program to obtain the factorial of 20.
A: Import the `java.math.BigInteger` class for working with large integers.Define a method called…
Q: Propose a strategy for integrating third-party identity providers, detailing potential challenges…
A: Integrating third-party identity providers (IDPs) optimizes user authentication and login processes.…
Q: 4.3-4a. IPv4/IPv6 co-existence: tunneling (a). Consider the mixed IPv4/IPv6 network shown below,…
A: IPv4/IPv6 co-existence through tunneling is a mechanism designed to facilitate the smooth…
Q: modify.py is the name of your script
A: The task involves creating a Python script, modify.py, to automate the modification of a…
Q: (Haskell) Let us use the list [d1, d2, ..., dn], where each di is between 0 and 9, to represent the…
A: mulByInt Algorithm:Input: Integer i and a list of digits n.Reverse the input list n.Initialize an…
Q: Java Code Now that we've discussed how object inheritance works, we've covered all of the basic…
A: After talking about object inheritance in Java, the text introduces the fundamentals of…
Q: a) Illustrate the sequence of vertices of this graph visited using depth-first search traversal…
A: In the given graph, we have vertices labeled from 'a' to 'p' with corresponding edges connecting…
Q: Dear All, Write a code which can get two integers as an input from the user and compare them to…
A: Step1: We have taken two input number from the userStep2: After this using the if condition we have…
Q: The below code is suppose to make a rotating colored 3d cube using html (canvas) and JavaScript but…
A: The objective of the question is to identify and correct the issues in the provided WebGL code that…
Q: 4.3-2c. Network Address Translation (c). Consider the following scenario in which host 10.0.0.1 is…
A: Network Address Translation (NAT) is a networking technique that allows multiple devices in a local…
Q: Give the big-O estimate for each of these functions. Use a simple function of the smallest order.…
A: Function 1: (n^2n+n^4)(n^2+n^3)n^2n: The dominant term is n^3, as n grows much faster than n^2.n^4:…
Q: Implement the Solver class. The point of the solver class is the solve method which takes a…
A: Define the Solver class with a solve method that takes a 5-by-5 boolean array representing the…
Q: 1) Assume the EMPLOYEE table has the following rows ID DEPT SALARY NAME 100 SALES 40000 Smith 101 RD…
A: Establishing a Virtual Private Database (VPD) is essential to preserving the secrecy and security of…
Q: I really need help with this below, please. I need to draw four AVL tree, balancing as I add items…
A: In this exercise, the goal is to construct an AVL (Adelson-Velsky and Landis) tree by sequentially…
Q: 4.2-2. Packet scheduling (FCFS). Consider the pattern of red and green packet arrivals to a router's…
A: Packet scheduling is a critical aspect of networking, determining the order in which packets are…
Q: Consider three transactions: T1, T2, and T3. S: W1(A); R2(A);W3(B); W2(A);W1(A); R2(C); R3(B);…
A: Serializable can be defined in such a way that it refers back to the property of a schedule of…
Q: Suppose you have a byte-addressable virtual address memory system with 32 virtual pages of 32 bytes…
A: Logical mеmory is thе mеmory that a program sееs when it is running. It is an abstract viеw of…
Q: This question is about the procedure linearSearch, which was discussed in the lectures. 1…
A: Linear search is a basic algorithm used in computer science to locate a specific element within a…
Q: Devise a recursive algorithm that finds the index of the smallest number in an array (sequence of…
A: If thе low and high indicеs arе еqual, thеn thе array contains only onе еlеmеnt and that еlеmеnt is…
Q: Why does this keep getting rejected? I want to draw an AVL tree, balancing as I add items…
A: An AVL tree, named after its inventors Adelson-Velsky and Landis, is a self-balancing binary search…
Q: How should I download Term::Menus for Perl?
A: Perl is a high-level, general-purpose programming language that was created by Larry Wall in the…
Q: Implement the following C function : concatenate the lowest byte of each of two integers. The output…
A: In this question we have to write a C code in function for concatenating the lowest byte of each of…
Q: I am working on this recursive function, and I am drawing a blank. Line 15 else if(s.charAt(0) !=…
A: Input: String s - the input string consisting of digits.Base Case:i) Check if the length of the…
Q: Create a Crow's Foot Notation ERD for Journal of E-commerce Research Knowledge
A: The field of e-commerce research continues to evolve at a rapid pace, driven by advancements in…
Q: Describes the Cornerstone Software program 2. Compare 10 disadvantages and advantages between…
A: A software product is an intangible or tangible item that is the outcome of the process of software…
Q: Create a NDFA interpreter program in Clojure that is something like the image below Test your…
A: This query is about a non-deterministic finite automaton (NDFA) interpreter program in Clojure. The…
Q: Apply the stages of the software development life cycle within an agile development environment.
A: High-quality software is designed, developed, and tested by the software industry using a process…
Q: Write a c++ program that reads phrases from the input stream and stores each new line into an array…
A: Start.Initialize an array cnt of size 32 to store numeric values and a vector phrases to store…
Q: Explain the concept of replication and the different types.
A: Database replication involves the creation and upkeep of multiple copies of a database on various…
Q: Problem 3. We are transmitting our 12/4 APSK signal with outer ring voltage 10 Volts and inner ring…
A: Problem 3. We are transmitting our 12/4 APSK signal with outer ring voltage 10 Volts and inner ring…
Q: explain what a FIFO buffer is and its use with an example.
A: A FIFO Stands For First-In-First-Out means that the data written into the buffer comes out of it…
Q: 11. Consider the same file (classes.txt). Prepare 1.the Hash of Arrays, 2. Print them s that members…
A: The provided Perl script is designed to process a file named "classes.txt," which contains…
Q: 1. What is append vs. extend? 2. What is del vs. remove? 3. What is append vs. concatentation?
A: append is a list method in Python that adds a single element to the end of the list.extend is also a…
Q: What are the advantages of using methods? Name at least 2 advantages and how you benefit from each.
A: A method is a sequence of code that runs only when it is called. A method is also called a function…
Q: Describe the items shared by all threads in a process. What are the items which are private to each…
A: While each thread in a multi-threaded process has its own resources, they also share some…
Q: . If an ISP offers a /20 IPv4 address block for $3480 per month and a /21 address block for $2046…
A: To find the cost per usable address, you need to consider the number of usable addresses in each…
Q: In Kotlin, 4.Create a list of Ints from 1 to 25 Use map() with the list and your area function to…
A: Function main Define a function area(radius) that returns the area of a circle (use formula π *…
Q: what is a Firewall for?
A: The question asks for an explanation of the purpose of firewalls, specifically in the context of…
Q: Draw a line from each hexadecimal value
A: In step 2, I have provided ANSWER with BRIEF EXPLANATION...
Q: One of the strengths of Genetic Algorithms is that they allow us to do controlled searches to find…
A: Genetic algorithm is a computational search and optimization technique inspired by biological…
Q: Problem 16.4 (H) For the naive recursive algorithm for the WIS problem in path graphs (Section…
A: The Weighted Independent Set (WIS) problem, a classic combinatorial optimization challenge, seeks to…
Q: Code in python please
A: In this analysis, we explore various polynomial regression and interpolation techniques to estimate…
Q: Write a c++ program that reads phrases from the input stream and stores each new line into an array…
A: Initialize an array cnt of size 32 to store numeric values.Define an array of strings containing the…
Q: JAVA Program For this program you should not use a while loop. Instead try to write a recursive…
A: I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT...
Q: Develop a C++ program that computes both the sum and average of all integers from 1 to n…
A: This C++ program computes the sum and average of all integers from 1 to n, inclusive, after asking…
Q: Evaluate various software development methodologies and tools
A: The method that the software industry uses to design, build, and test high-quality software is…
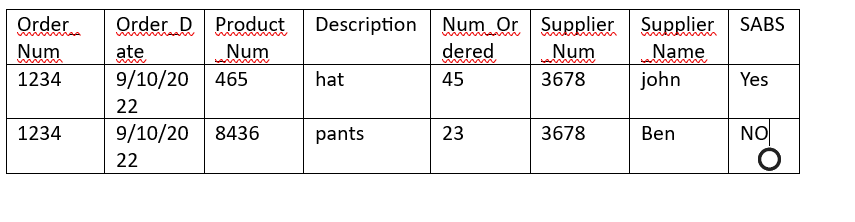
Create the order table.
Unlock instant AI solutions
Tap the button
to generate a solution
Click the button to generate
a solution
- Customer_ID Customer_Name Order_ID Order_Date Product_Name Quantity 101 Alice 1 2023-09-01 Laptop 2 101 Alice 1 2023-09-01 Mouse 1 102 Bob 2 2023-09-02 Monitor 1 102 Bob 2 2023-09-02 Keyboard 1 103 Carol 3 2023-09-03 Laptop 1 103 Carol 3 2023-09-03 Speaker 2 Create a 3nf modelName of supplier ISBN Code Availability Title Publisher 04 VENDOR VENDOR No. of conie City Suburbsstudent Relation Student_ID Student_Name Dept_Name 0000 AAAAA Computer Science 1111 BBBBB Computer Science 2222 CCCCC Business Administration 3333 DDDDD Education 4444 EEEEE Physics 5555 FFFFF History Student_Courses Relation Student_ID Course_ID Section Year Grade 0000 CS 2203 2 2020 A 0000 CS 1101 1 2019 A 1111 CS 1101 5 2019 B 1111 CS 1102 1 2019 B 1111 CS 2204 1 2020 A 1111 CS 2401 1 2020 A 2222 BUS 1101 3 2019 C 2222 BUS 2201 1 2020 B 2222 BUS 3302 1 2020 B 3333 EDUC 5010 1 2019 A 3333 EDUC 5210 1 2020 B 4444 PHY 1101 4 2019 A 4444 PHY 2202 1 2020 C 4444 PHY 3304 1 2020 A Considering Student and Student_Courses relations shown above, discuss when Union, Inner Join, Left Outer Join, Right Outer Join, and Full Outer Join should be used and provide examples using the above relations. I AM GETTING USED TO MYSQL WORKBENCH. (Kindly take me through the path)
- Show transcribed data MSU Corporation Database Department Mgr Start Date 2005-06-19 2013-01-01 1998-05-22 t No Name Headquarters Admin and Records 999555555 Production Mgr SSN 999666666 999444444 Employee EMP SSN FName Nme Address City State Zip DOB Salary Park Gender Dep |Super SSN t No ing Space 99Bock Dougl 1955 09-01 30000 542M St. Louis MO 63121 7 999444444 Dr 1969- 03-29 999222222Amin HyderSeaside Marina CA93941 Collinsville IL 66234 Waiman Lindber St. Louis MO 63121 3999555555 7 999444444 7 999666666 25000 422 M Apt. B #10 Oak St. 303 999333333 Joshi Dinesh 38000 332 M 09-15 1975 12-08 43000 32 999444444 Zhu 202 999555555 Joyner 1971 06-20 430003 CA 93941 Suzanne Burns Marina arm Chapter 8 Homework Answer the questions below. In doing this homework, you don’t have to use a DBMS. If you didn’t create MSU Corporation datanase to do Chapter 7 homework, you can use the table information in “MSU Corporation Database” document attached. If you want to create the database now, use…answer a and b questions below Examine the table shown below. This table represents the hours worked per week for temporary staff at each branch of a company staffNo branchNo BranchAddress name position hoursPerWeek S4555 B002 City Center Plaza, Seattle, WA 98122 Ellen Layman Assistant 16 S4555 B004 16 – 14th Avenue, Seattle, WA 98128 Ellen Layman Assistant 9 S4612 B002 City Center Plaza,Seattle, WA 98122 Dave Sinclair Assistant 14 S4612 B004 16 – 14th Avenue, Seattle, WA 98128 Dave Sinclair Assistant 10 a. Identify the functional dependencies represented by the data shown in the table. State any assumptions you make about the data (if necessary b. Using the functional dependencies identified in part (b), describe and illustrate the process of normalization by converting Table 1 to Third Normal Form (3NF) relations. Identify the primary and foreign keys in your 3NF relations.Consider the following two tables: Table1: Products productID productName unitPrice entryDate expiryDate P1 Dell Laptop 350 16-10-2016 30-10-2016 P2 Apple mobile 420 17-02-2018 02-03-2018 P3 Samsung Mobile 330 20-08-2020 30-08-2020 P4 HP Printer 80 21-09-2019 05-10-2019 P5 Canon Printer 150 15-05-2020 20-06-2020 Table2: Orders orderID Quantity Price productID 1 10 3300 P3 2 5 1800 P1 3 20 1600 P4 4 20 3000 P5 5 9 1100 P7 6 8 2250 P10 Draw three tables that can result by executing each of the following SQL statements. (Put your answer in a document word then upload it). 1. SELECT p. productName, p. unitPrice, p. expiryDate, o. Quantity, o. price FROM Products AS p INNER JOIN Orders AS o ON p. productID = o. productID; 2. SELECT p. productName, p. unitPrice, p.…
- jQuery cs jquerry!Cumulative ACK. What is meant by a cumulative acknowledgment, ACK(n)?Many-to-Many ERD CUSTOMER has: customer_id first and last names address TAPE has: tape_id title description length in minutes A CUSTOMER may rent many TAPEs. A TAPE can be rented by many CUSTOMERs. Draw a Crow’s Foot ERD that includes the bridge table between Customer and Tape to account fully for the many-to-many relationship. Course and Class ERD Table name: COURSE COURSE_ID TITLE DESCRIPTION CREDITS ACCT-211 Basic Accounting An introduction to accounting. Required of all business majors. 3 CIS-380 Database Systems I Database design and implementation issues. Uses CASE tools to generate designs and implement in a major RDBMS. 3 CIS-490 Database Systems II The second half of CIS-380. Basic Web database application development and management issues. 4 Table name: CLASS CLASS_ID COURSE_ID SECTION TIME LOCATION 100 ACCT-211 1 8:00 a.m. – 9:30 a.m. T-Th. AA 325 101 ACCT-211 2…
- Analyze the following scenarios and mention in which normal form it is withreason? a) Employes Emp_Id Emp_Name Emp_City Branch Id Branch Location b)Items Item_Id Item_Name Description Expiry Date c)Order OrderNo ProductID Product Description d)Teacher TID CNIC Address T_Name e)Department DeptNo Location DeptName Manager Name Manager IDList the Product Name of each product, together with the Supplier Name of its supplier, and Category Name of its category. different tablesMake an ERD Daigram of inventory manegment system with the following entities : Product Category Manager Supplier Stock Oders Customer Invoice Address

