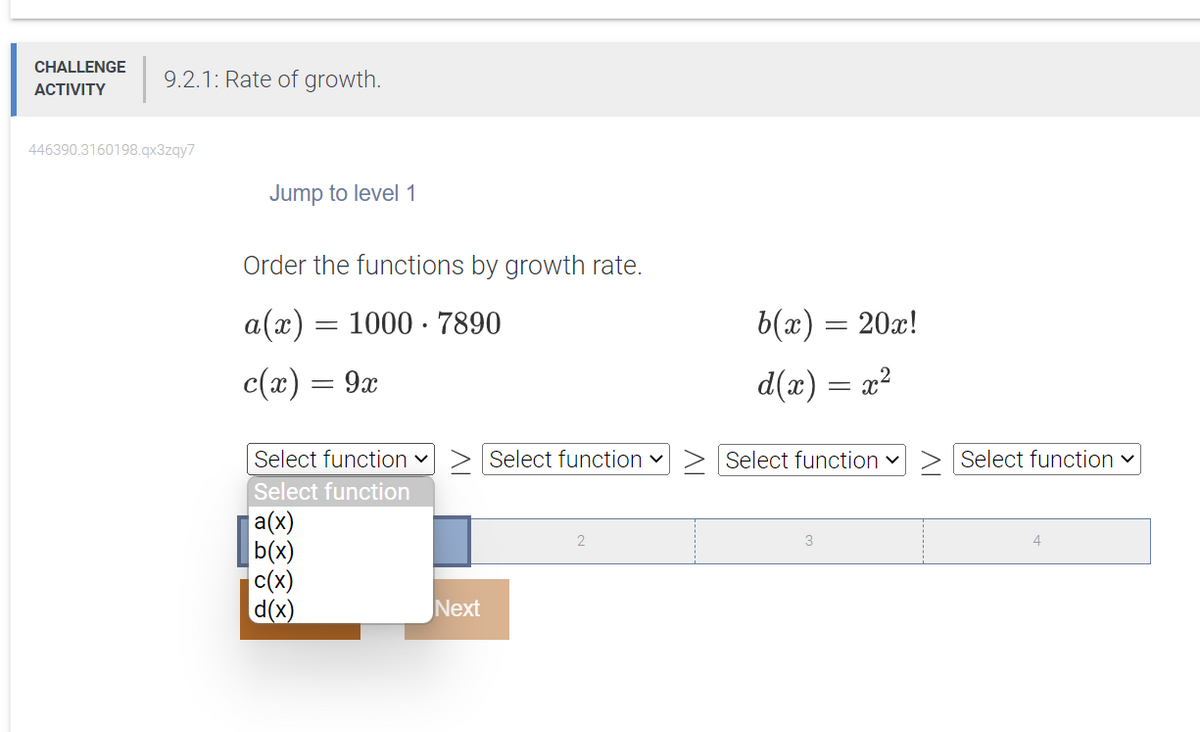
Order the functions by growth rate. a(x) = 1000-7890 c(x) = 9x b(x) = 20x! d(x) = x²
Q: As you construct the framework, think about the many challenges you'll encounter and the various…
A: Introduction: Cloud computing is a cutting-edge technology that has a powerful infrastructure that…
Q: How did information systems change over time, and what were the most important people and events?
A: Explain the evolution of information systems, focusing on the key figures and events that shaped the…
Q: List the three goals of designing relational databases and explain why each one is good.
A: The three primary goals of designing relational databases are:
Q: What is the worse case run time for following algorithm? CountDuplicatePairs This algorithm counts…
A: We have to explain the code and also we have to proivde the right option for the given question.
Q: Can the World Wide Web be considered an independent network?
A: The answer is given below step.
Q: When the Internet was first conceived, it was known as ARPANET. In what ways does the World Wide…
A: The World Wide Web (WWW) and the Internet are related but different concepts. Here are some key…
Q: a a + b generalized transition graph. ab 2 bb (a) Find an equivalent generalized transition graph…
A: We are given a transition graph which contains input alphabets as a and b and contains 3 states…
Q: Write a python function that accepts a string object and counts the number of vowels in the string…
A: The following Python code defines a function named countvowels that accepts a string object as input…
Q: While migrating from on-premises servers to a cloud-based IaaS architecture, do you anticipate any…
A: The answer is given below step.
Q: What kinds of information systems do companies use?
A: Introduction: In today's digital age, information systems have become an essential part of business…
Q: Specify the architecture of a computed unified device.
A: Introduction: A computed unified device (CUD) is a term used to describe a device that integrates…
Q: 1. Create a computer programme that contrasts each of the four sophisticated sorting algorithms…
A: The programme would evaluate the four advanced sorting algorithms—merge sort, quick sort, heap sort,…
Q: What is the most efficient technique for memory management, and why?
A: Here is your solution -
Q: Task 03: You are traveling through dangerous wilderness with bridges and rivers. Each of them has a…
A: The Python code is given below with output screenshot
Q: Following the development and testing of individual software modules, they must be combined and…
A: Introduction: Software development involves creating individual modules that perform specific…
Q: Find out what kind of cable will be used to link the switch and the router. What piece of hardware…
A: Straight-through cable is used for unlike devices: router to switch/hub, computer to Switch/hub.…
Q: As compared to other languages, how is SQL u
A: Introduction: SQL is known for its simplicity, efficiency, and versatility in handling complex data…
Q: What is the point of the service abstraction layer in the OpenDaylight SDN controller?
A: To find the point of the service abstraction layer in the OpenDaylight SDN controller.
Q: Analyze the benefits and drawbacks of employing agile methodologies in the system development and…
A: Agile methodologies have become increasingly popular in system development and deployment processes…
Q: What is the output? abc = 0 abc.append([1, 3, 5, 7]) abc.append(['yes', abc.append([11,…
A: Here, a python program is given. We have to find its output.
Q: Why does automation depend on information and knowledge technology?
A: Introduction: Automation has become an increasingly important aspect of modern business and…
Q: Look at how different companies use information systems.
A: Introduction: In addition to IT infrastructure, companies use organisational information systems,…
Q: Based on Activity Diagram - Object Oriented Modeling knowledge: 1. What process are…
A: The above diagram is an UML Activity diagram. This Activity diagram represents the flow of…
Q: What can we learn from cybercrime, both in terms of suggestions and generalisations?
A: There are various suggestions and the generalizations the cybercrime teaches us which are mentioned…
Q: 90 Q6.1 Kruskal 0 40 50 80 130 110 70 150 60 30 10 120 140 20 100 44 List the weights of the MST…
A: Kruskal algorithm:
Q: In what ways can you describe "the cloud?"
A: Your answer is given below.
Q: Explain how voice information systems are used today
A: Voice information systems (VIS) are computer systems that allow individuals to interact with a…
Q: Q Which of the following code will remove all the rows from the table LOCATIONS?
A: Below Is the answer for above question with detailed explanation
Q: What are the seven layers of connectivity in the OSI model? Briefly define the goal of each layer.
A: The answer is given below step.
Q: 14.3 Is list sorted Write a program that reads a list of integers from input and outputs "yes" if…
A: We need to write a program that reads a list of numbers and two positions from the user. The program…
Q: It is important to be aware of the distinction between encoding and encryption.
A: Answer: Yes, it is important to be aware of the distinction between encoding and encryption because…
Q: It is important to make a distinction between caches that are fully associative and caches that are…
A: The Answer is in given below steps
Q: 1. Write a Python function called add_daily_temp that is given a (possibly empty) dictionary meant…
A: 1) Below is program that defines a function add_daily_temp which accept a dictionary containing day…
Q: In terms of security, how can the advantages and disadvantages of various authentication methods be…
A: We have to write the advantages and disadvantages of different authentication methods.…
Q: NAS stands for "network attached storage," and SAN stands for "storage area network" (storage area…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: What are the jobs of people who work with computers?
A: SOLUTION - So, we can say there are so many jobs with computers, It an be in many positions or…
Q: Does the Boyer-Moore string search algorithm have any real-world applications that you're aware of?…
A: The Boyer-Moore String Search Algorithm is frequently used as a benchmark for other string-searching…
Q: As you construct the framework, think about the many challenges you'll encounter and the various…
A: Introduction: Cloud computing is a modern technology with a solid infrastructure that is both…
Q: Consider the following edge-weighted graph G with 9 vertices and 16 edges: 90 Q6.1 Kruskal 40 50 80…
A: Steps: 1. Sort all the edges in non-decreasing order of their weight. 2. Pick the smallest edge.…
Q: -ot of 105-Google Sear x Player/ Hultiple Choice What is the first element in the list after the…
A: let us see the answer:- Introduction:- In Python, a list is a data structure used to store a…
Q: Why is it that software engineering ideas such as process and dependability, management of…
A: Software Engineering: Software engineering is a discipline that involves the application of…
Q: Define the concept of Resource allocation ?
A: The answer to the query "useful resources for allocation" is a process for organising and allocating…
Q: How would I go about implementing for the above question for Invalid Input, individual Registation…
A: The question is asking for the implementation of a program in Java that allows for individual and…
Q: 1. Construct a dfa that accepts the language generated by the grammar S→ abA, A -> ba B, B -> a…
A: Here is a step-by-step approach to construct a DFA that accepts the language generated by the given…
Q: Define the concept of Resource allocation ?
A: Resource allocation refers to the process of distributing and assigning available resources, such as…
Q: How did information systems change over time, and what were the most important people and events?
A: In this question we need to explain the changes made in the Information System (IS) and people and…
Q: Explain how the ideas of user-centered design relate to the different stages of the software…
A: Software development life cycle: Software life cycle models (process models) illustrate the software…
Q: Define the concept of a unified memory architecture.
A: Introduction: Unified memory is about reducing the duplication of data transferred between the…
Q: What kinds of information systems do companies use?
A: How corporations utilise IT. An overview Business information systems are complementary networks and…
Q: Explain what the words "CRUD" and "REST" mean.
A: CRUD-: CRUD refers to the four basic operations a software application should be able to perform –…
please show final answer the same format as the oicture so it will b eeasy to underestand.
Step by step
Solved in 2 steps

- Your task is to implement Depth-first search algorithm to solve the problem of placing 8 Queens on a chess board so none can “take” each other.• A code framework, supporting videos and html documentation of the provided code-base will be provided via Moodle in assignments section.• The implementation should accept one command-line argument at the time it is invoked for the starting position of the first queen.o It will be tested with a range of values for that input.o If the input is not an integer in the range of 0-7 it should report “Invalid Input” and exit. • You will be supplied with a partially completed file ‘main.c’ which contains the code need to read the command line and sets up the initial working candidate within the code framework.o Your task is to complete the code to implement depth-first search. o Your code must finish with a call to the function PrintFinalSolutionAndExit(); when a valid final solution stored in the variable “workingCandidate”. please solve full…Suppose a Genetic Algorithm uses chromosomes of the form x=abcdef with a fixed length of six genes.Each gene can be any digit between 0 and 9 . Let the fitness of individual x be calculated as : f(x) =(a+b)-(c+d)-(e+f) And let the initial population consist of four individuals x1, ... ,x4 with the following chromosomes : x1 = 3 5 3 2 6 5, x2 = 9 8 0 1 2 2, x3 = 1 2 2 1 2 3, x4 = 7 9 2 3 1 1 1. 1.Evaluate the fitness of each individual, showing all your workings, and arrange them in order with the fittest first and the least fit last. 2. calculate the average fitness. 3. Perform the following crossover operations:a- Cross the fittest two individuals using one point crossover at the middle point.b- Cross the second and third fittest individuals using a two point crossover (points b and e). Suppose the new population consists of the four offspring individuals received by the crossover operations in the above question. Evaluate the fitness of the new population, showing all your…implement bitcount function Count the number of 1’s in x. you are onlyallowed to use the following eight operators:! ~ & ^ | + << >> “Max ops” field gives the maximumnumber of operators you are allowed to use to implement each function /** bitCount - returns count of number of 1's in x* Examples: bitCount(5) = 2, bitCount(7) = 3* Legal ops: ! ~ & ^ | + << >>* Max ops: 40*/int bitCount(int x) {return 2;}
- Need Help with Octave: function [w, t, flag] = margin_pcpt(X, y, max_iter, max_margin)[m, n] = size(X);flag = 0;w = zeros(n, 1);t = 1;while (t < max_iter) && (flag == 0)% Your tasks: % 1. searches for violation point p such that % (a) the label disagrees with p*w; OR % (b) the distance between p and seperation line is too close, i.e. % p*(w./norm(w, 2)) <= max_margin % 2. update the seperation plane vector w % 3. if there is no more violation point, set flag = 1. t = t + 1;end% as a good habit: normalise the seperation vector by it's normw = w./norm(w, 2);endWireless sensor networks are a special kind of network that facilitates communication. Sensor nodes in WSNs relay information to and from a central base station. The computing resources and storage space of a sensor node are limited. Take, for example, an algorithm that can be solved by solving subproblems. Is it preferable to use dynamic programming or divide and conquer to solve these subproblems independently at various sensor nodes? Try to keep your writing short and sweet.You are the sysadmin for a big tech company, and you have to estimate the amount of servers you need to handle some long-running jobs. One server can handle only one job at once. One job can only be executed by one server at once. Once a server has finished executing its current job, it can be reassigned to a new job. Given an array of time intervals intervals where intervals[i] = [starti, endi], representing the start and end time for a particular job that needs to be executed, return the minimum number of servers required to run all jobs. Constraints: 1 <= intervals.length <= 104 0 <= starti < endi <= 106 Function definition for Java: public int minMeetingRooms(int[][] intervals) { // Your code here } Function definition for Python: def minMeetingRooms(self, intervals: List[List[int]]) -> int: #Your code here Announced Test Cases: Input: intervals = [[0,30],[5,10],[15,20]] Output: 2Explanation: We need one server for the job that starts at 0. For the job…
- I want to add one green leaf on the right side of the flower how can I do this?? What should I add to my code for this? Thanks for help My code n=800;r=linspace(0,1,n);theta=linspace(0,2*pi,n);[R,THETA]=ndgrid(r,theta);% define the number of petals we want per cycle. Violets have 5!petalNum=5;x = 1 - (1/2)*((5/4)*(1 - mod(petalNum*THETA, 2*pi)/pi).^2 - 1/4).^2;% update the formula for phi to stop the spiralling effectphi = (pi/2)*exp(-2*pi/(8*pi));y = 1.95653*(R.^2).*(1.27689*R - 1).^2.*sin(phi);R2 = x.*(R.*sin(phi) + y.*cos(phi));X=R2.*sin(THETA);Y=R2.*cos(THETA);Z=x.*(R.*cos(phi)-y.*sin(phi));% color code for blueviolet RGB 138,43,226% Indigo rgb value (75,0,130)mapSize=20;blue_map=linspace(138,75,mapSize)';blue_map(:,2)=linspace(43,0,mapSize)';blue_map(:,3)=linspace(226,130,mapSize)';% and a pretty bit in the middlegold_map=[255 215 0; 250 210 0];% combine to form a full flower mapviolet_map=[gold_map; blue_map];% Now lets plot it and try and pick an attractive…Computer Science Use only NumPy to create the Normalize Class: Image Normalization is a technique used to touch up images that are too dark or too light for the human viewing experience. Implement a version that outputs images with full dynamic range (0–255 pixel intensity). In other words, for each color channel (r, g, b), rescale the range of pixel values for that channel to include both 0 and 255. After normalizing, there should be at least one pixel with a red value of 0, at least one pixel with a red value of 255, at least one pixel with a green value of 0, etc. To normalize a list of numbers nums to the range 0–n, set nums[i] = (nums[i]−min(nums))/(max(nums)−min(nums))∗n for all i. Be careful! When max(nums) == min(nums), you should not touch that list (why?).Problem: The Eight Queens problem is to find a solution to place a queen in each row on a chessboard such that no two queens can attack each other. Code below package queenchees; import static java.lang.Byte.SIZE;import javafx.application.Application;import javafx.event.ActionEvent;import javafx.event.EventHandler;import javafx.scene.Scene;import javafx.scene.control.Button;import javafx.scene.layout.Pane;import javafx.stage.Stage;import javafx.scene.image.Image;import javafx.scene.image.ImageView;import javafx.scene.shape.Line; public class QueenChees extends Application { // Declare a variable private static final int SIZE = 8; // Declare an array private int[] queens = new int[SIZE]; // Override start method @Override // Start method public void start(Stage primaryStage) { // Call the function search(0); // Create a chess CB ChessBoard CB = new ChessBoard(); // Create a scene Scene scene = new Scene(CB,…
- Q2: There are three buckets size X, Y, M (1<=X<=Y<=M). All three buckets are initially empty. Using these three buckets, we can perform any number of the following two types of operations. We can fill the smallest bucket (of size X) completely to the top with X units of water and pour it into the size-M bucket, as long as this will not cause the size-M bucket to overflow. We can fill the medium bucket (of size Y) completely to the top with Y units of water and pour it into the size-M bucket, as long as this will not cause the size-M bucket to overflow. Although we may not be able to completely fill the size-M bucket, but we can still determine the maximum amount of milk we can possibly add to largest bucket. Sample input: 17 25 77 Sample output: 76 In this example, we fill the bucket of size 17 three times and then bucket of size 25 once, accumulating a total of 76 units of water. You could use additional test case to test your program: Input: 52 791 877 Output: 843 Input: 26…Not pseudocode Suppose the economies of the world use a set of currencies C1, . . . , Cn; think of these as dollars, pounds, Bitcoin, etc. Your bank allows you to trade each currency Ci for any other currency Cj, and finds some way to charge you for this service. Suppose that for each ordered pair of currencies (Ci, Cj ), the bank charges a flat fee of fij > 0 dollars to exchange Ci for Cj (regardless of the quantity of currency being exchanged). Describe an algorithm which, given a starting currency Cs, a target currency Ct, and a list of fees fij for all i, j ∈ {1, . . . , n}, computes the cheapest way (that is, incurring the least in fees) to exchange all of our currency in Cs into currency Ct. Also, justify the its runtime. [We are expecting a description of the algorithm, as well as a brief justification of its runtime.]Q2. ""Euler's totient function, also known as phi-function ϕ(n),counts the number of integers between 1 and n inclusive,which are coprime to n.(Two numbers are coprime if their greatest common divisor (GCD) equals 1)."""def euler_totient(n): """Euler's totient function or Phi function. Time Complexity: O(sqrt(n)).""" result = n for i in range(2, int(n ** 0.5) + 1): if n % i == 0: while n % i == 0: n //= i. .











