OverflowS You have learned the concept of overflow (with say n! that overflows at 13! for integer) Now consider Fibonacci numbers this way: 1, 1, 2, 3, 5, 8, 13, 21, 34, 55, 89, 144, etc. A Fibonacci sequence f(n) is of the form: f(1) = f(2)= 1, and f(n+2) = f(n) + f(n+1) for n >= 1. 3. Write a Java computer program that prints out Fibonacci numbers in a certain data type from f(1) until f(n) with n an integer you input from the keyboard.
OverflowS You have learned the concept of overflow (with say n! that overflows at 13! for integer) Now consider Fibonacci numbers this way: 1, 1, 2, 3, 5, 8, 13, 21, 34, 55, 89, 144, etc. A Fibonacci sequence f(n) is of the form: f(1) = f(2)= 1, and f(n+2) = f(n) + f(n+1) for n >= 1. 3. Write a Java computer program that prints out Fibonacci numbers in a certain data type from f(1) until f(n) with n an integer you input from the keyboard.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter10: Classes And Data Abstraction
Section: Chapter Questions
Problem 19PE
Related questions
Question
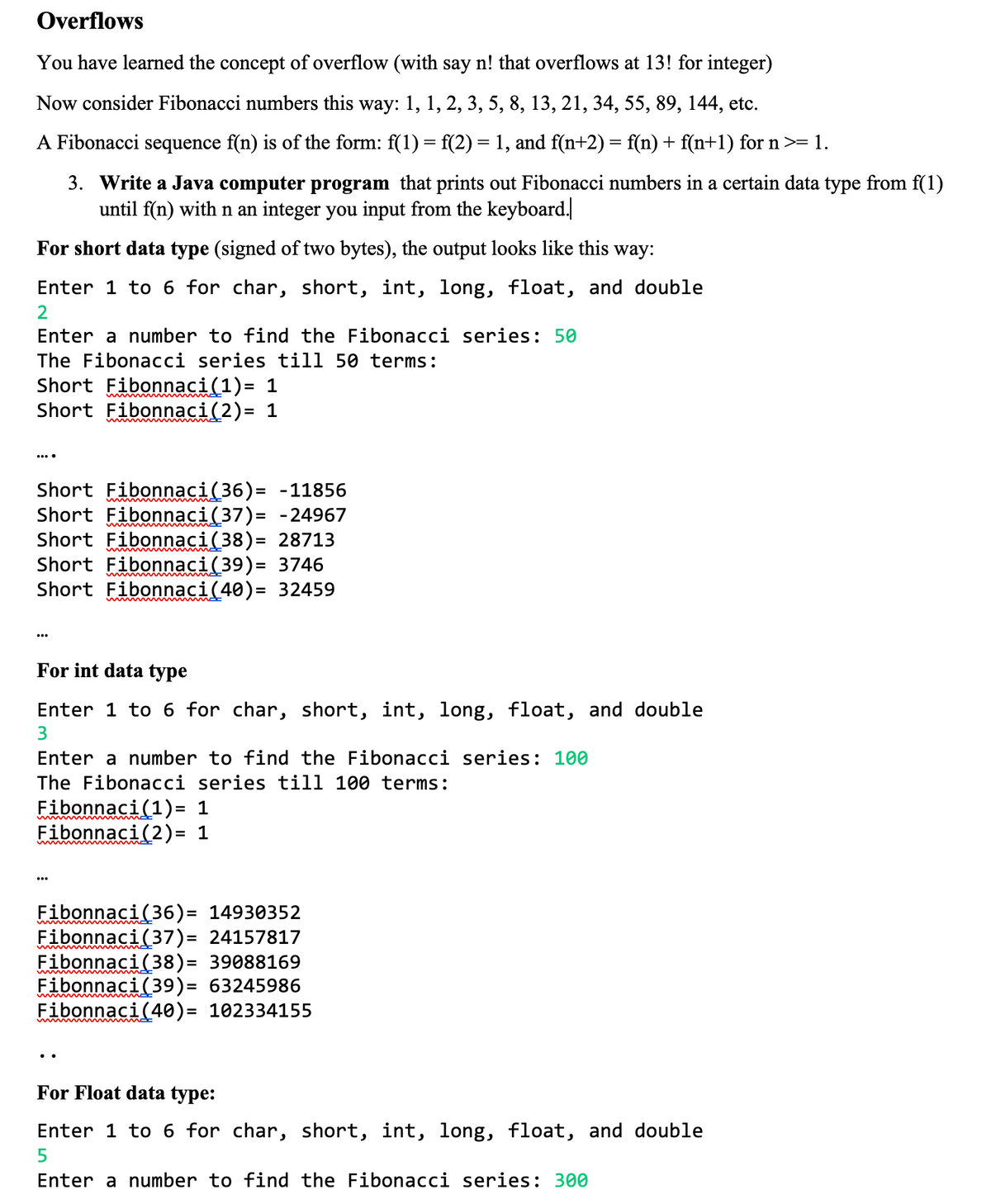
Transcribed Image Text:Overflows
You have learned the concept of overflow (with say n! that overflows at 13! for integer)
Now consider Fibonacci numbers this way: 1, 1, 2, 3, 5, 8, 13, 21, 34, 55, 89, 144, etc.
A Fibonacci sequence f(n) is of the form: f(1) = f(2) = 1, and f(n+2) = f(n) + f(n+1) for n >= 1.
3. Write a Java computer program that prints out Fibonacci numbers in a certain data type from f(1)
until f(n) with n an integer you input from the keyboard.|
For short data type (signed of two bytes), the output looks like this way:
Enter 1 to 6 for char, short, int, long, float, and double
2
Enter a number to find the Fibonacci series: 50
The Fibonacci series till 50 terms:
Short Fibonnaci(1)= 1
Short Fibonnaci (2)= 1
Short Fibonnaci(36)= -11856
Short Fibonnaci(37)= -24967
Short Fibonnaci(38)= 28713
Short Fibonnaci(39)= 3746
Short Fibonnaci(40)= 32459
For int data type
Enter 1 to 6 for char, short, int, long, float, and double
Enter a number to find the Fibonacci series: 100
The Fibonacci series till 100 terms:
Fibonnaci(1)= 1
Fibonnaci(2)= 1
Fibonnaci(36)= 14930352
Fibonnaci(37)= 24157817
Fibonnaci(38)= 39088169
Fibonnaci(39) = 63245986
Fibonnaci(40)= 102334155
For Float data type:
Enter 1 to 6 for char, short, int, long, float, and double
5
Enter a number to find the Fibonacci series: 300
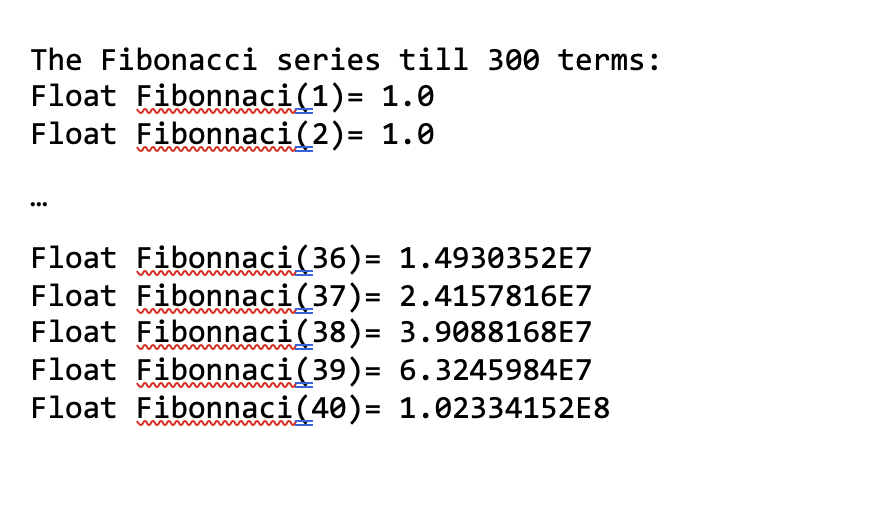
Transcribed Image Text:The Fibonacci series till 300 terms:
Float Fibonnaci(1)= 1.0
Float Fibonaci(2)= 1.0
Float Fibonnaci(36)=
1.4930352E7
Float Fibonaci(37)= 2.4157816E7
Float Fibonnaci(38)= 3.9088168E7
Float Fibonnaci(39)= 6.3245984E7
Float Fibonnaci(40)= 1.02334152E8
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning