P₁ P₂ P₁ PA Ps 0 3 5 9 13 20 10 9 4 16
Q: Do in Java Override the toString and equals of the Object class. For example: Test Result Book…
A:
Q: Pro B model checker vs Spin. Analyze and elaborate about the characteristics of each tool, their…
A: Pro B Model Checker
Q: This code segment find the value of the result of following series for five terms. * Y = X2 22 3X6…
A: Solution: Solution from step-2
Q: sed in a digital library based on the authors last name. Ea room to store only the last name of the…
A: Please find the answer below :
Q: What is meant by loop unrolling?
A: Loop unrolling The loop unrolling is a loop transformation method that helps to optimize the…
Q: to implement liner se coarch
A: Introduction: An effective algorithm for narrowing down a list of things is binary search. It…
Q: Create an assembly language program that will ask for the following information NAME SECTION…
A: Algorithm: Start. Get the inputs. Perform the operations. Print the output in square format. Exit.
Q: Suggest TWO (2) important factors that affect how software projects are managed.
A: Introduction: There are many different ways to manage projects, such as the traditional, waterfall,…
Q: Please review my code here in C... there are errors occurring and I'm not sure why. Input will…
A: According to the information given:- We have to follow the instruction in order to get desired…
Q: What is meant by pipelining?
A:
Q: Convert the following NFA into DFA that accepts the same language (e is the empty string) S Р e b…
A: The complete code in JFLAP is below
Q: Every "while" loop can be re-written using a "for" loop. O True O False
A: The given question are true or false based question.
Q: Note: The STL (Standard Template Library) stack and queue classes - not Nyhoff's - must be used for…
A: Algorithm for the given problem:- 1. start 2. Initialize a stack and a queue. 3. Input a string. 4.…
Q: What is meant by implicit objects and what are they?
A:
Q: hboard 9 urses oups endar Eb box story udio ? Help Announcements Syllabus Modules Files Discussions…
A: QUESTION 15:- What is it called when a variable is initialized before a loop to guarantee the loop…
Q: What is the sentinel of the loop in the following program? def main(): sum = 0.0 count = 0 X =…
A: A loop is an iterative statement that repeats statement until condition gets false. A sentinel of…
Q: Define - Static Multiple Issue.
A: Definition: The group of instructions that run simultaneously during one clock cycle is known as an…
Q: What is meant by delayed branch?
A: Delayed branch is a conditional branch instruction that can be present in different…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher:
A: Given CIPHER Text: MAXLJGTEAX f(p)=(5p+6) mod 26
Q: A savings account typically accrues savings using compound interest. If you deposit $1,000 with a…
A: the algorithm of the code is shown 1. Enter an initial amount to save: 2. Enter the yearly…
Q: Question 1 ( C++ pseudo code) Design a queue using only stacks. It must support the enqueue and…
A: Algorithms Step1: for the enQueue we need to stack1 and stack2 Step2: if stack1 is not empty then…
Q: Compare the use and the methodology of TEM with SEM? Provide at least one example where each would…
A: SEM Both scanning electron microscopy and scanning electron microscope are abbreviated as SEM. An…
Q: Explain White Noise.
A:
Q: 1. Design single-tape Turing machines that accept the following languages using JFLAP a) L₂=…
A: According to the information given:- we have to design single-tape Turing machines that accept the…
Q: Write the formula for CPU execution time for a program
A: Theory: Computer performance is its work output. The term performance in computer performance…
Q: ber or a special symbol. examples Enter a character: a Category: Alphabet
A: The answer is given below.
Q: include #include using namespace std; //main function int main() { //calling random number…
A: Answer:
Q: Drivers and cars are assigned to the request; and then the driver picks up the user to ride their…
A: This is very simple. Note: The problem is Incomplete. We are not provided anything about the Drivers…
Q: What is meant by branch target address?
A:
Q: Suppose the economies of the world use a set of currencies C1, . . . , Cn; think of these as…
A: Hi please find the solution below and I hope it would be helpful for you.
Q: Define - Static Multiple Issue.
A: Definition: An Issue Packet is the set of instructions that issues together in one clock cycle; the…
Q: Write a recursive function that finds the number of occurrences of a specified letter in a string…
A: The complete code in python is below:
Q: 2 3 In a singly linked list, each item points to the next item and to the previous item. No size…
A: - As per the guidelines, we can solve the first three questions only.
Q: reate a C PROGRAM for reversing a string by using pointers. Test Data : Input a string : Sharmaigne…
A: The answer is given below.
Q: int): Call print_stack(). Define a local string containing "ABCD". Call f2() passing the string…
A: The answer is given below.
Q: 14. What is SMT?
A:
Q: • Write a recursive method named searchList with the following header: • boolean searchList (int[]…
A: We need to write a Java code for recursive search on a list in Java. ***As per the guidelines, only…
Q: • A savings account typically accrues savings using compound interest. If you deposit $1,000 with a…
A: program in Java, to find the compound interest using recursion
Q: Give a brief summary of the benefits and drawbacks of using each of the three main types of…
A: Introduction In a computer network, two or more computers are linked together and share resources,…
Q: what are the Security and privacy in IoT healthcare systems please describe them in detail. thank…
A: Hi please find the solution below and I hope it would be helpful for you.
Q: Write a while loop that lets the user enter a number. The number should be multiplied by 10, and the…
A: Since no programming language is mentioned, I am using python. Algorithm: Start Initialize product…
Q: Differentiate in-order execution from out-of-order execution.
A: A single instruction will spend several clock cycles inside a CPU core, undergoing numerous…
Q: What is pipeline stall?
A: A pipeline stall is a type of fault that slows down the processing of an instruction in RISC or…
Q: Write the instruction format for the jump instruction.
A: Introduction: Instruction format: The instructions that are given to a computer will cause it to…
Q: Question 1 Which of the following is a risk that becomes important when using automatic blocking…
A: The complete answer is below:
Q: Define - Static Multiple Issue.
A: Define - Static Multiple Issue answer in below step.
Q: What is the probability that a number is divisible by 4?
A: Given question: What is the probability that a number is divisible by 4 ? Solution:
Q: The firsrt picture that has on headther "MATCH and PRIZE" does not have to be coded, it is only an…
A: In this question, it is asked to complete the given c++ code for the given lottery system. In…
Q: (ii) What is the value of z after executing the following code? int x = 33; double y = 5; double z =…
A: I have used C++ for represeting the output.
Q: Consider one TCP connection on a path with a bottleneck link with capacity L. We have a file of size…
A: TCP Connection which refers to the one that it is TCP which is connection-oriented, and a connection…
do in FCFS,SJF,SRTF,Priority
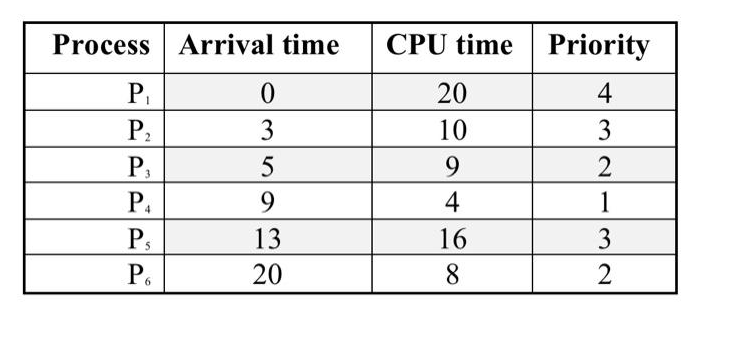
Step by step
Solved in 4 steps with 4 images

- Compare cypher block chaining to cypher feedback mode for sending large files.What percentage is more efficient?"Save and forward" is no longer a common method of communication. Verify the workings.159. _________ is around one-half of the maximum seek time. a. Access time b. Average seek time c. Seek time d. Rotational latency time
- Q1: Define the following terms . 1.Scheduling 2. Jitter 3.Varinble Bit Rate-Nou Real Time (VBR-NRT) 4. Wild Card Filter Style 5. Meter in traffic conditioners70. The protocol that is used for signaling in the telephone network is called ______. a. POP b. SSS c. SS7 d. none of the above View Answerques7 plz provide handwritten ans asap
- Give classification of access technologies.How many steps does it take for KMOS initialization to take placeContention-based access protocols _____. a.are nondeterministic b.scale very well under heavy media use c.have more overheads than controlled-access protocols d.have mechanisms to track the turns to access the media
- Provide a quick summary of the various approaches to handling device requests.Where would this function be executed in the ISO/OSI Reference Model if an encrypted or compressed communications session was needed during a communication session?With respect to computer network interface card, the term 10/100 refers to megabits per second explain?

