Part-1: Write a program that includes in its class the following methods: 1. A method named print Chars that takes two characters and an integer with the following header: public static void printChars (char ch1, char ch2, int numberPerLine) This method prints the characters between ch1 and ch2 with the specified numbers per line. Characters are separated by exactly one space. 2. A method named getLetters that takes two characters and an integer and returns a String with the following header: public static String getLetters (char ch1, char ch2, int numberPerLine) This method returns a String that includes the uppercase and lowercase English letters between chl and ch2 with the specified numbers per line. Letters are separated by exactly one space. 3. In your main method, use the methods you implemented to: a. Print all characters between 1 and Z, ten characters per line. b. Print all English letters between S and j, five characters per line.
Part-1: Write a program that includes in its class the following methods: 1. A method named print Chars that takes two characters and an integer with the following header: public static void printChars (char ch1, char ch2, int numberPerLine) This method prints the characters between ch1 and ch2 with the specified numbers per line. Characters are separated by exactly one space. 2. A method named getLetters that takes two characters and an integer and returns a String with the following header: public static String getLetters (char ch1, char ch2, int numberPerLine) This method returns a String that includes the uppercase and lowercase English letters between chl and ch2 with the specified numbers per line. Letters are separated by exactly one space. 3. In your main method, use the methods you implemented to: a. Print all characters between 1 and Z, ten characters per line. b. Print all English letters between S and j, five characters per line.
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter9: Advanced Modularization Techniques
Section: Chapter Questions
Problem 9RQ
Related questions
Question
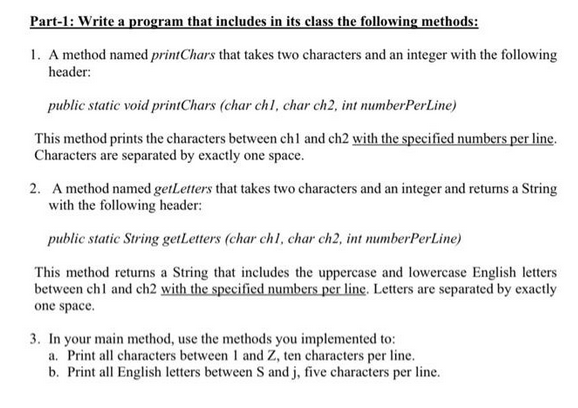
Transcribed Image Text:Part-1: Write a program that includes in its class the following methods:
1. A method named print Chars that takes two characters and an integer with the following
header:
public static void printChars (char ch1, char ch2, int numberPerLine)
This method prints the characters between ch1 and ch2 with the specified numbers per line.
Characters are separated by exactly one space.
2. A method named getLetters that takes two characters and an integer and returns a String
with the following header:
public static String getLetters (char ch1, char ch2, int numberPerLine)
This method returns a String that includes the uppercase and lowercase English letters
between chl and ch2 with the specified numbers per line. Letters are separated by exactly
one space.
3. In your main method, use the methods you implemented to:
a. Print all characters between 1 and Z, ten characters per line.
b. Print all English letters between S and j, five characters per line.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage