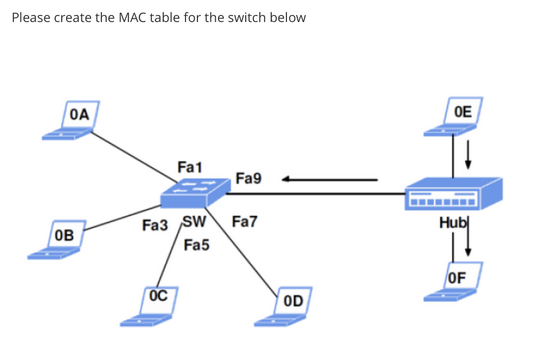
Please create the MAC table for the switch below OA OB Fa1 OC Fa9 Fa3 SW Fa7 Fa5 OD OE Hub OF
Q: the study of computer technology What consequences does everyday computer use have on individuals,…
A: Introduction: Computers and technology are two of today's most often discussed issues. Technology…
Q: Complete this C++ code with the following requirements: Write a program that will allow a user to…
A: C++ introduction:- Bjarne Stroustrup, a computer scientist from Denmark, developed the…
Q: The conventional Software Development Life Cycle has been used in a number of successful system…
A: According to the annual State of the Agile report, Agile is the best SDLC methodology and one of the…
Q: Give an example of a vertically coded control unit and describe your
A: SummaryThe control units are independent of each other. Therefore, this CU offers great flexibility.…
Q: Why would someone use formal methods? The use of specifications in software development must be…
A: Given: Why are formal methods used in the first place? The application of specifications during the…
Q: What characteristics of spoken language make it preferable than computer-generated language?
A: Introduction: Human language sentences are preferred for writing because they are more natural and…
Q: What distinguishes logical data flow diagrams from physical data flow diagrams? MetaData is the most…
A: The response: DFD based on logic: focuses on issues in business. Meetings. It provides a list of…
Q: How Can a Vertical Code Be Used to Create a Control Unit's Strategy?
A: One interpretation of the term "vertical code" is that it refers to a section of code or operators…
Q: What are some of the te programming? What sho programming language?
A: SummaryIn general, we believe that good software can be written in Java, C#, Python, PHP, or any…
Q: What would you want to discover by analyzing the ARP Protocol using Wireshark, and why would you…
A: ARP Protocol: An ever-changing Internet Protocol (IP) address and a fixed physical machine address,…
Q: Part 3 How low? (loops) Write a program that prints out how low low low low low can you go go go go…
A: Code in Python is given below along with output and code screenshot
Q: the Rational Unified process with the Classical Water Fall model side by side?
A: These two models are really part of the SDLC process. A highly organised technique known as…
Q: What are formal techniques used for? In order to be used, specifications in software development…
A: Introduction: Formal techniques are mathematical constructs used to represent complex systems. By…
Q: What precisely is a computer network described as? What constitutes the network's many components?…
A: An Electronic Network: A computer network is a collection of the linked computers that makes it…
Q: Why may software failures not be caused by bugs or faults in the program?
A: Several factors can contribute to the failure of a software project, including unrealistic project…
Q: Change Summation Integers problem to Finding the minimum problem. Make sure you properly…
A: java.lang.Math.min() method : In java, the min() function is an inbuilt function that gives…
Q: Do you have any particular recommendations for capturing the data flow?
A: Introduction: Dataflow: Dataflow is an overarching notion in computer science, with several…
Q: What does the word "automatic programming" refer to, and how does the process work?
A: A kind of computer programming known as automatic programming involves another software creating…
Q: How to string width with specific char in java Program
A: string width with specific char in java Program:-
Q: How long has the discipline of computer science existed?
A: According to these standards, computing can be considered a precise science. The body of knowledge…
Q: Many different models are used in software development, and each one has a different role based on…
A: Definition: Software development employs a variety of models, each of which h as a unique relevance…
Q: Give a colleague information about the ARP protocol. Include details about the layer it operates at…
A: ARP stands for Address Resolution Protocol and is used by routers to maps Internet Protocol (IP)…
Q: What precisely do you mean when you talk about the shared responsibility paradigm in terms of cloud…
A: Definition: A shared responsibility model is a way of looking at cloud security that establishes the…
Q: What proof is there that every kind of software can be written in only one programming language?
A: Here we have given a brief note on software that can be written in only one programming language.…
Q: Programmers with extensive programming language knowledge could benefit from learning more dialects…
A: Computer language Programmers communicate with computers using a programming language (developers).…
Q: ALGO2(A)// A is an integer array, index starting at 1 1:for i=1 to n-1 do 2: for j=n to i+1 do 3:…
A: The correct answer is Option 1), that is, the worst-case running time is a*(n^2) + b*n +c, where a,…
Q: Although model-driven engineering offers numerous benefits, how effective is it in actual use?
A: Model-Driven Engineering: Model-Driven Engineering (MDE) is the practice of elevating models to…
Q: Please describe how this distributed denial of service threat may be examined using security…
A: How to identify and investigate a DDoS attack: In-line inspection of all packages and out-of-band…
Q: What Components Make Up the Different Parts of a Computerized System? If at all possible, provide a…
A: We must comprehensively understand the central processing unit, the input unit, and the output unit.…
Q: There are several obstacles to implementing mobile technologies. How much money may you save by…
A: Definition: There are several obstacles to implementing mobile technologies. A network and a device…
Q: What qualities do you believe the ideal programming language ought to have?
A: Start: The key components of a great programming language are syntax, documentation, error messages,…
Q: What does it imply when someone states that data granularity has been specified?
A: A data structure's amount of detail is gauged by its data granularity. For instance, the name column…
Q: Why would someone use formal methods? The use of specifications in software development must be…
A: Given: Why are formal methods used in the first place? The application of specifications during the…
Q: When you provide null as an argument to the Split function of a string object, what characters are…
A: Split() function: The split() function is used to split the string into substrings of the given…
Q: PYTHON QUESTION: there is 2 different solving methods for our one differential equation.I want to…
A: There are two method given in above problem. We need to plot them different graph. See below step…
Q: What are some of the fundamental tenets of assembly language?
A: Question Can you name some of the most fundamental assembly language principles?
Q: Think about the changes you've witnessed in digital platforms throughout the years. How much have…
A: Digital Platforms: management of social media. The digital world's biggest stars are social…
Q: Why would someone use formal methods? The use of specifications in software development must be…
A: Formal methods are the use of mathematical modelling for the specification development and…
Q: Your assignment is to create a Web page that welcomes the user to the page with an appropriate…
A: Hello student The code will be in next step
Q: the study of computer technology What consequences does everyday computer use have on individuals,…
A: Introduction: It is a type of electronic device that changes information or data. It can store…
Q: What difficulties does using mobile technologies present? How much money will I really save if I…
A: Definition: You may save time and money thanks to mobile technology, which is advantageous for both…
Q: Explain the output The algorithm Seq(n) is shown below. What is the number of recursive call in the…
A: Recursive call : Recursive calls occur when a procedure calls itself or another procedure, which…
Q: It's unclear whether database administrators or server administrators are in charge of backing up…
A: We know that making backups is a necessary operation that must be carried out regularly. We can…
Q: What is the Waterfall method's purpose?
A: In software engineering, the software development process is the process of dividing software…
Q: While defining additional terms, it is also needed to specify terms such as "repository, modeling…
A: CASE: Computer-Aided Software Engineering is known as CASE. It uses a tool-based approach to…
Q: What if you documented the various programming paradigms? How many paradigms do we really require?…
A: A paradigm is a strategy for completing a task or solving a problem. A programming paradigm is a…
Q: 4.2) (L4) Give truth values for the propositional variables that cause the two expressions to have…
A: Truth table:- A truth table is a mathematical table used in logic, specifically in connection with…
Q: How to replace string with another string in java Program
A: The answer for the above question is given in the below step.
Q: What distinguishes the creation of network programs from the creation of other types of software?
A: A program is set of instruction or command to perform some specific task whether it is a network…
Q: Programmers with extensive programming language knowledge could benefit from learning more dialects…
A: 1) JavaScript:- One of the key components of the World Wide Web is the high-level computer language…
Step by step
Solved in 3 steps with 2 images

- Q3 In macOS Pages View > Table of Contents, how do you edit the title of the section independently from editing the first phrase on the title's corresponding page?You're utilizing what type of protocol when you use the ping command.Q2) A) what status code indicates the request object does not exist? B)what is cookie? C)what DNS server is usually owned by the organization?
- In HomeController.cs, set three session states to get course name, student id and date. Use Course, StudentId and CurrentDate(yyyymmdd) as the session variables. Set these states in the IActionResult Tools ( ) method. ASP.NET MVCHope to explain in the code using #. The Excel file is in the link. Thanks a lot https://we.tl/t-cs1Lxia7S6What is the problem with assigning a port number to more than one server application?
- Configure the switch S1 as per below & write the command in the answer text window Configure the host name for the switch Assign pass as the privileged EXEC encrypted password. Assign exams as the VTY password and enable login. Encrypt the clear text passwords.Which command will display the number of hops between your computer and the other?I'm curious about DCL commands. How does DCL distinguish between the two kinds of commands?
- The MAC address 3333.3333.3333 want to send a message to the MAC address 1111.1111.1112, what is the destination device(s) name for the message?Once you have created your domain in Windows Server 2012 0r 2016 or 2019, you will want to create your OUs, user accounts, computer accounts, groups, and so on. Outline the steps to follow.Question 13 sum.Why would you want to run the RODC (read-only domain controller) on Windows 2008 and newer versions? What are available in the newer versions that's not available in previous versions. Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line



