Please Enter Pas word must contain: se letter se letter
Q: As a computer scientist, how would you define magnitude?
A: The representation of a number's magnitude (decimal) in computer science is referred to as the…
Q: What is the default folder in which the ISO file will be stored when it is created automatically?
A: ISO : In addition to ISO file, ISO image is also used. It is common to utilize ISO images to…
Q: Is it possible to distinguish between pure and impure functions?
A:
Q: What is the difference between the Internet and Interspace?
A: Internet is the perfect example of connectivity and a huge network that provides connectivity.
Q: What are Decision Patterns for Manufacturing Processes and how do they work?
A: Decision pattern: A decision pattern is a collection of decisions made before and during the…
Q: What is the difference between a candidate key and an alternative key?
A: Justification: A collection of characteristics that uniquely identify tuples in a database is known…
Q: What is the purpose of the "forward lookup zone" in the DNS?
A: Justification: Reverse lookup zones translate IP addresses to names while forward lookup zones…
Q: Nome and dusbe o (3) major vouer tuncfiony. Rou lers are cvitical Componens of Compukr neluerkg.
A: INTRODUCTION: Here we need to tell the name and describe the major router functions.
Q: For an input image of size 10 x 10, using a vertical edge filter of size 4 x 4 with stride 1 and no…
A: Please refer below for your reference: Size of output image is given by formula: [(W−K+2P)/S]+1…
Q: load in organizations The preceding factor all combine to create a heavy program that rely on…
A: Excessive Program Maintainance: The preceding factors all combined to create a heavy program…
Q: Two schools in the same city sought to share information on e-learning. What kind of network will be…
A: Justification: A wide area network (sometimes referred to as WAN) is a huge network of computers…
Q: What is the syntax for the drop table command?
A: Justification: In SQL, the DROP statement is used to deactivate a component in a relational database…
Q: The 'customer' table contains ten columns but no row. The table is then updated with 10 new rows and…
A: Start: The term "table" refers to a collection of connected data that is recorded in a database in a…
Q: What is the name of the frequency range accessible for data transmission?
A: The bandwidth is the maximum amount of data transmission over an internet in a given time.
Q: An attacker's efforts to assure the success of a sniffer attack must include the following steps.…
A: The main question is, how may an attacker take use of the sniffer system if they have network…
Q: What exactly is a magnetic disk?
A: Disk Magnetism: A magnetic disc is a storage device that uses a magnetization process to write,…
Q: Mr. Rohan has constructed a table called'student,' which contains information such as the student's…
A: Tip A primary column (or a set of columns) is used to uniquely identify rows in a table and database…
Q: 10 11 1 2 Using the given graph, answer the following questions: a. Write the adjacency list of the…
A: The Answer is
Q: When a symbolic constant would suffice, why use a formal argument to provide data into a function?…
A: A formal parameter is a variable that is declared in the function declaration. By invoking a…
Q: Differentiate among point-to-point, ring, and mesh network topologies by stating their advantages…
A: Introduction: The differences between point-to-point, ring, and mesh topologies are as follows:…
Q: What factors should you consider while choosing a database management system?
A: Data management is the process of organizing and maintaining organization data. It entails…
Q: What do you think is the way forward with the Game Changing Technologies that we currently have?…
A: Advanced robotics, black chain, autonomous tram-pent devices, vin-final, augmented reality, and…
Q: What are the most common multimedia file formats?
A: Multimedia: Multimedia is a term that refers to a collection of several types of content, including…
Q: In the absence of control structures, how would programming be affected?
A: Control Structures: Control structures are the primary decision-making element in a programming…
Q: Would you prefer an error to be found during runtime or during compilation?
A: an error to be found during runtime or during compilation?
Q: Show Static structures and external structures can be initialized. The member initializers must be…
A: Show Static structures and external structures can be initialized. The member initializers must be…
Q: eate a flowchart and write a proper C program that continuously prompts the user to enter a positive…
A: We can use a for loop which will run from 1 to n and then find all divisor i such that n%i==0.
Q: PLEASE SOLVE THIS. ADDITION!! Signed Binary Operation: -57610 + 48910
A: This question comes from Number System which is a paper of Computer Science. Let's discuss it in the…
Q: Is the inner loop of the BubbleSort algorithm always executed the same number of times as the outer…
A: Please upvote, I am providing you the correct answer below. Bubble sort in java (Basic…
Q: 8 10 11 4 7 1 2 3 Jsing the given graph, answer the following questions: a. Write the adjacency list…
A: We are given a graph with 12 nodes and it is a directed graph. We will first find out the adjacency…
Q: a) Explain fault, error & failure. Discuss hardware & software fault tolerance with example. a)…
A: As per our guidelines we are suppose to answer only the first question ,if we get multiple…
Q: Please write a code in MATLAB for False Position Method for f(x)=0. After that, please provide a…
A: Start. Get the values for x0, x1 and tolerance. Perform the operation. Print the outputs. Exit.
Q: The use of indices speeds up query processing, although it is usually a terrible idea to establish…
A: Introduction: Indexing in a Database Management System (DBMS): Indexing is a time-saving way of…
Q: Write a parameter and return program that will require the user to enter a temperature in Celsius…
A: The program is written in C++. Check the program screenshot for the correct indentation. Please…
Q: PLEASE SIMPLIFY PLEASE!!!! truth table, simplified equation, and logical diagram. Show your…
A: Please refer below for your reference:
Q: The following is an instance of the conjunctive normal form (CNF) problem. (x1 V x2 V x3) ^ (x3 V…
A: Construct a graph G containing k clusters, each with a maximum of three nodes. A clause in…
Q: The relationship between the sides (a,b) of a right triangle and the hypotenuse (h) is given by the…
A: 1) Below is C++ program that reads in the two sides of triangle and computes the hypotenuse In…
Q: By using C ++ write aprogram to fprint the 0,1,1,2,3, 5,8,13,12,
A: This sequence is called as Fibbonacci Sequence. -> The Fibonacci sequence is a sequence where the…
Q: What is the difference between hashing passwords saved in a file and saving them in a password…
A: Introduction: In this question, we're asked to identify the probable differences between employing a…
Q: Nome and dscribe two (3) major vouer tuncfiony. Rou lers are cvitical Components af Compukr nehuerk.
A: The Answer is in Below Steps
Q: Question 1: Use Dijkstra's Algorithm to find the shortest path length between the vertices a and z…
A: We are going to find out the shortest path length between vertices a and z using Dijkstra's…
Q: how each of the cybersecurity discipline's key ideas is applied to overall system security
A: Cybersecurity: It is an implementation made for protecting computers, network and information or…
Q: Q2: If m-the odd numbers between (10, 25), n- the even numbers between (10, 25) find men (1) m-n (2)…
A: Question from discrete mathematics, computer science topic. Here, we will write the all odd numbers…
Q: What are the roles and responsibilities of data management professionals who contribute to data…
A: Data management is very important for the reputation of an organisation.
Q: 7. The object feature is not inherited if set to private True False
A: Note :- As per our guidelines we are supposed to answer only one question. Kindly repost other…
Q: Is there a distinction between criteria and requirements in the context of software testing?
A: Software Testing: Specific circumstances or ongoing activities that must be present before a…
Q: Why are partitions necessary?
A: Start: Various filesystems may be installed for different types of files thanks to partitioning.…
Q: Write a SQL query to add a column totalprice to a table product with a data type of numeric and a…
A:
Q: What is the default order by command value?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. ASC is the…
Code 44.
Desgn
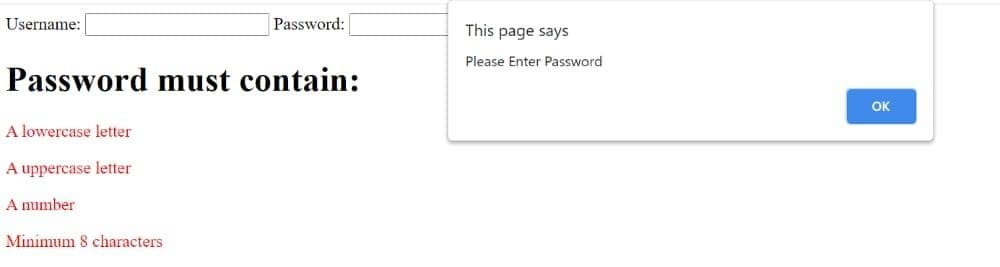
Step by step
Solved in 3 steps with 1 images

- HiI have a homework to create php code for this login pageYou only have to activate the password button and log inOtherwise, it should be identical as in the picture below: Note: Please confirm all details and below the image.You are going to create a Login and Registration page using CodeIgniter 4. Login Email Address Password Require to have validation of user input Valid email address Validate the email address and password before showing home page (Picture as example)<input type="text" id="number" placeholder="Choose from item 1-9"> write a java script code that makes sure once the user enters a number 1 through 9 it is valid for example if the user puts 10 it says "its invalid" under the box in html if they put 3 then it says its valid!
- Create an E-Book application that allows the user to insert an author name, book title, and book category. The user is able to retrieve all the book titles in the E-Book app.Create a web form to help in creating simple random passwords. Your web form should have four text fields named Word1, Word2, Word3, and Word4, as well as “Reset” and “Submit” buttons. You need to create a separate PHP form-processing script that verifies that all four words are entered, that all of them contain only letters, and that all four are between 4 and 7 characters long. Once all of the words have been verified as correct, use the strtoupper() and str_shuffle() functions to produce four suggested jumbled sets of passwords using the words entered in the text fields Note: you need to perform the validation on the server side using PHP scripts. use the preg_match() function to check for lettersSocial security numbers can be entered either as ddddddddd or ddd-dd-dddd. Write a regular expression to match either pattern.
- C++ OOP You are creating an Employee Record App. Following information is required to store.o name. A string that holds the employee’s name.o idNumber. An int variable that holds the employee’s ID number.o department. A string that holds the name of the department where the employeeworks.o position. A string that holds the employee’s job title.o CovidStatus: Either the employee has been covid Positive or not.Which class is used to create a badge? .label .badge .tag .flagWindow 1Should have a welcome message, a textbox to receive AN EXISTING ID of the user and a button to access the data base. All users ID should be saved in a data base (Don’t use access). Once the Id is verified then the program will give the user access to the main menu window.Your database should have the following columns.
- Create a menu-driven application to keep track of a list of subscribers to a newsletter.The application should allow the user to add a new subscriber, remove a current subscriber, update a subscriber’s data, and display the current list of subscribers. Each subscriber should be identified by a unique ID assigned by the system.For each subscriber, you need to store first name, last name, and email address.The application must have:• A linked list as the main data structure in the application. You must use the C++ Standard Template Library (STL).• A “subscriber” class that contains data and methods related to each subscriber.Create Kotlin Project (Mobile Application) Create a Birthday Card app that accepts a person's name and date of birth. Clicking the Submit button will load a new activity which will display the person's name, age, birthstone, and Chinese Zodiac sign. Submit layout files (.xml), code behind file(s) (.kt), and manifest file.Create a project named MyFlix. Its Form contains a ListBox with the titles of at least six movies or TV shows available to purchase. Provide directions that tell users they can choose as many downloads as they want by holding down the Ctrl key while making selections. When the user clicks a Button to indicate the choices are final, display the number of selections made and total price, which is $1.99 per download. If the user selects or deselects items and clicks the button again, make sure the total is updated correctly.





