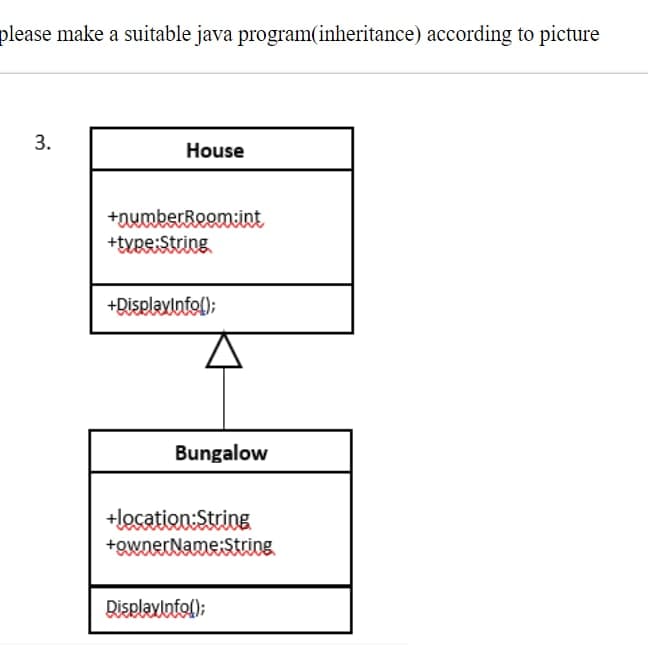
▪lease make a suitable java program(inheritance) according to picture 3. House +numberRoom:int +type:String +DisplayInfo(); Bungalow +location:String +ownerName:String DisplayInfo();
Q: Discuss how technical review and legal review compliment each other. Why is this holistic approach…
A: Answer: We have discussed about the technical review and legal review compliment each other. and why…
Q: at is the logic behind Queens Prob
A: Introduction: Problem of arranging eight queens on anchessboard so that none of them attack each…
Q: vlysteryExami Language/Type: Java parameters return The following console program uses parameters…
A: Here we have a function named hamburger(), which takes 3 string parameters, prints them on the…
Q: ure of Google Maps would you like to alter or add? Explain in both words and illus
A: Introduction: Google Maps began as a C++ programme developed at Sydney-based Where 2 Technologies by…
Q: Show the steps of insertion sort following the example of the solved problems on the handout for the…
A: Answer: We need to write the insertion how it work so we will see in the more details with the…
Q: In linux code: 1. Identify command name options in the following command line $ ls -l / /usr . $…
A: The above question is solved in step 2 :-
Q: The following MIPS instructions are executed: 11: SUB R1, R5, R7 12: ADD R1, R1, R5 13: SUB R1, R7,…
A: MIPS ( Millions of Insttruction per second), It is one of the ways to compute the raw speed of the…
Q: What is privileged communication/confidentiality? Identify a scenario where a mental health…
A: The above question is solved in step 2 :-
Q: a + b * C + d
A: Binary Tree:- Each parent node can have a maximum of two children in a binary tree, which is a type…
Q: Consider the following code: Queue q = new LinkedList(); q.add(5); q.add(7);…
A: Queue is used to keep the elements that are processed in the First In First Out (FIFO) manner.…
Q: Write aAlgorithm for Blocks Image Input: a base and strong generating set of a group G acting on fl;…
A: given data:- Input: a base and strong generating set of a group G acting on fl;an invariant…
Q: a) A+B+C/D b) A (B-(C-D)/(E+F));
A: Draw the expression trees that represent the following expressions ? 1). A + B + C / D 2). A - (B…
Q: Write a Python function named check_email(email_address) takes as input a string (possibly)…
A: Here is the python code of the above problem. See below steps.
Q: Q.19 Explain in brief "Security of Hasn functions.
A: Hash function The motivation behind a hash function is to squeeze a bunch of inputs of any size into…
Q: What are the theta values for the recurrences given below in Q1-Q3? (Show your work in details) (1)…
A:
Q: Home Courses Scheduled My Plans Light up your Lanterns and Roam around to get as many candies as you…
A: The complete code in Notepad++ is given below:
Q: Suppose three algorithms A, B, and C, can be implemented to perform a task. The algorithms have the…
A: Introduction The duration of input determines how long it takes for an algorithm to execute, which…
Q: Perform the following number conversions. (You are required to show your conversion steps learly.)…
A: 1. (7563)8 :: - = 7*83 +5*82 +6*81 + 3*80 = 7*512 + 5*64 + 48 + 3 = 3584 + 320 + 51 = (3955)10 2.…
Q: TDMA frame" is composed of eight disti
A: The answer is
Q: convertToAltCaps ♡ Language/Type: Related Links: Java string return String V Write a method named…
A: Approach to define the method: Create a function convertToAltCaps to convert alternate character to…
Q: Write a while loop that prints the multiples of 3 from 300 down to 3. A decrement operator (++ or…
A: Here I have defined a variable named num and initialized it with a value of 300. Next, I have…
Q: Q1. Given the following dictionary: players = {'Adam Vinatieri': 49, 'Trevor Lawrence': 21, 'Kyle…
A: The python program is given below:
Q: 417118.2791720.qx3zqy7 Jump to level 1 Declare a Boolean variable named allValid. Read in an input…
A: The above question is solved in step 2 :-
Q: Write a function build_csv_string(data) that takes in a list data. data will be a list of lists,…
A: Code
Q: Two DNA strands of length 100 (number of bases in the sequence) are given in DNA1.txt and DNA2.txt…
A: Python introduction:- Similar to the English language, Python has a straightforward syntax. Python…
Q: Minimize z = 3x1 + 6x2 subject to X1 + 2x2 5 X1, X2 > 0
A: Here, As you have not mentioned which one to solve, so I am just solving the first to give you the…
Q: For LL(1) parsers, the following must happen: Chose the correct anwser below: Grammar can have…
A: As given, we need to choose the correct answer for the given question - Grammar must follow which…
Q: Explain types of Intrusion detection systems (IDS).
A: An Intrusion Detection System (IDS) which are the system that monitors the network traffic which are…
Q: What does the output of dir in this case show? x = "/home/username/thesis/data" dir(x) Select one:…
A: The above question is for Python language. We have given a code, and we need to choose suitable…
Q: 2. Use a paper-and-pencil approach to compute the following division in binary. i. Dividend = 1110,…
A: Binary In general, binary represents anything that consists of two things or parts. In the context…
Q: Develop a realistic retirement-planning simulation model for your personal situation. If you are…
A: answer Now, after retirement you will have a corpus of $2.94 million at your disposal, and can…
Q: Consider the grammar below: SaBCa B →dBd | a CeCe a (a) Construct the LR(0) canonical set of item.…
A: Context Free Grammar S -> aBCa B -> dBd | a C -> eCe | a SLR 1 Items:
Q: 1. (4 points) Suppose we have a hash table of size 29 and we want to implement a system for looking…
A: 1. (4 points) Suppose we have a hash table of size 29 and we want to implement a system for…
Q: A Media Access Control (MAC) protocol is used to control when and what a computer transmits. With an…
A: A media access control (MAC) is a network data transfer policy that controls how data is sent over a…
Q: # The data has features ID, Race, Age, Sex, Hour, IQ and Height with class variable Died. The aim is…
A: Below I have provided the solution to the given question. Also I have attached the screenshot of the…
Q: 1. (4 points) Suppose we have a hash table of size 29 and we want to implement a system for looking…
A: ANSWER:-
Q: Suppose three algorithms A, B, and C, can be implemented to perform a task. The algorithms have the…
A: Answer : For the size 100. The time complexities given are : O(n) , O(n^2) , O(log2(n))
Q: I am sorry but you did not provide the answer to the problem!!!
A: The range() method in Python creates an immutable sequence of numbers beginning with the provided…
Q: Assuming an 8-bit system is used (i.e. the system uses 8 bits to represent an integer): -6710-6710…
A: Foundation This question comes from Number System which is a paper of Computer Science. Let's…
Q: Suppose you wrote a program that you suspect is in an infinite loop because it just keeps running…
A: The above question is solved in step 2 :-
Q: CSU asks you to design an loT system for smart lights on the Albury-Wodonga campus. Your design…
A: Solution : Smart Lighting System : IoT can be used to create a smart lighting system that allows…
Q: All print output should include descriptions as shown in the example output below. 1) Dictionary…
A: //Python Code: # Create a dictionary of fruit and desserts made from the fruit. fruit is the key and…
Q: e the left recursion from the pr E →E+T|E-T|T T→T* FT/F|F
A: Introduction: The grammar is changed by left factoring to make it suitable for top-down parsers.With…
Q: After executing the following piece of code: mass_kg = 1 mass_lb = mass_kg * 2.2 mass_kg = mass_kg +…
A: The complete answer in python language is below:
Q: To isolate the variable in the expression x-17, one would
A: The above question is solved in step 2 :-
Q: cial settings in the paper where different types of social signal measurements were used to predict…
A: Introduction: The Special Issue Editorial introduces the research environment in which Social Signal…
Q: modifier: Consider the following grammar, with terminals noun, verb, and T→ SVO S → noun | MS V →…
A: Parsing Table : An LR parser using tables created from a grammar by a parser generator is one…
Q: Let EK: {0,1}128 → {0, 1}128 be an ideal block cipher with message space {0, 1}128, ciphertext space…
A: Hash function The purpose of a hash function is to fit a set of inputs of any size into the a table…
Q: Select the class relationship that best describes the following scenario: • Class B creates an…
A: UML stands for Unified Modelling language, It is a type of general purpose modeling language used to…
Q: Insert the keys into hash table of size m=11 using linear probing hashing. Here, h(k, i) =((k mod…
A: Inserting 1313 mod 11 = 213 is inserted at position 2 Inserting 1919 mod 11 = 819 is inserted at…
OOPs
In today's technology-driven world, computer programming skills are in high demand. The object-oriented programming (OOP) approach is very much useful while designing and maintaining software programs. Object-oriented programming (OOP) is a basic programming paradigm that almost every developer has used at some stage in their career.
Constructor
The easiest way to think of a constructor in object-oriented programming (OOP) languages is:
Step by step
Solved in 2 steps

- create a java program that uses polymorphism, inheritance, and recursion. can be anything, but needs to be less than 3 classesCreate A Java Program that Suffice the two images attached. They cover inheritance ,method over-riding and polymorphism.Explain the following Java Abstraction code in details and draw the UMLnotations diagram.abstract public class Shape{private String color;public Shape (String color){this.color = color;}public String toString(){return "Shape of color=\"" + color + "\"";}abstract public double getArea();}public class Rectangle extends Shape{private int length;private int width;public Rectangle(String color, int length, int width){super(color);this.length = length;this.width = width;}public String toString(){return "Rectangle of length=" + length + " andwidth=" + width + ", subclass of " + super.toString();}public double getArea(){return length*width;}}public class Triangle extends Shape{private int base;private int height;public Triangle(String color, int base, int height){super(color);this.base = base;this.height = height;}public String toString(){return "Triangle of base=" + base + " and height="+ height + ", subclass of " + super.toString();}public double getArea(){return 0.5*base*height;}}public…
- please make a suitable java program(inheritance) according to picture.. please show outputWrite a suitable inheritance program according to the following program in Java, and print an outputUSING JAVA: Enhance the Invoice-printing program by providing for two kinds of line items: One kind describes products that are purchased in a certain numerical quantities ( Such as “3 toasters”), another describes a fixed charge ( Such as “shipping $5.00”). Hint: Use inheritance. Produce a UML diagram of your modified implementation.
- write a java program use the principle Inheritance to create two class first-class name is Car and the second-class name is type car (اسم الكلاس الثاني انت اختار نوع السيارة على كيفك) then second-class extends from first-class then print all properties the type car ************ parameter Car class (color , size , model ) ////// parameter type car class (type , name , serial number )write a java program use the principle Inheritance to create two class first-class name is Car and the second-class name is type car then second-class extends from first-class then print all properties the type car ************ parameter Car class (color , size , model ) ////// parameter type car class (type , name , serial number )Hi can you help me to solve this question using java language , we have to use oop in this question also use string , we are not allow to use any thing inheritance
- In this problem you will implement a simple library system based on object-oriented approach (using inheritance, polymorphism and abstract classes). At the library we have items and people are allowed to borrow them for a while or use them in the library premises. We have 3 types of items at the library. Books, Magazines and Compact Discs (CDs). All items have a unique number called serial number, shelf number that the item put on that shelf and shelf index, the index of the item at the shelf. Items at the library have additional different properties changing to item type. For example books have name, publisher name, and author name. CDs have title property and magazines have name, publisher properties. But people are allowed to borrow only books and CDs, but not magazines. Suppose that two kinds of people using library items. These are students and academic staff. Students can borrow only one item at a time, and academic stuffs can borrow at most 3 items at the same time. Also people…. Draw an inheritance hierarchy representing parts of a computer system (processor, memory, disk drive, DVD drive, printer, scanner, keyboard, mouse, etc.). (BlueJ)Draw a Class Diagram of a GUI Java Checkers game where player 1 chooses to play with CPU or player 2 (multiplayer).

