Two DNA strands of length 100 (number of bases in the sequence) are given in DNA1.txt and DNA2.txt file. Solve the LCS problem using dynamic programming top-down (memorization) approach. Submit your code to solve the problem. How much time (in seconds or milliseconds) is required by your computer to run the algorithm.
Two DNA strands of length 100 (number of bases in the sequence) are given in DNA1.txt and DNA2.txt file. Solve the LCS problem using dynamic programming top-down (memorization) approach. Submit your code to solve the problem. How much time (in seconds or milliseconds) is required by your computer to run the algorithm.
Chapter10: Application Development
Section: Chapter Questions
Problem 9VE
Related questions
Question
Two DNA strands of length 100 (number of bases in the sequence) are given in DNA1.txt and DNA2.txt file.
- Solve the LCS problem using dynamic
programming top-down (memorization) approach. Submit your code to solve the problem. How much time (in seconds or milliseconds) is required by your computer to run thealgorithm .
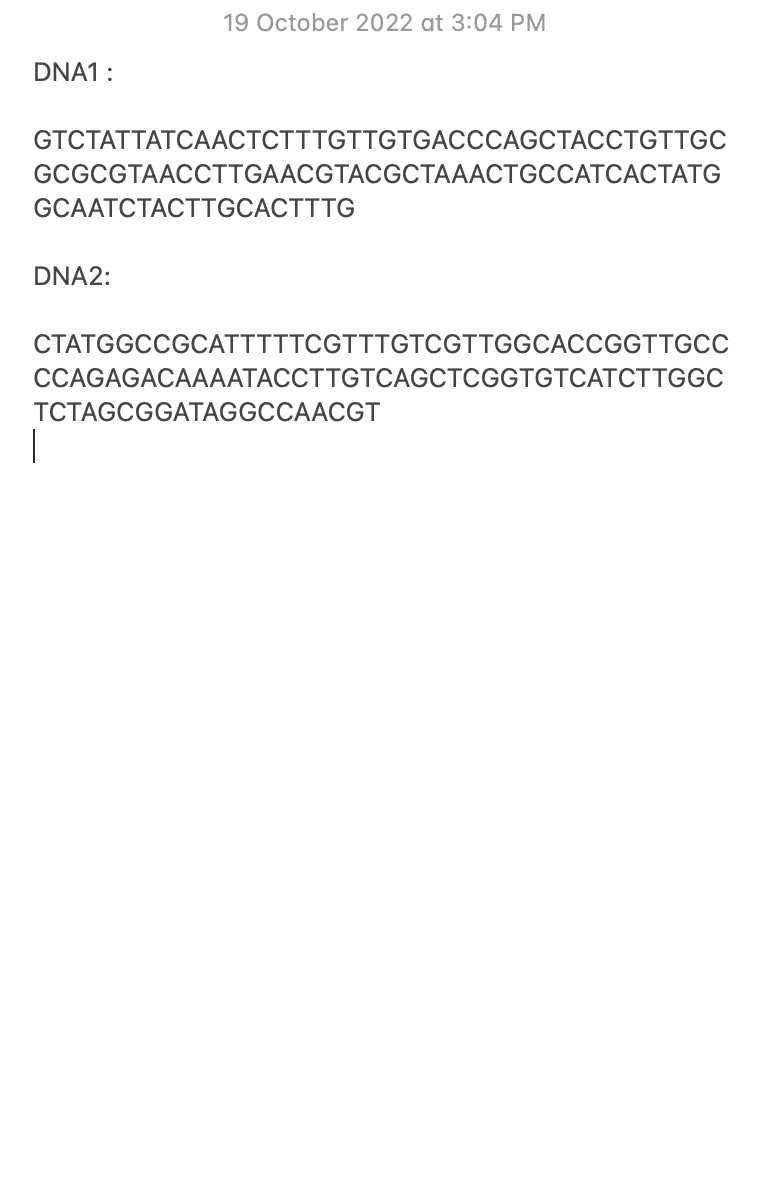
Transcribed Image Text:DNA1:
GTCTATTATCAACTCTTTGTTGTGACCCAGCTACCTGTTGC
GCGCGTAACCTTGAACGTACGCTAAACTGCCATCACTATG
19 October 2022 at 3:04 PM
GCAATCTACTTGCACTTTG
DNA2:
CTATGGCCGCATTTTTCGTTTGTCGTTGGCACCGGTTGCC
CCAGAGACAAAATACCTTGTCAGCTCGGTGTCATCTTGGC
TCTAGCGGATAGGCCAACGT
I
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning