please solve with python language ...And don't copy from chatgpt please please,humble request. no explamination needed ,,only code
Q: How do we know if wifi networks are safe?
A: The answer is given below step.
Q: Who are "accelerated filers," and what criteria (such as income or number of employees) are used to…
A: Accelerated filers are American public firms who have a faster deadline than other companies to…
Q: riteprogram that takes in a year and determines whether that year is a leap year..
A: code works: The program defines a function is_leap_year(user_year) that takes in a year as an…
Q: While some computer fraud may be intentional, such as hacking, other types may be unintentional,…
A: 1. The statement is true because computer fraud can occur intentionally or unintentionally. For…
Q: What are some of the ethical and legal issues that arise from the use of big data analytics and…
A: Privacy: The collection, storage, and analysis of large volumes of personal data can lead to…
Q: Knowing only the "type" of a variable may provide insufficient information. Each variable is…
A: 1) Variables in programming are typically categorized into different data types, which determine the…
Q: If you could provide four persuasive arguments in favour of continuous event simulation, I'd be…
A: As technology continues to advance, so too does the need for accurate and efficient modeling and…
Q: How much does it need to be made sure that the change from batch processing to serial processing…
A: The answer is given below step.
Q: The Boolean function F(x, y) = x'y + xy' + (x+y')x can be simplified to:
A: F(x,y)= x'y + xy' + (x+y')x
Q: I am writing a C# program that uses LINQ. This is what it is supposed to do: Take a sequence of…
A: The Where method is used to filter the sequence by keeping only even integers. The Select method is…
Q: Write the assembly language equivalent for the machine instruction: 0001101000001000. (Address…
A: MARIE stands for Machine Architecture that is Really Intuitive and Easy. It is basically a simple…
Q: Given the following CFG a) Convert the CFG to an equivalent CFG in GNF. b) Construct an NPDA that…
A: In formal language concept, a context-free language (CFL) which refers to the one it is a language…
Q: I need help with my java compiler program by Generating intermediate code from the AST, such as…
A: The code provided is a simple Java calculator software that can evaluate mathematical statements…
Q: using python Use the list n = [34, 24, 14, ‘eleven’, 21, 31, 41] to answer the following question:…
A:
Q: Consider f(x) = 3x³ - 2 and g(x) = 1 2x+1 the program prints the value of (fog)(x) and the value of…
A: 1. Def g(x)= return 1/(2*x+1) 2. Def f(x)= return 3*x*x*x -2 3. Read value of x. 4. Find f(g(x))…
Q: According to you, the most significant change is the shift from serial processing to bulk…
A: The transition from serial to bulk processing is an important movement in computer science that has…
Q: Given the nature of a set, one could implement the Set interface using any one of a variety of other…
A: One technique to creating a Set data structure is to implement the Set interface using a LinkedList.…
Q: Does the Object-Oriented Design concept have a name? Developing Object-Oriented Software
A: Object-Oriented Design (OOD) is a fundamental concept in computer science that is widely used in…
Q: Implementation of C++ Median-of-Three Partitioning display the quickSort2.cpp software with…
A: The C++ code is given below with output screenshot Algorithm Define a class called Array with a…
Q: This week's discussion topic focuses on functional requirements. These need to be clearly written so…
A: The question asks for an analysis and evaluation of a student's response to a prompt about…
Q: I need to be able to test all 3 test cases at the same time like I can't delete one and do the other…
A: In this question we have to modify the code for a test case to ask for input values 3 times Let's…
Q: How susceptible is your system to the numerous potential security hazards that exist in the digital…
A: Systems are susceptible to a wide range of potential security hazards in the digital domain,…
Q: 3. Consider the two scenarios below: a. An electrocardiogram waveform is sampled by a computer…
A: Digital signal processing (DSP) is an essential part of many modern technological applications,…
Q: Which of the following is the time equation of the Hesap function? Hesap(n) if n==0 return 1 else…
A: The time equation of the Hesap function can be determined using the master theorem, which provides a…
Q: spot is, how it operates,
A: Internet is simply called as Net. Internet is a collection of interconnected devices which shares…
Q: Security, crime, privacy, social interactions, and even government are just few of the many areas…
A: 1) Computer ethics is a broad field that explores the ethical and societal implications of the use…
Q: Find a phrase-structure grammar for this language: the set of bit strings consisting of an even…
A: Phrase-structure In linguistics and computer science, grammar is a formal way for describing a…
Q: Given ip address 130.30.0.0 Complete a table for the first 4 subnets in the network and give the…
A: subnets are used to divide a larger network into smaller, more manageable sections. This can be done…
Q: Problem#6 6.10 A set of final examination grades in an introductory statistics course is normally…
A: We have to explain the code and also we have to write a code for the given instruction in R…
Q: Explore the websites of Cisco, Oracle, and Microsoft, plus two additional sites of your choosing…
A: Before embarking on the task of exploring the websites of Cisco , Oracle and Microsoft , as well as…
Q: Answer the given question with a proper explanation and step-by-step solution and don't copy past…
A: - We need to get an optimal parenthesization and the minimum number of scalar multiplications for a…
Q: The Boolean expressions (xy)' = x'+y' and (x + x)' = x'y' are examples of (the):
A: The question is asking about two Boolean expressions and what kind of properties they represent in…
Q: How does the Diffie-Hellman key exchange protocol work? Give an example. How does the…
A: Cryptography: The study of secure communication while third parties or enemies are present is known…
Q: What would be most important to you if you had to switch to a system that handles data in batches?…
A: Batch processing is the method computers which is use to periodically complete the high-volume and…
Q: What is the name of the law in Europe that regulates data privacy? A) GPDR B) DSA C) license…
A: General Data Protection Regulation is a comprehensive data protection regulation that was…
Q: Write a program in C that asks the user to enter a number of seconds and works as follows: • There…
A: Answer to the above question is given below
Q: Because of the nature of a set, the Set interface may be implemented using a variety of other…
A: What is the set interface ? In the java programming language the set interface is nothing but the…
Q: Describe a linear-time algorithm for computing the strongn connected component containing a given…
A: A strongly connected component (SCC) of a directed graph is a subgraph that has a directed path…
Q: What can you discern about an object's attributes in the Designer simply by examining its bounding…
A: In computer science, a bounding box is a rectangular box that encapsulates an object or a group of…
Q: Why are internal and external routing protocols so prevalent in the twenty-first century?
A: In the twenty-first century, internal and external routing protocols are used for a number of…
Q: In a three-tier architecture, the intermediate layer resides between the client servers and the…
A: Certainly! In a three-tier architecture, also known as a three-tier model or three-tier application,…
Q: The "Internet of things" now exists. "three new fascinating uses"
A: The "Internet of Things" (IoT) is a network of interconnected physical objects, such as cars and…
Q: Consider what you would do in the event of a catastrophe. What distinguishes a mobile backup…
A: Protecting the data in the event of a catastrophe is of utmost importance. Catastrophes such as…
Q: What are some of the key considerations that must be taken into account when designing and…
A: In today's increasingly digital world, cybersecurity is of utmost importance to businesses and…
Q: The Java hash function for Strings generates a hash code based on the string's maximum length. Given…
A: The maximum length of a string, which is 231 - 1, is the foundation for the Java hash function for…
Q: Can you clarify why Pinterest considers Google to be its primary rival? Pinterest has distinguished…
A: What is google: Google is a technology company that operates in the search and digital advertising…
Q: Given an integer array [A], efficiently find a descending sorted triplet such that: A[i]>A[i]> A[k]…
A: We can solve this problem in O(n) time complexity using a variation of the LIS (Longest Increasing…
Q: What can be considered the “currency” that corporations want? A)consumer information B)limited…
A: In today's digital age, corporations are seeking resources that can provide them with a competitive…
Q: I need to be able to test all 3 test cases at the same time like I can't delete one and do the other…
A: Two Python codes are given below Code (if you want to enter all inputs at one run) Code (if you…
Q: First, the term "technical documentation" must be defined. Exists a table that compares and…
A: Technical documentation and user documentation are two different types of documentation that serve…
please solve with python language ...And don't copy from chatgpt please please,humble request.
no explamination needed ,,only code
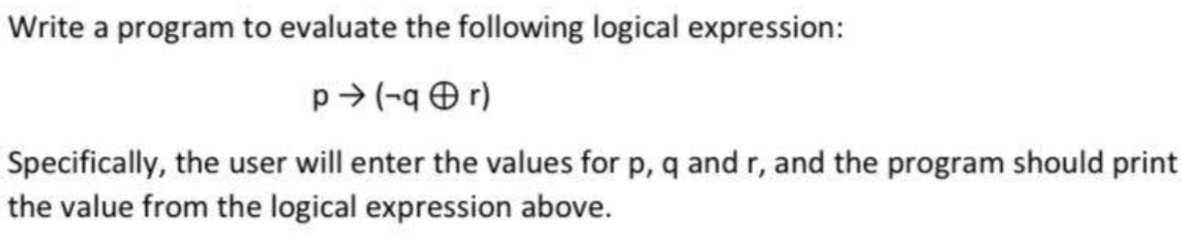
Step by step
Solved in 3 steps with 1 images

- Construct a truth table for the statements belowa. (p ∧ q) ∧ (~r ∨ q).b. ~[~p ∧ (q ∧ r)]c. [p ∧ (q ∨ ~p)] → ~p then find the truth value of the statement givena. p is a false statement, q is a true statement and r is a true statement.b. p is a false statement, q is a false statement and r is a false statement.c. p is a false statement, q is a false statement and r is a true statement.Exercise 1.3.4: Truth tables for logical expressions with conditional operations. info About Give a truth table for each expression. (a) (¬p ∧ q) → p (b) (p → q) → (q → p) (c) (p ∨ q) ↔ (q → ¬p) (d) (p ↔ q) ⊕ (p ↔ ¬q) (e) (p ∨ q) ↔ (q ∧ p)Evaluate the following infix expression using algorithm and choose the correct answer. a+b*c-d/e^f where a=1, b=2, c=3, d=4, e=2, f=2. i) 6 ii) 8 iii) 9 iv) 7
- Write the pseudocode that will adequately represent the logic contained in the scenario below:“If a student has studied less than six years and have passed his Grade 12 exams he can obtain entry into a tertiary course.”Using these values: m = 12, n = 24, p = 6, q = 3, r = 2, s = 4, and t = 1,, show whether the following Boolean expressions evaluate to ‘true’ or ‘false’: if (m > p) and (q > s) and (r > t) then print true else print false if (m > n*p) or (q*r < p) or (p > s+t) then print true else print false if (m/p = r) and (p-q = r) or (p+q = 2*s) then print true else print falseCreate a DFA to match the following regular expression. Remember to show accepting states. (a | b)(a | c)*b
- Construct a truth table to decide if the two statements are equivalent. ~p ∧ ~q; ~(p ∨ q) TRUE FALSEdesign by C++ Using subroutines write a program to perform numerical integration of f(x)=x^2*sin(x)*exp(x^2) over x=[0,Pi] having a choice of (i) rectangular rule (ii) the Simpson’s rule Divide the domain into N subsections, where N=20,40. Compare your results.Complete the truth table for the given statements and then determine if the two statements are logically equivalent. ∼p∨∼q∼p∨∼q and p⇒∼q
- Determine whether statement forms p ∧ (q ∨ r) and (p ∧ q) ∨ (p ∧ r) are logically equivalent.Justify your answer.Simplify the following Boolean expressions to a minimum number of literals: (Note:Literal(AND,OR,NOT)) ∗ xyz + x ′ y + xyz’ a ′ bc + abc ′ + abc + a ′ bc’1;Write a c-program that can detect if a given function is increasing or descreasing. 2:Write a c-program to calculate R5 for the below relational matrix MR. MR =[1 1 1 01 1 1 11 0 0 00 1 1 1] 3.Write a c-program to evaluate and print the truth table for (P ∧ Q) ∨ R.

