Premises: p → (q ^r), s⇒r, r → p. Prove: s →q. p→ (q^r) Premise s r Premise Premise 1 23456789 4 r→ p S r Р (q^r) q s q
Q: The Jaccard similarity can be applied to sets of elements. Sometimes, documents (or other objects)…
A: The question is solved in step2
Q: At your university or workplace, is there an AUP in place? What are some prohibited activities…
A:
Q: Write a Class named "Login" where it has private data members of String Username and String…
A: ALGORITHM : 1. Start2. Create a new class called Login.2. Declare two variables, username, and…
Q: Bruce Wayne has been assigned 98.127.64.0/22. How many IPs total is in that subnet?
A: Check for explanation in step 2
Q: If an array has n elements, what are the values of the indices of the first and last elements
A: Array : An array is a data structure that stores related data items. It is the most basic type of…
Q: 429668.2827918.qx3zqy7 Jump to level 1 Write multiple if statements: If car_year is before 1967,…
A: The above question is solved in step 2 :-
Q: What steps can a systems analyst take to guarantee a solid groundwork for system design?
A: System analyst: A system analyst is a professional who evaluates a business or organization's…
Q: You must take responsibility for evaluating your digital holdings. Describe the steps you'd take to…
A: Digital holdings: Digital holdings are collections of digital assets, such as documents, images,…
Q: In Java Assume code that has imported Scanner and instantiated it for keyboard input as stdln.…
A: In java process to create array is: first declare array ://sets variable with data type then…
Q: Question 8 Cross-validation can be used to get rid of A Local minima B none of the answers…
A: Cross validation: Cross-validation is a technique for evaluating ML models that involves training…
Q: Asset management was not given enough attention or understood at the firm you just audited. How can…
A: Asset Administration: In general, good management of investments made into any kind of organisation…
Q: +
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT---------------
Q: information security strategy for your MIS, it is essential to first identify the various cyber…
A: Dear Student, The answer to your question is given below -
Q: (a) Express the binary number 1111110 in octal, decimal and hexadecimal (b) Express the octal…
A: The answer is given below step.
Q: 13. In cell A17, use the SUMIF function and structured references to display the total membership in…
A: SUMIF function : One of the math and trig functions, SUMIFS, adds all of the inputs that satisfy…
Q: Figure Q4 shows the overview of device management with user and kernel operation modes. Answer the…
A: Introduction: The User mode is the standard mode in which the process has limited access. While the…
Q: Instructions: 1. Create and define a class called GradeCalc that has the following: 7 variables all…
A: Note: You not mentioned programming language so i will be answer in c++ code: #include…
Q: Draw the exchanges of numbers for a four-dimensional hypercube, using the parallel hypercube…
A: Introduction: An algorithm is used to solve a problem or conduct a calculation. Algorithms function…
Q: Make a simple diagram that clearly shows the overall layout of a real-time system. Can you provide…
A: Introduction: REAL-TIME OPERATING SYSTEMS (RTOS) consist of "Real-Time" and "Operating System". An…
Q: Deadlocks select which is true options: a If a resource-allocation graph is expedient, a knot is a…
A: Deadlock:- Deadlock is a situation in which two or more competing actions are waiting for the other…
Q: Print the next smallest and largest positive integers that have the same number of 1 bits in their…
A: A simple method is to count the number of ls in n and then increase (or decrease) until you find a…
Q: Building #11 is undergoing a major renovation. Implement a query to close all requests from…
A: The question is solved in step2
Q: In python In this assignment, we’ll be creating several different classes to represent the crew of…
A: The python program is given below:
Q: I have the following code: import java.util.*; import java.io.*; public class GradeBook…
A: Solution: This error comes because MIDTRM_MAX_POINTS is defined as MIDTEM_MAX_POINTS in…
Q: Give a recurrence relation for W(n),
A: A recurrence is an equation or inequality that describes a function in terms of its values on…
Q: cyber
A: Dear Student, The answer to your question is given below -
Q: Why doesn’t this work? And how does the marcher class work? Thanks!
A: import java.util.Scanner; import java.util.regex.Matcher; import java.util.regex.Pattern; public…
Q: I need help with this assignment
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT…
Q: Write a Procedure code in MIPS assembly language for the following subroutine: (Note that 3 integers…
A: Solution: Given, int aFunction(int w, int x, int y){ int f; q = (w == 1) ? x+y : x-y;…
Q: The data transfer rate of wireless networks is extremely slow in comparison to wired ones.
A: One explanation is that all contemporary Ethernets are full duplexes, but a wireless LAN operates in…
Q: What is the general reason for a software licensing? A. to protect the intellectual property of the…
A: Software licensing- Software licensing is the legal agreement between a software vendor and an end…
Q: The intent of the DSL is to specify commands which forward to another object, but which always…
A: The question is solved in step2
Q: do a flowchart and pseudo-code algorithm for the snake game in language C
A: Algorithm for snake game: The individual algorithms and flowcharts have been present in a sequential…
Q: Using at least one of following ADTS : Array, Grid, Stack, Queue, and LinkedList. write a python…
A: ALGORITHM : 1. Start2. Define a 9x9 grid and assign each cell an initial value of 0.3. Define a…
Q: Maintenance is an essential task that is often considered to be dull. In information security,…
A: The question is solved in step2
Q: Which development methodology, Waterfall or Agile, is more suited for a university's online course…
A: Dear Student, The answer to your question is given below -
Q: More than 90% of the microprocessors/micro-controllers applications. Why? Could you explain this…
A: The above question is solved in step 2 :-
Q: Previous research on the subject of The dark side of technology: toward a remedy for college…
A: INTRODUCTION: We now enjoy luxuries and conveniences that were difficult to conceive even a…
Q: Do you understand the duties of a database administrator?
A: To store and arrange data, database administrators need specialised software. Capacity planning,…
Q: For the scheduling method "Round Robin" (RR), specify the average execution time (average turnaround…
A: All the process arrive at same time in the sequence P1->P2->P3->P4. The time quantum time…
Q: [F] Is each of the following statements true or false? (21) "If two graphs are isomorphic, then…
A: The degree sequence of a graph is the sequence of the degrees of the vertices in ascending order.
Q: Create a Java Program to find the sum and the average of all integers greater than 100 and less than…
A: Please find the answer below :
Q: 3. Model the enterprise architecture design of the following scenario using Activity diagram…
A: Below i have provided the solution to the given question
Q: Discuss the most common sources of risk in IT projects and the steps used to lessen or eliminate…
A: IT: IT stores and retrieves data using computer systems. It's leveraging technology to make business…
Q: Your task is to locate and summarise two peer-reviewed research articles on project management…
A: Articles about project management ethics: The first paper is titled "Workplace Bullying: An Ethical…
Q: Given a list (43, 74, 88, 35, 60, 98) and a gap array of (3, 2, 1): What is the list after shell…
A: Shell sort is based on the Insertion sorting algorithm and it belongs to the group of very efficient…
Q: List some of the features that define the Just in Time approach.
A: Dear Student, The features that define the Just in Time approach is given below -
Q: An explanation of how the DBMS could combine several heuristic rules and cost estimation tactics…
A: Introduction: A software program called a database management system (DBMS) is used to store and…
Q: Write a program (pseudo code to simulate an assembly line that has 4 stations.
A: The question is solved in step2
Q: agram network in whic through two switches S e to destination. Packe ofo oit ot + Qwit.
A:
From the given premise. Indicate the rules of inference used and the corresponding premises used
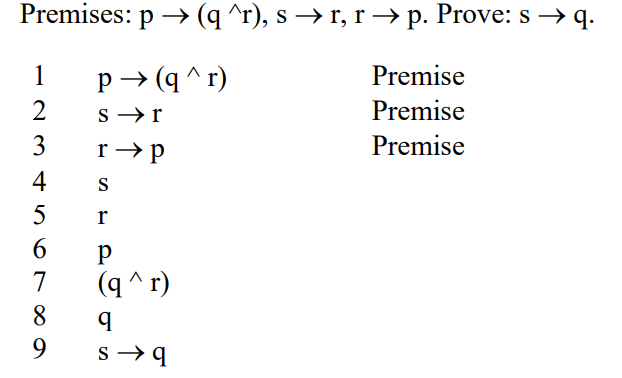
Step by step
Solved in 2 steps

- The set of letters S consists of 30 As, 6 Bs, 24 Cs, 15 Ds, and 15 Es. The set of letters T consists of 25 As, 20 Bs, 15 Cs, 5 Ds and 35 Es. What is the mutual index of coincidence between sets S and T? Leave your answer as a fraction in lowest termsprove the equivalence of the schemata:~(~(p • ~ q ) • ~ ( ~ p• q)) equal to ~(p • q) • ~(~p • ~q)Show that ((p→q) ∨ (¨(p ∧ ¨q) ∧ T)) ≡ ¨p ∨ q using the logical equivalences.
- Let R=ABCDEGHK and F= {ABK→C, A→DG, B→K, K→ADH, H→GE} . Is it in BCNF? Prove your answer.Suppose a Bayesian network has the from of a chain: a sequence of Boolean variables X1, . . . Xn where Parents(Xi) = {Xi−1} for i = 2, . . . , n. What is the complexity of computing P(X1|Xn = true) using enumeration? What is the complexity with variable elimination? Please explain.Consider a Diffie-Hellman scheme with a common prime q = 17 and a primitive root α = 3. a) If user A has a private key XA=4, what is A’s public key, YA? b) A sends YA to B. If B has a private key XB=6, what is the shared secret key, K that B can calculate and share with A? c) If B computes YB and sends it to A, what is the shared secret Key, K computed by A?
- Suppose the following PDA P = ({q, r}, {0,1}, {Z0, X}, δ, q, Z0, ∅) is given: 0, Z0/XZ0 1, Z0/ϵ 0, X /XX 1, X /XX 1, X /X ϵ, X/ϵ Convert P to a PDA P′ with L(P′) = N(P).Let L = { <M> | M is a TM that accepts sR whenever it accepts s } . Show that L is undecidable.Match the following sentence to the best suitable answer: - A. B. C. D. for the linear congruence ax=1(mod m), x is the inverse of a, if__________ - A. B. C. D. What is -4 mod 9 ? - A. B. C. D. The solution exists for a congruence ax=b(mod m) such that GCD(a,m)=1 and - A. B. C. D. (107+22)mod 10 is equivalent to :_________ A. 5 B. c divides b C. GCD(a,m)=1 D. 9 mod 10
- Compute the gradient with respect to all parameters of f(w0 + w1a1 + w2a2) when w0 = 3, w1 = −2, a1 = 2, w2 = −1, a2 = 4, and β = 0.25 using backpropagationFor straight-line distance heuristic, draw the search tree after expansion of each node until the termination of the algorithm for: a) Greedy best-first search (label all node with their h values). What is the solution (list of visited cities) found by the algorithm? b) A* search (label all nodes with their f values). What is the solution (list of visited cities) found by the algorithm?Consider the given graph below. The weights represent the time, in minutes of reaching one destination from another destination. Using the Brute Force Method in this complete weighted graph, determine all the Hamilton circuits starting at L and its optimal solution.

