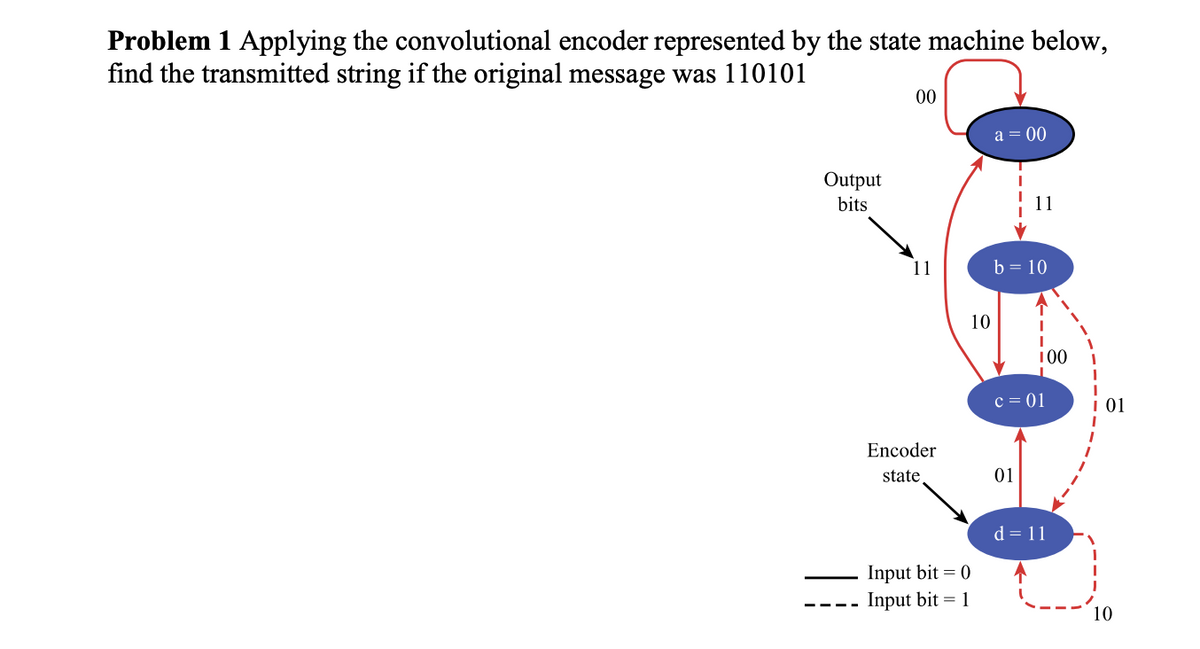
Problem 1 Applying the convolutional encoder represented by the state machine below, find the transmitted string if the original message was 110101 Output bits ———- 00 11 Encoder state Input bit = 0 Input bit = 1 10 a = 00 b = 10 100 c = 01 01 d = 11 10
Q: When it comes to computers, what are the key distinctions between memory (RAM) and read-only memory…
A: Here is your solution -
Q: Web application data flow must be explained in depth.
A: The following are the components of a data flow Web application that will be explained: The…
Q: If you are unclear of the location of the update.txt file on your computer, you are strongly…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: A compiler's correctness and efficiency depend on its consideration of the following. Explain.
A: Answer to the above question is given below
Q: Provide one example to illustrate the many kinds of interruptions and why they are so important to…
A: An interrupt is a signal from a device attached to a computer or from a program within the computer…
Q: Create a SinglyLinkedList class function named reverse that flips the order of the list's…
A: Singly linked list is a data structure in computer science that is used to represent a sequence of…
Q: s it vital to interrupt either the hardware or the software, and if it is, at what time should this…
A: Interrupts are a crucial mechanism in computing systems that allow hardware devices or software to…
Q: Write a method of SinglyLinkedList, called reverse, that reverses the order of the elements in the…
A: Step-1: StartStep-2: Create structure Node Step-2.1: Declare data Step-2.2: Declare Node pointer…
Q: Rewrite the client program to use the Baby class that you have done using ArrayList. You should also…
A: The question is asking you to rewrite a program that manages a list of babies using an ArrayList…
Q: Just how reliable are sentiment analysis results? I was wondering how you think this is typically…
A: Sentiment analysis, a prominent technique in natural language processing, has gained significant…
Q: When individuals speak about "scope," what precisely do they mean by those words?
A: When people refer to "scope," they are generally talking about the extent or boundaries of a…
Q: Using the appropriate ports, please describe how the following system components communicate with…
A: The Difference Between Random Access Memory (RAM) and Read Only Memory (ROM) (Read-Only Memory).…
Q: mpi4py to create the pi calculation technique similar to As previously, the worker process…
A: MPI (Message Passing Interface) is a standard interface for communication among parallel computing…
Q: The console is where human and machine interaction takes place. Explain
A: A console is a tool that enables people to interact with machines, and it can come in the form of a…
Q: What do we know better about website construction now?
A: Throughout the course of our history, we have amassed a wealth of experience in the design and…
Q: Not compiling
A: javac BSTMain.javaBSTMain.java:151: error: cannot find symbol BST bst = new BST(); ^…
Q: How are the ideas of cohesion and coupling related to one another when applied to the process of…
A: The answer to the above question is given below
Q: Thanks to recent advancements in technology, most modern household appliances may now be wirelessly…
A: The proliferation of wireless information appliances and services, including modern household…
Q: df. 636636.
A: The question asks to write a program in Java to reverse the bits of a given 32-bit unsigned integer.…
Q: Answer the given question with a proper explanation and step-by-step solution. Write an assembly…
A: The question asks for an assembly language program that multiplies two values, x and y, and stores…
Q: Because of this, you need to manufacture computers that are not only of great quality but also of a…
A: Rapid prototyping is the fast fabrication of a physical part, model or assembly using 3D Computer…
Q: In order for a web application to work successfully, it is necessary to have an understanding of the…
A: Web applications are complex systems that rely on multiple components working together to provide a…
Q: stage in creating a website, and how many are there
A: Is there more than one stage in creating a website, and how many are there? Justify the importance…
Q: The title of the show will appear as follows at the top of the screen:
A: The title bar in a graphical user interface is the horizontal bar at the very top of each window.…
Q: Errors produced when calling 3. Find the maximum element from the BST or 4. Find the minimum element…
A: In this question we have to write a Java code for the BST implementation as per the given…
Q: How can I back up my Windows 10 computer, and what are the primary advantages of doing so?
A: There are several ways to back up a Windows 10 computer, including: Using Windows File History:…
Q: Share your thoughts on how computers can be made faster by pipelining, how pipeline dangers can be…
A: The answer is given below step.
Q: The two types of automata machines, deterministic and non-deterministic, are distinct from one…
A: Automata theory, a subject of computer science, focuses on mathematical models of computers.…
Q: Explain why IBM is the best and biggest computer manufacturer in the world.
A: Using the soft-sectored floppy disc format was common with older systems. The disc was…
Q: Follow these steps to create your Warhol Grid: 1. Find or create an image (for this activity, a…
A: Install the Pillow library using pip or the Repl.it package manager. Load the image you want to…
Q: Choose how you like to define "computer environment," and then read up on the three subsets of this…
A: The computing environment consists of various computer hardware, data storage devices, workstations,…
Q: Is there still logic in the subsystems of massive computer processes and programmes when they are…
A: You should determine whether it makes sense for huge computer processes and programs to have…
Q: It is unclear how operating systems really execute processes.
A: In general, an operating system is responsible for managing the resources of a computer, including…
Q: In what respects may the discrete event simulation be considered relevant with regard to these four…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Provide an example of the wide variety of software assets that may be shared in a distributed…
A: Let's define a distributed system: The discipline of computer science known as "distributed…
Q: Explore two modes that allow the OS to defend itself and other system components.
A: Operating systems use many methods to protect themselves and their components. We'll compare User…
Q: What exactly does it imply when someone says "nondeterministic finite automata" (NFA)?
A: A non-deterministic finite automaton (NFA) is a theoretical model of a symbol-processing machine…
Q: When it comes to computers, what are the key distinctions between memory (RAM) and read-only memory…
A: This allegation lacks substantial credibility. ROM (Read-Only Memory) and RAM (Random Access Memory)…
Q: Explain why IBM is the best and biggest computer manufacturer in the world.
A: One of the most reputable and well-known producers of computers worldwide is IBM. It has a long…
Q: Are there genuinely only three tasks that an operating system is intended to fulfil, or is there…
A: The tasks of an operating system can vary depending on the type and purpose of the system. While…
Q: Find out which strategies and resources will be used most often during the process of developing the…
A: In this question we have to understand and find out which strategies and resources will be used most…
Q: How dissimilar are public and private cloud services? In your opinion, which of these approaches…
A: The answer is given below step.
Q: Find out which strategies and resources will be used most often during the process of developing the…
A: Find out which strategies and resources will be used most often during the process of developing the…
Q: Explain why IBM is the best and biggest computer manufacturer in the world.
A: IBM is played the most significant role in the development of modern computing, having created some…
Q: What does it take to implement multi-factor authentication, and how does it work? Why should you…
A: According to information given:- We have to define multi-factor authentication implement, and how…
Q: If you wish to design a programming language that is of a high quality, what do you believe to be…
A: Most crucial things to consider are given below
Q: How can you be sure that your information stored in the cloud is secure? Can we ensure their safety…
A: How can you determine if your data is secure while utilizing cloud services Can we ensure their…
Q: What kinds of industries may gain from web development? Is there anything specific about creating…
A: Web development has uses outside of computer science: E-commerce: E-commerce is a burgeoning topic…
Q: To connect the central processing unit and random access memory, do you choose a synchronous or an…
A: The answer to the above question is given below
Q: What would you say are the top four advantages of continuous event simulation?
A: 1) Continuous event simulation is a technique used in computer science and engineering to model the…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Consider a convolutional code with k = 1, n = 3 and L = 3. The encoder generators aregiven by 91 = [110], 92 = [001] and 93 = [011].Assume the Viterbi algorithm is used for decoding at the receiver and considerthe received bit sequence at the input of the channel decoder being [10 0100110011].Answer the following questions.(a) What is the decoded information bit sequence? (b) What is the value of the cumulative metric (i.e., Hamming distance) of thefinal survivor path of the decoding process?(c) Draw the final survivor path of the trellis for the decoding process.Instruction for Part (c): An example of drawing a path in the trellis is shown below.Assume an encoded 8-bit hamming code is stored in the memory for transmission from A to B. Using Even Parity Hamming code technique, determine the parity bits/position and the data to be stored in the memory. The 8-bit hamming code (10111011)2 is transmitted from sender A and the receiver B receives the code as (11111011)2. Draw the layout of data bits and check bits. How will the processor detect the error and correct it?2.Consider the bit stream 01101101. Draw the waveforms for following line codes.(i)(ii)Biphase Manchester codingBiphase Differential Manchester codingPolar PSEUDOTERNARY(iii)(iv)Multilevel -8B6T(v)Multilevel-2B1Q Assume that the signal level for the most recent preceding 0 bit (pseudoternary) has a negative voltage.
- A block of bits with n rows and k columns uses horizontal and vertical parity bits for error detection. Suppose that exactly 4 bits are inverted due to transmission errors. Drive a mathematical expression of n and k for the total number of different cases where these 4 error bits will be undetected. Show each important step of your derivation. (Hint: the error bits will be undetected if all the parity bits computed from the block remain unchanged.)Suppose that during transmission there is an error which results in bits being flipped. What correction measures can be implemented to correct the error messageA bit stream 10011101 is transmitted using CRC method. The generator polynomial is x^3 + 1. Show the actual bit string transmitted. Suppose the third bit from the left is inverted during transmission. Show that this error is detected at the receivers end.
- Suppose the binary data stream 000011110011 is differentially encoded and then transmitted sketch each of the following codes Unipolar NRZ Polar RZ AMI (Alternate Mark Inversion) ManchesterComputer Network : Suppose 3 blocks of 16 bits need to be sent, using Checksum method proves the following cases: When there is no error When there is a burst error and detected. When there is a burst error and remains undetected Block 1: 1011101110101011 Block 2: 0101000011111010 Block 3: 0111010110101010A)Convert the data word OxAF96 into Hamming Code using even parity B)Transmitter sent OxAF96. Assume that the data word received at the receiver was OxBF96. How does the receiver detect an error bit and correct the bit? Show the working steps.
- a) Compute the CRC for the following message M = 1110 1010 1110 0100 0101 using the generator x4+x2+x+1. Show your detailed work. Let us call M’ the message M after appending the CRC to it. b) Suppose the following error message E = 1111 0000 1110 0000 1010 0000 is XORed to M’ obtained in part a. Is the error detected at the receiver? Show your detailed work.In ___________ there is always a transition at the middle of the bit, but the bit values are determined at the beginning of the bit. If the next bit is 0, there is a transition; if the next bit is 1, there is none. a. Manchester b. differential Manchester c. both (a) and (b) d. neither (a) nor (b)a. Compute for the data efficiency of transmitting if the data format is a General Synchronous Data Frame. b. For an asynchronous data transmission (wherein 1 byte of data is accompanied by a specific number of auxiliary bits), how many start and stop bits are there if the data efficiency in transmitting is ? The number of start bits is equal to the number of stop bits.

