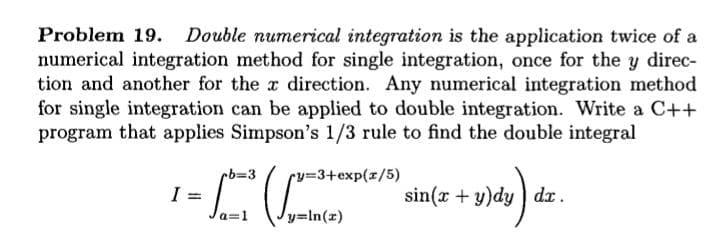
Problem 19. Double numerical integration is the application twice of a numerical integration method for single integration, once for the y direc- tion and another for the r direction. Any numerical integration method for single integration can be applied to double integration. Write a C++ program that applies Simpson's 1/3 rule to find the double integral rb%3D3 rv3+exp(z/5) I = a=1 sin(x + y)dy ) dr. y=In(z)
Problem 19. Double numerical integration is the application twice of a numerical integration method for single integration, once for the y direc- tion and another for the r direction. Any numerical integration method for single integration can be applied to double integration. Write a C++ program that applies Simpson's 1/3 rule to find the double integral rb%3D3 rv3+exp(z/5) I = a=1 sin(x + y)dy ) dr. y=In(z)
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter14: Numerical Methods
Section: Chapter Questions
Problem 1PP
Related questions
Question
Transcribed Image Text:Problem 19.
Double numerical integration is the application twice of a
numerical integration method for single integration, once for the y direc-
tion and another for the x direction. Any numerical integration method
for single integration can be applied to double integration. Write a C++
program that applies Simpson's 1/3 rule to find the double integral
1-CC
%3D3
ry%3+exp(x/5)
I
sin(x +y)dy) dr.
%3D
Jy=In(x)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr