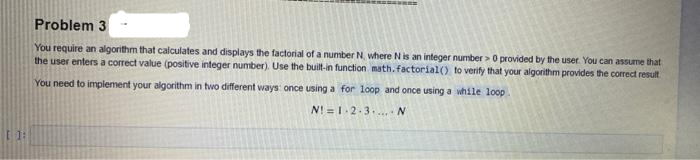
Problem 3 You require an algorithm that calculates and displays the factorial of a number N. where Nis an integer number > 0 provided by the user. You can assume that the user enters a correct value (positive integer number). Use the buit-in function math. factorial() to verity that your algorithm provides the correct result You need to implement your algorithm in two different ways once using a for loop and once using a while loop N!=1-2-3.. N
Q: Given a number N, and we have to generate a dictionary that contains numbers and their squares (i,…
A: Given a number N, and we have to generate a dictionary that contains numbers and their squares (i,…
Q: Why is it critical for a programme to terminate an open file once it has finished utilising it? Give…
A: Introduction: To close an open file, follow these steps:
Q: is given by the a Boolean following ath table: (127 - no), (abclefg. %3D a) Draw the corresponding…
A:
Q: When does a function template's code get generated by the compiler?
A: Introduction: The compiler generates code for the function Template:
Q: How would you define and list four distinct techniques to safeguard a campus or organization…
A: The answer is given below.
Q: Explain how the idea of Mutual Exclusion (ME) is regarded a vital mechanism for the smooth running…
A: Mutual exclusion (mutex) A mutual exclusion (mutex) is a program object that forestalls synchronous…
Q: 1. Which strings of the following are accepted by the pda below? acb, acab, acb, bacab, abcba, λ,…
A: PDA stack push elements: State q0 push all the strings into the stack. The push scharacters must a…
Q: which operators would make the following statement FALSE? 11_ 2
A: The three operators would make the 11_2 statement false. These are <, ==, <=
Q: Create a table which should contain at least the following fields: name, password, email-id, number…
A: Register_1.jsp <%@ page language="java" contentType="text/html; charset=ISO-8859-1"…
Q: Computer science how an organizations uses database in their information systems,
A: Introduction: Databases are used by businesses to increase data access inside the firm, strengthen…
Q: Discuss the role of multimedia and virtual reality in teaching computer science
A: Introduction: Multimedia includes everything we see and hear in the form of text, photographs,…
Q: Why is it important to limit the size of the broadcast domains in a network?
A: Answer is given below-
Q: Describe dynamic testing.
A: Explanation Mostly the dynamic testing is accomplished by those who know the codes and development…
Q: Instructions This assignment will show that you understand how columns should be separated between…
A: Here I am providing a relational database image of the given question.
Q: For each of the algorithms below, draw the spanning tree and find the sequence of visited nodes…
A: The solution of the given question is:
Q: Discuss how important it is to be able to import data from external sources such as online tables or…
A: Answer: Being able to import data from external sources into the workbook provides flexibility in…
Q: What exactly is STP? How does it work?
A: Introduction: STP (Spanning Tree Protocol) and how it works must be defined. The Spanning Tree…
Q: A length of at least 8 characters • At least 1 uppercase letter At least 2 numbers • At least 1…
A: Step-1: StartStep-2: Declare variable upper, num, ch, containSpecial and passwordStep-3: Start a…
Q: If the size of each 4-bit memory component is 4 x n cells where n = 1G (i.e., 4 xn uniquely…
A: The answer is
Q: To manage user security credentials, network administrators construct domain groups. Why?
A: Network administrators creating domain groups Network administrator is responsible for managing the…
Q: Create a two-dimensional array "arr" of size (4X3) that will be used in the following functions: A.…
A: Start main function call 3 functions fillArray function read text document elements print function…
Q: What are the different types of ROM memory?
A: ROM: ROM stands for Read-Only Memory. It is a memory that is non-volatile. When it is made, it is an…
Q: Present an example of walking through the merge sort or the quick sort algorithm (your choice) This…
A: Merge Sort is a an example of Divide and Conquer algorithm. It divides the input array and then…
Q: 1. Which node(s) in the following tree violate(s) the ordering imposed on an AVL tree?
A: The Answer is in Below Steps
Q: Learn how to register a fully qualified domain name (FQDN) on a DNS server for usage on the Internet…
A: Start: A DNS Server is any system that has been configured to connect to the Domain Name System. A…
Q: algorithms have the following time complexities: A~0(n), B~0(n²), C~ 0(log2(n
A: The answer is
Q: LAB7/addstudent.html - windows Intermet Explorer e http://localhost/LAB7/addstudent.html BigSeekPro…
A: Please refer below code and output: <!DOCTYPE html><html><body> <h2>Add a…
Q: Q4.Draw the dependency diagram for the DESPATCH_LIST table above. Identify all dependencies…
A: I have provided the dependency diagram for the DESTPATCH_LIST of the given table.
Q: transmission time? b) Suppose the server begins to transmit the packet at time t-0. when t=…
A: The answer is
Q: In software engineering, discuss the purpose and goals of prototyping.
A: Introduction: In Software Engineering, prototype technique is a software development process in…
Q: Why do we require so many addressing modes?
A: Address mode: An addressing mode is an operand that refers to the specification of instruction and…
Q: Method main: Print the message "Math Quiz". Call method display_menu and assign the return value…
A:
Q: Which one statement out of following four statements about Merge sort and Quick sort is tr Both…
A: Sorry for that as the bartleby guidelines we can solve only one question for you if you want to…
Q: What are the core concepts of software engineering that are missing? explain?
A: Introduction: While the phrase "making computers do things" is true, it falls far short of…
Q: For the following sequence in the order shown, build an AVL tree: 1, 9, 2, 8, 3, 7, 4, 5, 6. Show…
A: Introduction: Here we are required to build an AVL tree for values 1,9,2,8,3,7,4,5,6, also we are…
Q: Write a program in JSP to design a Login Page with student Reg_No and Password. Reg_No & Password…
A: JSP to design a Login Page with student Reg_No and Password. If Reg_No & Password Field are both…
Q: A multilayer neural network uses gradient descent to search for a global minimum in the loss space.…
A: Answer - A multilayer neural network uses gradient descent to search for a global minimum in the…
Q: What is the physical address of this instruction Source operand of MOV BL, [SI +
A: The answer is
Q: Using C Language, use the multidimensional array to produce the following output: P.S. Do number 4
A: Start Take the number of rows Read the number of rows Compute the required pattern. Print required…
Q: Give your own insights to this question " Why computer literacy be mastered by all college students…
A: Introduction Give your own insights to this question " Why computer literacy be mastered by all…
Q: A ____________ is a grouping of two or more computers linked together for the purpose of exchanging…
A: The communication process among systems or exchanging the data plays very important role in almost…
Q: With examples, describe the four types of activity relationships.
A: Introduction: Note:- I'm explaining 1 question here, for other parts kindly resubmit the question.…
Q: What is it that the core notions of software engineering do not take into account. explain?
A: Introduction: Software development: Software engineering is characterised as a systematic,…
Q: You've begun photographing a computer drive at a crime scene. A little fire has started in the…
A: Start: A man is murdered in his home's backroom. When the investigating agency arrives at the crime…
Q: Computer science Why is automation necessary for contemporary societies
A: Introduction: Increased automation can assist handle issues including wage growth, ageing…
Q: RPC (Remote Procedure Call) has some flaws despite its conceptual elegance. Describe three of them…
A: The Answer is in step-2.
Q: b:D,R a:0,R 0;0,L. q2 90 q1 a;0,R b;0,R
A: Answer: In this given diagram only two variables are used. One is a and other is b. Ans c is not…
Q: Describe how computer programs can analyze sequence files.
A: Explanation: Sequence files contain the information in a binary format that is the data are stored…
Q: hat happens if you use ios::out to open a file that doesn't exist?
A: Introduction: A file is defined as a collection of data kept in a single unit and identified by a…
Q: Fill out the table for executing the polynomial-time dynamic programming algo- rithm for deciding…
A: Solution ::
Computer Science
Step by step
Solved in 4 steps with 2 images

- please code in python Find the Error The following function takes in a positive integer and returns True if the integer is divisible by at least one integer between 2 and 7, inclusive, or False otherwise. Or at least, that’s what it’s supposed to do; there is a logic error that causes it to fail (for example, it should return True when passed in 15, but it returns False instead). Find the error and fix it. If you’re working in a pair, make sure that both of you are able to explain the error to your TA. Hints: As with most logic errors, the first thing you should do is put in print statements. Print out what i is at each step of the loop. At what point can you safely return False (that is, how many values of i do you have to check before you can be sure num isn't divisible by any of them)? def div27(num): for i in range(2,8): if num % i == 0: return True else: return Falsecoral programming Write a program that takes in a positive integer as input, and outputs a string of 1's and 0's representing the integer in binary. For an integer x, the algorithm is: As long as x is greater than 0 Output x % 2 (remainder is either 0 or 1) x = x / 2 Note: The above algorithm outputs the 0's and 1's in reverse order. Ex: If the input is 6, the output is 011. Your program should define and call a function: Function IntegerToBinary(integer num) returns nothing The function should output 1's and 0's representing the integer in binary (in reverse).1. Write a program uses a Boolean-valued function to determine whether a set of numbers is in a given range. a) Define a function, isInRange(x) with an integer parameter. b) isInRange(x) returns true if the integer number x is in the range (-100, 100). Otherwise, return false.c) Define a main() function, in which a loop will be created to do the following ten times: 1) get a random integer, n, in the range (-500, 500). 2) call isInRange(x) function to determine and print out if the number n is in the range. d) Call main() function to initiate the tasks to be performed. Output Example: 2 is in the range.66 is in the range.171 is not in the range. 67 is in the range.-28 is in the range.355 is not in the range. 343 is not in the range. 233 is not in the range. -263 is not in the range. 11 is in the range. 2. Write a program that sums up all positive user input numbers. a) For every iteration output the sum of all positive input values.b) Implement the loop to stop if a negative…
- Code should be in Python, please Write a program that takes in a positive integer as input, and outputs a string of 1's and 0's representing the integer in binary. For an integer x, the algorithm is: As long as x is greater than 0 Output x % 2 (remainder is either 0 or 1) x = x // 2 Note: The above algorithm outputs the 0's and 1's in reverse order. You will need to write a second function to reverse the string. Ex: If the input is: 6 the output is: 110 Your program must define and call the following two functions. The function integer_to_reverse_binary() should return a string of 1's and 0's representing the integer in binary (in reverse). The function reverse_string() should return a string representing the input string in reverse.def integer_to_reverse_binary(integer_value)def reverse_string(input_string)MAKE A FLOWCHART PLEASE clc;clear; function [] = Bisection(xl,xu,es,imax)ea = 100xr = (xu+xl)/2;x=xrfr=evstr(f)while (ea>es)a=fl-fu;if (a==0) thenmprintf("Error: Division by Zero")abortendtest = fl * fr;mprintf(" %d %10f %10f %10f %12.7f %12f %12.f %10.7f\n",iter,xl,xu,xr,fl,fu,fr,ea);if (test<0) thenxu=xr;elseif (test>0) thenxl=xr;elseif (test==0) thenmprintf("\n\nThe root of the equation is %f",xr)abortendx=xlfl=evstr(f)x=xufu=evstr(f)xrold=xrxr=(xu+xl)/2;x=xrfr=evstr(f)ea=abs((xr-xrold)/xr)*100;iter=iter+1;test=fl*frif ea < es thenmprintf(" %d %10f %10f %10f %12.7f %12.f %12.f %10.7f\n",iter,xl,xu,xr,fl,fu,fr,ea);mprintf("\n\nThe approximate root for the given function is %f",xr)abortendif iter > imaxmprintf("The approximate root for the given function is %f",xrold)mprintf("\nSlowly converges. It is suggested that the initial values should be change");abortendendendfunction //main disp("This program will solve/give the approximate root of any given nonlinear…A natural number is prime if it is greater than 1 and has no divisors other than 1 and itself. Example: 8 isn't a prime number, as you can divide it by 2 and 4 (we can't use divisors equal to 1 and 8 as the definition prohibits this). On the other hand, 7 is a prime number as we can't find any legal divisors for it. Your task is to write a function checking whether a number is prime or not. Please us phython language The function: is called IsPrime() takes one argument (the value to check) returns True if the argument is a prime number, and False otherwise. Hint: try to divide the argument by all subsequent values (starting from 2) and check the remainder - if it's zero, your number cannot be a prime; think carefully about when you should stop the process. If you need to know the square root of any value you can utilize the ** operator. Remember: the square root of x is the same as x**0.5 Write a code that calculates all the prime numbers between 1 and 20. (Hint: Use a loop and…
- solve in assembley language, MIPS Square Root Calculation: Newton’s iterative method can be used to approximate the square rootof a number x. Let the initial guess be 1. Then each new guess can be computed as follows:guess = ((x/guess) + guess) / 2; Write a function called square_root that receives a double-precision parameter x, computes,and returns the approximated value of the square root of x. Write a loop that repeats 20 timesand computes 20 guess values, then returns the final guess after 20 iterations. Use the MIPSfloating-point register convention (Section 9.6) to pass the parameter x and to return thefunction result. All computation should be done using double-precision floating-pointinstructions and registers. Compare the result of the sqrt.d instruction against the result ofyour square_root function. What is the error in absolute value?only pythonYour program should ask the user to input a number of family members. The program should then repeatedly ask the user to input the age of a family member until the specified number of family members is reached. Finally, the program should output the average age of the family members based on the input values. If the user inputs zero for the number of family members, the program should output a friendly message informing the user that at least 1 family member is required. A function has already been defined for you which asks the user for the age of a family member. You must use this function as part of your solution. Your solution must be implemented using a for loop on a range.add on to this: def ask_for_age(): age = int(input('Enter the age of a family member: ')) return ageNEED HELP WITH PYHTON..PASTE INDENTED CODE PLZZ 4. Boolean Functiona) Define a function, isInRange() with an integer parameter, x. This function returns true if the integer number x is in the range (-100, 100). Otherwise, return false. b) Define a main() function, in which a loop will be created to do the following ten times: 1) Get a random integer, n, in the range (-500, 500). 2) Call isInRange(x) function to determine and print out if the number n is in the range. c) Call main() function to initiate the tasks to be performed. Example Output 2 is in the range. -358 is not in the range. -44 is in the range. 297 is not in the range. -295 is not in the range. 205 is not in the range. 467 is not in the range. -116 is not in the range. 388 is not in the range. 53 is in the range.
- Use the Fibonacci search method for optimization and code a program in C to determine the maximum or minimum of a given function. The user must specify the function, the intervals, if the search is for a maximum or minimum and the number of iterations. The Fibonacci number and the new interval of each iteration needs to be displayedpython only** define the following function: This function accepts a string as its only parameter, and it must return a tuple containing first the length of the string, and then the string itself. Define lengthAndValue with 1 parameter Use def to define lengthAndValue with 1 parameter Use a return statement Within the definition of lengthAndValue with 1 parameter, use return _in at least one place. Do not use any kind of loop Within the definition of lengthAndValue with 1 parameter, do not use any kind of loop.(Numerical) Write a program that tests the effectiveness of the rand() library function. Start by initializing 10 counters to 0, and then generate a large number of pseudorandom integers between 0 and 9. Each time a 0 occurs, increment the variable you have designated as the zero counter; when a 1 occurs, increment the counter variable that’s keeping count of the 1s that occur; and so on. Finally, display the number of 0s, 1s, 2s, and so on that occurred and the percentage of the time they occurred.



