Problem Description Design a flowchart using Flogorithm, to solve the following problem, then open Code Block IDE, create a new project. Use this project to create a program that Reads in an integer number that represents the number of rows of a checkerboard pattern Based on the user's choice, the pattern is printed as shown in the sample output below: O Organize the output to appear as shown in the sample output below Sample Output |\Printing Pattern\\ Input number of rows: 6 ######################## The checkerboard pattern is: 6 12 18 24 30 36 5 10 15 20 25 4 8 12 16 3 6 9 2 4 1
Problem Description Design a flowchart using Flogorithm, to solve the following problem, then open Code Block IDE, create a new project. Use this project to create a program that Reads in an integer number that represents the number of rows of a checkerboard pattern Based on the user's choice, the pattern is printed as shown in the sample output below: O Organize the output to appear as shown in the sample output below Sample Output |\Printing Pattern\\ Input number of rows: 6 ######################## The checkerboard pattern is: 6 12 18 24 30 36 5 10 15 20 25 4 8 12 16 3 6 9 2 4 1
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter6: Modularity Using Functions
Section: Chapter Questions
Problem 4PP
Related questions
Question
c language
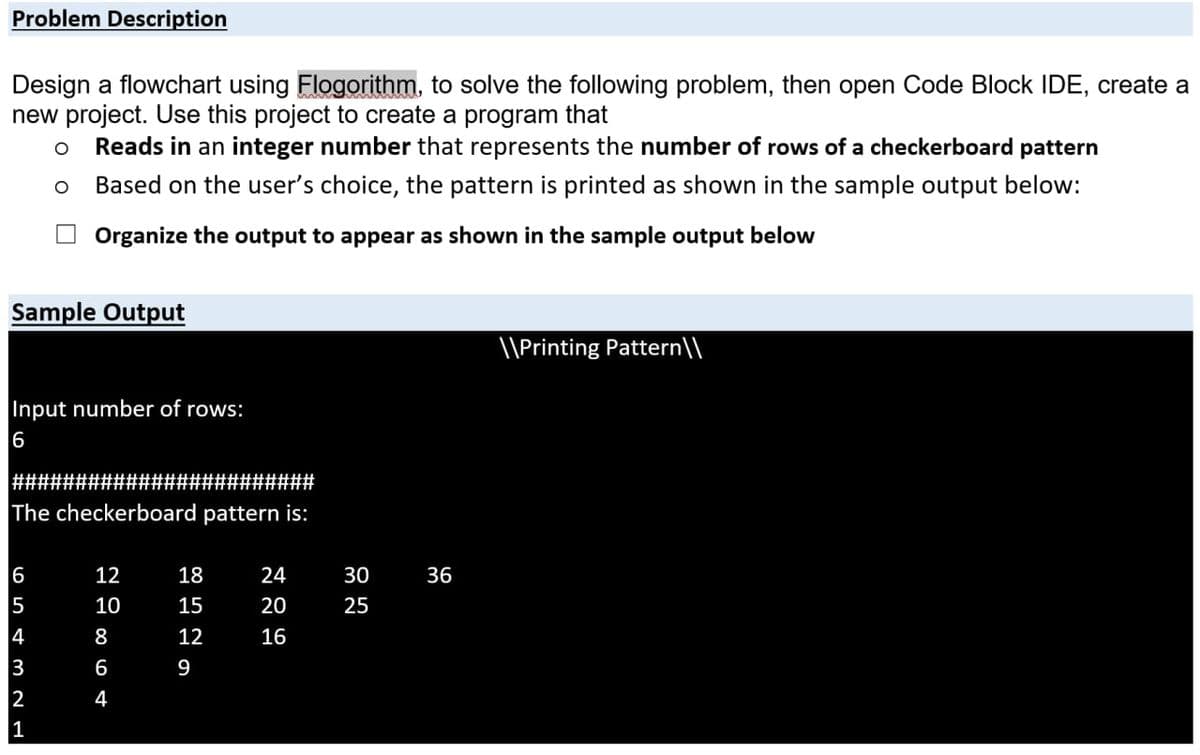
Transcribed Image Text:Problem Description
Design a flowchart using Flogorithm, to solve the following problem, then open Code Block IDE, create a
new project. Use this project to create a program that
Reads in an integer number that represents the number of rows of a checkerboard pattern
Based on the user's choice, the pattern is printed as shown in the sample output below:
Organize the output to appear as shown in the sample output below
Sample Output
\\Printing Pattern\\
Input number of rows:
########################
The checkerboard pattern is:
6
12
18
24
30
36
5
10
15
20
25
4
8
12
16
3
6
9
2
1
4
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT