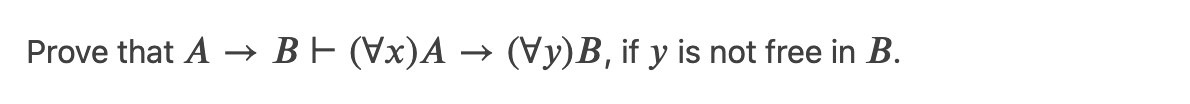
Prove that A → B E (Vx)A → (Vy)B, if y is not free in B.
Q: Compare the picture formats GIF, JPEG, BMP, and PNG based on your knowledge of digital images.
A: A digital picture is a numerical representation of a real image that can be stored and processed by…
Q: What is multifactor authentication, and how does it work? What role does it play in the fight…
A: Answer the above questions are as follows
Q: What does the kernel technique do in the instance of an SVM classifier? Is it possible to use this…
A: Problem Analysis : Kernal Trick : This is a concept that is used in the SVM classifier that enables…
Q: How does an application programmer create the forms that will appear on the screen?
A: Introduction: Forms Development: Essentially, forms are containers for storing data and user…
Q: What exactly are phases in multimedia? Explain each one.
A: Introduction: The following are the fundamental steps of multimedia production:
Q: The Cloud Computing Movement has had an influence on cooperation, although the extent of that impact…
A: Introduction: The process of transferring digital company processes to the cloud is known as cloud…
Q: A PC is a single-user microcomputer that can only be used by one person at a time for general…
A: INTRODUCTION: This type of computer is called a PC. It is a general-purpose computer that only one…
Q: Certain features of a database relation may be encrypted for security reasons. Why are encrypted…
A: Introduction: A value that has been encrypted cannot be indexed unless the value is encrypted to the…
Q: How long is the data retained by Spansion on a memory device before it is overwritten?
A: Introduction: Data retention refers to the duration of time during which data is stored and…
Q: What media characteristics distinguish an infrared network?
A: Introduction: Infrared networks are a kind of wireless technology that allows devices or systems to…
Q: What is the fundamental reason why servlets outperform programmes written in C or C++, despite the…
A: Servlets: It is a server-side component that provides web-based applications for the server.…
Q: What are some of the network-layer services that a link-layer protocol can provide? What IP services…
A: Some of the services that a link-layer protocol can provide to the network layer are as follows.…
Q: ternal storage than computers running other desktop operating systems?
A: Introduction An operating system is a software program that manages and operates computing devices…
Q: What is the best technique for minimising the majority of failures in distributed systems, and why?
A: Introduction Distributed computing systems have their own infrastructure and no shared memory. «…
Q: When using classes in programming the concept of public and private members of a class (the data and…
A: Public and private member of the class
Q: Can somebody tell me which development model agile software development is based on?
A: Our task: We must ascertain the approach used within the agile software development life cycle.
Q: List the components of a typical operating system's kernel and briefly describe their functions?
A: Operating system: An operating system can be defined as a system like a large & complex is…
Q: Design a flowchart or pseudocode for a billing program at a day care center. The program accepts…
A: - We are creating a pseudocode for the fee care program.
Q: Python How do you choose between for and while loop?
A: INTRODUCTION: Iterating through a sequence is done with a for loop (that is either a list, a tuple,…
Q: 3. Please provide professionally crafted solutions to the following: 1. For the following tree A B D…
A: What Is a TREE? A tree is an abstract data type in computer science that depicts a hierarchical tree…
Q: write a method that returns the maximum of two given integers(in java)
A: The java code for the above given question is given below:
Q: Identification and short description of numerous tools and methods that will be used throughout the…
A: Systems development is the process of conceptualizing, designing, developing, testing, and…
Q: Can this java code be cracked? If so how can I make so that it cannot be cracked? import java.io.*;…
A: Solution: Java Code: import java.io.*; public class Main { static int plnTxt[] = new…
Q: locks, deletions, or authorizations are applied to the content in order to achieve the desired…
A: Introduction By converting their content into a compact digital asset or impression using a known…
Q: What advantages does Connectivity Software provide?
A: Introduction: The Connectivity Software refers to the data sharing feature of the software with the…
Q: Why is knowledge information technology required for automation?
A: Introduction Information technology and Automation: Information technology is storing and sharing…
Q: If you're a software tester, you've come to the right place. You use a calculator for testing. Which…
A: Introduction: We need to know what sort of testing you like and what five scenarios you'd want to…
Q: What are the most important elements of a data warehouse architecture?
A: Your answer is given below. Introduction :- The data warehouse works as a central repository for…
Q: Can somebody tell me which development model agile software development is based on?
A: Justification: Agile project management and software development is an iterative method that helps…
Q: Who is in charge of creating device drivers for a certain operating system?
A: Introduction: System software or huge, sophisticated programs that regulate and manage a computer's…
Q: What is the time complexity of pushing and popping items to/from a stack containing n items,…
A: Note:-As per policy, we are entitled to answer the first three questions. Stack using linked list:-…
Q: Give a definition of the phrase tactile.
A: Intro Tactile is defined as anything that can be touched or perceived by the touch, A book written…
Q: Do you prefer the usage of a synchronous bus's CPU and memory or an asynchronous bus's CPU and…
A: Intro synchronous bus If the timing of transactions between devices in a computer system is…
Q: Which technical advancements have been the most important in computing? Discuss each participant's…
A: Given: In the field of computers, there have been a number of notable breakthroughs.In the field of…
Q: In GSM, a "TDMA frame" is composed of eight distinct time slots. Each GSM time slot is 577 s…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: What are the benefits of knowing how to use a computer? What are the advantages of technology in…
A: INTRODUCTION: Computer literate individuals can enhance their job performance, incorporate…
Q: As an example, suppose a user creates a new relation r1 with a foreign key pointing to another…
A: Introduction: A foreign key is like a column or set of columns in one table whose values match the…
Q: What are the approaches to MDM in database ?
A: Introduction To be determined - what are the approaches to MDM in database
Q: Describe what vulnerabilities 'WannaCry' exploited to infect its targeted
A: INTRODUCTION: Crypto ransomware, such as WannaCry, is a form of harmful software (malware) used by…
Q: What negative impact did 'WannaCry' malware have on its victims and their systems?
A: Introduction: When it comes to malware, WannaCry is a game changer.
Q: Describe what vulnerabilities 'WannaCry' exploited to infect its targeted systems
A: In this question we will understand the 'WannaCry' How it will infect the targeted system and what…
Q: b) Consider the following linear programming problem: Min z = x1 + x2 s.t. 3x1 – 2x2 <5 X1 + x2 < 3…
A: Solve linear programming question Find out optimal solutions
Q: Justify the use of inferential statistics
A: Inferential statistics: Inferential statistics is When comparing the differences between treatment…
Q: Define the shift from first to fifth generation computer technology in a few simple sentences.
A: Introduction: In computer jargon, generation refers to a change in the technology on which a…
Q: What are the advantages and disadvantages of using internal static analysis? Computer science
A: Introduction We need to talk about the benefits and drawbacks of employing internal static analysis.
Q: When running several instructions via a computer processor, what sort of processing and what…
A: The term "fetch-execute cycle" refers to the fundamental processes that a CPU takes to complete a…
Q: What are the two drawbacks of having software installed? Give an example of a Web application. What…
A: Introduction: Installed software need a computer to operate. Desktop software is either bought on a…
Q: Should a control structure have multiple entries?? why?
A: We need to find if a control structure can have multiple entries.
Q: The system enables the specialist and guardian to treat and follow up on autism disorder cases. The…
A: Here the state diagram is given below:
Q: What exactly is the difference between a webpage and a website.
A: Website: A website is a central place where many web pages are kept by a person or organization and…
2.
Step by step
Solved in 2 steps with 2 images

- Prove that the following instance of PCP does not have a match [aba, bb], [ab, a], [bab, aa], [ab, ba]Let R=ABCDEGHK and F= {ABK→C, A→DG, B→K, K→ADH, H→GE} . Is it in BCNF? Prove your answer.Show that property (3) of a matroid implies: For any S ∈ I, {x} ∈ I, there exists y ∈ S, such that S \ {y} ∪ {x} ∈ I.
- Prove that ((P Ꚛ Q) →¬R) ↔¬P is a tautology, a contradiction or contingency.(a) Give the definition of an isomorphism from a graph G to a graph H. (b) Consider the graphs G and H below. Are G and H isomorphic?• If yes, give an isomorphism from G to H. You don’t need to prove that it isan isomorphism.• If no, explain why. If you claim that a graph does not have a certain feature,you must demonstrate that concretely. (c) Consider the degree sequence (1, 2, 4, 4, 5). For each of the following, ifthe answer is yes, draw an example. If the answer is no, explain why. (i) Does there exist a graph with this degree sequence?(ii) Does there exist a simple graph with this degree sequence?Simplify the following k-map and compare it to boolean simplification. Answer both item.
- Prove that for any m ∈ N, there exist an NFA with m states such that the equivalentDFA has at least 2^m−1 statesUsing Logically Equivalent Law's, Show that (p -> q) > (r -> s) and (p -> r) -> (q -> s) are logically NOT equivalent?Prove that the following wff is a tautology, a contradiction or neither. Be sure to say which one. (A → B) ∨ (A′→ B)

