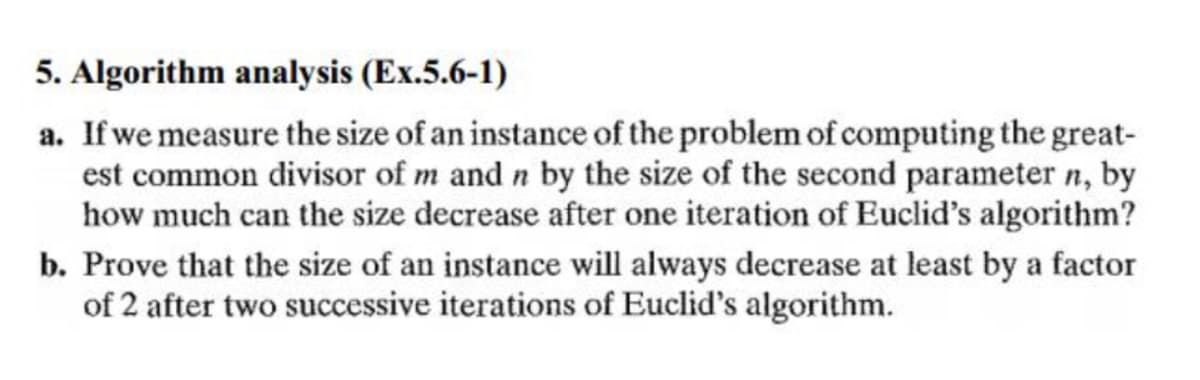
Prove that the size of an instance will always decrease at least by a factor of 2 after two successive iterations of Euclid's algorithm.
Q: Compiled languages have an advantage over translated ones due to the fact that they are simpler to…
A: Introduction: The term "interpreted language" refers to a programming language that does not need a…
Q: Why does Microsoft believe that Linux presents a threat to its economic interests in China and the…
A: Why does Microsoft fear that Linux is a danger to the industry, not just in China but worldwide?…
Q: Q\ Create a Visual Basic project to find the value of function f(Z) from the equations are below, by…
A: PROGRAM: Public Class Form1' to draw line take object lPrivate l As New List(Of String)Dim y, z, x,…
Q: Consider the following representation of a queue ADT that is implemented using an array data…
A: #include <iostream>using namespace std;//implementing queue class using arraytemplate…
Q: Write at least one difference between items below (1)i++ versus ++i Answer: (2)int versus…
A: Here in this question we have asked to give at least one difference between these i++ versus ++i…
Q: What is the objective of system modeling in the context of software engineering?
A: The question is to write the objective of system modeling in the context of software engineering.
Q: In the context of the creation of software, what does it imply when we talk about the "lifecycle"?
A: Given: To discuss SDLC (SDLC). Of the SDLC SDLC is a software project procedure in software…
Q: What does this query produce. SELECT CODE FROM TAUGHT WHERE SEMESTER-fall2018 and semester fall2019…
A: The above question is solved in step 2 :-
Q: Each model of a computer has a unique …. A. Assembley language B. Machine language C. High level…
A: Answer in step 2
Q: Problem Solving, Design, Implementation and Testing in MATLAB (a) Write a function isPrime (n) that…
A: A number is said to be prime number if it has only two divisors or factors 1 and itself .Then only…
Q: When we talk about 4G or 5G networks in the context of telecommunications, we don't necessarily know…
A: Introduction: The Internet is a vast network that connects billions of computers and other…
Q: When it comes to the general design, why would it be a waste of time to delve into the particular…
A: Answer: Our functioning memory is where the magic happens with regards to undeniable level mental…
Q: Understanding the role of firewalls in network security and protection is crucial. Remember to…
A: Introduction: It is critical to comprehend the role of firewalls in network security and…
Q: A co-processor A. is relatively easy to support in software B. causes all processes to function…
A: Answer: A coprocessor is a computer processor used to enhance the elements of the primary processor…
Q: Find out which level is responsible for the bulk of the work that has been completed both…
A: Given: The "project management lifecycle" is a model of a project's progression from start to…
Q: 5. Consider the following program written in C syntax: void swap (int a, int b) { int temp; temp =…
A: Here we have given the explanation of the given task. You can find the solution in step 2.
Q: This course will help you get a deeper understanding of social networking blogs, cloud computing,…
A: Given: Learn about social media blogging, cloud computing, and other subjects. Answer Instagram,…
Q: What are the FOUR (4) advantages of the Waterfall Model vs the Incremental Model?
A: The question has been answered in step2
Q: Why is it termed "Auto index" when it refers to an index register that is incremented or decremented…
A: As a result: Why is Auto index an index register that is automatically increased or decremented with…
Q: What is the difference between the functions urlopen and urlretrieve?
A: Given: urlopen vs urlretrieve
Q: What is the value of scores[2][3] in the following array? int [] [] scores = { {88, 80, 79, 92},…
A: Please find the answer below :
Q: Comparing Ubuntu to other well-known Linux distributions, just as you would with any other Linux…
A: Answer: The process of breaking down a huge database into smaller components is known as data…
Q: The two different forms of primary memory are
A: Primary memory is a segment of computer memory that can be accessed directly by the processor…
Q: The Internet Protocol (IP) address of a computer is its unique identity on the Internet. How do…
A: Solution: To talk about IP addresses and mnemonic addresses, go to: Determine the greatest number of…
Q: The property of a control, like the characteristics of other controls, determines whether or not the…
A: Given: The Control class is responsible for implementing the essential components needed to display…
Q: One method of network intrusion might be the rerouting of malicious traffic from one VLAN to…
A: Given: Since the desktop is unable to access the server's hardware address, there is no possibility…
Q: How does the computer programming process work? What factors should be considered before settling on…
A: The question is to define how does the computer programming process works and What factors should be…
Q: Consider the following recursive algorithm. ALGORITHM Q(n) //Input: A positive integer n if n = 1…
A:
Q: What exactly is meant by the phrase "custom software," and what are three examples of this kind of…
A: Please refer below for your reference: Custom application software is a type of application software…
Q: Which word defines a piece of software that performs certain activities, such as virus detection,…
A: Introduction: The term "computer software," which is sometimes referred to simply as "software,"…
Q: Determine and evaluate three particular dangers or attacks that might be launched against the…
A: Introduction: Malware assaults are common cyberattacks in which malware (typically malicious…
Q: When individuals talk about an operating system, what precisely do they mean
A: This question comes from Operating System which is a paper of Computer Science. Let's discuss it in…
Q: When a command cannot be chosen until another condition is met, it is referred to as a hold command.
A: Here is the answer :
Q: A discussion is offered on how formative assessment may be utilised to answer user issues and…
A: It refers to the quality of a user's interaction with objects or systems such as websites, software,…
Q: What storage structure does the Android operating system employ?
A: SOLUTION: In Android, we utilize a certain type of storage to save the data permanently (not erased)…
Q: ose and importance
A: Solution - In the given question, we have to describe the purpose and importance of software…
Q: Investigate and evaluate the server capabilities of Linux, then compare and contrast them with those…
A: Microsoft Windows: Portrayal: Microsoft Windows is a gathering of OSs made by Microsoft. Windows is…
Q: Wireless networks have a number of difficulties. Describe the impact of three of these concerns on…
A: Intro It's infuriating when you're unable to connect to your wifi network. Worse still, the…
Q: What exactly do you understand e-mail to be? How can I send an email from one place to another in…
A: Answer: What image do you have in your mind of the e-mail? How can I deliver email messages from one…
Q: What is the approximate loss per km for 850 multimode fiber? O.19 dB/km O.34 dB/km O2.0 dB/km O 1.1…
A: AS PER GUIDELINE I CANNOT ANSWER ALL Question - 13 Multimode fiber is used for short distances and…
Q: How can we ensure that the "building blocks" of a network, such as the switches, routers, and…
A: Explanation: A computer network is a network made up of two or more computer systems that are…
Q: A security framework may help a successful security infrastructure, but how? What are the…
A: Given: The protection of computer systems and networks against breaches, thefts, or damages to…
Q: Because of how they are constructed, wireless networks are the source of a variety of technical…
A: The above question is answered in step 2 :-
Q: What will the following Code segment print on the screen?
A: The output of the above java program will be :
Q: What is the Jaccard similarity between these two sets? A={a,b,c,d,e,f} B={h,i,j,k,l,m} What is the…
A:
Q: What does the word "computer programming" imply, and how does the process work? What are some of the…
A: Computer programming: The DML language is used in a basic SELECT query to create a list of table…
Q: Which organisational style is best for you?
A: Introduction: The vast majority of new firms begin as sole proprietorship. This is the most basic…
Q: In order to explain how to install various programmes, certain user and system software, such as the…
A: Given: If you're new to Linux and want Cent OS, follow these steps. Create Cent OS bookable media or…
Q: During the process of setting up and installing Linux, you will be given a variety of options from…
A: Introduction: During the configuration and installation of Linux, you have the following choices to…
Q: oes the User Datagram Protocol (UDP) relate to the Transport Control Pr
A: Introduction: Below the describe the User Datagram Protocol (UDP) relate to the Transport Control…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- 5. Let R = {1, 3, π, 4, 1, 9, 10}, S = {{1}, 3, 9, 10}, T = {1, 3, π}, and U = {{1, 3, π}, 1}. Which of thefollowing are true? For those that are not, why not? (d) 1 ⊆ U(e) {1} ⊆ T(f) {1} ⊆ S(g) {1} ∈ SArtificial Intelligence - Adversarial Search 1. Consider the following three variants of minimax search: the simple version, alpha-beta search, anddepth-limited search, and consider the games of tic-tac-toe and chess. For the chess game, supposethat the Threefold Repetition Rule and the Fifty-Move Rule, and the similar rules if any, are notconsidered, i.e., the game will not terminate if the same position occurs multiple times. For eachcombination of minimax variant and game, answer the following question: can that minimax variantpossibly never terminate, in computing the best next move? Justify your answer.Problem 8: Divide and Conquer Recurrences Consider the recurrence that naturally arises in some divide-and-conquer algorithms: T(1) = 1, T(n) = 4T(n/2) + n for n > 1 [a] Explain what the initial condition and the various parts of this recurrence mean in the context of the analysis of algorithms. [b] Use the Master Theorem to determine the order of magnitude of T(n). [c] Using the methods of our course, derive a closed-form formula for T(n). [d] For the case n = 2, test your formula for T(n) against the original recurrence.
- [Introduction to the Design and Analysis of Algorithms, 3rd Edition] Maxima search. A point (xi, yi) in the Cartesian plane is said to be dominated by point (xj , yj ) if xi ≤ xj and yi ≤ yj with at least one of the two inequalities being strict. Given a set of n points, one of them is said to be a maximum of the set if it is not dominated by any other point in the set. For example, in the figure below, all the maximum points of the set are circled. Design an efficient algorithm for finding all the maximum points of a given set of n points in the Cartesian plane. What is the time efficiency class of your algorithm?2 (**) Rubik's Cube Consider the task of solving Rubik's Cube. Please formulate it as a state-space search problem. Specifically, please define the state space and the successor function. For simplicity, let us consider a 2 × 2 × 2 cube.1.Consider the following Boolean Satisfiability problem:Given a Boolean expression consisting of variables, does the expression have an assignment for the set of variables where the expression evaluates to TRUE. (i)Outline, in pseudocode, an exact algorithm for the problem. This should guarantee a solution if one exists. (Please state clearly the algorithm used) (ii)For the exact method used in part (1) (i), estimate the time required for the algorithm to find an exact solution in the big O-notation.
- Prove that the following problem is NP: We're provided S and t. Is there a subset of S whose members add to t? Algorithm and Data Structure IssuesUsing c++ Apply both breadth-first search and best-first search to a modified version of MC problem. In the modified MC, a state can contain any number of M’s and any number of C’s on either side of the river. Assume the goal is always to move all the persons on the left side to the right side. The Initial state should be a parameter given to the program at beginning of execution. As in the original problem, boat capacity =2, the boat cannot move by itself, and on either side C’s should not outnumber M’s. For best-first search, you need to come up with an appropriate heuristic. In addition to solving the problem, your grade will also be based on th effectiveness of the heuristic. As an example, the program should execute as follows. Initial state… Enter number of M’s on left side of the river: 3 Enter number of C’s on left side of the river: 1 Enter number of M’s on right side of the river: 0 Enter number of C’s on right side of the river: 0 Enter location of the boat: L The output…Correct answer will be upvoted else downvoted. Computer science. There is an exhibit a1,a2,… ,an of n positive integers. You should isolate it into a negligible number of ceaseless portions, to such an extent that in each section there are no two numbers (on various positions), whose item is an ideal square. Also, it is permitted to do all things considered k such activities before the division: pick a number in the exhibit and change its worth to any certain integer. However, in this form k=0, so it isn't significant. What is the base number of consistent fragments you should utilize in the event that you will make changes ideally? Input The primary line contains a solitary integer t (1≤t≤1000) — the number of experiments. The principal line of each experiment contains two integers n, k (1≤n≤2⋅105, k=0). The second line of each experiment contains n integers a1,a2,… ,an (1≤ai≤107). It's surefire that the amount of n over all experiments doesn't surpass 2⋅105.…
- Problem 2: Search an ArrayConsidering the search problem, we have a list of n integers A = ⟨v1, v2, · · · vn⟩. We wantto design an algorithm to check whether an item v exists or not such that it should returneither the index, i, if it was found or −1 otherwise, when not found.a) Implement the algorithm in Pythonb) Empirically, show the performance curve of the algorithm using time measurements.c) Using the basics of the theoretical analysis, write the complexity of its worst-casetime.d) Prove your algorithm is correct—it terminates with the valid output in every caseThe function below has the recursive relation T(x,y) = 2T(y/2)+O(1) when x,y>0Knowing these information, find the following: 1) The worst-case time complexity of the function2) The worst-case auxiliary space complexity of the function3) Explanation as to how the time complexity of the function can be improved without using multiplication operations.Let A ={a1,...,an} and B ={b1,...,bm} be two sets of numbers. Consider the problem of finding their intersection, i.e., the set C of all the numbers that are in both A and B. a. Design a brute-force algorithm for solving this problem and determine its efficiency class. b. Design a presorting-based algorithm for solving this problem and determine its efficiency cla

