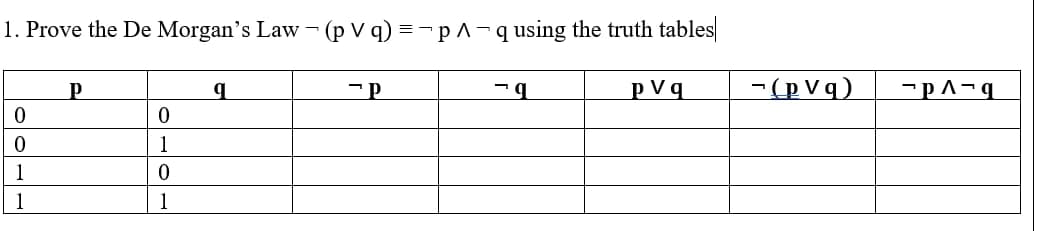
Prove the De Morgan's Law - (p V q) =-pA-qusing the truth tables| p Vq -(p V q) 1 1
Q: Give an example of how virtual servers are being utilized in the educational setting, if you…
A: Virtual Server: In contrast to dedicated servers, a virtual server shares hardware and software…
Q: Is there a governance challenge involved in transitioning from servers hosted on-premises to an…
A: Introduction:Architecture of Ia As:In the Ia As model, cloud providers host infrastructure such as…
Q: , what is the minimum number of children that a nonleaf, nonroot node may have?
A: Solution - In the given question, we have to select the correct choice.
Q: What exactly is the discipline of computer science, and how does it differentiate itself from other…
A: Your answer is given below.
Q: As a computer maker, make high-quality computers with fast processing rates accessible to everyone.…
A: Introduction: Processing speed refers to the amount of cycles/seconds it takes a central processor…
Q: When shifting your information technology systems to the cloud, where should you search for…
A: When shifting your information technology systems to the cloud, where should you search for…
Q: When an incoming call is received by a smart modem, it may automatically dial, reject, and answer…
A: Method of Error Detection: The most well-known error-detection approach is parity, in which each…
Q: What are the chances of providing both an introduction to the compiler and an explanation of why…
A: Examinability advice: This is the whole testability tip in its entirety.Use nonverbal communication…
Q: What was the rationale for the development of new programming languages?
A: what was the rationale for the development of new programming languages?
Q: Were you aware of the many uses for SSH? Please provide a list of all the SSH acronyms, along with a…
A: SSH acronym full form with brief explanation
Q: Write a program that first reads in the name of an input file and then reads the input file using…
A: def read_file(filename): file = None # open file try: file = open(filename) except: print("Unable…
Q: To connect the CPU and memory, should we utilize an asynchronous or synchronous bus? Who's got the…
A: Overview: The clock ticks on synchronous buses and instructions are only performed when the clock…
Q: Discrete event simulation's advantages may be explained in four ways
A: SIMULATION OF DISCRETE EVENTS: Discrete event simulation is a method for representing a system's…
Q: Discrete event simulation's advantages may be explained in four ways.
A: DISCRETE EVENT SIMULATION: Discrete event simulation is a method used to represent the many types of…
Q: List implementations include both array lists and linked lists. Give an example of why a linked list…
A: Given: List implementations include array lists and linked lists. Give an example of why an array…
Q: How does Model-View-Controller (MVC) contribute to the overall organization of web applications?…
A: data given: MVC organizes web apps. MVC architecture's advantages Answer: MVC organizes web apps.…
Q: What role do design patterns play in software development and how do they work? Which three design…
A: Design patterns are high-level solutions to problems that software engineers encounter frequently.…
Q: Which of the six steps that make up the DBLC does the data dictionary play a part in?
A: Given: A data dictionaryThe data dictionary is a component of a relational database management…
Q: What does the term "Internet of Things" (loT) or "machine-to-machine" (M2M) relate to?
A: Introduction: The term "Internet of Things" (10T) or "machine-to-machine" ( M2M) relate :
Q: What are the three best practices for enhancing your software's performance?
A: Techniques for Improving the Coding three орtimization options: 1. Elimination of often occurring…
Q: How does PACS tie in with the concept of the Internet of Things?
A: Introduction: PACS (Physical access control system)Software is used in physical access control…
Q: a) Employee motivation is a key to organisational performance, and the goal-setting model is said to…
A: There should a proper management for employees in an organisation.
Q: Is it true that discrete event simulation has four distinct advantages?
A: Answer: an adaptable and differing level of detail and intricacy of the reenactment model. The…
Q: It's possible that the referential integrity of a database may be compromised, which would have…
A: Referential integrity: Describes the link between two tables. Each table in a database must have a…
Q: What functions should your operating system's kernel do when it is booted up with a smaller kernel?
A: The Kernel is a kind of computer program, which is available at the basic core of the computer's…
Q: Why is wireless network throughput lower than wired network throughput?
A: Throughput in networking has the primary objective of defining the amount of data or packets that…
Q: I'd want to know more about the metrics used to evaluate the quality of the product and the software…
A: Introduction: A software metric is a program's measurable or countable property.
Q: What does the term "Internet of Things" (IoT) or "machine-to-machine" (M2M) relate to
A: Introduction What does the term "Internet of Things" (IoT) or "machine-to-machine" (M2M) relate to?…
Q: If you don't know where the update.txt file is located on your computer, it's a good idea to print a…
A: For Finding File Location: When you do not know the location of a file but know its name, you may…
Q: What is the significance of modeling discrete events?
A: Answer: Discrete event simulation (DES) is a method used to show real world frameworks that can be…
Q: Create a flowchart, pseudocode and program to display the sum of n numbers using a list. (PYTHON)
A: The question is to create a flowchart, pseudocode and program to display the sum of n numbers…
Q: Why? The power of today's computers is really astounding. Is there any evidence to back up the broad…
A: Given: PCs have been influential ever since its introduction, but now they are everywhere; we can…
Q: Give a brief description of four broad types of strategies for the Public key distribution.
A: The public key can be distributed in four ways: Public announcement Publicly available directory…
Q: Explain why it is important to simulate the system's context throughout development. If software…
A: INTRODUCTION : Context models are used to illustrate the environment in which a system is being…
Q: What are the key distinctions between a database and a data warehouse?
A: Answer in step 2
Q: Is it possible to explain in detail the four main benefits of continuous event simulation?
A: Continuous event simulation is critical: a risk-free setting Simulation is a safe technique to…
Q: It's important to understand how multipoint connections work in a mesh network.
A: Introduction A dedicated identification connection connects each device in a mesh architecture to…
Q: I already saw the responses to this question but I want another way. Please don't copy and past it!…
A: Here is the solution
Q: What are some of the most significant benefits associated with the client/server model of computer…
A: When compared to alternative methods of computer processing, the client-server architecture…
Q: Consider the impact of high-speed memory and processor devices and technologies on HCI improvements.…
A: Introduction: All of them are mostly unimportant. They are being driven by HCI, not the other way…
Q: I'd want to know more about the metrics used to evaluate the quality of the product and the software…
A: Introduction: Defining Software Metrics: Software development metrics are measures of the amount of…
Q: Implementations of database systems often make use of a strict two-phase locking protocol. Why is…
A: Locking protocol: If Locking and Unlocking can be done in two steps, a transaction is considered to…
Q: Create an anonymous block to display the number of classes offered for a given course.
A: Tables used: CLASSESTopics Incorporated => SQL SELECT with COUNT. To test: DECLARE…
Q: The CISO approaches the interns who seem to be breaking various security standards, who express…
A: Answer is given below-
Q: What sparked the development of computer languages?
A: In this modern era computer programming is very important.All those social media, mail system, phone…
Q: When a computer program is in an infinite loop, how can a programmer recognize it and get out of it?
A: Infinite Loop Detection and Escape : We introduce Jolt, a method to identify and escape endless…
Q: In order to create a compiler that is both fast and accurate, several factors must be taken into…
A: Compiler Optimization: An optimizing compiler is a piece of computer software that aims to minimize…
Q: What kind of experience do you have dealing with computer networks? Explain the differences between…
A: All computer network connects in different form ,some geographically ,some within limited area and…
Q: Please tell me if you have any examples of discrete event simulation.
A: Answer: Here is the example of discrete event simulation. For example, a truck shows up at a…
Q: etween a fat-c
A: While a fat client actually expects essentially occasional association with a network or focal…
Step by step
Solved in 2 steps with 1 images

- The set of letters S consists of 30 As, 6 Bs, 24 Cs, 15 Ds, and 15 Es. The set of letters T consists of 25 As, 20 Bs, 15 Cs, 5 Ds and 35 Es. What is the mutual index of coincidence between sets S and T? Leave your answer as a fraction in lowest termsLet R=ABCDEGHK and F= {ABK→C, A→DG, B→K, K→ADH, H→GE} . Is it in BCNF? Prove your answer.Solve this proof with no premises: (~Q->~P)->((~Q->P)->Q)
- Determine the truth tableComplete solutions must be shown, not just the final value for FUsing a truth table determine whether (p∧q) → q is a tautology, or a contradiction, or a contingency.Using Logically Equivalent Law's, Show that (p -> q) > (r -> s) and (p -> r) -> (q -> s) are logically NOT equivalent?

