provide internal storage to the CPU. * O Control units 1/0 devices O ALUS O Registers
Q: Ql) Fill in the blanks: 1- The acronym VHDL stands for. 2- FPGA consists of a matrix of…
A: Fill in the blanks.
Q: Design and write a C program that performs the following functionality: 1. Read your student number…
A: CODE #include <stdio.h> // for argv for command line argument int main(int argc, char…
Q: Consider a processor implementation, P1 of some RISC (MIPS or risc-v) instruction set architecture…
A: Answers Part a) The instruction class Ld/St has CPI(1)=4 and Frequency1= 30%=0.3 Let the instruction…
Q: In what ways could users be affected by the presence of several files?
A: The answer is given below.
Q: Write a JavaFX program that displays a 10-by-10 binary matrix, where each element in the matrix is…
A: import javafx.application.Application; import javafx.event.ActionEvent; import…
Q: A C E F H K M Figure 7.13 Module hierarchy of software system. Using the module hierarchy given in…
A: The Answer start from step-2.
Q: Calculate i) f(2,4) and ii) f(-3, 2) using Parmas's tabular expressions (normal table) _y =5 _y >5…
A: Answer i) f(2,4)=>
Q: Give the regular expression for the set of all strings having odd number of 1's
A: INTRODUCTION: Here we need to give the regular expression for the set of all strings having odd…
Q: Is there a difference between symmetric and asymmetric key cryptography?
A: Yes, there is a difference between symmetric and asymmetric key cryptography. The detailed…
Q: Use the encryption congruence C = (3P + 7) mode 26 to encode the message EASY
A: Given C=(3p+7) mod 26 Given message EASY A B C D E F G H I J K L M N O P Q R S T U V W X Y Z 1…
Q: WAP to calculate and display square of an integer and float variable using function overloading
A: Algorithm to display square of an integer and float variable Input float and integer variable to…
Q: Is it even feasible to describe how the development of integrated circuits led to the creation of…
A: Introduction: Is it possible to say that integrated circuits contributed to the development of…
Q: What are the names of the three most fundamental cryptographic operations?
A: Cryptography: Cryptography protects private information by encrypting it to prevent unauthorized…
Q: The following code extracts contains PIC18F2455 program. The readADC() function read: a value from…
A: Let us see the details below.
Q: Write C++ program to create a base class named Person that includes variables: name and age and then…
A: Your C++ program is given below as you required with an output.
Q: Explore the concept of abstraction by comparing and contrasting it with some instances drawn from…
A: Our assignment: The debate center's on the significance of abstraction in software engineering and…
Q: In order to understand how artificial neural networks operate, we need to know what they are.
A: Foundation: An artificial neural network (ANN) is a computer system component that simulates how the…
Q: Describe each assessment method in the realm of human-computer interaction in a few words. Testing…
A: Given: Human-computer interaction (HCI) research focuses a lot on how people and computers work…
Q: The Spiral Model may be useful for planning and managing even the smallest of projects.
A: Spiral Model: In the spiral model, which is used for risk management in the systems development…
Q: Today, it is important to evaluate the significance of wireless networks in developing countries…
A: Answer: because of following advantages Wireless Network is better than local area networks(LAN)…
Q: Examine the dangers and advantages of cloud security from a security stance. A move from on-premise…
A: Inadequate planning and execution went into the cloud's security architecture and strategy. There is…
Q: What's the most efficient approach to set up a routing table on each router?
A: Router: A router accepts data packets from other devices and forwards them to their intended…
Q: Write C++ program to print the following pattern: ** *** **** *** **** ******* *
A: Algorithm to print half pyramid pattern of star Input the number of maximum length of star i.e. n.…
Q: Data may be collected over time and then aggregated before being fed into a computer for processing.…
A: Before entering the information into a computer for processing, the data should be collected over…
Q: What is the difference between preemptive and non-preemptive scheduling? Create examples for each…
A: Given: Preemptive and non-preemptive scheduling have several key differences. The CPU is assigned to…
Q: Perform a cost-benefit analysis of deploying NAS (network attached storage) and SAN (network…
A: A NAS is a single storage device that delivers data via Ethernet and is affordable and…
Q: Why is multitasking, also known as multithreading, more frequent than having a number of processes…
A: A single process can contain many threads, each of which can operate independently while still…
Q: Explain the influence of "changing time quantum" on process execution in Round- Robin scheduling by…
A: Given: The time quantum is specified in Round Robin Scheduling, and then processes are scheduled…
Q: Directions: Read each item carefully. Create command/codes based on the information requested on…
A: Code: nvec <- c(1:30,34,45,47,50:70)cvec<-rep(c('A','B','C'),times=30)mat <-…
Q: Use case diagram] Draw a use case diagram for a story publishing system with the following…
A: The use-case diagram will include 6 actors:- Writer Proofreader Editor Agent Distributor Bookseller…
Q: Web servers employ a range of technologies to build customized web pages that are suited to the…
A: Client-side refers to the software that operates on the web browser of a user, while the server-side…
Q: How are RGB color beams formed in CRT displays
A: The Beam-Penetration method has been used with random-scan monitors. In this method, the CRT screen…
Q: What makes commercial SSDS distinct from those used in laptop computers?
A: Given: SSDs are more dependable and shock-resistant than conventional hard drives since they don't…
Q: The redundancy provided by network segmentation ensures high availability. With relevant visuals,…
A: Given: Network segmentation divides a network into smaller networks; network isolation creates and…
Q: What alternatives are there for maintaining data integrity in the field?
A: DATA INTEGRITY: In phase two, the data developer must integrate components that increase the data's…
Q: What are the main distinctions between conventional on-premises data centers and cloud settings when…
A: Given: Five differences between on-premises and cloud IT SECURITY solutionsTercentenary security is…
Q: To illustrate this point, consider the pros and downsides of using an example such as cloud storage.
A: Cloud based infrastructure has gained a lot popularity recently.
Q: It's possible that our LMS will be the target of a denial-of-service (DDOS) assault. In what ways…
A: DoS Attack: Denial-of-service (DoS) attacks target networks, websites, and online resources to deny…
Q: What criteria should be used to assess a cloud computing service by a company?
A: Faster delivery times and cheaper infrastructure costs are transition-specific benefits. To begin,…
Q: Q3: Consider that the values of parameters for the stop and wait ARQ protocol are as given below-…
A: Answers: We have to provide the detailed solution in the below Picture:
Q: What does the term "Data Preparation" indicate, and what steps are involved?
A: Data Preparation:- Data preparation is a pre-processing method that comprises cleaning and modifying…
Q: how services and apps that are hosted in the cloud may be accessed and utilized.
A: This question pertains to accessing and utilizing cloud-based services and applications.
Q: What was the significance of UNIVAC becoming the first commercially available computer?
A: The first computer made available for business usage was known as "UNIVAC."
Q: System management is based on the three-sphere model. Avoid copying examples from your textbooks.
A: A three-sphere model of system management: Three realms of system management exist.BUSINESS…
Q: Does a node need to be mobile if it has a wireless Internet connection? Explain Think about the…
A: wireless Internet connection: A network that delivers Internet access through transmission over the…
Q: How exactly does the notion of an infrastructure-based wireless network operate? What other tasks…
A: Infrastructure-based Wireless Network: An infrastructure-based network (IBN) is a wireless network…
Q: In microprocessor, zero flag is set to 1 when the result is zero the result is positive O the result…
A: Answers for both with explanation given below
Q: . List 5 ( FIVE ) point to explain what is business intelligence?
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: When it comes to cryptanalysis, what is the difference between differential vs linear?
A: Cryptanalysis it is the way to retrieve the plain text communication without accessing the key. It's…
Q: Instruction: Pick out the meaning of the underlined word. Question 1: Buy versatile clothes. Don't…
A: A noun is an element that represents a name, place, animal or a thing.
Hi
Solve the 2 q plz
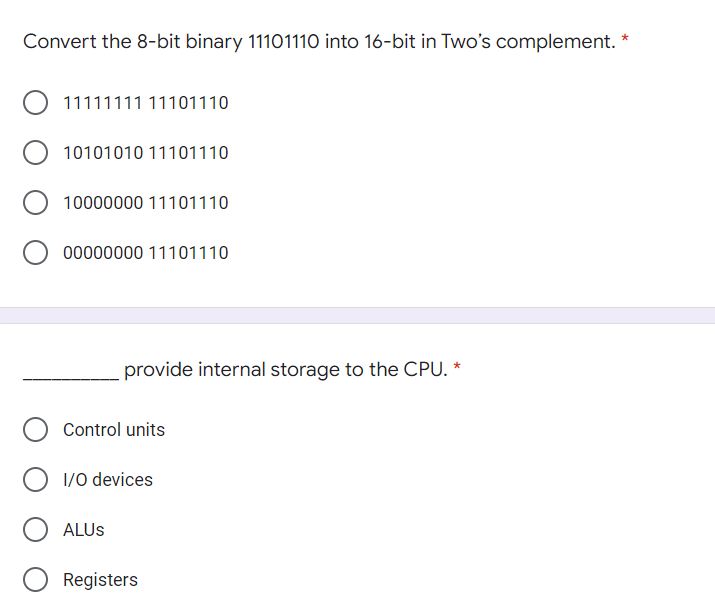
Step by step
Solved in 3 steps

- A 16-bit register in a computer contains 0011 1000 0101 0111. What does its contentsrepresent if it contains d) a 4-digit hexadecimal number (express your answer as a decimal number),e) a 16-bit signed binary number (express your answer as a decimal number),f) two characters in an odd parity ASCII code (the parity bit is on the left)?Computer Science Assume the following register contents: $t0 = 1111 1111 1111 1111 1111 1111 0011 1010 = 0xFFFFFF3A $t1 = 0010 0011 0100 0101 0110 0111 1000 1001 = 0x23456789 a. What are the decimal values of $t0 and $t1, respectively, if they are 32-bit two's complement signed numbers? b. For the register values shown above, what are $t2 binary and hexadecimal representations, respectively, for the following sequence of instructions? sll $t2, $t0, 4 or $t2, $t2, $t1 c. For the register values shown above, what are $t2 binary and hexadecimal representations, respectively, for the following sequence of instructions? sll $t2, $t0, 2 nor $t2, $t2, $t1 d. For the register values shown above, what are $t2 binary and hexadecimal representations, respectively, for the following sequence of instructions? srl $t2, $t0, 4 and $t2, $t2, $t13) Given binary data A = 10110110, and B = 01101001 in 8-bit CPU, please show the results of • A&&B • A&B • A||B • A|B • ~A • !A
- Consider the following hexadecimal readout: 000000 8A00 8E00 CFA1 48BF 7900 3202 9015 AD34 000010 0218 6D30 028D 3402 AD35 0288 3102 8D35 000020 0E30 0290 DAEE 3102 4C00 0200 0040 004B Refer to the first byte of memory shown above, address 000000. Assume that this byte is used to store an 8-bit unsigned integer. What is the decimal value stored in this byte? Group of answer choices 138 -27 22,842 66What bit pattern is stored for the following characters assuming an 8-bit byte? a. A b. a c. 8 d. % 2. What character is represented by the following bit patterns? a. 0011 0000 b. 0100 0011 c. 0111 1000 d. 0010 1010Calculate the value of the following arithmetic expressions as if they were performed on a 6- bit computer that uses 2’s comp: a) 0b011001 − 0b000111 b) 0b100011 + 0b111010 c) 0x3B + 0x06 d) 0xFF − 0xAA Steps are required.
- 0001 = Load AC from memory 0010 = Store AC to memory 0101 = Add to AC from memory 0011 = Load AC (the accumulator register) from an I/O device 0111 = Store AC to an I/O device With these instructions, a particular I/O device is identified by replacing the 12-bit address portion with a 12-bit device number. Remember that a number ending with a small ‘h’ means the number is a hexadecimal number. What is the hexadecimal string that expresses the following instructions? Load AC from memory location 62h. Add the contents of memory location 451h to AC. Store AC to memory location 8h. Store AC to I/O device number 8h.Given the following decimal numbers, convert the numbers to a 16-bit memory location in binary using two's complement. (show all details step by step) 165910 - 165910 954610 - 954610 Convert the following decimal numbers to binary using the two’s complement format, using 8 bits: 4810 -3910 -28410 010 Briefly explain why two’s complement is the best format for representing signed integers in a computer. 4. Convert the following decimal numbers to binary floating-point representation, using 4 bits for the fractional part: 68.510 125.4410 99.9910 give the answer of everything otherwise dont give. pleaseConsider a 32-bit hexadecimal number stored in memory as follows: Address Value 100 2A 101 C2 102 08 103 1B If the machine is little endian and the number is an IEEE single-precision floating-point value, determine the decimal equivalent of the number stored at address 100 (you may leave your answer in scientific notation form, as a number times a power of two).
- It is common practise to divide computer memory into many categories using bytes, each of which consists of 8 bits. How many dist values can a tell? How many distinct valueytes may be represented by two separate bytes?Calculate (3.41700875 *10-3 + 6.34005625*10-3)* 1.25625* 102 by hand, assuming each of the values are stored in the 16-bit half precision format describedin in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to thenearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.Write a program to determine Y, where Y= (2X +5) Assume that X is an eight bits .stored in any memory location

