Put the verb into the correct form: I sent Joe an email this morning, but (he/not/ reply)
Q: I need help with the following code: In C, write a program that will convert a binary number betwee...
A: I give the code in C as per your requirement along with output and code screenshot
Q: Identify the parts of the chaos program as follows: Color code each: identifier, expression, stateme...
A: Basically identifiers are called as naming words.Identifiers are used to name the entites like class...
Q: Figure Q3 shows the memory mapped I/O of a LPC1768 microcontroller. It shows that the microcontrolle...
A: Given The answer is given below.
Q: How many bit strings with length not exceeding n, where n is a positive integer, consist entirely of...
A:
Q: Determine where the filter is the low pass filter of high pass filter and use the EAYSEDA software s...
A: The answer is given below.
Q: Design a Class Customerinsurance that implements Customer and Insurance interfaces, The Customer...
A: An interface in Java is a blueprint of a class. All the methods in an interface are abstract All the...
Q: In 00, the concept of IS-A is based on: O Class inheritance and Interface implementation Interface i...
A: Given: To choose the correct option.
Q: Given the Boolean function F(x,y,z) = Σ(0,6), simplify it using the Karnaugh map. Be sure to type/wr...
A: steps:- draw the kmap. Fill the boxes by 1 as per the given numbers in question. here 0 and 6 is gi...
Q: DATABASE: library (library_name [pk], City, Phone, manager_SSN[pk, fk]) book (book_name [pk], Genre,...
A: answer is
Q: 1. Convert 82ADh to decimal. 2. Convert 11101b to decimal. 3. Convert 2BD4h to decimal.
A: Given: 1. Convert 82ADh to decimal.2. Convert 11101b to decimal.3. Convert 2BD4h to decimal. Goal: C...
Q: What part of the program has a BUG?
A: C program: C program is a general purpose programming language developed by Dennis Ritchie at AT&...
Q: Think of any form (other than the movie form done in the videos of this week) and create a component...
A: The answer is given below:-
Q: Natural – language processing makes more sense in a mobile environment than in a desktop environment...
A: - We need to talk about NLP and its effects on smartphones.
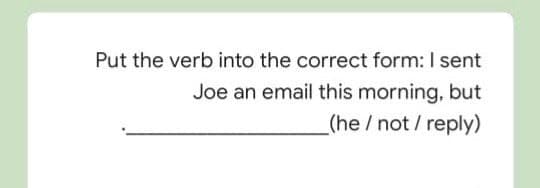
Q: Put the verb into the correct form: I sent Joe an email this morning, but (he /not/ reply)
A: The answer is given below.
Q: human computer interaction In designing a system, game or any relevant tasks, a task analysis is ne...
A: Task analysis is analysis of the task, how it is accomplished and this includes the detailed descrip...
Q: Which message timing factor impacts how much information can be sent and the speed at which it can b...
A: Defined the given statement
Q: ]: A # Exercise 1 1. If I'm using the and operator with two conditions that are both false, what is ...
A: Here in this question we have given some set of statement and we have asked to find the boolean valu...
Q: (b) What is the class of the sample (-3,-4) when you classify it with the LDA classifier. Justify th...
A: Bootstrap Aggregation or bagging involves taking multiple samples from your training dataset (with r...
Q: IP stands for Internet Protocol and is a best-effort protocol. Please explain what you mean. Why is ...
A: Protocol Internet: - It is a protocol that is used to route and address data packets in order for th...
Q: Paragraph Completion: Switzerland is only a small country but has rich natural endowments, especiall...
A: ANS:- Option 4:- In the alps the weather is generally cool even in the summer
Q: Put the verb into the correct form: The film wasn't very good. I it _(enjoy) .much
A: you question is about correct verb from
Q: Write a Java program to reverse elements in a array list?
A: Algorithm: 1.import util package 2.create a class called main 3.Create a list and add some component...
Q: Write 2 functions in C program thát calculate surface drea and the volume of 3 (three) boxes where t...
A: Logic:- iterate from i=1 to i=3 read l, b and h call volume(l,b,h) call(surfaceArea(l,b,h) disp...
Q: Explain why each principle is vital to security and how it permits the development of security mecha...
A: Introduction: A security policy is a collection of rules or processes that an organization imposes o...
Q: _init__(self, items: list) -> None: self._first = None for item in items: self.append(ite
A: “ArrayList” is a part of the collection framework and is present in “java.util” package. It provides...
Q: How many bit strings of length 10 contain at least three 1s and at least three 0s?
A:
Q: The________ method is used to create cross compilers for other computers
A: Filled the given statement
Q: Beginning with a singly linked list composed of 5 nodes, draw step-by-step the process of removing ...
A: Answer :-
Q: How does digital technology assist us in our daily lives?
A:
Q: Discuss/Explain how can an IT professional utilize the tools on your multiboot usb drive
A: A multiboot USB flash drive allows booting multiple ISO files from a single device. The ISO files ca...
Q: We want to construct a regular expression for the language accepted by the following DFA: b а,b a ´a...
A:
Q: Explain What Is Difference Between Baseband And Broadband Transmission?
A: Baseband is generally used for transmitting the signal using medium with the help of signal codes. B...
Q: Question 2 One of the important tasks in computational biology is to find short repeating patterns f...
A: let us see the answer:-
Q: Suppose you are given a binary tree with n internal key nodes. Show that the number of leaf key node...
A: total nodes = n+x {x is no. of leaf nodes} since internal nodes= ((n+x)-1)/2 n=((n+x)-1)/2 2n=n+...
Q: 1. Convert 82ADH to decimal. 2. Convert 11101b to decimal. 3. Convert 2BD4H to decimal.
A: Given: Goal: Convert given numbers into decimals.
Q: Consider a local network with a 1 Gbps access link to the Internet. Hosts on this network are access...
A: The LAN is mainly of two types wired LAN and wireless LAN. The wired LAN uses switches, servers, and...
Q: Consider a router connecting an input link to an output link. This router has a buffer where it can ...
A: Introduction Consider a router connecting an input link to an output link. This router has a buffer ...
Q: F(?,?,?)=?′?′?+?′??+??′?′+??′? can you simplify this and draw the diagram of the simplified function
A: As the function parameters are not present the function is resolved using a general understading.
Q: Plaso's psort command (choose all that apply): O Exports file content from a device, media image, or...
A: The answer is
Q: What is the big-O behavior of the following code segment? Explain. i = n; while ( i > 0 ) { ...
A: Algorithms and algorithmic problem resolving that can concern as a central place in computer science...
Q: 1. Compute the asymptotic complexity for the following recurrence relation: a. ao = 1 b. а, — а, -1+...
A: Given recurrence relation: a0 = 1 an = an-1 + 2 solving it using substitution method: an = an-1 + 2 ...
Q: Problem 2: Input age and identify the hours lived and hours slept using the formula below. HL - Age ...
A: Given: Goal: Write java program.
Q: 6. Given an random number generator rand5() that generates a uniform random integer in the range [1,...
A: By the given question we have rand5() function, which generates the random number between the 1 to 5...
Q: Put in much/many/little/few (one word only). Did you take _pictures at the ?wedding
A: Answer: I have given answered in the brief explanation
Q: curious to know what a m
A: Lets see the solution.
Q: write a simple shell.
A: ANSWER: Shell: A shell is a PC program that presents an order line interface which permits you to co...
Q: (25 min) The following table shows the foreign exchange rates for a few currencies. Foreign Currency...
A: Step 1 : Start Step 2 : Print the Currency Exchange Rate Table. Step 3 : Take user input of the Curr...
Q: Put in alan or the. It's a beautiful day. Let's .sit in garden
A: The given sentence is - It's a beautiful day. Let's sit in ________ garden.
Q: add $a0, $t5, $t5: sub $41, $t5, $s2:
A: The 5 stages in order pipeline as fetch, decode, execute, memory access and write back to use the ex...
Q: Write a piece of code that prints the elements of a queue of integers, one per line.
A: As no programming language is mentioned, it is solved using C++
Step by step
Solved in 2 steps

- For what reasons is it more probable that the meaning of an email may be misunderstood? There are at least two ways to improve the formality of your email communications. So, what about this alternative reading?For what reasons is it more likely that the intent of an email may be misunderstood? There are at least two things you can do to show professionalism in your email correspondence that will impress the other person. Is this alternative interpretation acceptable to you?What are some of the reasons why it is more probable that the intention of an email may be misunderstood? There are at least two helpful ways that you may conduct yourself in a professional manner in the email conversation that you have. What about the following understanding of the phrase?
- Different answer then other post please.Is it possible for an encrypted e-mail address to give proof to a sender that a receiver has read an e-mail message? Why do you think it is?For what reasons is it more likely that the intent of an email may be misunderstood? There are at least two things you can do to show professionalism in your email correspondence. How about this other interpretation?
- For what reasons is it more likely that the intended intention of an email may be misunderstood? There are at least two methods in which you may show professionalism in your email correspondence that can be advantageous to you. As an alternative, how about this?In the communication cycle, the the recipient needs to........... the message before understand the message. A. Nyatakan / Denote B. Pengekodan / Encode C. Nyahkod / Decode D. Pengekodan dan nyahkod / Decode and encodeThere are two major advantages of electronic mail over standard mail for modern communication. Be sure to back up your assertions with examples.
- Correct and detailed Answers will be given Upvoted else down voted What is meant by message ordering?I need only correct answer don't give me wrong answer. Send only correctIn general, applications like Voice over Internet Protocol (VoIP), online games, and live audio streaming use UDP connections rather than TCP connections. Justify the statement's accuracy.

