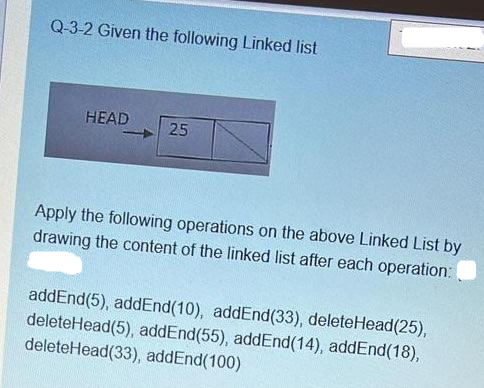
Q-3-2 Given the following Linked list HEAD 25 Apply the following operations on the above Linked List by drawing the content of the linked list after each operation: addEnd(5), addEnd(10), addEnd (33), deleteHead(25), deleteHead(5), addEnd(55), addEnd(14), addEnd(18), deleteHead(33), addEnd(100)
Q: Perioperative computers are used for what purposes?
A: Given: BasicsUsing a piece of software, a computer will process data that has not yet been processed…
Q: PROBLEM 11 Solutions Plus is an industrial chemicals company that produces specialized cleaning…
A:
Q: What is output? class Student { public: Student() { cout << "This is constructor" << endl;…
A: a special member function is responsible for initializing the class's objects in C++ the…
Q: How can you tell whether an application is interfering with a device's output? The stability and…
A:
Q: Suggest four reasons why the productivity rate of programmers working as a pair might be more than…
A: please check the step 2 for solution
Q: Q4. In a restaurant, whenever customers visit, they are provided with items from two categories, one…
A: Source codeBattery classpackage com.company;public class Battery { //instance variable…
Q: Exercises: Write a VB6.0 program to find the sum of first 10 numbers (1, 2,3, to 10).
A: CODE:
Q: Discuss the evolution of the internet as well as its technological foundation.
A: Introduction: Many networks are linked together via a variety of wireless and optical networking…
Q: Given the relation schema R(A, B, C) and S(C, D, E), please match each of the following relational…
A: Union Operator (∪) is used to find the union of two relational schemas. The result will include the…
Q: Java and C++ enable machine-independent programme development. How does "machine independence"…
A: Answer: Creating software needs the use of programming languages that can be executed by machines:…
Q: color and black-and-white posters, lithographs, and banners. The firm's owners, Kathleen and Lindsey…
A: Complete answer in EXCEL is below:
Q: Discuss one of the tools and techniques listed above and tell us how the technique selected can be…
A: Solution:: Let's choose Expert Judgement from the listed tools and ways of doing things. Expert…
Q: What are the dangers of having a security system placed everywhere? Why has this infrastructure not…
A: Security device: Security cameras are an excellent tool for increasing your feeling of security…
Q: Write a Java method that accepts an array of integer as input. The method returns true or false to…
A: * Java Code * import java.util.*; public class Main { static boolean isSorted(int[] array) //…
Q: Microcomputers changed software distribution. Who caused this change?
A: Start: The term "personal computer revolution" refers to another name for the "microcomputer…
Q: Solve the recurrence relations. a. Compute --2(2k + 1) k b. Compute 1+1
A:
Q: (d) If a command some_command would give exit code 7 when run, what will be the exit code of:…
A: Introduction: In the given code it is a code snippet of Linux where myvar is getting the value…
Q: WAP for mergesort program in C.
A: Code:
Q: Talk about the importance of database backup and recovery procedures and what they do. Then, go over…
A: The significance of database data backup and methods have been suggested, as well as their…
Q: switch times needed follow used: (a) Circuit switching; (b) Virtual circuit and datagram packet…
A: The answer is
Q: What exactly is SMP (Symmetric Multiprocessing)?
A: Multiprocessing (MP) is a computer hardware and software architecture in which many processing units…
Q: In one of convolutional layers a ConvNet, the input has the size of 68x62x32, and you convolve it…
A: The Answer is in Below Steps
Q: Make this C language code into modular code (functions) #include #include main() { char choice; int…
A: CODE:
Q: Discuss the main functions of vi editor in detail.
A: vi Editor vi stands for Visual Editor. vi is a text editor with a focus on screens that was…
Q: Create a Python program that calculates the monthly fuel cost for an automobile, given the average…
A: Explanation : - First miles per gallon is taken input from the user and stored into mpg Then, price…
Q: Write the differences between structures and arrays.
A:
Q: McQ 19. At present, the LAN used basically adopts star topology. a. Right b. Wrong 20. TCP/IP…
A:
Q: looking at adding some other mathematical formulas to our calculator, crat the code th determine the…
A: A triangle is shape of geometry of polygon in which three vertices and edges join to make a…
Q: A laptop's operating system may show signs of compromise in many ways. How can you detect if this…
A: Operating system: In order to compromise digital devices and networks, hacking is defined as gaining…
Q: {1, 3, 5, 7, 8, 9}. P(x) is the predicate "x is odd and x 5 Give a counterexample to show that P(x)…
A: Using the idea of predicates and negations, this problem can be resolved. Predicates are statements…
Q: 4. What postfix expression does this sequence of stack operations evaluate? What is its equivalent…
A:
Q: Consider a system with a dynamic range of 48 dB, find the following: a. Minimum and actual number of…
A: Dynamic Range= 48 dB Minimum and actual number of bits, Dynamic range= 20 log(2n-1)…
Q: IT departments may be organised in a variety of ways in commercial companies.
A: Here is the solution:
Q: the study of computers Discuss the importance of systems administration in a company.
A: Given: In a company, below the key aspects of system management is found. A business system…
Q: In the field of computer science, explain the relevance of cross-functional teams in the workplace.
A: GIVEN: Describe cross-functional teams' value in business. Multidisciplinary teams Cross-functional…
Q: Q-2-1 Write a C++ code to declare a node that contains two fields (Data and Next), multiply each…
A: code snippet:
Q: c++ problem Write a main function that does the following. 1. Store the words Computer Science into…
A: The question has been answered in step2
Q: The a. b. is the physical path over which a message travels. MEDIUM SIGNAL
A: The correct answer is given in the below step with an explanation
Q: PROBLEM 10 The Graphic Palette is a firm in Charleston, South Carolina, that does graphic artwork…
A: The solution includes a link to the flow diagram. The green type correlates to the price of a poster…
Q: 5. Find a closed form representation for the function defined recursively by f(0) = 5 and…
A:
Q: Prim's MSP algorithm has running time in terms of number of vertices n with number of edges k ~ n…
A: In this question, we have to select the correct option for running time complexity of prim's and…
Q: Problem: Derive the logic expressions for a circuit that compares two unsigned numbers: X = X2X₁ Xo…
A: Given that X = x2x1x0 and Y = y2y1y0 To compare two unsigned numbers, we need to compare…
Q: 5. Find a closed form representation for the function defined recursively by f(0) = 5 and…
A:
Q: Q-2-2 Write a C++ program to read the elements in a one dimensional array A[5], find and print the…
A: Program: #include <iostream> using namespace std; int main() { // decalaring i variable for…
Q: Curricula are also developed by educators. As a curriculumist, how do you propose to make your use…
A: Integrating technology into their instructional spaces: The ability of teaching staff members to…
Q: What exactly is SMP (Symmetric Multiprocessing)?
A: Symmetric Multiprocessing: Multiple processors working together to process data using symmetric…
Q: Kruskal's MSP algorithm has running time in terms of number of vertices n with number of edges k n…
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: Describe some of the exciting new applications that are becoming feasible as the internet of things…
A: Introduction: For starters, as IoT technology progresses, more firms will benefit from IoT…
Q: Explain top-down analysis with an example.
A: Answer:
Q: MCQ26: Which of the following is a software process model? a. b. Glassboxing Timeboxing
A: The statement given is:- To find which of the given options is software process model. The options…
Step by step
Solved in 5 steps with 5 images

- Select true or false for the statements below. Explain your answers if you like to receive partial credit 8) Which of the following is true about the delete function in a standard linked list (only a head pointer and nodes only having a next pointer)?a. There is only 1 scenario to consider when looking for a node to delete in a linked listb. When you traverse the list to find the element to delete, it improves theperformance to O(1)c. You should always check first to see if the list is empty before attempting to find and delete a nodeConsider the following piece of pseudocode:new DynamicArray dd[1] ← 1d[2] ← 2d[3] ← 3d[2] ← Ød[1] ← ØWhich of the following describes a linked list implementation of this pseudocode?a. Create a new empty linked list, insert a node (with value 1) with next pointer to null, insert a node (with value 2) at the end of list, insert a node (with value 3) at the end of list, remove end node.b. reate a new empty linked list, insert a node (with value 1) with next pointer to null, insert a node (with value 2) at the end of list, insert a node (with value 3) at the end of list, remove middle node, remove first node.c. Create a new empty linked list, insert a node (with value 1) with next pointer to null, insert a node (with value 2) at the beginning of list, insert a node (with value 3) at the end of list, remove end node.Which of the following statements regarding linked lists and arrays is correct? Group of answer choices: a. A dynamically resizable array makes insertions at the beginning of an array very efficient. b. Using a doubly linked list is more efficient than an array when accessing the ith element of a structure. c. A dynamically resizable array is another name for a linked list. d. Any type of list tends to be better than an array when there are a set number of maximum items known beforehand. e. If many deletions at any place in the structure were common, a linked list implementation would likely be preferable to an array
- A linked list is: A. set and once established cannot have new nodes or records added. B. variable in size, shrinking or growing as there is need C. fixed in size D. identical to a vectorReverse a singly linked list by changing the pointers of the nodes. The datarepresented by the list should continue to remain in the same nodes of the originallist.For example, given a singly linked list START, as shown in Figure P6.9(a), the listneeds to be reversed, as shown in Figure P6.9(b), by manipulating the links alone.8. Make a comparison between a linked list and a linear array. Which one will you prefer to use and when? 9.Given a linked list that contains English alphabet. The characters may be in upper case or in lower case. Create two linked lists—one which stores upper case characters and the other that stores lower case characters.
- Implement a program using Doubly LinkedList. Your doubly linked list should store information of students (Reg_no., Name, CGPA, city, age). Your program should provide following functionalities: Insert at Front Insert at Rear Insert in middle Delete from front Delete from rear Delete from middle Display all the data Data Structures in C++ Needed urgent i will thumb up for you1) Which of the following statements are true about Linked Lists. a) Linked Lists use exactly as much memory as is needed for for all nodes. b) Linked Lists always have a head reference c) Linked Lists can grow dynamically d) None of these answers. e) Linked Lists are efficient when you need random access. 2) What is the average Big O runtime of retrieving a value of an item in a link list given its index? a) O(n) b) O(1) c) O(n^2) d) None of these answers. e) O(nlogn) 3) When does the insert() function of a Dynamic List have a big O runtime of O(1)? a) When you are inserting to the end of the list. b) When you are inserting to the beginning of the list. c) When the size of the data is small. d) None of these answers. 4) Why does retrieving a value from an array have a runtime of O(1)? (Select all that reasons that make this possible.) a) Arrays use simple math calculations to compute the requested index location. b) Arrays have to search…Which of the following procedures may be performed in constant time on an unsorted singly linked list with head and tail references? Select the most complete option. (1) Insertion at the beginning of the linked list (2) Insertion at the end of the linked list (3) Remove the front node of the linked list (4) Remove the last node of the linked list (1) and (2) (1) and (3) O (1), (2), and (3) O (1), (2), and (3) O (1), (2), and (3) O (1), (2), and (3) O (1), (2), and (4) None of the above
- write a function that will swap tow adjacent elements by adjusting only the links (and not the data) using a single linked listsA singly linked list can be reversed by altering the nodes' pointers. The original list's nodes should still contain the data that the list represents.For instance, if a single linked list START is supplied, as in Figure P6.9(a), the list must be reversed using just the links, as in Figure P6.9(b).Please do not copy from chegg. C++ Dividing a linked list into two sublists of almost equal sizes Add the operation divideMid to the class ListData in Chapter17.cpp on Canvas as follows: void divideMid(ListData &sublist); //This operation divides the given list into two sublists //of (almost) equal sizes. //Postcondition: first points to the first node and last // points to the last node of the first sublist. // sublist.first points to the first node // and sublist.last points to the last node // of the second sublist. Consider the following statements: ListData myList; ListData subList; Suppose myList points to the list with elements 34 65 27 89 12 (in this order). The statement: myList.divideMid(subList); divides myList into two sublists: myList points to the list with the elements 34 65 27, and subList points to the sublist with the elements 89 12. Write the definition of the function template to implement the operation divideMid. chapter 17.cpp #include…

