Q. Lensures that the encrypted messages can be viewed only by authorized endpoints? Q. Every IP phone will come with a default Q. It is essential to securely lock the phone and the internal servers and also regularly update to keep up with latest security measures? Q. IP phones provide authentication by forcing the user to enter a password or logging in to the phone? Q. The main purpose of. maintenance and management is to get maximum utilization of the packet based VolP networks?
Q. Lensures that the encrypted messages can be viewed only by authorized endpoints? Q. Every IP phone will come with a default Q. It is essential to securely lock the phone and the internal servers and also regularly update to keep up with latest security measures? Q. IP phones provide authentication by forcing the user to enter a password or logging in to the phone? Q. The main purpose of. maintenance and management is to get maximum utilization of the packet based VolP networks?
Chapter12: Network Configuration
Section: Chapter Questions
Problem 10RQ
Related questions
Question
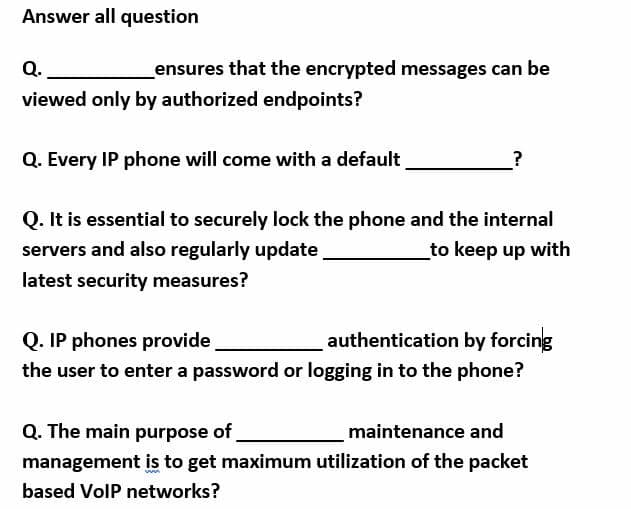
Transcribed Image Text:Answer all question
Q.
ensures that the encrypted messages can be
viewed only by authorized endpoints?
Q. Every IP phone will come with a default
?
Q. It is essential to securely lock the phone and the internal
servers and also regularly update
_to keep up with
latest security measures?
Q. IP phones provide
authentication by forcing
the user to enter a password or logging in to the phone?
Q. The main purpose of
management is to get maximum utilization of the packet
maintenance and
based VolP networks?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L